Web Application Pentest Lab setup Using Docker
In the world of cybersecurity, penetration testing and vulnerability assessment are crucial steps in identifying and mitigating potential security threats. With the increasing number of web applications, the need for secure and reliable testing environments has become more important than ever. In this article, we will explore the world of vulnerable web applications, their importance in penetration testing, and how to set them up using Docker.
Table of Content
- Introduction to Vulnerable Web Applications
- Prerequisite
- Setting up Docker on your Machine
- Setting up Vulnerable Web Applications using Docker
- Damn Vulnerable Web Application (DVWA)
- OWASP Juice Shop
- OWASP VulnerableApp
- OWASP WebGoat
- SQLi-Labs
- bWAPP
- OWASP Mutillidae II
- Damn Vulnerable GraphQL Application
- Damn Vulnerable RESTurant API
- Pixi
- PyGoat
- Server-Side Request Forgery
- VulnBank
- VulnLab
- OWASP WrongSecrets
- Yrprey
- Zero Health
- Conclusion
Introduction to Vulnerable Web Applications
Vulnerable web applications are intentionally designed to be insecure, allowing penetration testers and security researchers to test and improve their skills in a safe and controlled environment. These applications are crucial in identifying and mitigating potential security threats and are widely used in the cybersecurity industry.
Prerequisite
- Basic understanding of Docker and its commands
- Familiarity with Linux and web applications
Setting Up Docker on Your Machine
Docker is a platform that allows you to run applications in lightweight, isolated containers — perfect for deploying vulnerable apps without affecting your main system.
To install Docker and Docker Compose on a Debian/Ubuntu-based system, run:
apt install docker.io

apt install docker-compose

Setting up Vulnerable Web Applications using Docker
Here are the instructions for setting up various vulnerable web applications using Docker:
DVWA (Damn Vulnerable Web Application)
DVWA is a PHP/MySQL web application that simulates a vulnerable website, allowing users to practice exploiting common web vulnerabilities such as SQL injection and cross-site scripting (XSS).
To configure DVWA on Docker, you can use the following commands:
docker pull sagikazarmark/dvwa

docker run --rm -it -p 8080:80 sagikazarmark/dvwa

DVWA configuration & Login Steps
Access the Login Page
- Open DVWA in your browser (http://localhost:8080/login.php).
- Default Credentials:
- Username: admin
- Password: password
- Click Login.

Create/Reset the Database
- After logging in, you’ll see a “Database configuration” page.
- Click the “Create / Reset Database” button to:
- Initialize the DVWA database (if first-time configuration).
- Clear existing data and reset to default (if resetting).

Note: Ensure MySQL credentials in /var/www/html/config/config.inc.php are correct.
Main Page Loads Automatically
- After database configuration, you’ll be redirected to the DVWA Welcome Page.
- From here, you can:
- Select security levels (Low/Medium/High/Impossible).
- Access vulnerability modules (e.g., SQL Injection, XSS).

Juice Shop
OWASP Juice Shop is an open-source web application that is designed to be insecure, with over 30 vulnerabilities and challenges for users to discover and exploit.
To configure Juice Shop on Docker, you can use the following commands:
docker pull bkimminich/juice-shop
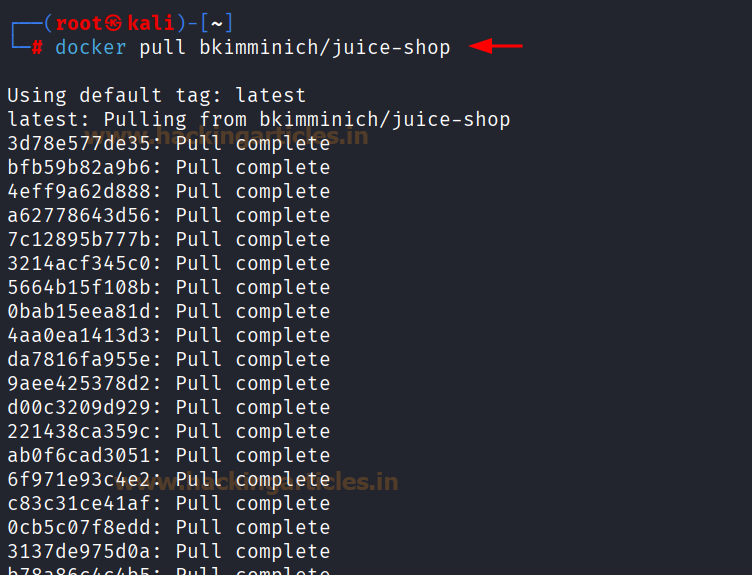
docker run --rm -p 3000:3000 bkimminich/juice-shop

Once you have started the Juice Shop container, you can access it by visiting http://localhost:3000 via your web browser. From there, you can begin your hands on testing journey.

OWASP VulnApp
OWASP VulnApp is a web application that is intentionally insecure to various types of attacks, offering an environment for users to learn about web security and practice exploiting vulnerabilities in a safe and controlled environment. It covers a range of vulnerabilities, including SQL injection, XSS, and file inclusion.
To configure OWASP VulnApp on Docker, you can use the following commands:
git clone https://github.com/SasanLabs/VulnerableApp.git cd VulnerableApp

docker-compose up

Once you have started the OWASP VulnApp container, you can access it by visiting http://localhost:80 via your web browser. From there, you can begin your hands on testing journey.

WebGoat
Web Goat is a web application that is designed to teach web application security through a series of lessons and exercises, covering topics such as authentication, authorization, and input validation.
To configure WebGoat on Docker, you can use the following commands:
docker pull webgoat/webgoat docker run -p 127.0.0.1:8080:8080 -p 127.0.0.1:9090:9090 -e TZ=Europe/Amsterdam webgoat/webgoat

Once you have started the WebGoat container, you can access it by visiting http://localhost:8080/WebGoat/login via your web browser. From there, you can begin your hands on testing journey.

SQLi-Labs (Dhakkan)
SQLi-Labs is a web application that is specifically designed to teach SQL injection attacks, providing a range of challenges and exercises for users to practice exploiting SQL injection vulnerabilities.
To configure SQLi-Labs on Docker, you can use the following commands:
docker pull acgpiano/sqli-labs docker run -d -p 80:80 acgpiano/sqli-labs:latest

Once you have started the SQLi-Labs container, you can access it by visiting http://localhost via your web browser. From there, you can begin your hands-on testing journey.
SQLi-LABS configuration & Challenges
Database configuration
- Click “configuration/reset Database for labs” to:
- Purge old database (SECURITY) if it exists.

-
- Create new tables (USERS, EMAILS, etc.) and populate them with test data.

- Output confirms successful creation of databases/tables (e.g., [*]……Creating New Table ‘USERS’ successfully).
Challenge Categories
- Page-1 (Basic): Error-based, blind, and time-based SQL injections (e.g., GET – Error based – Single quotes).
- Page-2 (Advanced): Complex injections like double injections, outfile dumping.
- Page-3 (Stacked): Multi-query injections (e.g., ST – Double Injection).
- Page-4 (Challenges): Mixed difficulty levels (Less-1 to Less-22).

bWAPP
BWAPP is a web application that is intentionally insecure to various types of attacks, offering an environment for users to learn about web security and practice exploiting vulnerabilities in a safe and controlled environment. It covers a range of vulnerabilities, including SQL injection, XSS, and file inclusion.
To configure bWAPP on Docker, you can use the following commands:
docker pull raesene/bwapp docker run -d -p 80:80 raesene/bwapp

Once you have started the bWAPP container, you can access it by visiting http://localhost/install.php via your web browser.
Click “here” to install bWAPP.

After Installation, main page will open.

Mutillidae
Mutillidae is a web application that is intentionally insecure to various types of attacks, offering an environment for users to learn about web security and practice exploiting vulnerabilities in a safe and controlled environment. It covers a range of vulnerabilities, including SQL injection, XSS, and file inclusion, and is known for its realistic and challenging scenarios.
To configure Mutillidae on Docker, you can use the following commands:
git clone https://github.com/webpwnized/mutillidae-docker.git cd mutillidae-docker docker compose -f.build/docker-compose.yml up --build –detach

Once you have started the Mutillidae container, you can access it by visiting http://localhost:80 via your web browser. From there, you can begin your hands on testing journey.

Damn Vulnerable GraphQL Application
Damn Vulnerable GraphQL Application is a GraphQL-based web application that is intentionally insecure to various types of attacks, offering an environment for users to learn about GraphQL security and practice exploiting vulnerabilities in a safe and controlled environment.
To configure Damn Vulnerable GraphQL Application on Docker, you can use the following commands:
docker pull dolevf/dvga docker run -t -p 5013:5013 -e WEB_HOST=0.0.0.0 dolevf/dvga

Once you have started the Damn Vulnerable GraphQL Application container, you can access it by visiting http://localhost:5013 via your web browser. From there, you can begin your hands on testing journey.

Damn Vulnerable RESTurant API
Damn Vulnerable Resturant API is a RESTful API that is intentionally insecure to various types of attacks, offering an environment for users to learn about API security and practice exploiting vulnerabilities in a safe and controlled environment. It covers a range of vulnerabilities specific to APIs, such as authentication and authorisation flaws.
To configure Damn Vulnerable RESTurant API on Docker, you can use the following commands:
git clone https://github.com/theowni/Damn-Vulnerable-RESTaurant-API-Game.git cd Damn-Vulnerable-RESTaurant-API-Game ./start_app.sh

Once you have started the Damn Vulnerable RESTurant API container, you can access it by visiting http://localhost:8091/docs via your web browser. From there, you can begin your hands on testing journey.

Pixi
Pixi is a web application that is intentionally insecure to various types of attacks, offering an environment for users to learn about web security and practice exploiting vulnerabilities in a safe and controlled environment.
To configure Pixi on Docker, you can use the following commands:
git clone https://github.com/DevSlop/Pixi.git cd Pixi docker-compose up

Once you have started the Pixi container, you can access it by visiting http://localhost:8000/login via your web browser. From there, you can begin your hands on testing journey.

PyGoat
PyGoat is a web application that is designed to teach web application security through a series of lessons and exercises, covering topics such as authentication, authorisation, and input validation. It provides a hands-on environment for users to learn about web security and practice exploiting vulnerabilities, with a focus on Python-based web applications.
To configure PyGoat on Docker, you can use the following commands:
docker pull pygoat/pygoat:latest docker run --rm -p 8000:8000 pygoat/pygoat:latest

Once you have started the PyGoat container, you can access it by visiting http://localhost:8000/login via your web browser. From there, you can begin your hands-on testing journey.

SSRF
SSRF is a web application that is designed to teach Server-Side Request Forgery (SSRF) attacks, providing a range of challenges and exercises for users to practice exploiting SSRF vulnerabilities.
To configure SSRF on Docker, you can use the following commands:
docker pull youyouorz/ssrf-vulnerable-lab docker run -d --name ssrf-lab -p 9000:80 youyouorz/ssrf-vulnerable-lab

Once you have started the SSRF container, you can access it by visiting http://localhost:9000 via your web browser. From there, you can begin your hands-on testing journey.

VulnBank
VulnBank is a web application that is designed to simulate a vulnerable online banking system, allowing users to practice exploiting common web vulnerabilities such as SQL injection and cross-site scripting (XSS).
To configure VulnBank on Docker, you can use the following commands:
git clone https://github.com/Commando-X/vuln-bank.git cd vuln-bank docker-compose up


Once you have started the VulnBank container, you can access it by visiting http://172.24.0.3:5000 via your web browser. From there, you can begin your hands-on testing journey.

VulnLab
VulnLab is a web application that is designed to provide a hands-on environment for users to learn about web security and practice exploiting vulnerabilities. It covers a range of vulnerabilities, including SQL injection, XSS, and file inclusion, and is known for its realistic and challenging scenarios.
To configure VulnLab on Docker, you can use the following commands:
docker pull yavuzlar/vulnlab docker run -d -p 1337:80 yavuzlar/vulnlab

Once you have started the VulnLab container, you can access it by visiting http://localhost:1337 via your web browser. From there, you can begin your hands-on testing journey.

WrongSecrets
WrongSecrets is a web application that is designed to teach users about secrets management and how to properly store and manage sensitive data.
To configure WrongSecrets on Docker, you can use the following commands:
docker run -p 8080:8080 jeroenwillemsen/wrongsecrets:latest-no-vault

Once you have started the WrongSecrets container, you can access it by visiting http://localhost:8080 via your web browser. From there, you can begin your hands-on testing journey.

Yrprey
Yrprey is a web application that is designed to simulate a vulnerable web application, allowing users to practice exploiting common web vulnerabilities such as SQL injection and cross-site scripting (XSS).
To configure Yrprey on Docker, you can use the following commands:
git clone https://github.com/yrprey/yrprey-application.git cd yrprey-application docker-compose -f.docker/dev/app.yaml -p yrprey up -d

Then, once you have started the Yrprey container, you can access it by visiting http://localhost:3005 via your web browser. From there, you can begin your hands-on testing journey.

Zero Health
Zero Health is a web application that is designed to simulate a vulnerable healthcare system, allowing users to practice exploiting common web vulnerabilities such as SQL injection and cross-site scripting (XSS).
To configure Zero Health on Docker, you can use the following commands:
git clone https://github.com/aligorithm/zero-health.git cd zero-health docker-compose up

Then, once you have started the Zero Health container, you can access it by visiting http://localhost:3000 via your web browser. From there, you can begin your hands-on testing journey.

Conclusion
Vulnerable web applications offer hands-on opportunities for both Red and Blue Teams to sharpen their skills. By mapping these apps to the MITRE ATT&CK framework, security professionals can simulate real-world attack chains and improve their defense posture. Docker makes deploying these labs easy and repeatable. Whether testing XSS, SQLi, or API abuse, always follow ethical guidelines and use them in isolated environments.
To Learn more about Container Security. Follow this Link.
Author: Anmol Dev is a Technical Writer, Researcher and Penetration Tester. Contact here: Linkedin and Twitter.
Hello Kavish,
I like your post and I am interested to learn penetration testing, I did CEH v10 and I am IT auditor by profession. So could you please help me with this.
Thanks in advance.
contact ignite technologies
https://ignitetechnologies.in/
git clone https://github.com/eystsen/pentestlab.git
when we are using this command it is asking for the username and password sir…..
Its working sir…no probelm
Thanks for a good article!
I’m using that script myself and it used different localhost IPs for each app.
So it will not use 127.0.0.1 as you mentioned above. It will use:
127.1.0.1,
127.2.0.1,
127.3.0.1, etc
can the lab be accessed via the internet without using vps?