A Deep Drive on Proactive Threat Hunting
We all know that the proactive threat hunting is need of the hour and as we have already discussed the basic requirement that highlights all generic step required for Threat Hunting Activity in our previous article “Threat Hunting – A proactive Method to Identify Hidden Threat”.
In this post, we will explain the main factors that organizations should consider before conducting a threat hunting activity. These key factors will help an organisation to prepare a roadmap of the hunting activity before execution.
Table of Content
- The pyramid of Pain
- Threat Hunting Techniques
- Datasets
- Hunting Maturity Model (HMM)
The Pyramid of Pain
The Pyramid of Pain, first proposed by security professional David J Bianco in 2013, concentrates on incident response and threat hunting in order to improve the applicability of attack indicators.
- The Pyramid measures the potential usefulness of your Intel
- It also measures the difficulty of obtaining that Intel
- The higher you are, the more resources your adversaries have to expend.
For example, if an attacker uses malware to exploit an endpoint within their attack chain and the security professional, as a defender, uses file hash values to distinguish such actions, they can trivially recompile the malware illustration so that the file hash value the team uses to detect the original sample becomes useless.

Hash Values: Identifying Indicator of compromise with the help of the corresponded hash values is a most trivial step. Unfortunately, they are extremely susceptible to change (even accidentally).
IP Addresses: An IPv4 or IPv6 address, in most cases netblocks or CIDR ranges also fit here.
An only foolish person uses their own addresses. VPNs, Tor, open proxies all make it easy to change the IP address.
If it’s hardcoded into a config, maybe adversaries have to do a little work to update it. We have found that attackers have begun to manipulate or confuse targets with malicious IP in DWORD format. The definition of a malicious URL is as follows:
“http:// 77683606/GoogleSearch.image”
IP to DWORD format
1) This can be done by separating the original IP into four octets. Let’s take the above IP address, which is “74.21.11.150”. Split the IP address into four octets – 74, 21, 11 and 150.
2) Covert each octet into HEX and you will get “4a15b96” for all four octets.
3) Further, change HEX “4a15b96” into decimal and ultimately you will get “77683606” which is the DWORD form of the IP address.
Domain Names:
This could be either a domain name itself (e.g., “freeinternet.net”) or maybe even a sub- or sub-sub-domain (e.g., “the.new.game.freeinternet.net”).
The attackers use the fast-flux or double flux to mask and safeguard their actual infrastructure. They compromised a range of easy targets like vulnerable computers or weak home routers. These routers are then used as tunnels for carrying command-control messages and data across the actual network
As per a report “APT1: Exposing One of China’s Cyber Espionage Units | Mandiant | FireEye,” you can read how an attacker plan to get a domain registered for APT1.
1) The first persona, “UglyGorilla”, has been active in computer network operations since October 2004. His activities include registering domains attributed to APT1 and authoring malware used in APT1 campaigns. “UglyGorilla” publicly expressed his interest in China’s “cyber troops” in January 2004.
2) The second persona, an actor we call “DOTA”, has registered dozens of email accounts used to conduct social engineering and spear-phishing attacks in support of APT1 campaigns. “DOTA” used a Shanghai phone number while registering these accounts.
3) We have observed both the “UglyGorilla” persona and the “DOTA” persona using the same shared infrastructure, including FQDNs and IP ranges that we have attributed to APT1
Network/Host Artifacts:
It is very difficult for an adversary to conduct any useful operation without leaving any traces, which ensures that any byte flowing through the network as a result of an adversary’s involvement may be an artefact.
For example, Classify the outbound traffic with a C&C server that will be viewed as network artifacts, while on hosts, search for files & folders, registry objects, mutexes, memory strings will be considered as host artifacts.
Tools: In this step, the hunter tries to investigate “what kind of program or command might be used by intruders to achieve their target” such as PowerShell, mimikatz, or other restriction circumvent commands for a lateral moment.
Tactics, Techniques and Procedures (TTPs): In this phase, the hunter attempts to examine “how the intruder achieves its target with the aid of the cyber-kill-chain” (as discussed in Part-I). They choose social engineering to target such as phishing, which is the most common TTP used to trap the user in order to gain a foothold in the network by linking a malicious object to the mail.
Threat Hunting Techniques
Skilled threat hunters use a variety of techniques when reviewing data sources such as firewall logs, SIEM and IDS warnings, DNS logs, file and network data, authentication systems, and other sources in order to detect IoCs and recognize the threat.

SEARCHING
This is the simplest and least difficult technique used in threat hunting. It is the process for querying data for specific artifacts using defined search criteria and tools. It involves environmental data to analyze like logs, alerts, memory dumps, system events etc. As a security professional who involves in threat hunt need to analyze more data so in starting of threat searching. It’s not possible to know exactly what you are looking for. So, there are two important factors need to keep in mind while doing a search:
- Too wide hunting for common artifacts that can produce unnecessarily varied results of very little use.
- Focusing too specifically will lead to very few findings and prevent it from being concluded.
CLUSTERING
Clustering is an analytical process, typically performed using machine learning. Involving the classification of related classes (or clusters) of data points based on certain behaviors from a wider range of data. In actual fact, the technique is popular in various fields such as machine learning, pattern recognition, retrieval of information, data compression and computer graphics, for statistical data analytics.

source: https://en.wikipedia.org/wiki/Cluster_analysis
A statistical technique in which analysts establish groups of like data points on specific aspects of a large data set and separate them into groups. This is most effective when acting upon a broad group of data points that do not share behavioral characteristics. Clustering finds precise cumulative behaviors, like an unusual number of instances of a common occurrence, through various applications such as outlier detection.
Read more from here: https://en.wikipedia.org/wiki/Cluster_analysis
GROUPING
The grouping includes taking a variety of different objects and determining when multiple objects come together based on common criteria. This involves identifying common criteria that people use to group objects, such as incidents that occur within a given period. Users should best apply this when hunting for other artifacts that are equally unusual.
Researchers perform the grouping differently from clustering by looking at unusual data sets and their concerns to see the root cause, whereas clustering uses enormous quantities of data to classify data sets that require more analysis using the grouping technique.
STACKING
Hunters conduct the stack counting analysis method in a simulated haystack to find the needle. It is the most popular practice for examining a hypothesis.
“You are familiar with the term if you have ever used the pivot tables of Microsoft Office, the stats command of Splunk, or the “top” command of Arcsight”.
Researchers use data stacking to isolate and classify patterns by using frequency analyses in large quantities of related data. They need an algorithmic method to reduce vast volumes of data that can be processed and analyzed into manageable chunks.
In the context of a large data set, the investigator identifies the characteristics that differentiate the odd data rows and may prove that they are malicious. Instead, these attributes are the grouping parameters used to build estimates for the frequency analysis.
For example, To identify a thread count with the help of Process Explorer.

Datasets
The methods you use are all part of the strategy and experience of what you will do. If you don’t have sufficient details, but what is the right details, you can’t hunt? The response to that question is dependent on what you are aiming for. But the following is a broad list of datasets that are well-suited for hunting and security:

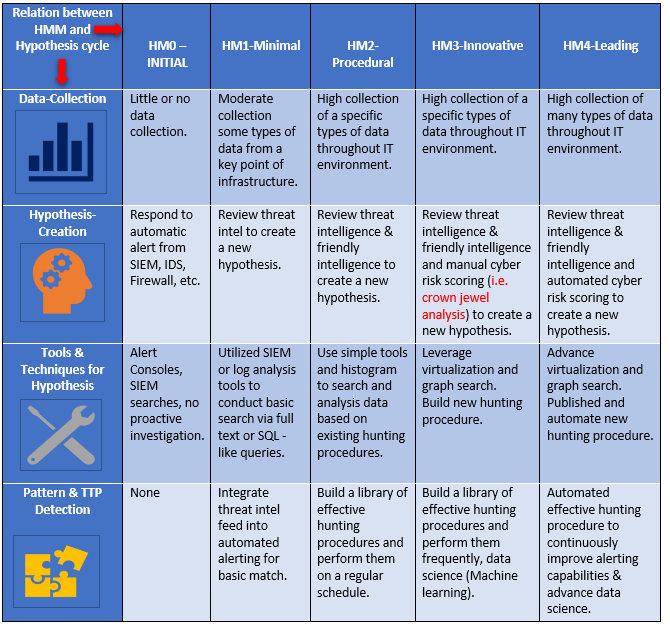
Hunting Maturity Model (HMM)
The Hunting Maturity Model was developed by Sqrrl’s security architect and David JBianco. It measures the current maturity level of hunting of any organization based on the data collection, creates data analysis procedures, incident responses, and hunting automation.
There are five levels of Hunting Maturity Model (HMM)
The increasing level of maturity demonstrates how an organization can track and establish data analysis procedures (DAP) based on the data it collects and its hunting automation. Analysts and managers will use the HMM to assess the current maturity and to build a roadmap.
HM0 – INITIAL:
HM0 uses automated alerting tools, such as IDS, SIEM, or antiviruses, mainly to identify malicious activities across the organization. They may provide signature update feeds or indicators of threats and even build their signatures or indicators, but these are fed directly into the monitoring system.
HM1-Minimal:
An organization in HM1 still relies mainly on automatic warnings, but at least some routine IT data collection they carry out. They also utilize threat intelligence to drive
detection.
HM2-Procedural:
At Level 2 maturity, an organization follows analysis procedures created by others. It has a high or very high level of routine data collection. They may periodically practice and adapt procedures developed by others and can make minor improvements but are not yet able to establish entirely new guidelines themselves.
HM3-Innovative:
At least a few hunters are present in HM3 organizations who understand different forms of data analysis techniques and are able to use these approaches to detect malicious activities. Such organizations are typically those which establish and publish procedures rather than depend upon procedures established by other parties (as in the HM2 case).
HM4-Leading:
HM4 is exactly the same as HM3, with a significant difference: automation. We will introduce and translate every effective hunting process at HM4 into automatic detection. This liberates analysts from the pressure of continued implementation of the same processes and encourages them than to focus on developing current or new processes.
Keywords: Crown jewels analysis: Crown Jewels Analysis (CJA) is a process for identifying those cyber assets that are most critical to the accomplishment of an organization’s mission.
Reference:
https://www.threathunting.net/files/hunt-evil-practical-guide-threat-hunting.pdf
https://www.threathunting.net/files/huntpedia.pdf
Author: Nisha Sharma is trained in Certified Ethical Hacking and Bug Bounty Hunting. Connect with her here