Metasploit for Pentester: Clipboard
In this series of articles, we will focus on the various mechanisms of the Metasploit Framework that penetration testers can use. Specifically, we will discuss the External API extension provided by Metasploit, which, among other things, allows attackers to target the clipboard of the target.
Table of Content
- Introduction
- Starting Clipboard Monitoring
- Getting a File from Clipboard
- Dumping Clipboard Data
- Pausing the Clipboard Capture
- Purging Clipboard Capture
- Setting Clipboard Data
- Stopping Clipboard Capture
- Conclusion
Introduction
During the late 2014s, the Metasploit Framework received an update featuring a functionality similar to the OJ TheColonial Reeves Extended API (extapi). Initially, the update targeted Windows systems only. However, developers refined and expanded it over time to include more capabilities.
The update introduced three functionalities.
Service Management: With the help of this, Meterpreter users access a service management interface. This interface allows them to read detailed information about services running on the target, including the startup status and interaction capabilities with the desktop.
Window Management: Using this functionality, users can enumerate all open windows. Consequently, this helps penetration testers determine if the target is worth connecting to via VNC at a particular time.
Clipboard Management: which we will discuss in detail in this post. It allows the attacker to read and write to the target’s clipboard. Moreover, it is not limited to text, as attackers can also download files and images.
To begin the process, we first need to obtain a meterpreter shell on the target machine. After achieving this, we then use the load extapi command to load the External API module into the session, as demonstrated below.
load extapi

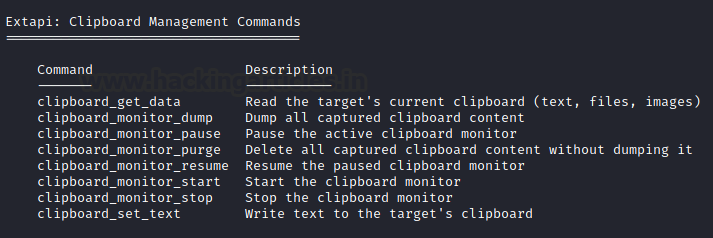
Running the help command generates a list of commands that users can run from the meterpreter shell. In addition to regular commands, the list also includes commands that are part of the Extapi module. Here, we can observe commands for reading the target’s clipboard data, dumping captured clipboard data, initializing, pausing, resuming, terminating clipboard capture, and setting clipboard data on the target.
Starting Clipboard Monitoring
This module does not indefinitely capture clipboard data because the clipboard overwrites itself each time the target copies new data into memory. Consequently, this data can range from plain text to files. Surprisingly, the amount of valuable data obtained from the clipboard can be significant. To initialize the capture process, we simply use the clipboard_monitor_start command.
clipboard_monitor_start

Getting a File from Clipboard
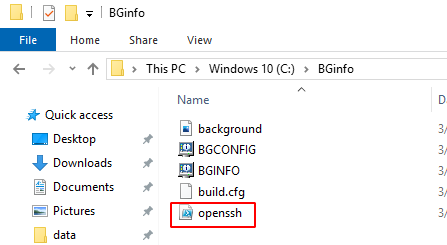
After starting the clipboard monitoring using the command in the previous section, we move to our target machine to stimulate the Copying of files. Here we can see that inside a directory we are copying a PowerShell script file named OpenSSH. It is quite possible that it might contain a key that can be used to connect via SSH service.
Back to our attacker machine to the meterpreter shell. Here, we run the get data command to retrieve the file copied on the clipboard.
clipboard_get_data

Dumping Clipboard Data
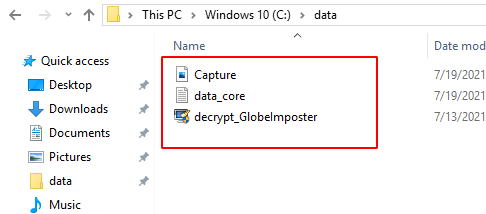
We just grabbed a singular file from the target but what if we want to get multiple files that are copied on its clipboard. To stimulate this, we again get back to the target machine. Here, we see that the target has an image file, text file and an application file inside a directory by the name of data. As the target user, we copied all the files inside the directory.
Back to our attacker machine to the meterpreter shell. Here, we run the dump command to retrieve the files copied on the clipboard. We can see that the OpenSSH file was downloaded again. It is because we initialized the capture earlier, so any files that were copied since then will be retrieved.
clipboard_monitor_dump

Pausing the Clipboard Capture
It is possible to get a large capture that could result in a failure and the amount of data transfer can raise some flags. Hence, it is recommended to pause the capture when you are not actively gathering the clipboard data from the target machine. If you ever want to un pause the capture, use the resume command.
clipboard_monitor_pause

Purging Clipboard Capture
The next command to discover is another that can help while working with the clipboard data. The amount of data captured by the clipboard can be overwhelming or maybe you just want to remove the captured data altogether. In such scenarios, you can use the purge command. In the demonstration, we tried to dump the capture after running the purge and we can see that there is no data in the capture.
clipboard_monitor_purge

Setting Clipboard Data
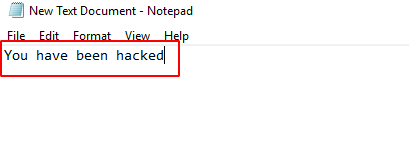
While introducing the clipboard commands, we said that it is possible to set the clipboard of the target machine as well. We need to use the set text command for this task. We take the text that we want to be stored inside the clipboard of the target user and then use it as a parameter between the double quotes as demonstrated in the image below.
clipboard_set_text “You have been hacked”

To stimulate the response from the target end, we move back to the Target machine and open a text editor. Then we paste onto the text editor to find the same text stored inside the clipboard as we set through our attacker machine.
Stopping Clipboard Capture
Similar to the Pausing of the Clipboard. There is a command to stop the capture altogether. The difference between the both is that while Paused capture can be resumed but the stopped cannot be resumed and the data that is captured is not accessible after the fact.
clipboard_monitor_stop

Conclusion
Concluding this article, we can say that this was one of the lesser-known mechanisms of the Metasploit Framework that can be used by any Penetration Tester. We will be discussing about the External API extension provided by Metasploit later.
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester. Can be Contacted on Twitter and LinkedIn