Forensic Investigation of RAW Image using Forensics Explorer (Part 1)
Forensic Explorer is a tool for the analysis of electronic evidence. Primary users of this software are law enforcement, corporate investigations agencies and law firms. Forensic Explorer has the features you expect from the very latest in forensic software. Inclusive with Mount Image Pro, Forensic Explorer will quickly become an important part of your forensic software toolkit.
It enables investigators to:
Manage the analysis of large volumes of information from multiple sources in a case file structure;
- Access and examine all available data, including hidden and system files, deleted files, file and disk slack and unallocated clusters;
- Automate complex investigation tasks;
- Produce detailed reports; and,
- Provide non forensic investigators a platform to easily review evidence.
Supported File Formats
Forensics Explorer supports the analysis of the following file formats:
Apple DMG
- DD or RAW;
- EnCase® (.E01, .L01, Ex01);
- Forensic File Format .AFF
- FTK® (.E01, .AD1 formats);
- ISO (CD and DVD image files);
- Microsoft VHD
- NUIX File Safe MFS01
- ProDiscover®
- SMART®
- VMWare®
- XWays E01 and CTR
Using Forensic Explorer
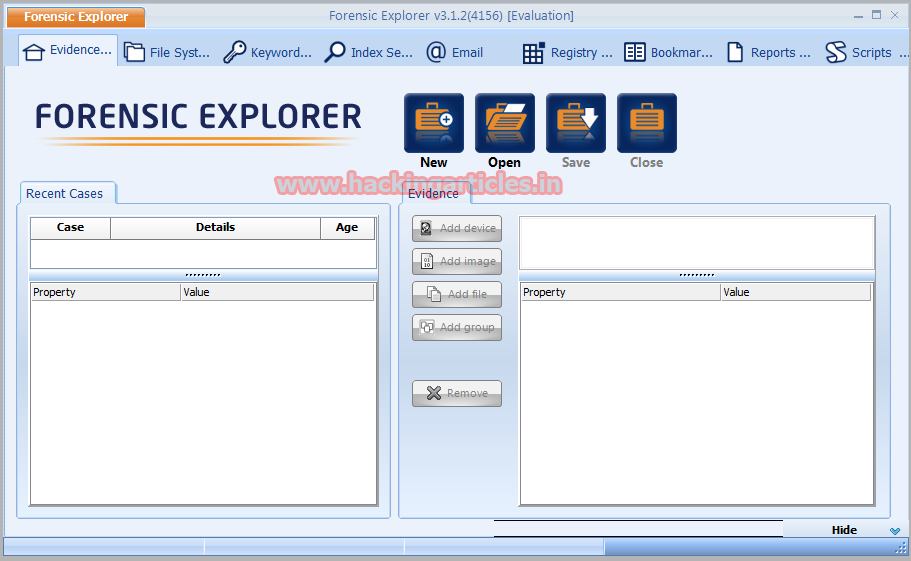
Firstly, Download Forensics Explorer From here and install in your pc. And Click on New Option.
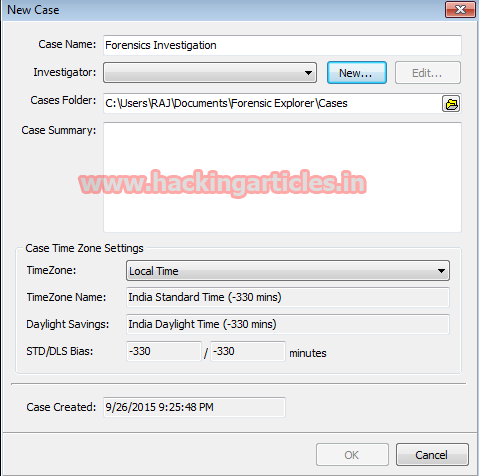
Then, Enter the Case Name and click on new option in Investigator TAB
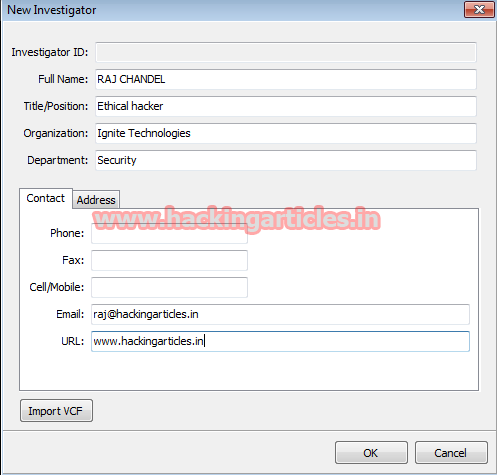
Here in next step you have to enter the FULL NAME, TITLE, and Organization, Department and email details and click on ok to proceed to next step.
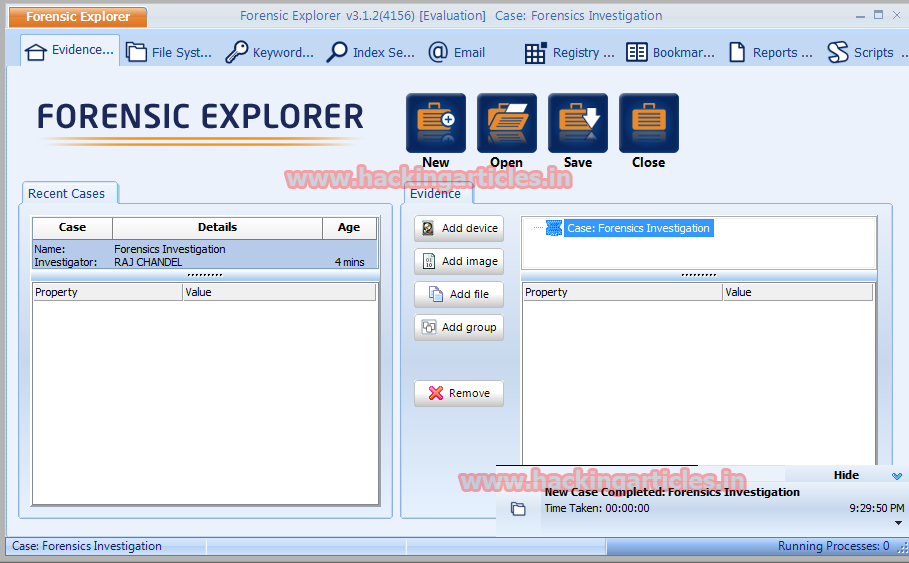
Then, Select the cases folder where Forensic Evidence will be created. And click on ok

Now Click ‘Add Image.
Then, select the path of RAW Image. To create RAW Image Select the given LINK.
http://www.hackingarticles.in/how-to-create-copy-of-suspects-evidence-using-ftk-imager

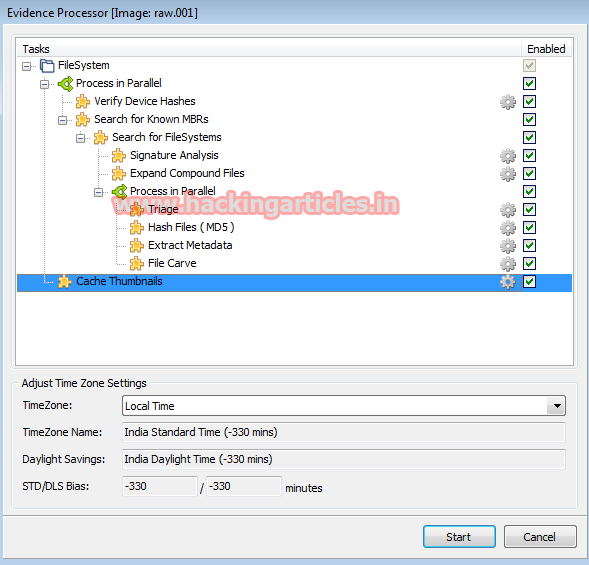
Then, Select tasks to be processed on RAW image from given list and click on Start.
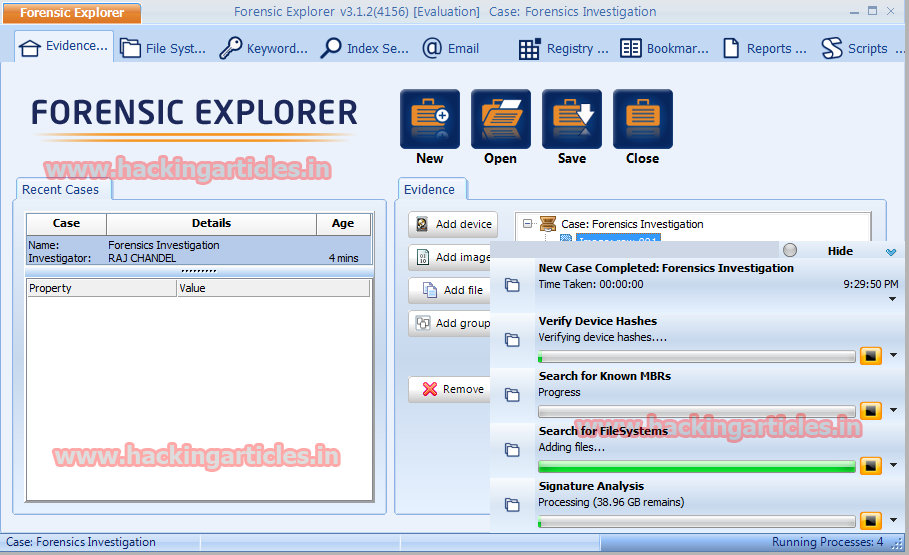
After Process completion, it will show Result for all the tasks selected earlier.
Now Click on File System. The File System module is the primary Forensic Explorer window where actions such as highlighting, selecting, sorting, filtering, flagging, exporting and opening occur.
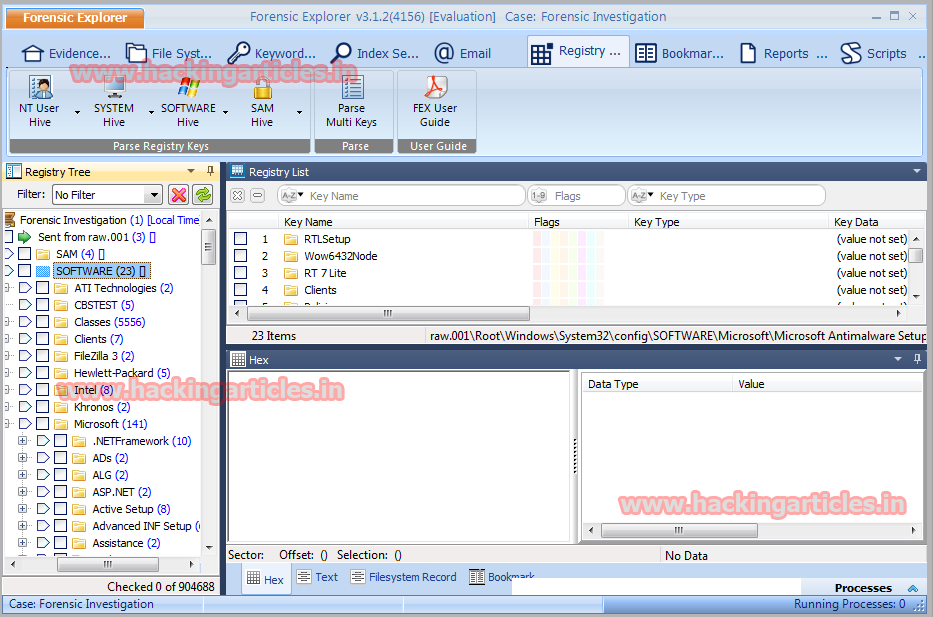
Select Registry analysis
Open and examine Windows registry hives. Filter, categorize and keyword search registry keys. Automate registry analysis with RegEx scripts.
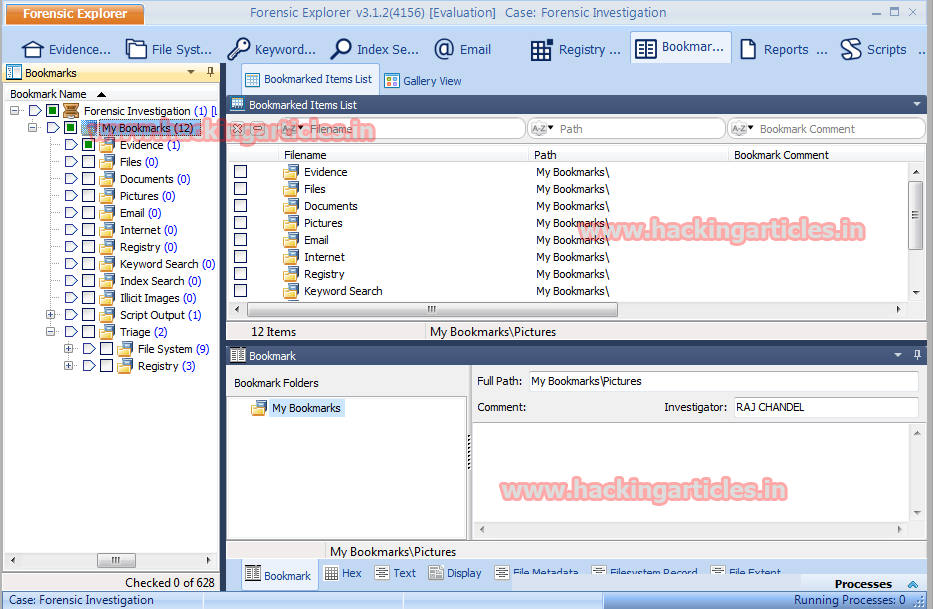
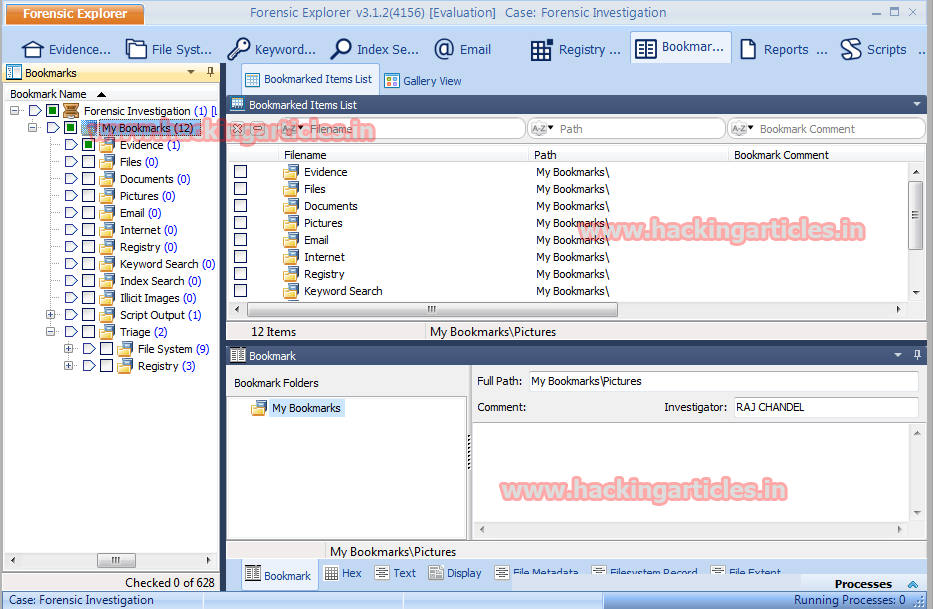
Finally, Bookmark selection enables almost any item (e.g. file, folder, keyword, search hit, etc.), or a selection from an item (e.g. a fragment of text from a file or unallocated clusters), to be bookmarked and listed in the Bookmarks module.
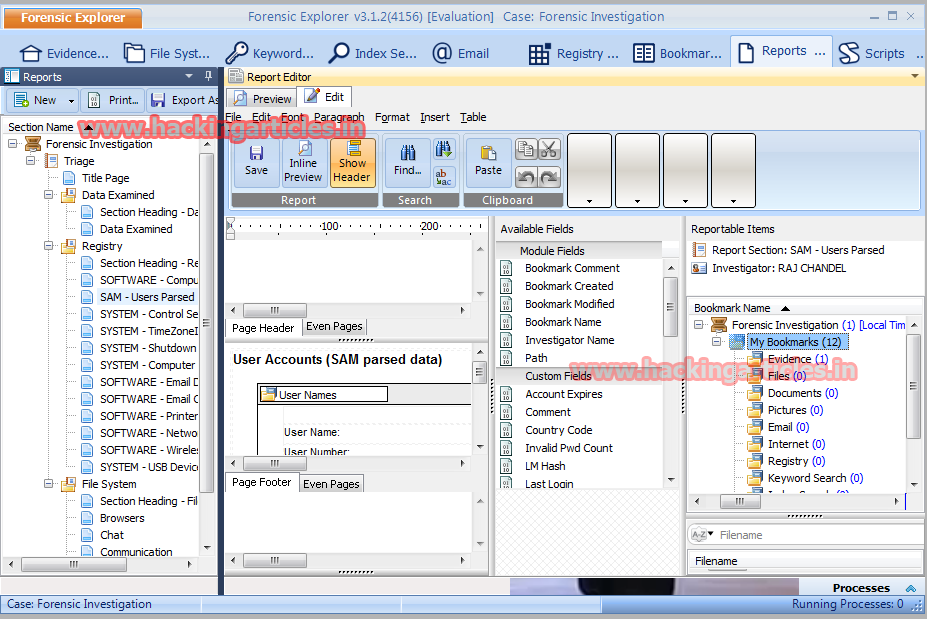
Reports
The purpose of the Reports Module is to assist in the generation of a report that documents the forensic analysis. Furthermore, the Reports module is based on the use of templates that can be re-used across multiple investigations.
To learn more about Cyber Forensics. Follow this Link
Author: Microsoft Certified Mukul Mohan is a messaging and security system engineer.He has extensive experience managing server-side operations using the Windows platform and is a Microsoft Certified Technology Specialist. An expert in IT technical training with more than two decades of technical training. Contact here.