Credential Dumping: Windows Autologon Password
Autologon helps you to conveniently customize the built-in Autologon mechanism for Windows. Rather than waiting for a user to enter their name and password, Windows will automatically log in the required user. It does this using the credentials you submit with Autologon. These credentials are encrypted and stored in the registry.
In this guide, we explore Windows Autologon Password Dumping, a technique used to retrieve stored autologon credentials from the Windows registry. By leveraging tools like Nirsoft’s Network Password Recovery and DecryptAutologon.exe, security professionals can extract these credentials for analysis. This process is crucial for understanding potential vulnerabilities in systems where autologon is enabled.
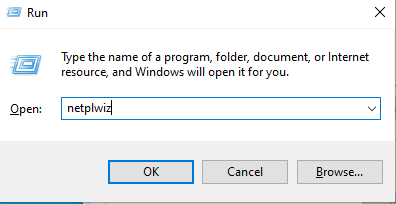
Let’s see the settings for autologin, first, you need to access the User Accounts Control Panel using netplwiz command inside the run prompt.
Choose the account for autologon. For example, we have selected the user Raj.

Enter your password once, and then enter it again to confirm. After that, uncheck the box labeled “Users must enter a user name and password to use this computer.” Finally, click OK.

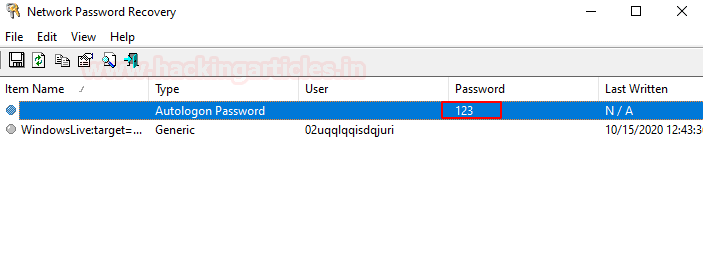
Method 1: Nirsoft-Network Password Recovery
Network Password Recovery is very easy to use, install and run the tool on the local machine whose password you chose to extract. It will dump the stored credential for the autologon account.
You can download this tool from here
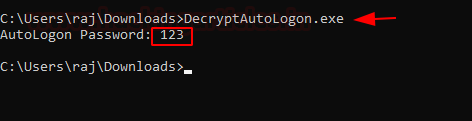
Method 2: DecryptAutologon.exe
This tool extracts and decrypts the password stored in the LSA by SysInternals AutoLogo.
You can download its Compiled Version HERE
Run the downloaded .exe as shown in the given image, it will dump the password in the Plain text.
In summary, understanding Windows Autologon Password Dumping is essential. It helps identify potential credential storage risks in Windows systems. By using tools like Nirsoft and DecryptAutologon, security professionals and penetration testers can effectively uncover stored autologon credentials, enhancing their ability to assess system vulnerabilities.
For more articles on Credential Dumping. Follow this: Link
Author: Vishva Vaghela is a Digital Forensics enthusiast and enjoys technical content writing. You can reach her on Here
Hi, I really appreciate and want to thank you for your posts. I really learn a lot about your posts and want to specifically want to ask you to keep posting as I learn a lot about them. As a Director and Founder of my Company a Cyber and Digital Forensics Company in my country South Africa, I says THANK YOU