Incident Response: Windows Account Logon and Logon Events
When a user authenticates a Windows endpoint, the system generates an Account Logon event and records it. Meanwhile, the system records these account logon events in its Security event log, which is responsible for authenticates the user.
In addition, when a user accesses an account for a resource, the system records a Logon event. Consequently, the system records these logon events in its own Security event log.
As an incident responder, if you spot account logon events on a machine other than the Domain Controller, it could be a sign of local user account usage.
Local user account usage is abnormal on domain environments and can indicate a compromise
Table of Contents
- Introduction
- Logon Events
- Account Logon Events
- Event ID’s
- Event ID 4624
- Event ID 4625
- Event ID 4634
- Event ID 4647
- Event ID 4648
- Event ID 4672
- Kerberos Authentication Protocol
- Event ID 4768
- Event ID 4769
- Event ID 4776
- Event ID 4778
- Event ID 4779
Introduction
A windows system has various authentication and logon methods to establish remote sessions between different systems over a network. In this article, we will be learning about different account logon events and authentication protocols like Kerberos.
The methods of Windows authentication range from a simple logon-based thing depending on the user’s knowledge like a password, tokens, public key certificates, and biometrics, etc.
An authentication protocol like Kerberos defines rules and conventions and serves the authentication of users, computers, and services. The process of authentication allows an authorized user and services and gives access to resources in a much secure way.
Logon Events
The Audit logon events are usually settings in the policy that records all attempts to log on to the local computer, whether by using a domain account or a local account. Audit Logon/Logoff events generate on the creation and destruction of logon sessions. These events occur on the machine that was accessed.
Account Logon Events
Account Logon policy setting generates events for any type of credential validation. These events occur on the machine that is authoritative for the credentials. For domain accounts, the domain controller is authoritative. For local accounts, the local machine is authoritative.
So, let’s see these event IDs one by one across the Windows server.
Event ID’s
Event ID 4624
This event usually is generated for a successful logon. This event will contain information about the host and the name of the account involved. For remote logons, an incident responder should focus on the Network Information section of the event description for remote host information.
The fields Caller Process Name and Caller Process ID in the Process Information section of this event description provides more details about the process of initiating the logon.

When a user successfully logs on to a computer, this event will be generated.

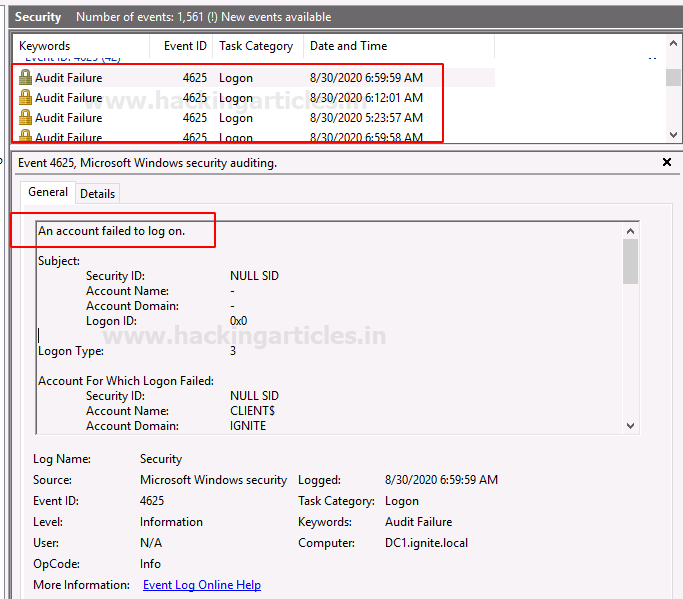
Event ID 4625
This event is created on a failed logon attempt. Usually, these logs in a network may indicate password guessing attacks. The Network Information of this event can provide valuable information if a remote host is attempting to log on to the system.
As an incident responder, you can determine more about the reason for the failure by going through the description.
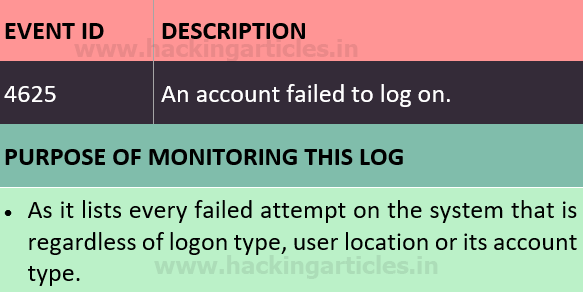
When a user has a failed login attempt on to a computer, this event will be generated.
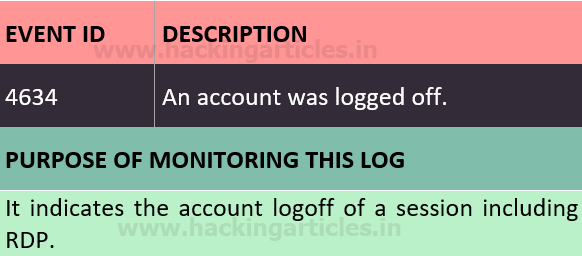
Event ID 4634
When a user logs off from their system, the system records the event with Event ID 4634. Meanwhile, as an incident responder, you should not consider the absence of a logoff event overly suspicious if a system does not show one.

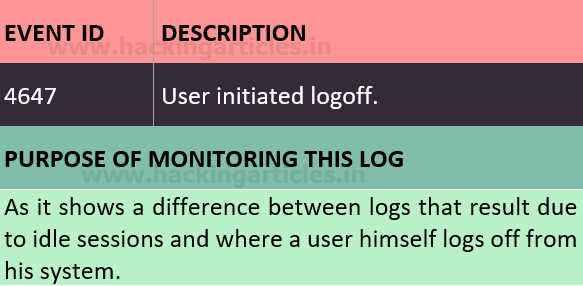
Event ID 4647
This event generates when a user logon is of remote type and the logoff was with some standard method.

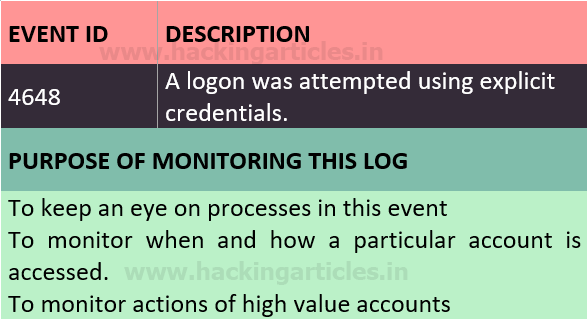
Event ID 4648
A logon was attempted using explicit credentials. When a user attempts to use credentials that are of other than his, or if there is a user account control bypass to open a process with administrator permissions, this event is logged.

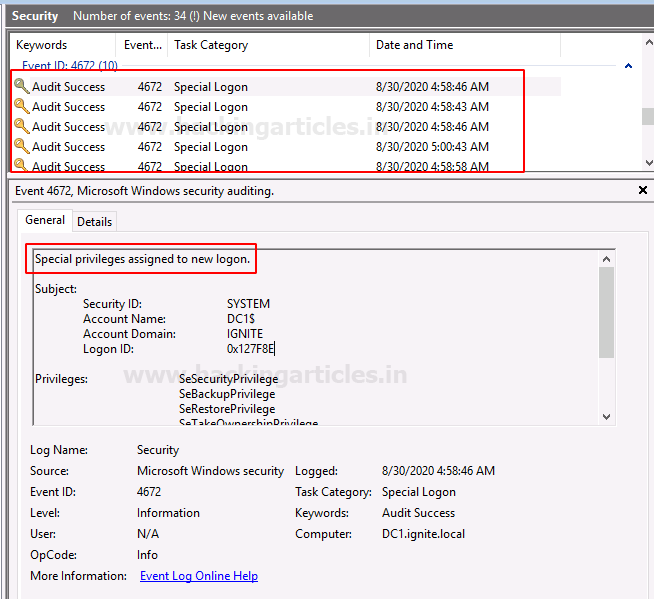
Event ID 4672
When a set of sensitive privileges are assigned to a new logon session, this event is generated for that particular new logon. This event is usually recorded in the event viewer as and when a single local system account logon triggers this event.

Kerberos Authentication Protocol
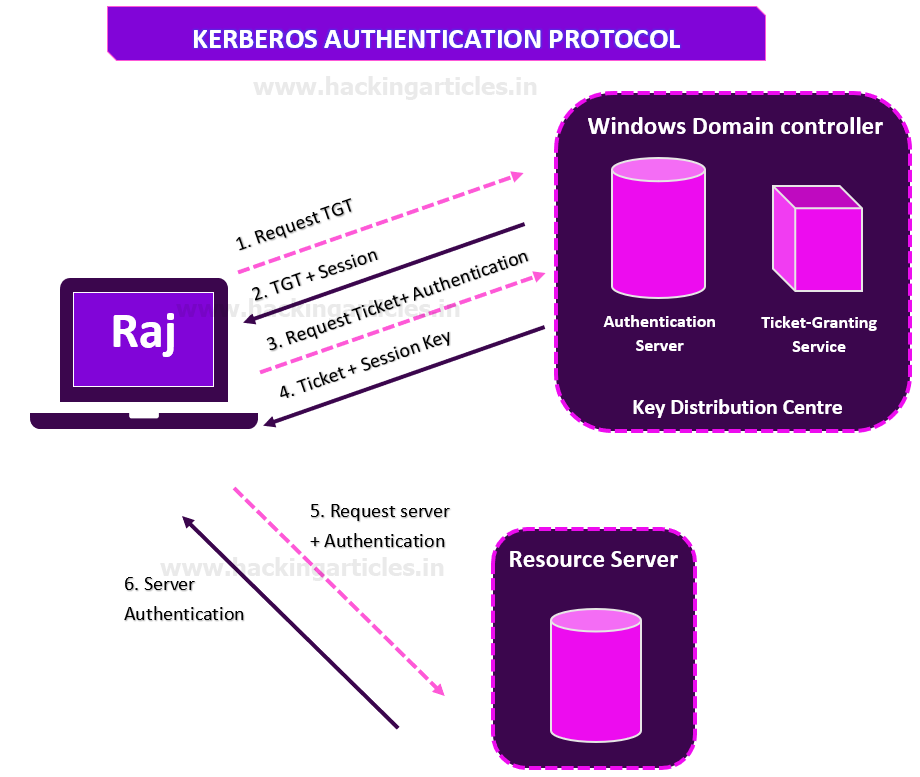
Kerberos is an authentication protocol that works on the basis of tickets that allows the nodes to communicate over a non-secure network to prove their identity to each other in a secure manner.
So, let us understand the basics of Kerberos and then go ahead with Kerberos authentication protocol and the proceed with the event logs.
Client: A user that requests communication service request.
Resource Server: The server with the service the user wants to access.
Authentication Sever: It performs client authentication, issues TGS on successful authentication.
Key Distribution Centre: Database, Authentication Server and Ticket Granting Server collectively is called Key Distribution Centre.
Ticket Granting Server: It is an application server that provides the issuing of service tickets as a service.
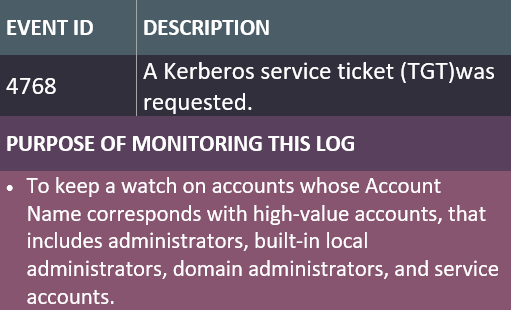
Event ID 4768
On successful issuance of a TGT, it will show that a user account was authenticated by the domain controller. The Keywords field would indicate whether the authentication attempt was successful or failed.

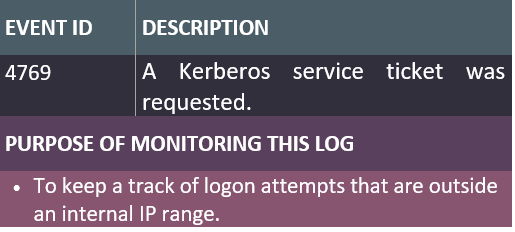
Event ID 4769
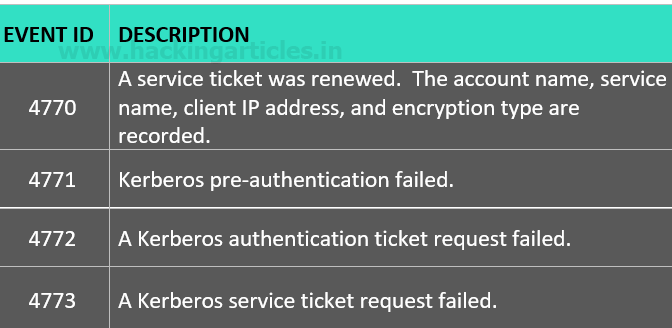
Once the client successfully receives a ticket-granting ticket from the KDC, it will store that TGT and send it to the TGS with the Service Principal Name (SPN) of the resource that the client wants to access. TGTs are valid for a certain period of time only.
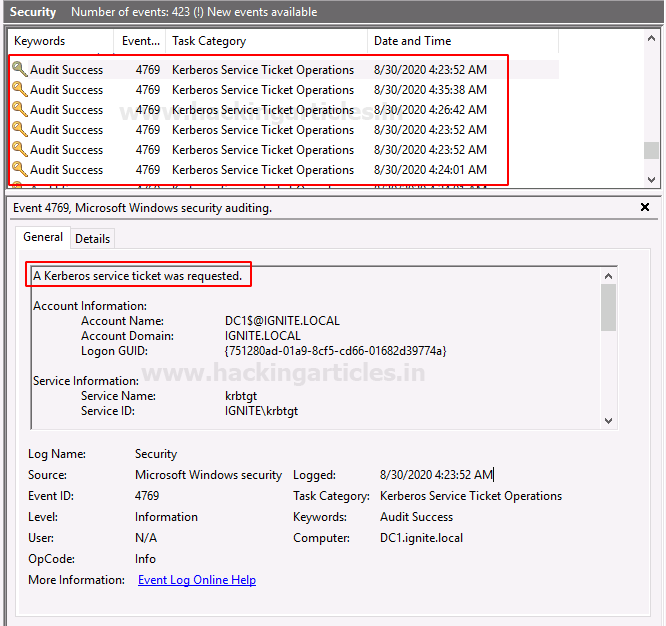
Event ID 4776
When the computer logon is to be verified, this even is created. It contains additional information about the remote host in the event of a remote logon attempt. The Keywords field indicates whether the authentication attempt succeeded or failed

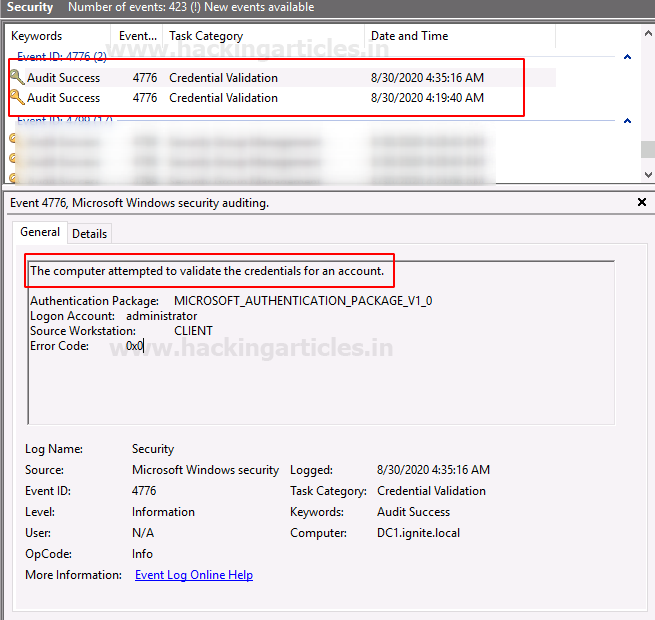
Event ID 4778
Furthermore, the system creates this event when a user reconnects a session to a Windows station. For instance, the user triggers event 4778 by reconnecting to an existing Terminal Services session, or by switching to an existing desktop using Fast User Switching. Similarly, the user also triggers this event by reconnecting to a virtual host.

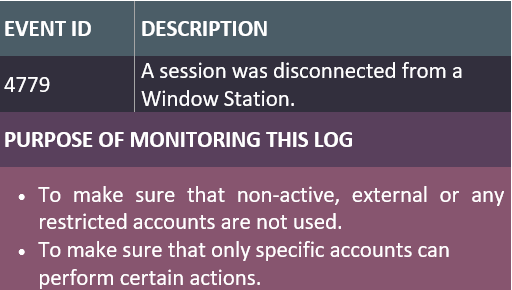
Event ID 4779
Moreover, the system generates this event when a user disconnects from an existing Terminal Services session, or switches away from an existing desktop using Fast User Switching. Additionally, the user causes this event to be created by disconnecting from a virtual host.

You can also try out some other event ID’s from below.
To learn more on Incident Response follow this Link.
Author: Jeenali Kothari is a Digital Forensics enthusiast and enjoys technical content writing. You can reach her on Here
Very useful contents
Very good