Caldera: Red Team Emulation (Part 1)
Caldera is an open-source framework that assists in Red Team Emulation. This tool is invaluable for conducting adversary simulations based on the MITRE ATT&CK framework, automating red team activities, and enhancing cybersecurity testing.
This article aims to demonstrate an open-source breach & emulation framework, through which red team activity can be conducted more efficiently. It focuses on the MITRE simulation and offers many other functions that can also enhance the effectiveness of the activity.
Table of Contents
MITRE Att&ck
Caldera
- Pre-requisite & dependencies
- Interface
- Installation
- Plugins
Campaigns
- Step1: Deploy an Agent
- Step2: Abilities
- Step3: Setting up Operations
- Step4: Exporting the result
Conclusion
Mitre Att&ck
The Mitre framework provides a comprehensive list of Tactics, Techniques, and Procedures (TTPs) along with their corresponding sub-techniques, all arranged in a well-structured form. This list is highly useful for conducting red team activities.

Caldera
CALDERA breach & emulation tool designed to easily automate adversary emulation, assist manual red-teams and automate incident response.
The framework consists of two components:
The core system: This is the framework code, consisting of what is available in this repository. Included is an asynchronous command-and-control (C2) server with a REST API and a web interface.
Plugins: These repositories expand the core framework capabilities and provide additional functionality. Examples include agents, reporting, collections of TTPs and more.
Pre-requisite & dependencies
These requirements are for the computer running the core framework:
- Any Linux or MacOS
- Python 3.7+ (with Pip3)
- Recommended hardware to run on is 8GB+ RAM and 2+ CPUs
- Recommended: GoLang 1.17+ to dynamically compile GoLang-based agents.
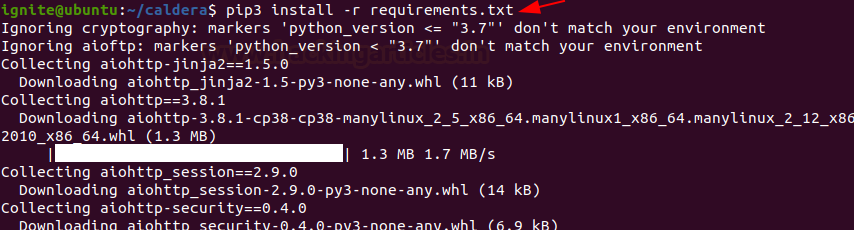
Installation
Follow these steps for setting up caldera:
git clone https://github.com/mitre/caldera.git --recursive

cd caldera pip3 install -r requirements.txt python3 server.py –insecure
Interface
Caldera provides web interface which is simple to navigate and use.
http://127.0.0.1:8888 username: red Password: admin


Plugins
The Plugins category offers a list of all current plugins and allows you to quickly and easily access their functionality.
- Access (Red team initial access tools and techniques)
- Atomic (Atomic Red Team project TTPs)
- Builder (Dynamically compile payloads)
- CalTack (embedded ATT&CK website)
- Compass (ATT&CK visualizations)
- Debrief (Operations insights)
- Emu (CTID emulation plans)
- Fieldmanual (Documentation)
- GameBoard (Visualize joint red and blue operations)
- Human (Create simulated noise on an endpoint)
- Manx (Shell functionality and reverse shell payloads)
- Mock (Simulate agents in operations)
- Response (Incident response)
- Sandcat (Default agent)
- SSL (Enable HTTPS for caldera)
- Stockpile (Technique and profile storehouse)
- Training (Certification and training course)
To know more about a particular plugin, follow the link.
Campaigns
Agents, adversaries, and operations make up the Campaigns category, which plays a crucial role in building the numerous agents, adversaries, and operations required for an effective red team operation or adversary emulation.
Step1: Deploy an Agents
Firstly, to begin with initial access we need to implant an agent inside the target system.
To set up an agent or listener:
In the campaign tab, click on agents

Then, choose an agent (3 types currently available).

Then, choose the platform (Windows, Linux or Darwin [mac OS]).

As soon as the platform is selected, you need to set up the IP, Port & name of the implant

It will also give a set of commands needed to be executed on the target
In the case of Linux/Mac OS, execute it on terminal

Deploy agent inside the target machine by simple copy-paste

In the case of Windows, execute it on PowerShell (Bypass the execution policy first)
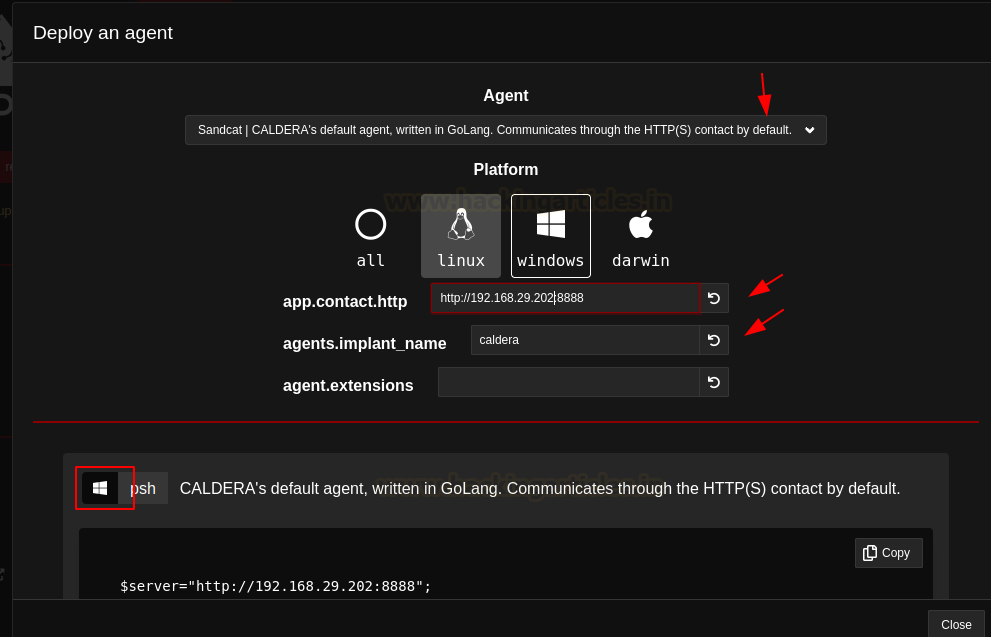
Deploy agent inside the target machine by simple copy-paste.

The agent pops back onto the caldera which specifies the command which was executed on the victim end was successful

Step2: Abilities
An ability is a specific ATT&CK tactic/technique implementation which can be executed on running agents. Abilities will include the command(s) to run, the platforms/executors the commands can run on (ex: Windows / PowerShell), payloads to include, and a reference to a module to parse the output on the CALDERA server.

As you can see in the above ss, we can select Platform and related TTP. Let us take a discovery as a tactic & Linux as a platform (the same tactic demonstrated for windows in this article)

Step3: Setting up Operations
After setting up the agent, now it is time to run the abilities or the set of instructions as shown above. For this, we need to set up an operation
To do this:
- Under the Campaigns tab, select operations
- Choose Create operations

Then, choose the adversary – Adversary Profiles are collections of ATT&CK TTPs, designed to create specific effects on a host or network. Profiles can be used for offensive or defensive use cases.

Fill in the details and specifications of the operation you want to run

Click on start, after a while, you can see that it starts running and populating the results on the screen

As you can see, all set of commands running is obfuscated in base64nopadd format (also you can select other options specified), we can also see the command and we can view the output of the command (Also, we can see the status of the task performed)


Step4: Exporting the result
After completing the activity, you can extract the report in two ways:
- Directly from the download tab, which appears once the operation is completed.

- Alternatively, go to the debrief tab, select the pointers to include in the report, and then download the full report as a PDF.


Conclusion
We have thus been able to perform the adversary simulation with the help of Caldera. Using this framework, Red/Purple team activities can be easily performed.
Reference: https://caldera.readthedocs.io/en/latest/
Author: Ankit Sinha is a security researcher with expertise in Pentesting, Threat hunting and red teaming. Also, likes to work on a Myriad of things in the discipline of offensive security. Contact here