Steganography: The Art of Concealing
In this post, we will introduce the multiple ways for hiding any text that are based on Audio, Image, Video and White text. For achieving this we will use a method that is known as “Steganography”. The term steganography refers to the technique of hiding secret data within an ordinary, non-secret, file or message in order to avoid detection. So here we will check all those methods that can help us for doing the same.
Table of Content
Introduction
Purpose of steganography
Methods of steganography
- Audio-based steganography
- Image-based steganography
- Video-based steganography
- White text Steganography
Introduction
Steganography is the practice of hiding a file, message, image or video in another file like message video or audio. In general, the hidden message seems like something else like pictures, articles and sometimes shopping list. While the practice of encryption is to protect the content of a message alone, the style of steganography both concerns the disclosure and content of a secret message. Steganography covers data concealed in computer files. So, let’s understand this in a better way with the examples. First, let’s understand what is the purpose of steganography.
Purpose of Steganography
Effective communication is steganography. At first, you can encrypt and hide a private file inside a picture of another file type before sending it to somebody else. The likelihood of being intercepted will reduce. If you send any encrypted file to someone the other person will try to decrypt it in many ways and possibly, he will be able to do so. But in this case, it will reflect like a normal image and the other person will have no hint that what can be there on the other side of the picture. So, it is always a better and safe way of communication for those organisations where they want to protect their selves from these kinds of attacks.
So, let’s start and see how it works.
Audio Steganography
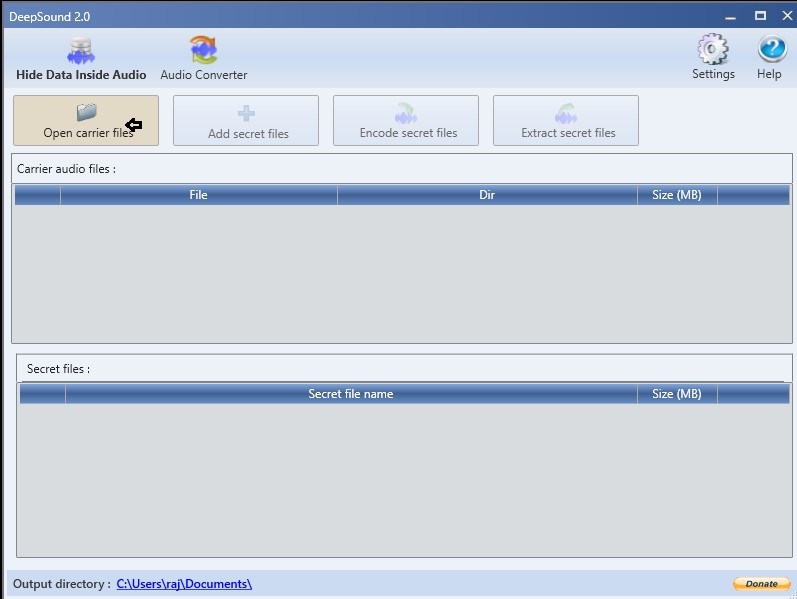
First, we will install a software named deep sound which is meant to convert all our audio files to some other format files. For installation please visit the link given below
https://deepsound.en.uptodown.com/windows
Conceal Approach: Now open the application and click on open carrier files and select an mp3 file behind which you want to conceal the original file.
Here we have selected an audio file behind which we will hide the data as we have done.

After selecting the file, we will now click on add secret file and give any file here which we want to conceal. Here we have opted for a document file.

Here you can further add one more extra security layer which is encoding by putting a password to the file. As you can see that we have given 123 as a password without which it won’t be possible for the other person to open the file.

The file is created successfully.

Now we can share this mp3 file with the other person to continue the hidden communication in the network.
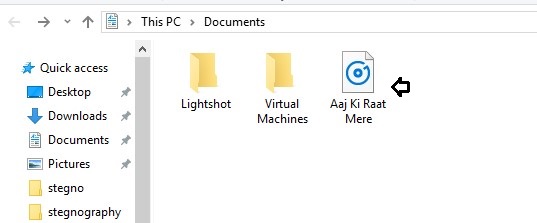
Reveal Approach: The person also needs to open this with the same password which we had given for encoding. As the other person enters the password, he will be able to see the concealed content of the file by clicking on extract files.
As the other person enters the password, he will be able to see the concealed content of the file by clicking on extract files and the doc file is extracted successfully. So, by this tool, we have successfully concealed our doc file behind the mp3 file.

Image Steganography
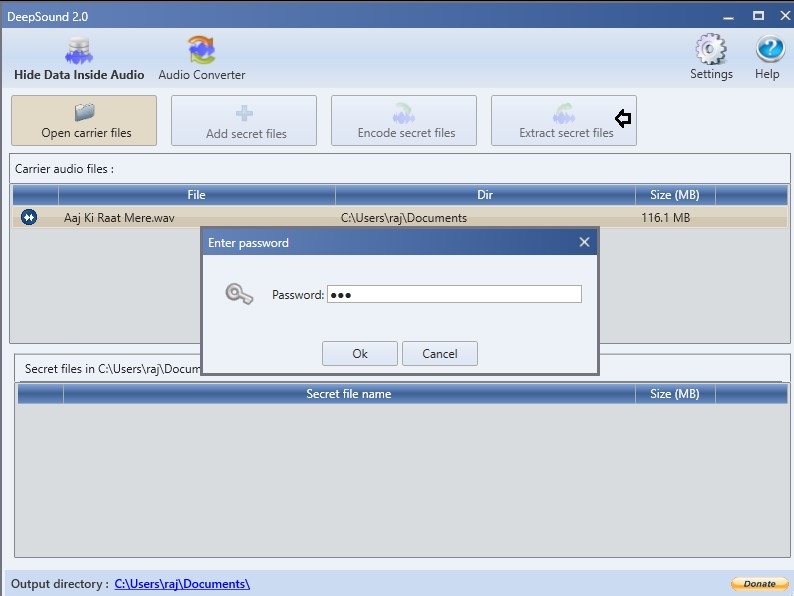
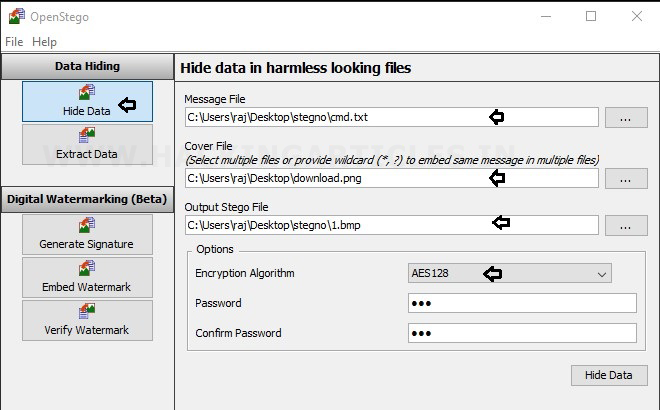
Let’s now hide some text file behind an image file. So, we have installed the next tool which is OpenStego.
Conceal Approach: We will first select the doc file which we want to hide. After that we will add the image file behind which we will conceal the doc file. And then we will choose a password and the concealed file is created.
Reveal Approach: Now we will extract the doc file by adding the image and then giving the right password and we have extracted the doc file.

Video Steganography
Now let’s see how we can hide anything behind a Video file. For this, we will install the tool Our secret from the link given here.
https://oursecret.soft112.com/
Once it is downloaded successfully. We will now be trying to conceal a doc file behind a video file.
Let’s start.
Hide: So first we will select a video which went to send. So, by clicking on select a carrier file we will choose our video. And then that file which we want to hide and then giving it a password and click on hide and our new file is created.

Unhide: Now we will try to open this file with the same tool for unhiding and it will ask for the password. Once you will enter the password, we will get the concealed file here.

Text Steganography
Now we are moving towards a new idea of steganography which is white space steganography. In this kind of steganography, we will hide text behind the text which will be not possible for anyone to judge. For this, we will visit a website

Conceal Approach: Here we will click on encode and add the text which you want to hide and click on encode.

As you clicked on encode you will see that a new text encoded file is created.

Reveal Approach: To decode this encoded text, we will copy this text and paste it in the box given and click on decode.
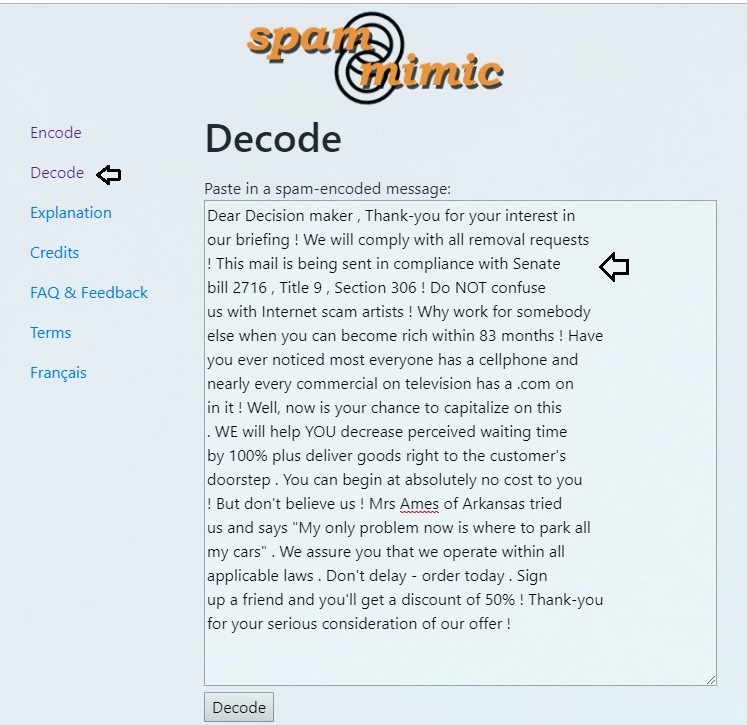
And finally, you will get the message which was hidden behind that.

Another Method
Conceal Approach: That’s not all! We can also send this message as an excel file which is hard to detect for anyone. To use this feature, we will click on “encode as a spreadsheet” and enter the text which you want to conceal and click on encode.
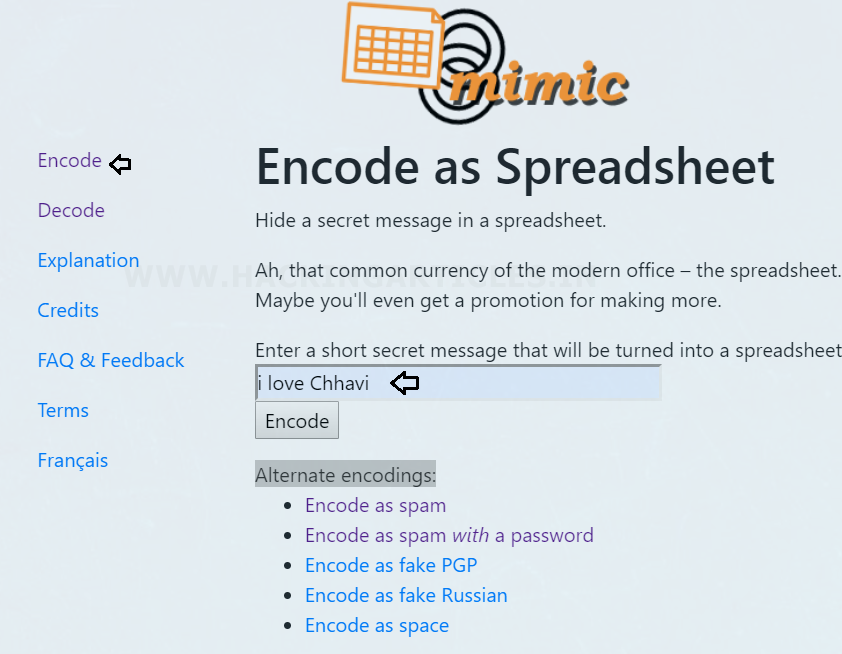
Then this generates a new excel file to conceal our “secret message” behind its record.

When we open this excel file it seems a very normal excel file by which no one will get to know the real message behind that.
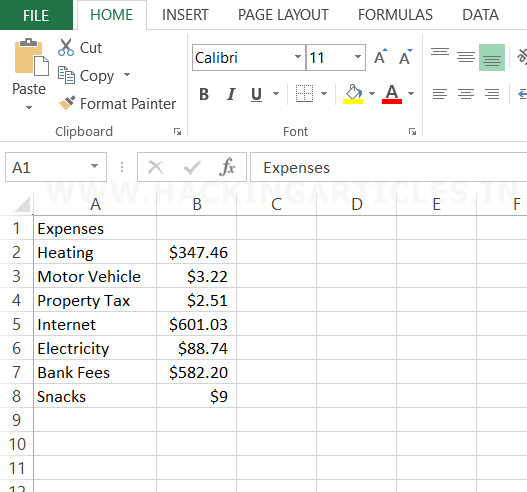
Reveal: But as we know that there is a hidden file behind this so we will decode this. So first click on decode fake spreadsheet.

Now paste the sheet which we want to decode in the column and click on decode.

Now you will get the real hidden message which was there behind this excel file as we got successfully.

So, it’s very clear that there are several ways of sending safe secret messages by the art of steganography.
To learn more about Steganography and Cryptography. Follow this Link.
Author: Geet Madan is a Certified Ethical Hacker, Researcher and Technical Writer at Hacking Articles on Information Security. Contact here
Very interesting… but how can we detect steganography contained in a file doc, mp3, xls? There is a tool that shows if a file has information hidden in it?
Thankyou for the appreciation
Yes there are some tools which can detect if there is something hidden in the original file and these are available in Kali.
For this information please wait for our upcoming article where you will find all the answers of your query.
Thks