Incident Response: Windows Account Management Event (Part 2)
To perform well and ensure its maintenance, administrators must monitor and manage events on a system, which is extremely important. Meanwhile, administrators use Event Logs, a built-in part of the Windows system, to track events created on a system. Among these, Windows Account Management Events are particularly critical, as they provide insights into user account activities such as creation, deletion, or modification. Additionally, administrators or users can check these logs locally or remotely at regular intervals. Furthermore, administrators can import these logs into a SIEM tool, which enables them to view the logs and ensure efficient Incident Response. In this way, administrators can proactively manage system events, identify potential issues, and respond to incidents effectively.
Incident Response: Windows Account Management Event (Part 1)
Table of Contents
- Security Policy Settings
- Advantage of security settings
- Event Log
- Account Management Events
- Events in Windows Server 2016
Security Policy Settings
Administrators use a set of rules to configure a computer or multiple devices, securing resources on a device or network. Meanwhile, the Security Settings extension of the Local Group Policy Editor enables administrators to define a security configuration as part of a Group Policy Object (GPO).
In addition, administrators link GPOs to Active Directory containers, such as sites, domains, or organizational units, allowing them to manage security settings for multiple devices from any device joined to the domain. Furthermore, security settings policies play a crucial role in overall security implementation, helping to secure domain controllers, servers, clients, and other resources within an organization.
Advantage of Security Setting
- Administrators authenticate users on a network or device.
- Meanwhile, administrators define these users to access the resources that are present.
- Whether to record a user’s or group’s actions in the event log.
- Membership of a user in a group.
Event Log
The event logs usually keep a record of services from various sources and then stores them in a single place. Events logs can be of Security, System and Application event. As an incident responder, you should look for multiple sources of log information and should not forget to look at the older log files which may be present in backup systems or volume shadow copies.
When Event logs are assessed, Event IDs have various field details with them. Meanwhile, these Event IDs include various field details.

Account Management Events
Moreover, administrators consider Account Management extremely important, and they use these events to track the maintenance of users, groups, and computer objects in Local users and groups, as well as Active Directory. For instance, Account Management events enable administrators to track the creation of a new user account, password resets, or changes to group membership, such as adding or deleting members from a group.
Additionally, administrators can categorize account management events into different types, which helps them to better organize and monitor these events. Consequently, this categorization allows administrators to respond more effectively to various account management activities, such as user account creation or group membership changes.
Events in Windows Server 2016
Now, Switch on your Windows Server 2016 to get you started.
Event ID 4727

When you create a security-enabled – global(scope) group, then this event is generated.

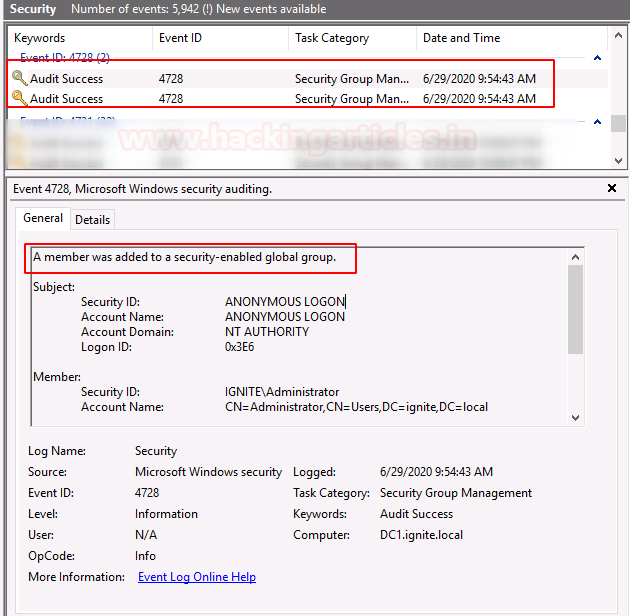
Event ID 4728
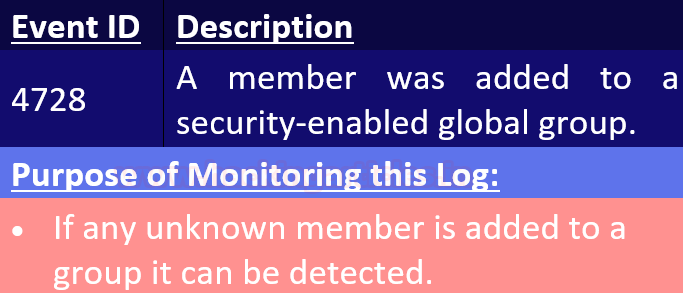
When you add a new member to a security-enabled -global group, then this event is generated.
Event ID 4729

You can go to the properties of the user and remove the user from the group.
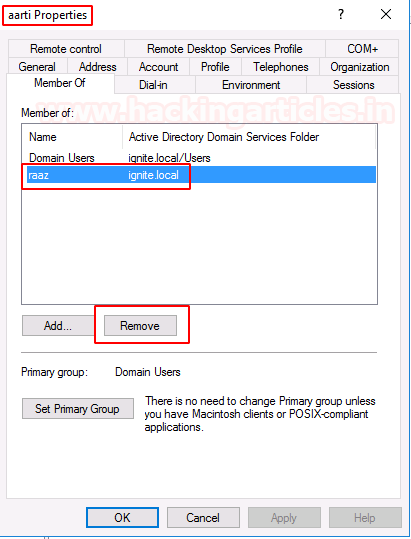
When a member is deleted from a group, this event is created.

Event ID 4737

When security enable group was changed, or any changes were made, this event was created.

Event ID 4741

Create a new computer account, using system properties by changing settings.

When a new computer account is created, this event is created

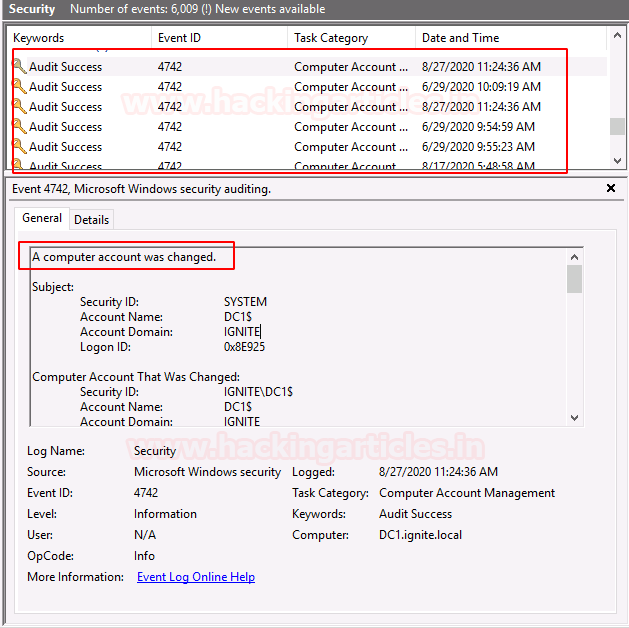
Event ID 4742
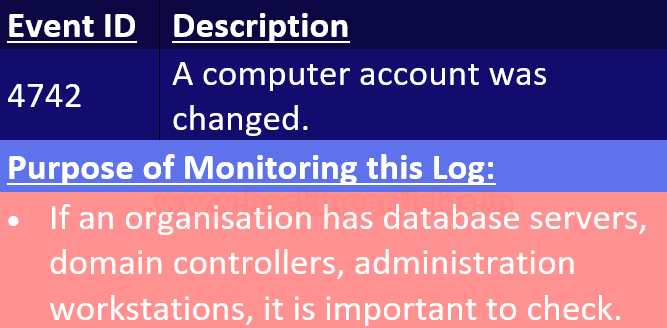
When any changes are made to the computer account, this event is generated.
Event ID 4743

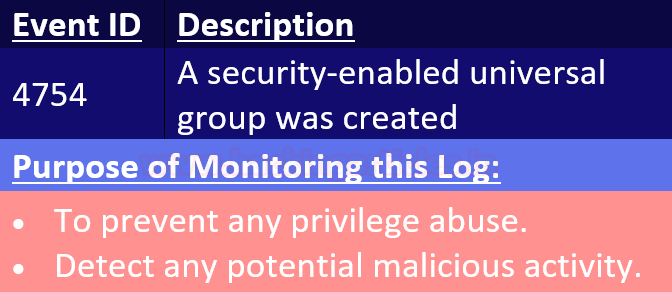
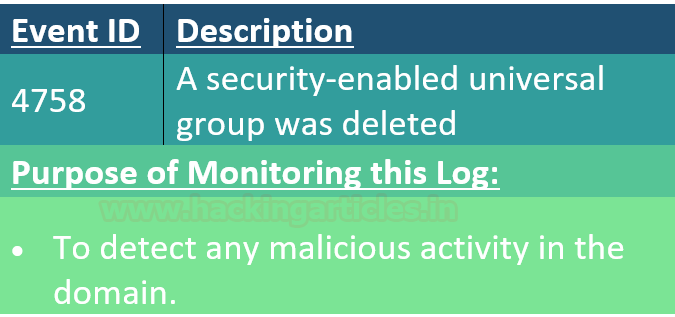
Event ID 4754
When a computer account is deleted, this event is generated.

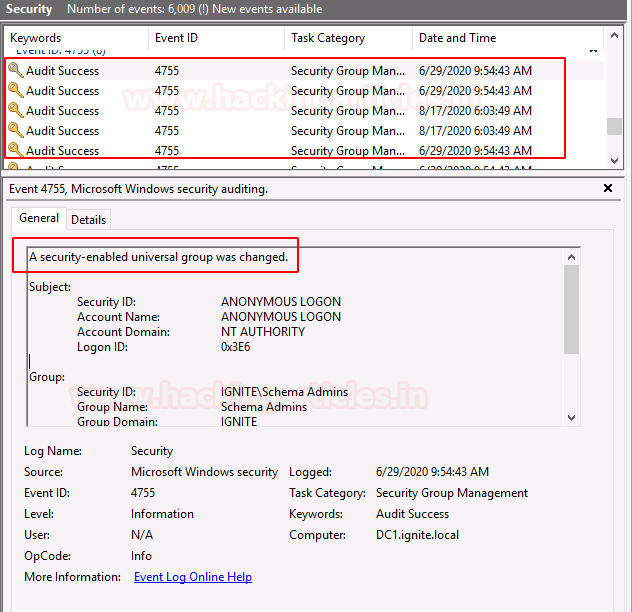
Event ID 4755

The system creates this log when it makes any changes in a security-enabled universal group.
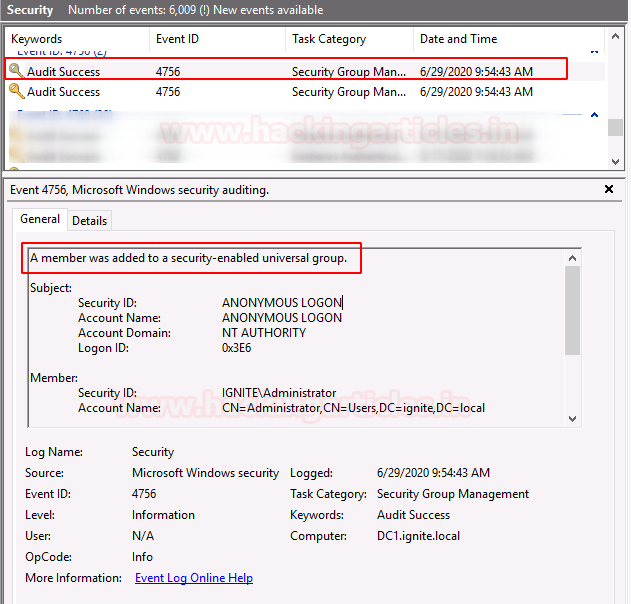
Event ID 4756
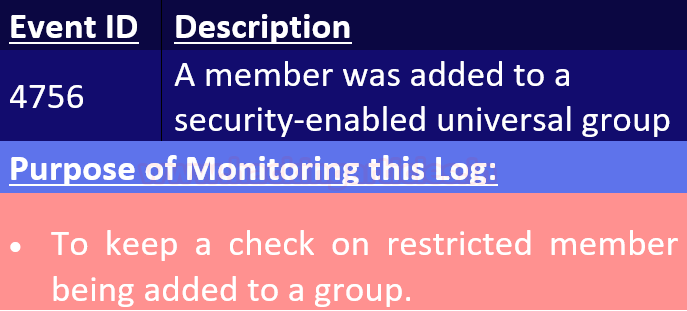
You can add the user to the group using
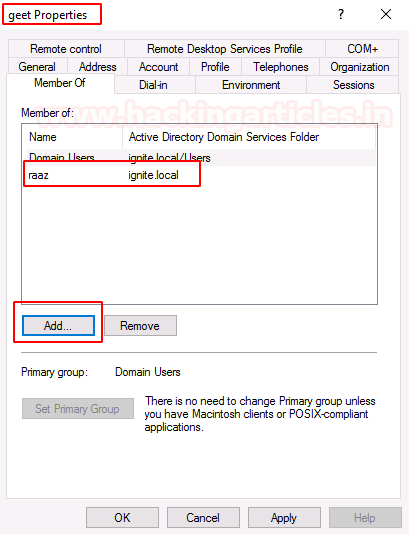
The system creates this event when it adds a new member to a security-enabled universal group.
Event ID 4799

When a member from a group is enumerated, this event will be generated.

You can try out the below event ID using Domain Controller:
Conclusion: Hence, being an incident responder, you can maintain the activity of users using account management event in windows.
Author: Jeenali Kothari is a Digital Forensics enthusiast and enjoys technical content writing. You can reach her on Here