Dradis: Reporting and Collaboration Tool
Hello friends, today in this article we are going to familiarize you with one of the most vital tools of kali that everybody needs in today’s era.
Eliminating bugs or finding any issue, is used to cover by everyone in their journey of pentesting. But apart from this one should also want to indulge ownself into a task that needs to perform in wide range i.e. “report writing”.
Writing a good report is an essential ability, almost an art, for penetration testers, and as for all the skills, can be enhanced through practice. There are many tools that help in report writing but in this tutorial, we are going to use “Dradis”.
Table of content
- Introduction to Report Writing
- What is Dradis?
- Working with Dradis
- Conclusion
Introduction to Report Writing
Penetration testing report is the core deliverable in any security valuation action. In this, the final deliverable is the report which shows the service provided, the methodology used, findings/results and the recommendation. This can be achieved by the use of many tools that kali supports.
Similarly, we are going to cover one such tool in this tutorial i.e. “Dradis”.
What is Dradis?
The Dradis Framework is an open-source collaboration and reporting platform for IT security experts. It is a platform-independent tool developed in Ruby. In other words, we can also say that It is a tool that helps in putting information together in one place. It also tends us the ability to organize all the information in one place. It allows us not only to import but also export output from the various tools that it supports.
Dradis is comprised of a list of a tool like: “Burp scanner, Nessus, NeXpose, Nikto, Nmap, and many more that are pretty common in doing penetration testing or ethical hacking.
Working with Dradis
In the next few steps, we will learn how to use Dradis. For beginning this journey first we need to find Dradis. This can be done by two methods.
First Method:
In this method, we will just write dradis on kali terminal and this will take you to its active status. Once this will be completed then it will take you to its browser for login.
Dradis is a self-contained web application. Hence, it will automatically open in the browser. The URL is https://127.0.0.1:3000.
dradis

Second Method:
For attaining this method you need to Launch the Kali-Linux tool after that Click on “Applications”, go to “Reporting Tools” and click on “Dradis”.

Next step is to create a server password to access the application. Then enter the credentials which we configured for the server.
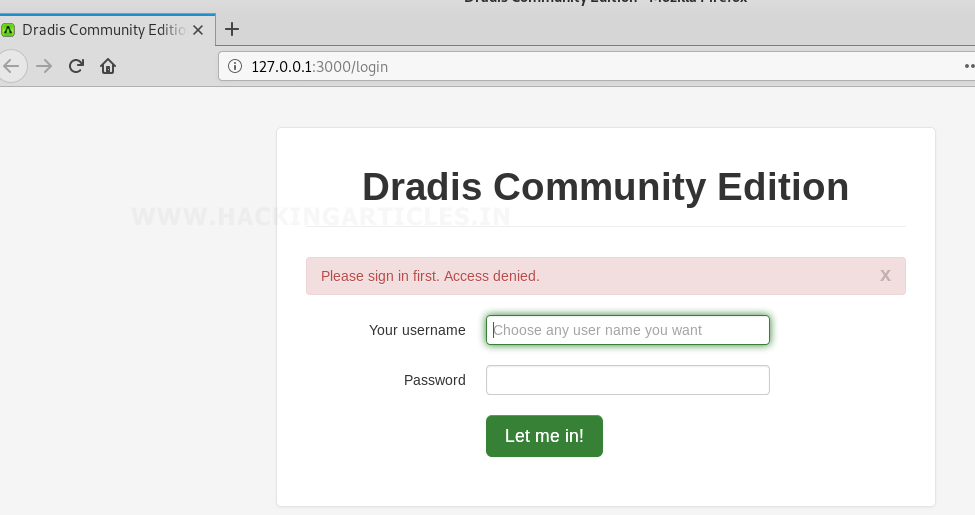
We are logged into the Dradis framework successfully. Now as in below screenshot you can see it’s showing three main operations that can help in any report writing i.e. “all issues, methodologies, trash, nodes” so, we will use all these operations as per the requirement of a task in.

All issues: In this, we have many options like we can add any issue manually, upload output, import result from the library. These options also can help to import the result of any tool in dradis.

Methodologies: When it comes to penetration testing methodologies you can basically narrow the field down to three. These are:
- Open Source Security Testing Methodology Manual (OSSTMM)
- Penetration Testing Execution Standard (PTES)
- National Institute of Standards and Technology
While all three are good methodologies but PTES and NIST 800-115 provide a bit more flexibility during penetration tests. Also, the methodologies more closely align with what’s taught in security course curriculum such as SANS. So whenever we need to add any methodology then we can use this option as reference.

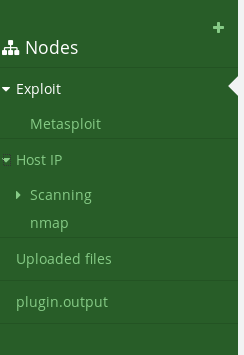
Now, we will start working with dradis. For begin this first we will create a new node by clicking on “nodes” tab after that click on the newly created node and then click the “add subnode” option to add sub-branch under a newly created node. Follow the same process to create multiple node and sub-node as per your requirement.

We can create a tree as per our convenience. In the below screenshot, I have created two main nodes i.e. “Exploit” and “Host IP” which is sub-divided into Metasploit, scanning and nmap. As shown below.
Upload File
After successful completion of creating no. of nodes and sub-nodes now our next step is to upload the output of file with the help of the tool.
For this first, we need to select the name of the tool which we have used. In this, we have used nmap so I will choose this option by using a drop-down button of “choose tool”.

After this, we will search for the file that needs to upload and then click to open button at the top of the screen.

Once the process of uploading the will completed then you can see its output result in its output console as shown in below image.
To view the file, double-click the uploaded image and a new tab will be open in the browser to display the uploaded screenshot.
Similarly, we can upload scan results of other tools like Nessus, Burp, Nikto, Owasp ZAP, etc.
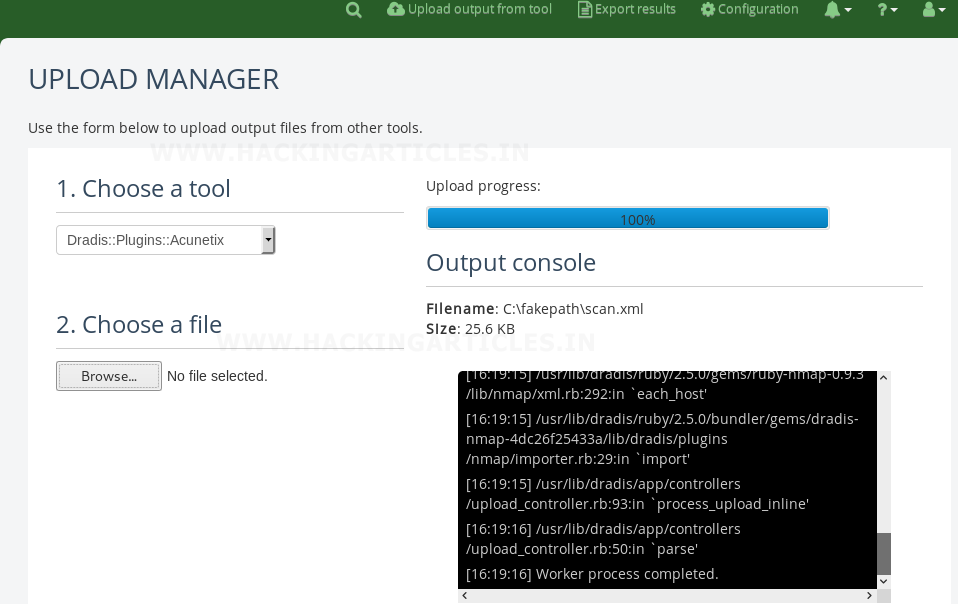
To view entire details of your result you can plugin. output option as shown below. In the below image it’s showing the result of nmap scan which I have saved in my file “scan.xml”

Creating notes
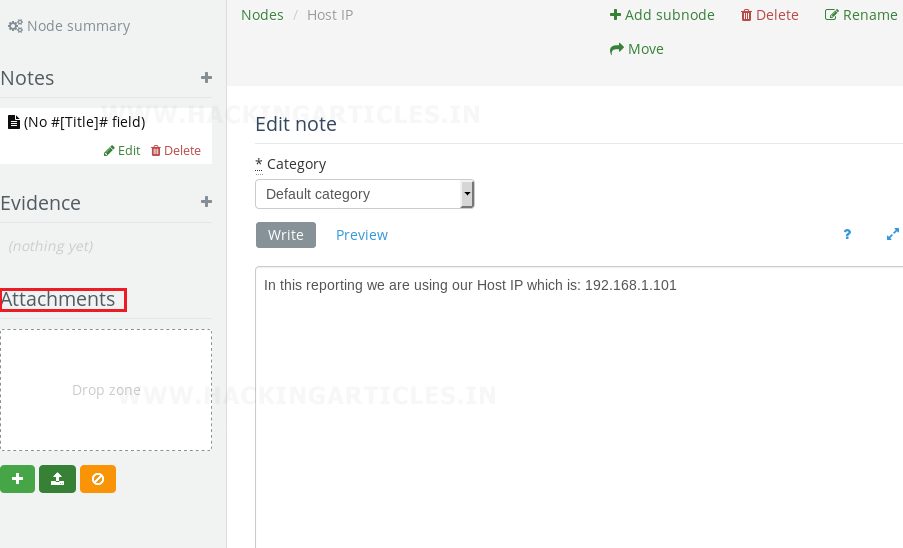
If you want to add a description about what you have done in each node and sub-nodes then it can simply be done by following below steps:
- Select node
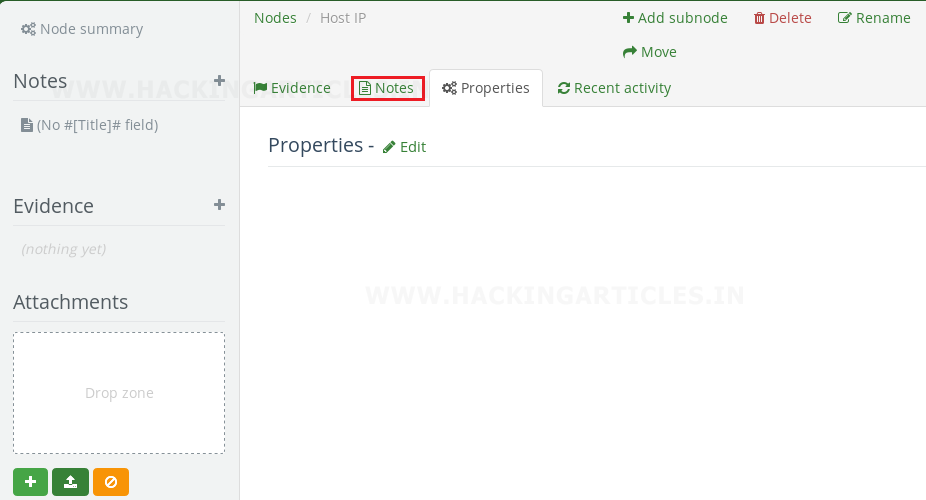
- Click on notes
- Click on add notes
- Write the description in space that is provided
- Click on create a note to confirm it.

In the below image, I have mentioned “IP” of my host machine as my note description. Similarly, you can create a note for any of node or sub-node to briefly describe your report. After creating your notes you can further edit, delete, and rename it as per desire. You can also add any of attachment, screenshot or image by simply drag and drop to attachment field.
Conclusion
This article focused on the main objective of using “Dradis” for creating any report rest all the options like “adding Issues, Methodologies” can be further use by the user as per requirements.
Author: Komal Singh is a Cyber Security Researcher and Technical Content Writer, she is completely enthusiastic pentester and Security Analyst at Ignite Technologies. Contact Here
Hello,
Just think you Mister CHANDEL.
I follow you.