Wireless Penetration Testing: Fern
Fern is a Python-based Wi-Fi cracker tool used for security auditing purposes. The program is able to crack and recover WEP/WPA/WPS keys and also run other network-based attacks on wireless or Ethernet-based networks. The tool is available both as open source and a premium model of the free version. In this article, we’ll be demonstrating a WPA dictionary attack using the open-source version. You can check the link to download it here.
Launching the Tool and Setting Up the Interface
The first step is to launch the tool. If you have installed all of the requirements mentioned, you’ll be able to see the following screen.

Now, here in the first option, the user can select the wireless interface from the drop-down menu. Here, we have selected the Wlan0 interface. As you can see that fern here has automatically put the Wlan0 interface on monitor mode.
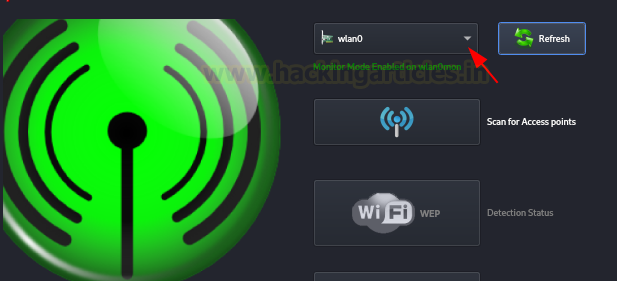
Monitor Mode: NIC cards typically capture only the packets destined for a specific device. However, in monitor mode, Wi-Fi adapters capture Wi-Fi management, data, and control packets without needing to associate with the access point first. Hence, we can understand that wireless adapters in monitor mode capture raw pcap files. These files can then be used for auditing and/or hacking purposes.
Scanning for Access Points and Launching the Attack
Once we have chosen the interface, we’ll need to scan for access points now.

Here, observe that we have scanned a total of 18 access points.
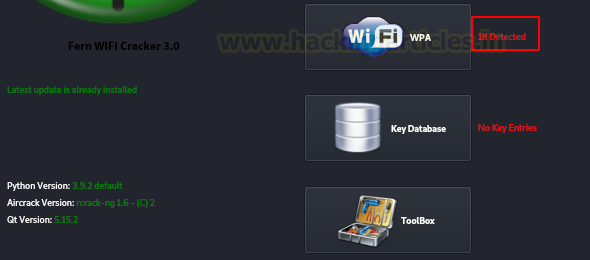
Access Point: It is a device that sends out wireless signals. Essentially the internet connection from a router runs down to an access point and allows users to access the internet using IEEE 802.11 protocol (commonly known as Wi-Fi). In our day to day usage scenario, we have a Wi-Fi router set up at home which also serves as a wireless access point.
SSID: Service Set Identifier is the name given to an access point for simplicity.
Launching the attack: Now we can click on the discovered access point, choose a dictionary file and click on launch attack with our chosen dictionary. It is that simple! As you can see that we have a matched credential and received the SSID password down below.

Please note that this program is only able to crack WPA/WEP/WPS keys. For tools that work on stronger encryption, like WPA2, please refer to the latest article on wireless penetration testing on Hacking Articles. Thanks for reading.
To learn more about Wireless Penetration Testing. Follow this Link.
Author: Harshit Rajpal is an InfoSec researcher and a left and right brain thinker. Contact here