Windows Privilege Escalation: DnsAdmins to DomainAdmin
In this article, we will show how attackers can escalate privileges from DNSAdmins to Domain Admin in Windows environments and gain unauthorized access. We will show you a method for escalating privileges on Windows-based Devices when they contain a compromised user of the DnsAdmins Group.
Table of Content
- Introduction
- Setting Up
- Enumeration
- Exploitation
- Indicator of Compromise
- Conclusion
Introduction
In our long series in search for methods to elevate privileges on Windows Devices. Today, we look at DNSAdmins. To be able to understand this, you need to understand the implementation of DNS on Windows by Microsoft. The Microsoft Team designing DNS integration decided to make the Domain Controller a DNS server by default. To manage that DNS service, a group named DnsAdmins is used. Then came the ability for the users of DnsAdmins to run code with elevated privileges, which, in their eyes, was a feature.
The DNS Management protocol operates on top of RPC. You can find an executable named dns.exe under C:\Windows\System32\ on Domain Controllers. On the Domain Controller, the DNS server essentially runs as a server.
Additionally, like every service, you can manage the DNS server using an interface available at dnsmgmt.msc. If you search for all the operations that the server needs to support, you will come across R_DnssrvOperation. This function contains the pszOperation parameter.
This parameter allows users who are part of the DnsAdmins group to load a DLL without monitoring for content. As a result, DnsAdmins users can execute this DLL with elevated privileges, which makes them vulnerable to Privilege Escalation.
Setting Up
To set up the conditions in our local environment for able to test the possibility of privilege escalation, we need to create a user. Then add that particular user to the DNSAdmins group. In the demonstration, we have a domain controller that is all set up with a bunch of devices and users connected to it. We take the Jeenali user and select the Add to a group option from the drop-down menu.

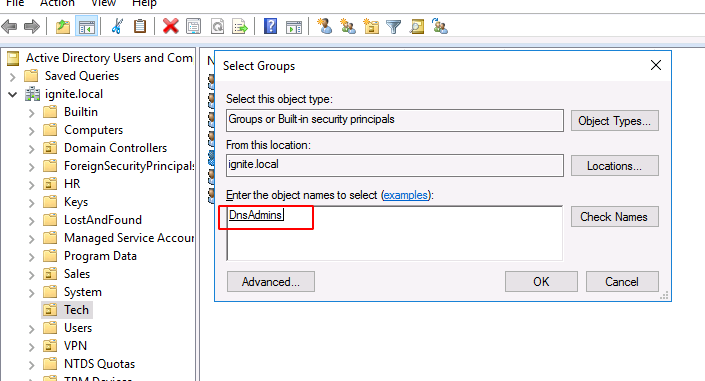
Clicking on Add to a group will open a new window that can enable the user to select the group they want to add their user to. Type in DnsAdmins in the Enter the object names to select field and click on Check names option. When It gets underlined as demonstrated, click on the OK button to add the user to that group.
Enumeration/Detection
The setup is complete with the jeenali user being a member of the DnsAdmins group. To verify in this case or case we do this demonstration from an attacker perspective to understand what would be the indicators that will point towards and the process through which the attacker would figure out if the target is vulnerable to this kind of privilege escalation. We connect to the jeenali user. We assume that the attacker has control or credentials for this user. After establishing a connection through Evil-WinRM we use the whoami command with the group parameter to enumerate for the groups that the current user i.e., belong to. We see that the jeenali user is a part of the DnsAdmins group. This verifies the setup we did earlier.

Exploitation
From the introduction, we know that the member of the DnsAdmins group can run the DLL file with elevated privileges. To exploit that privilege, we need to craft a malicious DLL file. We will be using msfvenom with the shell_reverse_tcp payload. We name the file raj.dll. The file we created is on our Kali machine. We use the smbserver.py python script from Impacket to host the /root directory as demonstrated below.

There are multiple ways to transfer the file to the target system. But there is always a chance that any Malware Scanner or Defender will detect the file and either quarantine it or remove it. Hence, we are hosting it on the smb server that makes it available for the Windows machine, and then we will directly interact with the DDL over the network. The executable we will use to pass the DLL code into the memory as SYSTEM is called dnscmd.exe. With the config and serverlevelplugindll parameters, we will pass the path of the DLL over the network as demonstrated below.

On the Kali machine on the SMB Server, it can be observed that a connection was made from the Domain Controller.

Run netcat and transfer the DLL file
At this stage, the attacker needs to perform two specific tasks to get the shell. First, the attacker must run a netcat listener on a new terminal using the same port mentioned while crafting the payload. Secondly, the attacker transfers the DLL file but does not execute it immediately. To inject the DLL into memory, the attacker restarts the DNS Service.

As soon as the attacker restarts the service, the netcat listener establishes a new connection. After the attacker runs the whoami command, they can confirm that the session generated is as Administrator and not as the Jeenali user. This also confirms that the DLL executes as SYSTEM when the user is a member of the DnsAdmins group.

Indicator of Compromise
Additionally, when the attacker performs this method, there is an indicator that can help identify the incident. During the attack, if the attacker runs the dnscmd.exe command. It creates an entry in the registry of the target machine. The defender can then check this registry entry to obtain the IP address from which the attacker launched the attack and the DLL file used for the compromise.
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\DNS\Parameters\ServerLevelPluginDll

Conclusion
This article/demonstration presents the attacker with an opportunity to escalate their access after the initial foothold. Being a member of a group can provide direct exploitation of the SYSTEM. Hence, from Blue Teamer’s perspective, it is advised to always authorize proper permissions and make sure the users are not assigned groups that they are not supposed to access. Also, treat the DnsAdmins group with the same attention as the Administrator group.
Learn more about Windows Privilege Escalation from this Link.
Source: https://medium.com/@esnesenon/feature-not-bug-dnsadmin-to-dc-compromise-in-one-line-a0f779b8dc83
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester. Can be Contacted on Twitter and LinkedIn