Nmap for Pentester: Ping Scan
In this article we are going to scan the target machine with different Nmap ping scans and the response packets of different scans can be confirmed by analysis of Nmap traffic through Wireshark.
Ping scan in nmap is done to check if the target host is alive or not. As we know that ping by default send the ICMP echo request and gets an ICMP echo reply if the system is alive. Ping scan by default send an ARP packet and gets a response to check if the host is up.
Nmap scans changes their behavior according to the network they are scanning.
- Scanning Local Network with Nmap where nmap sends an ARP packet with every scan
- If an external network is to be scanned; Nmap sends following request packets:
- ICMP echo request
- ICMP timestamp request
- TCP SYN to port 443
- TCP ACK to port 80
In this article we are using —disable-arp-ping attribute for changing the behavior of nmap scans to treat a local network as a public network.
Let’s Start!!
Ping Sweep
In order to identify live host without using ARP request packet Nmap utilize –sP option which is known as Ping Sweep Scan. We can use –sn flag which means no port scan also known as ping scan.
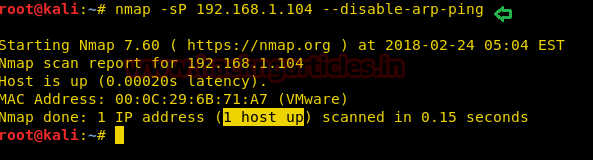
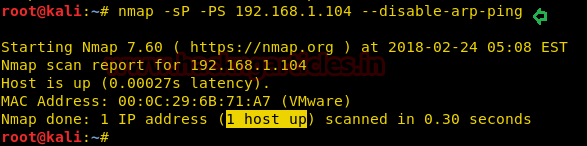
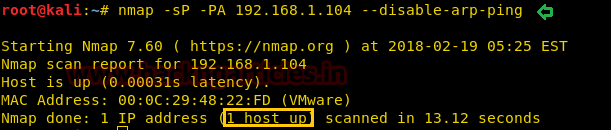
nmap -sP 192.168.1.104 --disable-arp-ping or nmap -sn 192.168.1.104 --disable-arp-ping
From given below image you can observe it found 1 Host is up. Since we have disabled Arp request packet for local network scans by using parameter –disable-arp-ping therefore here it will treat it as an external network and behave accordingly that as discussed above.
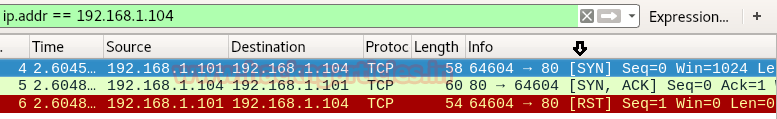
Demonstrating working of Ping Sweep using Wireshark
From given below image you can observer following packet of request and reply between both network IP
- ICMP echo request
- TCP SYN to port 443
- TCP ACK to port 80
- ICMP timestamp request
- ICMP echo reply
- TCP RST, ACK to port 443
- TCP RST to port 80
- ICMP Timestamp Reply

Block Ping Sweep Scan
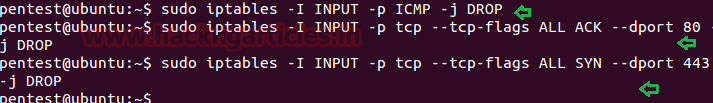
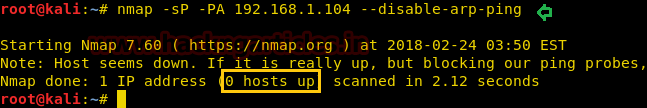
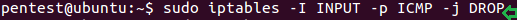
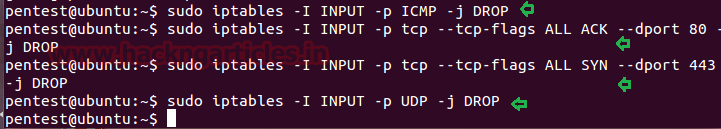
Now let’s put some firewall rules in IPTABLES to drop ICMP packets, TCP SYN packets on port 443 and TCP ACK on port 80 which will block Ping Sweep scan
sudo iptables -I INPUT -p ICMP -j DROP sudo iptables -I INPUT -p tcp --tcp-flags ALL ACK --dport 80 -j DROP sudo iptables -I INPUT -p tcp --tcp-flags ALL SYN --dport 443 -j DROP
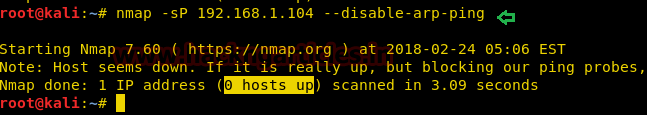
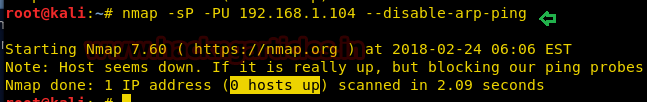
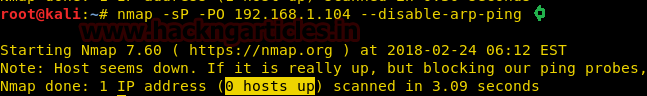
Now repeat again ping sweep scan for identifying the state of the live host. From given below image you can observe this time it shows that 0 host is up which means the firewall has blocked packets send by this scan.
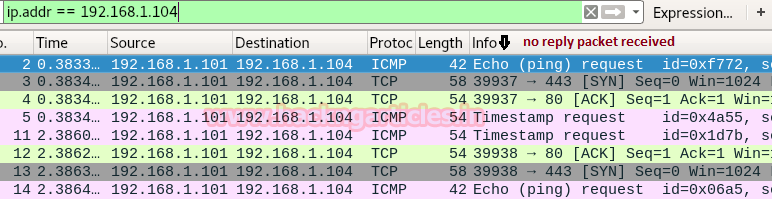
Again demonstrating request packets of Ping Sweep scan with Wireshark and if you notice given below image then you will found that this time it has not received any reply packet.
Bypass Ping Sweep Filter using TCP SYN Ping
Now, we’ll try to bypass the firewall rules by using ping scan with TCP SYN packets, for that we’ll use –PS attribute. –PS sends TCP SYN packet on port 80 by default; we can change it by specifying the ports with it, like -PS443.
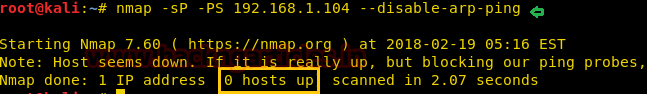
nmap -sP -PS 192.168.1.104 --disable-arp-ping
From given below image you can observe that observe it found 1 Host is up.
From given below image you can observe that it is showing the result which similar to NMAP stealth scan. Here it is following TCP Half connection mechanism where SYN packet is sent on port 80 and received SYN, ACK from port 80 and then RST packet for reset connection
The difference between –sP packet on port 80 and –PS packet on port 80 is as following:
- Ping sweep scan [-sP] send TCP ACK packet on port 80 and hex value of ACK flag is 10, as the reply from host machine it receives RST packet whose hex value is 4.
- TCP SYN Ping scan send TCP SYN packet on port 80 and its hex value is 2, as a reply it received SYN, ACK packet whose value is some of their hex value i.e. 2 + 10 = 12 and able to bypass above firewall rule applied on port 80 for TCK ACK packet.
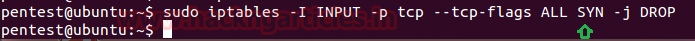
Block TCP SYN Ping Scan
Sometimes network admin applies the filter as given below using Iptables on TCP SYN packet to drop all SYN packet to initiate TCP connection with all TCP Port in their network.
sudo iptables -I INPUT -p tcp --tcp-flags ALL SYN -j DROP
As result, it blocks the NMAP TCP SYN Ping probes so that it could not identify the state of the live host.
Now repeat again TCP SYN Ping for identifying the state of the live host. From given below image you can observe this time it shows that 0 host is up which means the firewall has blocked packets send by this scan.
Bypass TCP SYN Ping using TCP ACK Ping
In order to bypass this, we’ll use ping scan using TCP ACK packets, for that we’ll use –PA attribute. –PA sends TCP ACK packet on port 80 by default, we can change it by specifying the ports with it, like -PA443
nmap -sP -PA 192.168.1.104 --disable-arp-ping
From given below image you can observe that it has found 1 Host is up.
When you will notice given below packets captured by Wireshark you will found that here ACK packet is sent on port 80 as reply received RST packet from port 80.

Block TCP ACK Ping Scan
Sometimes network admin applies the filter as given below using iptables on TCP ACK packet to drop all ACK packet to established TCP connection with all TCP Port in their network.
sudo iptables -I INPUT -p tcp --tcp-flags ALL ACK -j DROP
As result, it blocks the NMAP TCP ACK Ping probes so that it could not identify the state of the live host.

Now repeat again TCP ACK Ping for identifying the state of the live host. From given below image you can observe this time it shows that 0 host is up which means the firewall has blocked packets send by this scan.
Bypass TCP ACK Ping using ICMP Echo
In some scenarios network, admin apply firewall filter on TCP flag to resist unwanted TCP communication in the network, here let’s consider that network admin had blocked TCP communication by applying the filter on SYN as well on ACK flag.
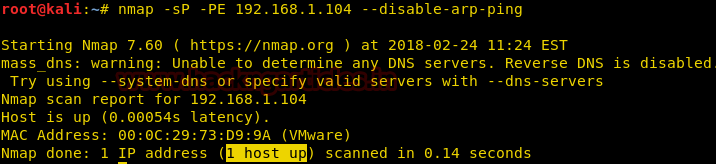
In order to bypass this rule, we’ll use ping scan with ICMP packets, for that we’ll use –PE attribute. –PE sends ICMP echo request packet [ICMP type 8] and received ICMP echo reply packet [ICMP type 0].
nmap -sP -PE 192.168.1.104 --disable-arp-ping
From given below image you can observe that observe it found 1 Host is up.
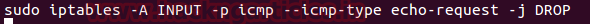
Block ICMP Echo Ping Scan
Usually, most of the network admin apply ICMP filter on their network so that other system or network cannot able to Ping their network.
sudo iptables -A INPUT -p icmp --icmp-type echo-request -j DROP
As result, it blocks the NMAP ICMP echo Ping probes so that it could not identify the state of the live host.
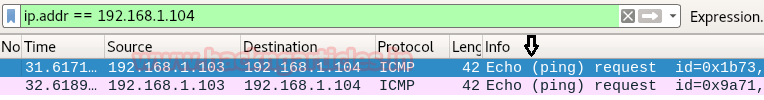
Now repeat again TCP ICMP Ping for identifying the state of the live host. From given below image you can observe this time it shows that 0 host is up which means the firewall has blocked packets send by this scan.
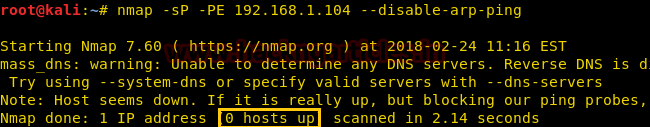
Demonstrating NMAP ICMP echo Ping with Wireshark shows only ICMP request packet in the network and didn’t receive any reply packet from the host network as shown in the given below image.
Bypass ICMP Echo Ping using ICMP Timestamp Ping
In order to bypass this rule, we’ll use ping scan with ICMP packets, for that we’ll use –PP attribute. –PP sends ICMP timestamp request packet [ICMP type 13] and received ICMP timestamp reply packet [ICMP type 14].
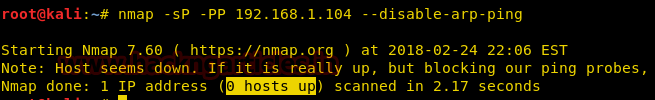
nmap -sP -PP 192.168.1.104 --disable-arp-ping
From given below image you can observe that observe it found 1 Host is up.
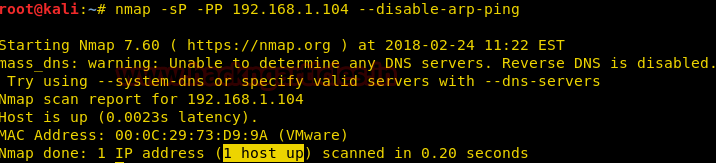
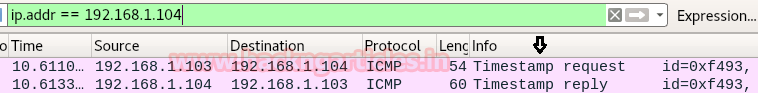
Demonstrating NMAP ICMP timestamp Ping with Wireshark shows ICMP timestamp request packet send in the network and received any timestamp reply packet from host network as shown in given below image.
Block ICMP Ping Scan
It might be possible that network admin had block entire types ICMP message by dropping all ICMP packets using following iptables filter.
sudo iptables -I INPUT -p ICMP -j DROP
As result, it blocks the NMAP ICMP Ping probes so that it could not identify the state of the live host.
Now repeat again ICMP Ping either –PP or PE for identifying the state of the live host. From given below image you can observe this time it shows that 0 host is up which means the firewall has blocked packets send by this scan.
Bypass ICMP Ping Scan using UDP Ping
We have seen multiple ways to check if the system is live. Now, you can determine whether a system is up or not whether it is on the local network or public network.
We had observed that ping scan with ICMP ping is not working or even if TCP packet filter is also enabled in host network then it becomes difficult to identify the live host, now to bypass such types of rules we’ll use ping scan with UDP packets, for that we’ll use –PU attribute.
–PU sends UDP packet when no ports are specified, the default is 40125, a reply received ICMP message such as “ICMP destination unreachable” which means the host is live.
nmap -sP -PU 192.168.1.104 --disable-arp-ping
From given below image you can observe that observe it found 1 Host is up.
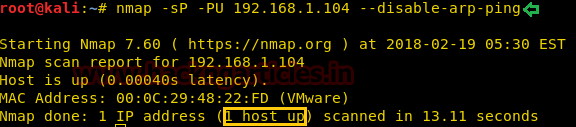
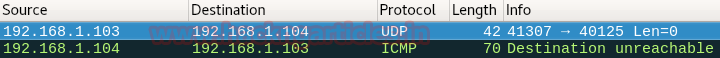
Demonstrating NMAP UDP Ping with Wireshark shows UDP request packet sent on 40125 in the network and received ICMP destination unreachable as reply packet from host network as shown in given below image.
Block UDP and Ping Sweep
Now let’s put some firewall rules in IPTABLES to drop ICMP packets, TCP SYN packets on port 443 and TCP ACK on port 80 which will block Ping Sweep scan as well as Drop UDP packet. Might be network admin had blocked entire TCP packet.
sudo iptables -I INPUT -p ICMP -j DROP sudo iptables -I INPUT -p tcp --tcp-flags ALL ACK --dport 80 -j DROP sudo iptables -I INPUT -p tcp --tcp-flags ALL SYN --dport 443 -j DROP sudo iptables -I INPUT -p UDP -j DROP
As result, it will resist NMAP for making TCP Ping, ICMP Ping, and UDP ping so that it could not identify the state of the live host.
Now repeat again UDP Ping for identifying the state of the live host. From given below image you can observe this time it shows that 0 host is up which means the firewall has blocked packets send by this scan.
Bypass UDP and Ping Sweep using Protocol Scan
Using Protocol Ping scan we can identify live host when ICMP, TCP, and UDP has been blocked, for that we’ll use –PO attribute. –PO sends IP packet with the particular protocol number place in their IP header, If no protocols are precise, the default is to send multiple IP packets for ICMP (protocol 1), IGMP (protocol 2), and IP-in-IP (protocol 4).
nmap -sP -PO 192.168.1.104 --disable-arp-ping
From given below image you can observe that observe it found 1 Host is up.

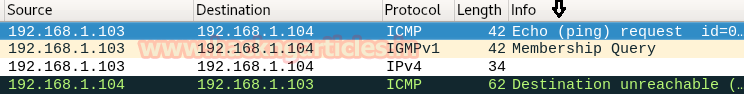
From given below image of Wireshark we can observe the following mechanism followed by Protocol ping scan.
- Send ICMP Echo to host network
- Send IGMP query to host network
- Send IPv4 (IP-in-IP) to host network
- Received ICMP Destination unreachable as the reply from Host
Block IP Protocol Ping Scan
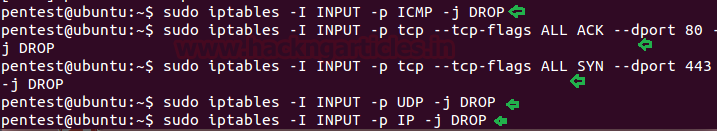
Now let’s put some firewall rules in iptables to drop ICMP packets, TCP SYN packets on port 443 and TCP ACK on port 80 which will block Ping Sweep scan as well as Drop UDP packet and IP protocol too in the network to prevent the network from any kind of Ping scan. Might be network admin had blocked entire TCP packet.
sudo iptables -I INPUT -p ICMP -j DROP sudo iptables -I INPUT -p tcp --tcp-flags ALL ACK --dport 80 -j DROP sudo iptables -I INPUT -p tcp --tcp-flags ALL SYN --dport 443 -j DROP sudo iptables -I INPUT -p UDP -j DROP sudo iptables -I INPUT -p IP -j DROP
As result, it will resist NMAP for making TCP Ping, ICMP Ping, UDP ping and Protocol ping so that it could not identify the state of the live host.
Now repeat again Protocol Ping for identifying the state of the live host. From given below image you can observe this time it shows that 0 host is up which means the firewall has blocked packets send by this scan.
Bypass IP protocol Ping using No Ping Scan
Now when above all Ping scan get failed to identify the state of Host is up or down then we choose the last and best option “No Ping” for we will use –PN/-P0/-Pn and basically perform TCP port scan for top 1000 ports.
If you want to prevent Port scan and ping scan use sweep ping with no ping as given below to identify the state of the host is up or down.
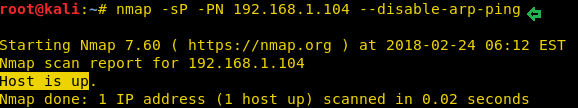
nmap -sP -PN 192.168.1.104 --disable-arp-ping
From given below image you can observe that observe it found 1 Host is up.
Author: Deepanshu is a Certified Ethical Hacker and a budding Security researcher. Contact here.
Good
It’s really a knowledgeable article step by step. Thank you.