Beginner Guide to Footprinting
There are many saying about knowing your enemy, time and time again these sayings have proved to be true. Today we hear all around the work of hackers and many-a-times we fail to protect ourselves. This happens because we are not familiar with their working process. Therefore, in this article, we are here to make to accustomed to the first step of the process i.e. Footprinting.
In the world of Cyber Security, Footprinting is the first step which lets penetration testers gather information about hardware or network. It is basically an exploration process which helps us to know our enemy. In order to complete the penetration process, one ought to gather as much information as possible. Footprinting can be done either actively or passively. Assessing a company’s website with their permission is an illustration of passive footprinting and trying to access sensitive information through social engineering is an illustration of active information gathering.
Types of Footprinting:
- Footprinting through Search Engine
- Footprinting through social engineering
- Footprinting through Social Networking sites
- Website Footprinting
- Competitive Intelligence
- WHOIS Footprinting
- Footprinting using advanced Google hacking techniques
- Email Footprinting
- DNS Footprinting
- Network Footprinting
As this is the first part of our footprinting series, we will discuss the first three types of footprinting.
Footprinting through Search Engine
Footprinting through the search engine is unambiguous in itself. People often wonder what one can find through the search engine as the common concept of the search engine is basic exploring. But results given by the search engine can be used to hacker’s advantage as they are vast in nature.
Attackers use search to gather information about their target such as technology platforms, employee details, login pages, intranet portals, etc. which helps in performing social engineering and/or other types of advanced system attacks.
Even search engine cache and internet archives may provide sensitive information that has been removed from the World Wide Web (WWW).
There are many search engines where you can find anything that desires from finding the meaning of the word to finding a person. Such search engines are:
Now let’s take the example of google.com. If I search “Raj Chandel” on Google, then it will give me every possible result associated with the said person.

Same will be the result from other search engines. But different search engines are often used for particular searches. As shown above, Google is good for general information. If you want to know which websites are hosted on a particular server then you can use the Bing search engine. To know an IP address of any website just ping the website as shown below :
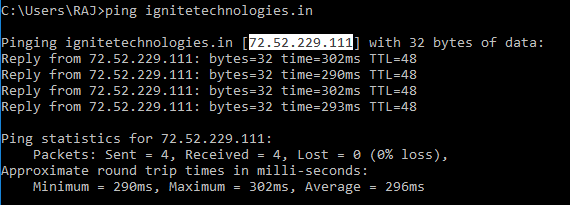
Now, open bing.com and type the IP in the search tab and press enter.
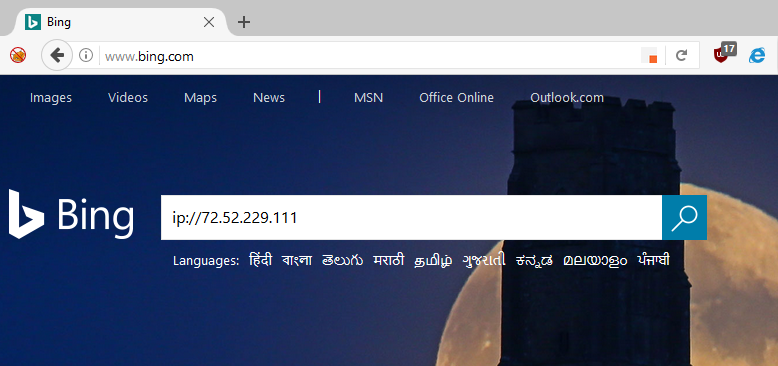
So like this, Bing can give you details about websites which are hosted in the same server
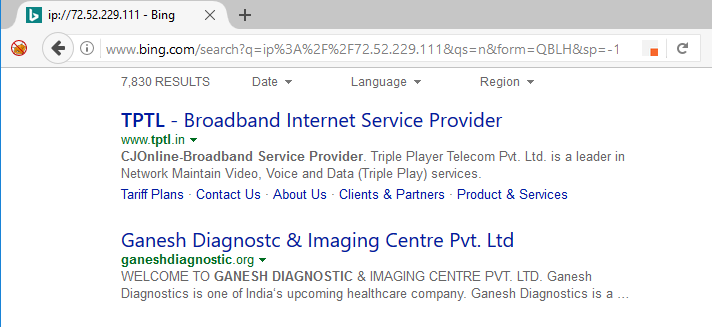
Another search engine is shodan.io, it helps to locate various open ports, vulnerable IP’s, and effected digital-ware all over the world. Open shodan.io in your browser and search for port or IP.
For a detailed tutorial of shodan.io please follow this link:
http://www.hackingarticles.in/shodan-search-engine-hackers-beginner-tutorial/
Footprinting through Jobs Seeking Sites
Similarly, you can collect an abundance of information through job sites. You can know about the company’s infrastructure details, employee’s profile, hardware information, software information. Some of such sites are:
https://www.careerbuilder.co.in/
www.naukri.com
Footprinting through Alerts
There is also a feature of adding alerts. This feature gives you an alert if anything is changed in a particular website; given that you have added an alert to the said website. To do so, open google.com/alerts and type the name of the website that you wanted to alert about. And then click on create an alert.
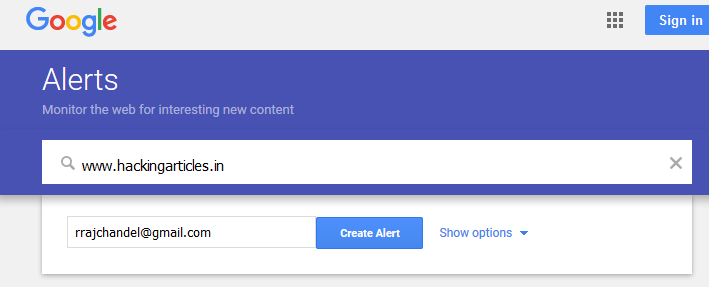
And this way an alert will be created.
Footprinting through Social Networking Sites
Attackers use social networking sites like Facebook, Twitter, and Pinterest etc. to gain important and sensitive data about their target. They often create fake profiles through these social media to lure their target and extract vulnerable information.
Employees may post personal information such as DOB, educational and employment background, spouse’s names, etc. and information about their company such as potential clients and business partners, trade secrets of business, websites, company’s upcoming news, mergers, acquisitions, etc.
Even the information about the employee’s interest is tracked and then they are trick into revealing more information.
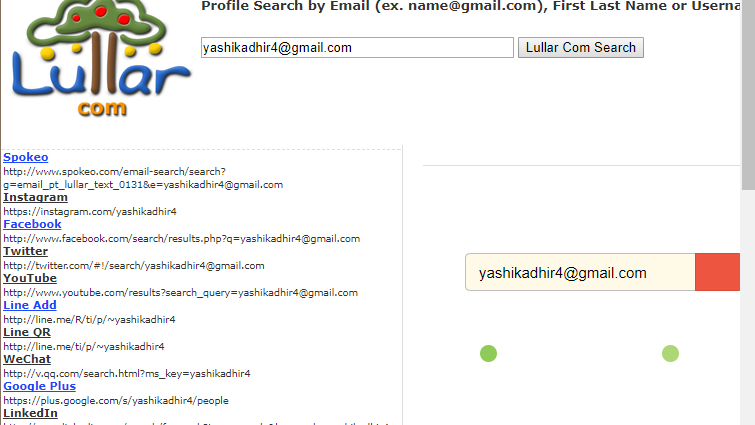
Now if you want to search a particular person using just their name or email then there are specialized websites for it like pipl.com and lullar.com
Open pipl.com and type the name of the person you want to search about. For instance, I have searched my own name and as you can see in the image below we get a positive result.

Now open lullar.com, here you can search for people using their email and much more. Here, I have searched through email (using my own email) and there is a positive result in the image below.
Footprinting through Social Engineering
Social engineering is an art of manipulating human behavior to our own advantage. This proves most helpful when the need for extraction of confidential information. To do so, we have to depend on the fact that people are unaware of their valuable information and have no idea about being exploited. The most common example for this is when people call as fake credit/debit card companies and try to extract information.
Techniques used for social engineering are:
Eavesdropping
Shoulder surfing
Dumpster diving
Impersonation on social networking sites
This is how footprinting is done through search engines, social networking sites and social engineering. As white hat hackers, we should know about it but we should also be aware try to protect ourselves from black hat hackers against footprinting.
Author: Yashika Dhir is a passionate Researcher and Technical Writer at Hacking Articles. She is a hacking enthusiast. contact here
I Am interested