Android Pentest: Automated Analysis using MobSF
Introduction
Ajin Abraham developed MobSF, an open-source tool that performs automated analysis of an APK. This collection of tools runs under one interface, performs their tasks (like Jadx, apktool, etc.), and displays their results under a common interface. Users can download these reports in PDF format too, which provide detailed analysis with necessary screenshots. You can download MobSF here. In this article, we’ll guide you through the installation phase in Ubuntu OS and walk you through the various options that this tool offers.
Table of Content
- Installation
- Landing Page
- Signer Certificate Analysis
- Application Permissions
- Browsable Activities & Network Security Analysis
- Manifest Analysis
- Code Analysis
- Related to Malware Analysis
- Hardcoded secrets
- Activity Components Present
- Files Present in APK Packages
- Dynamic Analyzer
- Logcat Stream
- API Monitor
- Downloading Reports
Let’s begin!
Installation
To install MobSF, create a directory and follow the commands:
git clone https://github.com/MobSF/Mobile-Security-Framework-MobSF.git cd Mobile-Security-Framework-MobSF
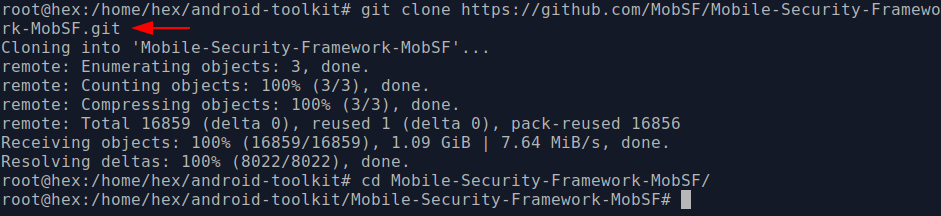
We need to install dependencies before we are able to run:
apt-get install python3-venv pip3 install -r requirements.txt
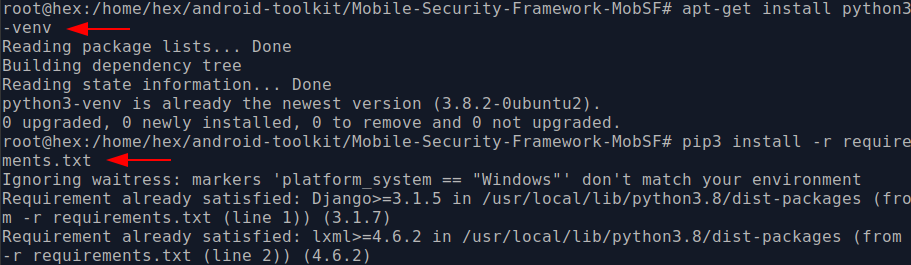
Once done, we can run the setup file to install MobSF and all the components automatically
./setup.sh

Now, to run MobSF we execute the run.sh file. As one could interpret from the screenshot below that MobSF would be running on a local server on port 8000.
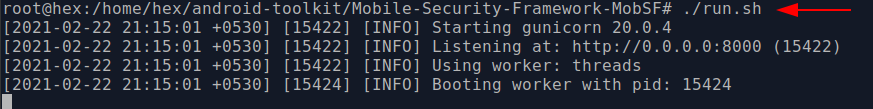
Now let’s open the link in the browser and see if MobSF was installed properly or not.
Landing Page
Now that the MobSF is up and running, we can drag a dummy APK (in this case, I’ll take InjuredAndroid by Kyle Benac (here)) into the MobSF interface and see what happens. After waiting for a couple of minutes we could see that static analysis of the APK is done. Now here on the landing page, we can see that a severity score is given. The higher this score the more secure app is. Next, hashes, filename and size of the APK are also given. In the third column in the first row, we can also see the package name, main activity, min SDK version and the application version as well. The description of the application is also given.
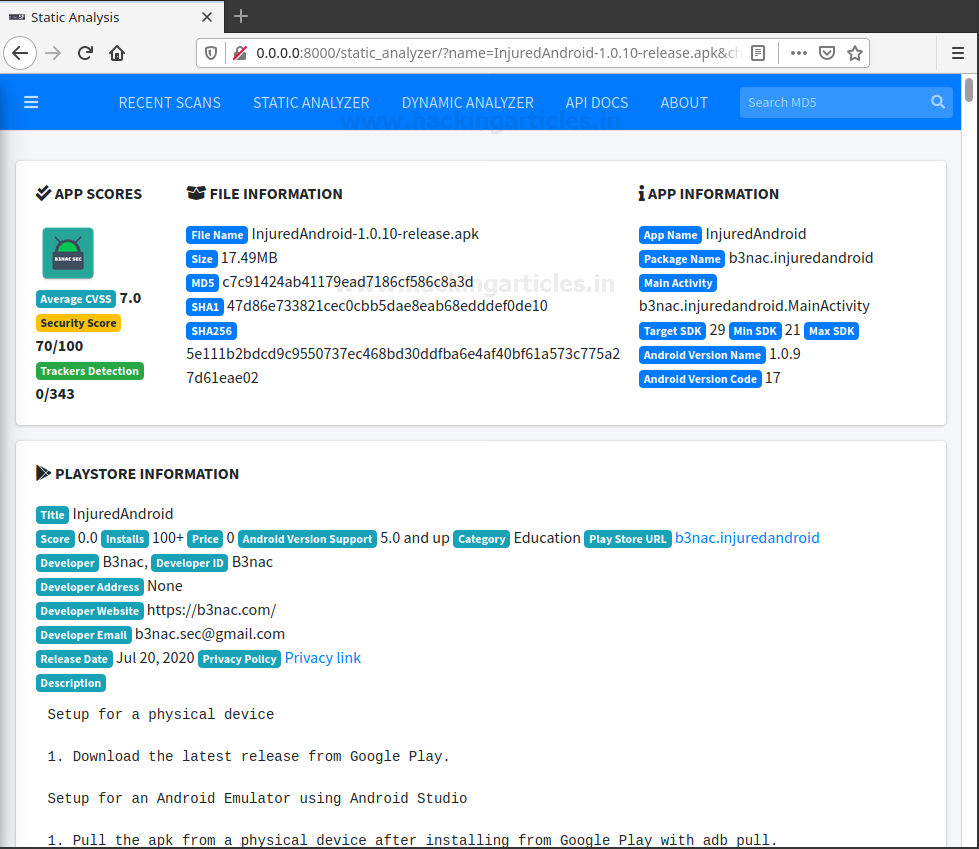
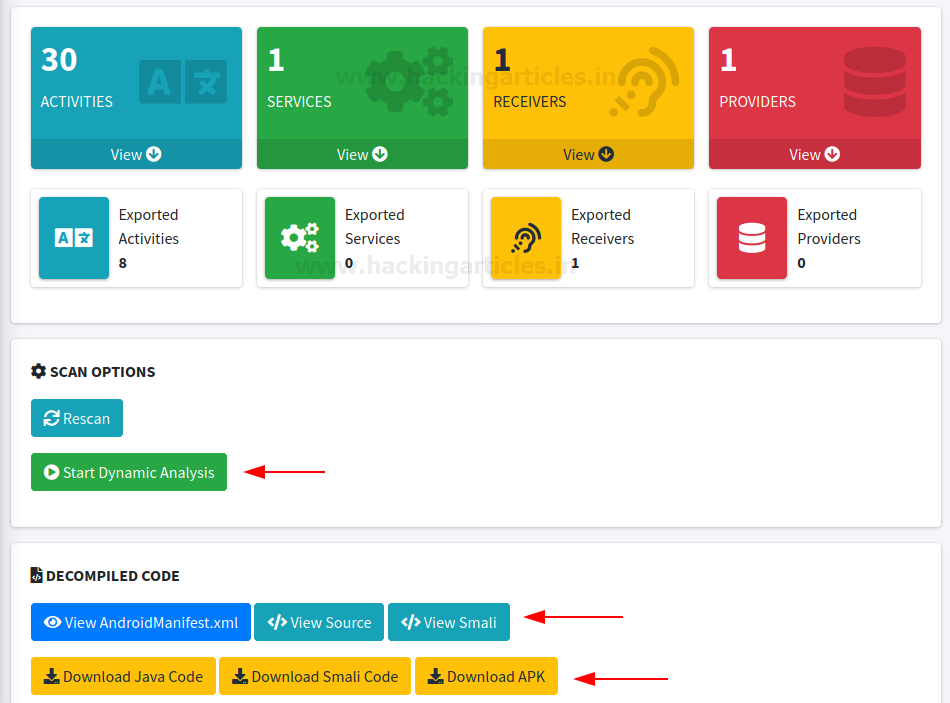
After scrolling down a little bit, here’s what all we can see:
- In small cards, we see different application components
- Dynamic analysis option that will help MobSF conduct runtime analyses
- Option to view decompiled code. This is the code that is generated by APKTool. Generally, the resources file would also be decoded. It is also possible to view smali code. It makes it easier to segregate and view source code in separate java classes using this.
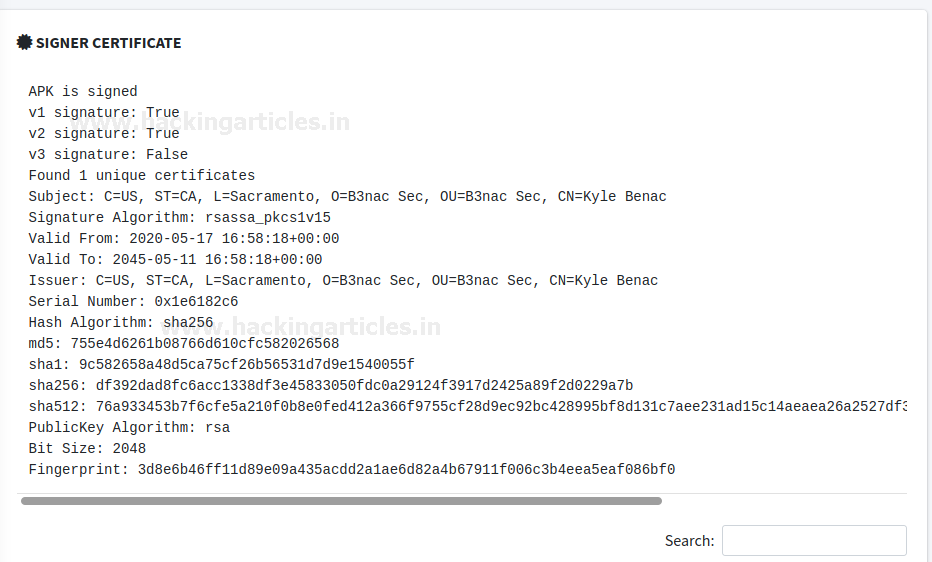
Signer Certificate Analysis
In the certificate column, we can see the signer certificate where one can find important information about the developer, country, state, type of algo, bit size etc.
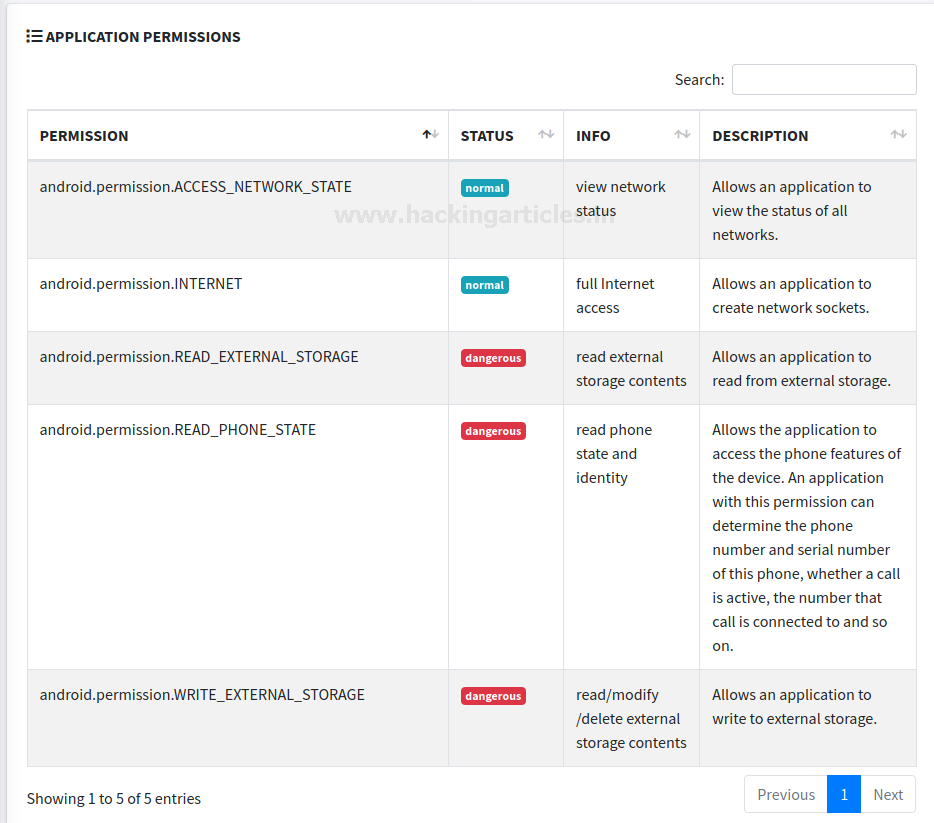
Application Permissions
Further, we can see all the permissions an application has. Various permissions are categorized as dangerous or normal. It is important from a security analyst’s point of view to understand which permissions can lead to further damage. For example, if an application has access to external media and stores critical information on the external media it could prove to be dangerous since the files stored on external media are globally readable and writable.
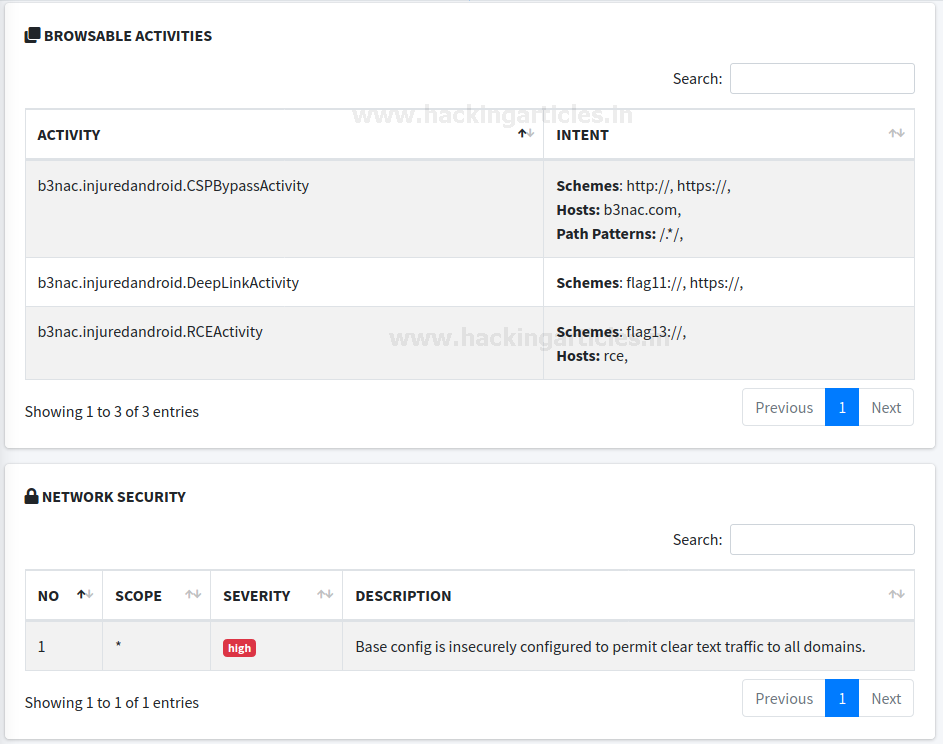
Browsable Activities & Network Security Analysis
Next, in the browsable activities section, we can see all the activities that have implemented a deep link schema. Please refer to the article here to understand all about deep links, its implementation as well as exploitation.
In the network security section, one can find some details about network security issues related to the application. These issues can lead to critical attacks like MiTM sometimes. For example, in the screenshot below, one can find that the application isn’t using the SSL pinning mechanism implemented.
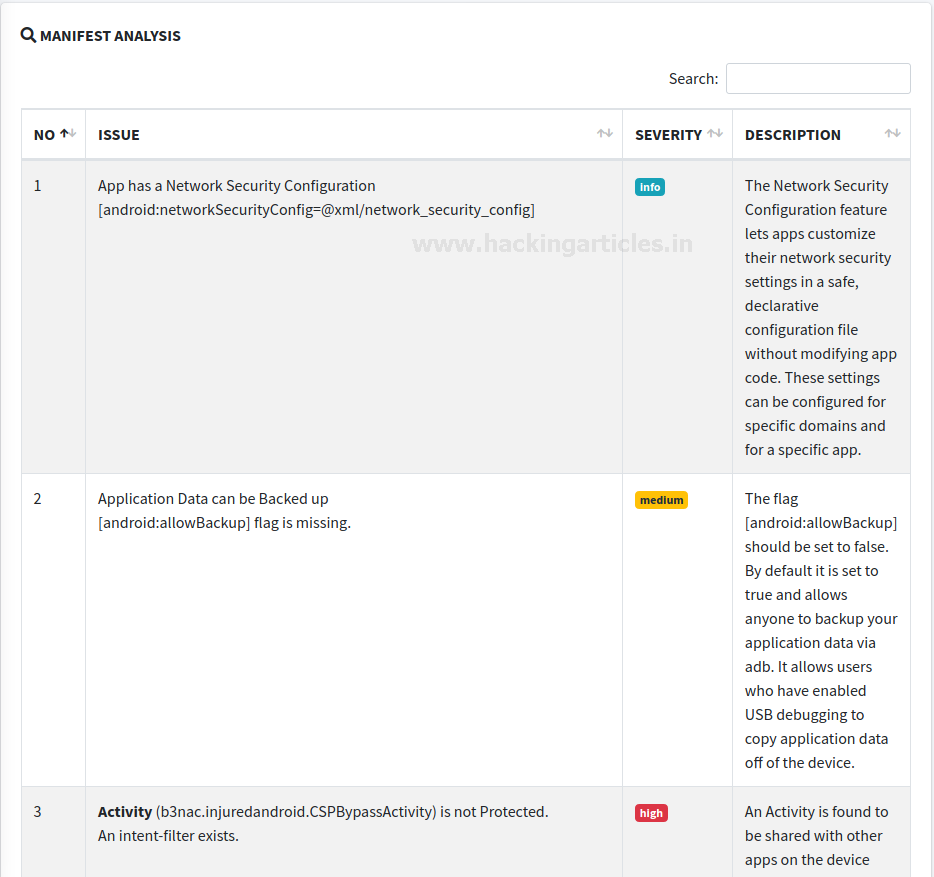
Manifest Analysis
In the next section, MobSF has analysed the manifest file. One can find many folds of information from the android manifest file like which activities are exported, if the app debuggable or not, data schemas etc. For reference look at the screenshot below.
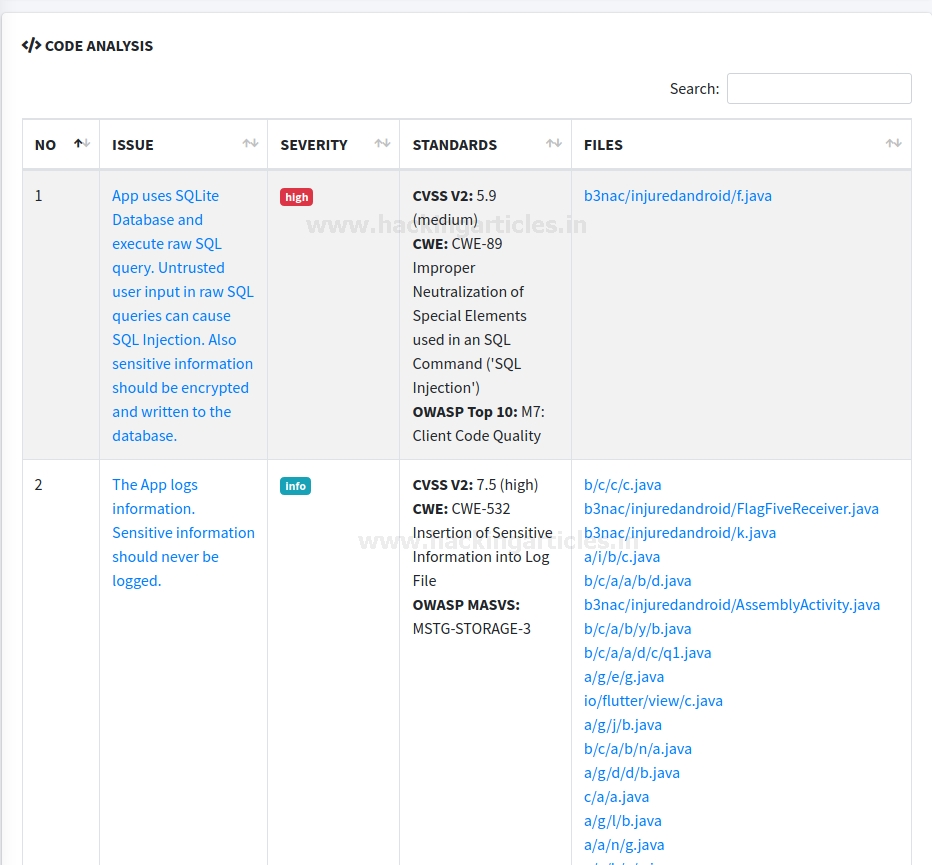
Code Analysis
One of the most interesting features of the MobSF tool is the code analysis section. In this section, we can see that MobSF has analysed and compared some behaviour of the application based on industry security standard practices like OWASP MSTG and mapped the vulnerabilities with OWASP Top 10. It is interesting to see CWE mentioned and CVSS score being assigned here which might help various analyst scenarios and help the creation of reports way easier.
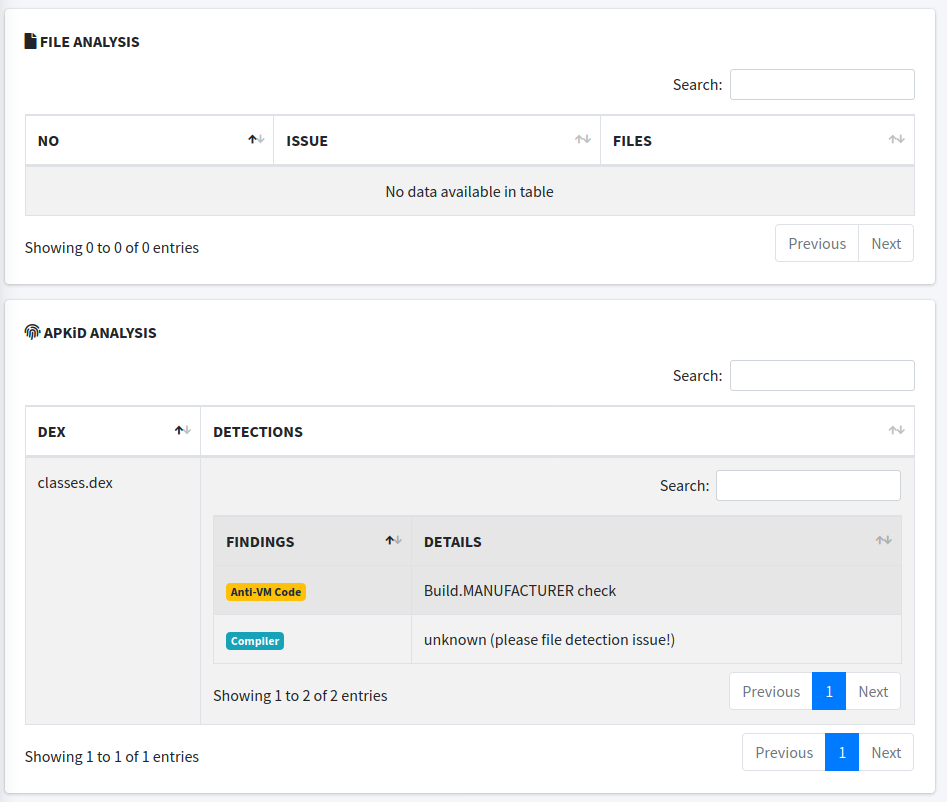
Related to Malware Analysis
MobSF also hosts a section where an APKiD analysis is given. APKiD is an open-source tool that is very helpful to identify various packers, compilers, obfuscators, etc in Android files. It is analogous to PEiD in APK. Here, one can see that it has detected an anti-vm code in the APK.
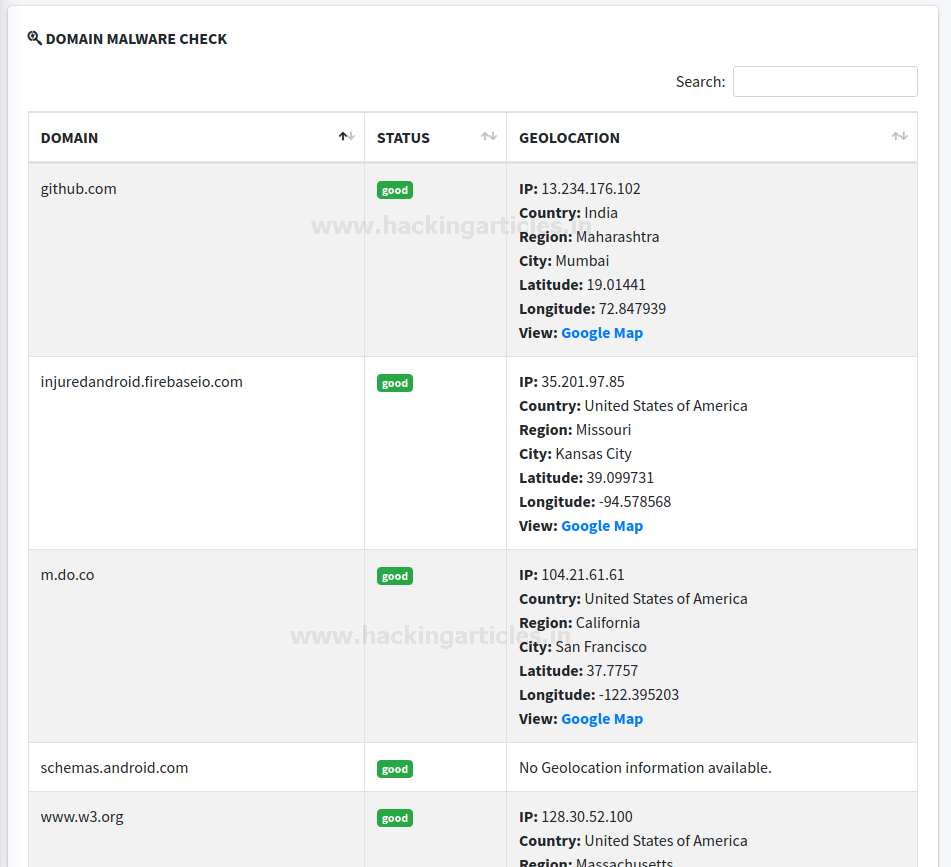
Something related to malware analysis is the domain malware check feature. Here, MobSF is extracting all the URLs/IP addresses that are hard-coded or being used in the application and shows its malware status as well as uses ip2location to give out its geolocation as well.
Strings Analysis and Hardcoded Data
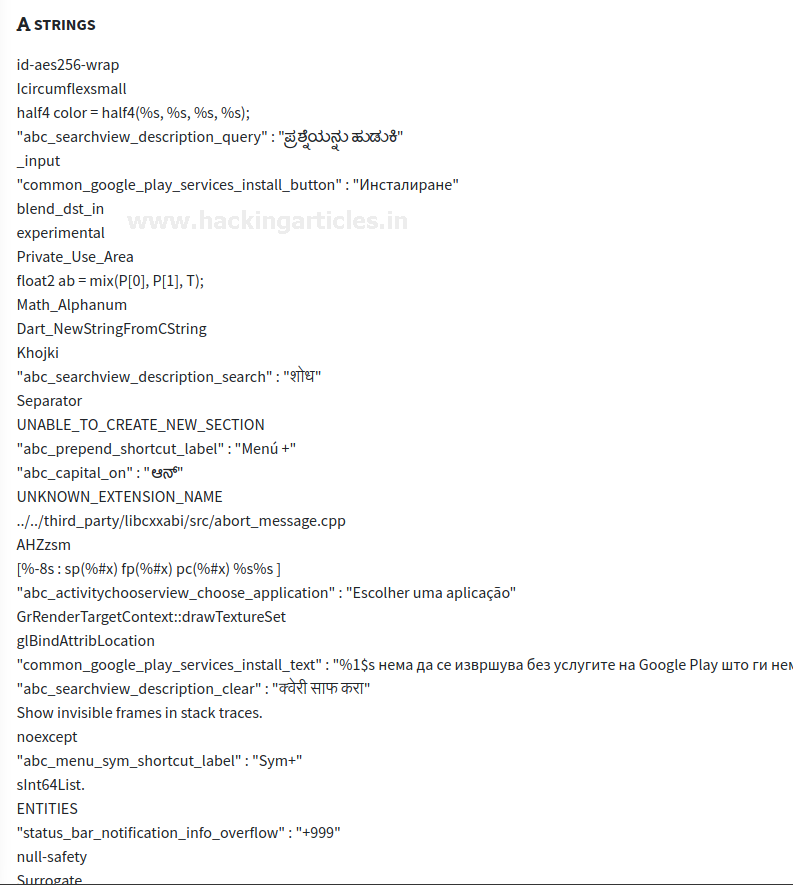
A comprehensive strings analysis is also available. People who are aware of malware analysis know about strings in-depth but for those of you who don’t, strings are ASCII and Unicode-printable sequences of characters embedded within a file. Extracting strings can give clues about the program functionality and indicators associated with a suspect binary. For example, if an APK shows something as an output so that stream would be called and hence shown in the strings. This is not the same as strings.xml file. Many times, a third party IP address with which APK is communicating gets visible here. This is essential from a malware analysis point of view.
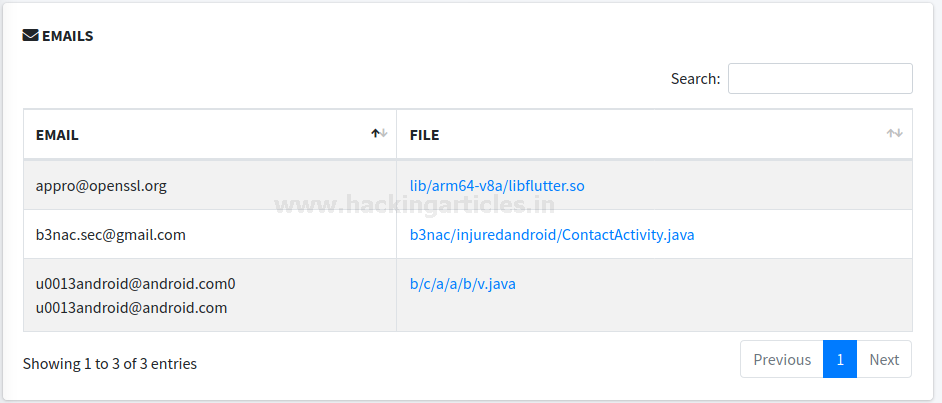
One can also find hardcoded emails in MobSF. This is all done using the decompiled source code. Often a pentester can find critical email IDs that were being used as a credential on a third party site, say, to access the database.
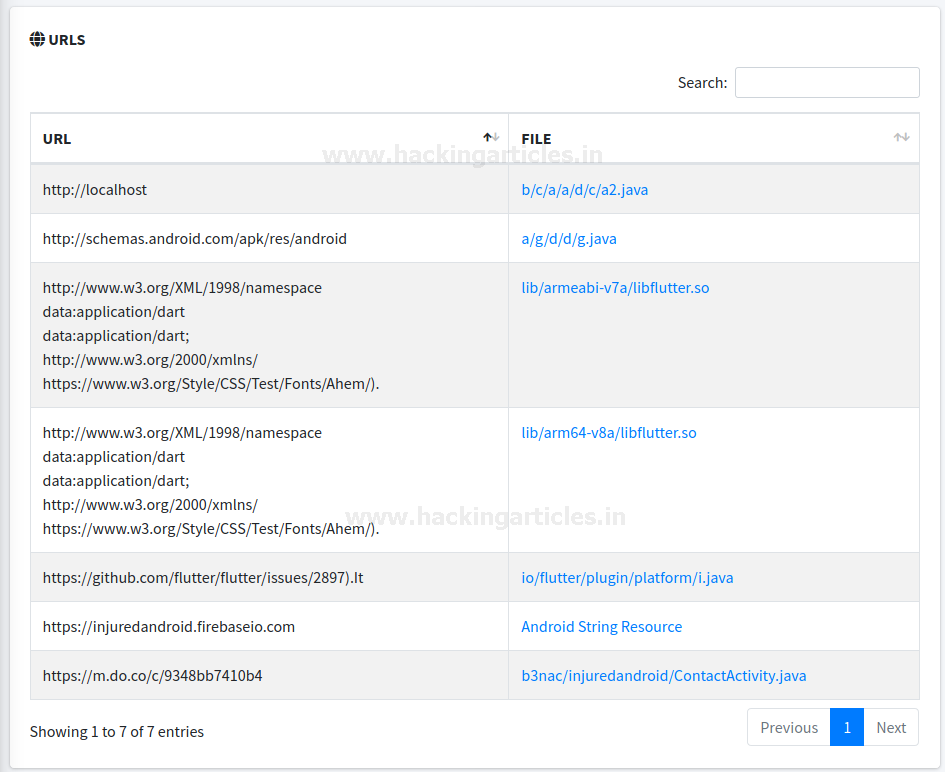
Just like emails, developers often hardcode URLs as well. One can sometimes find juicy URLs that users utilize. Oftentimes, analysts discover that malicious URLs are accessed as well or even a C&C server.
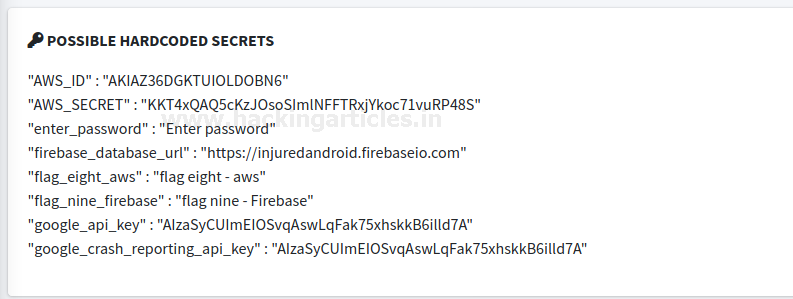
Hardcoded secrets
Oftentimes developers have this habit of storing critical keys like AWS ID and credentials in strings.xml and use an object as a reference in java activity. But doing this doesn’t help in any which way since strings.xml can be decoded easily.
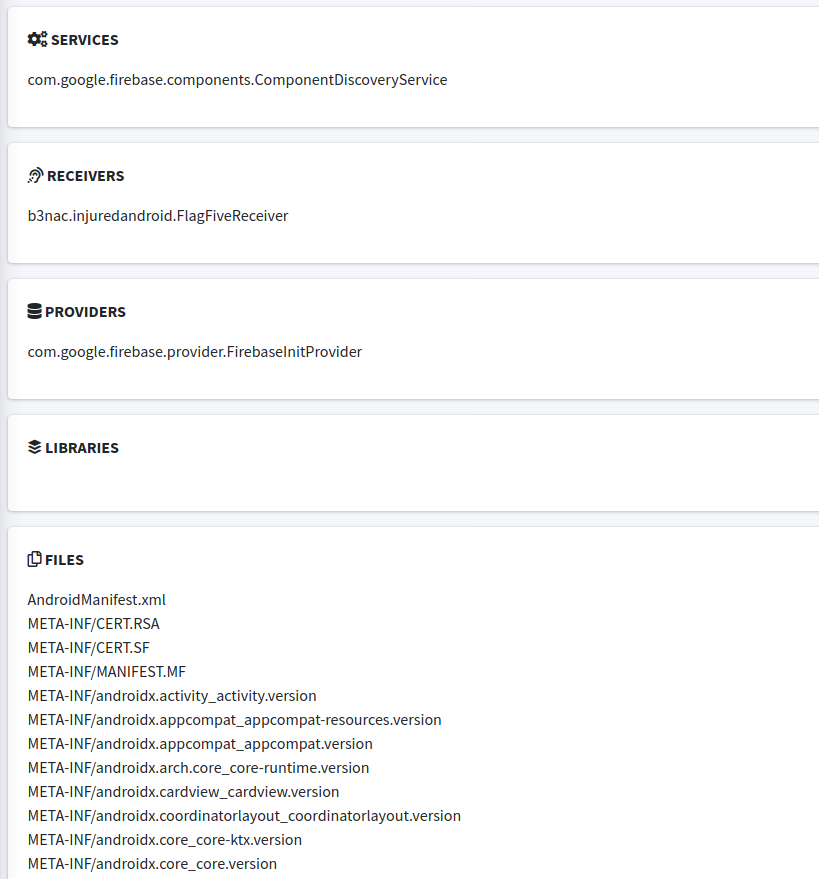
Activity Components Present
A list of all the activities present can also be scrolled using MobSF. This gives an insight into the skeleton of the android APK. Also sometimes jadx replaces the real names of the class with some random letter if the developer has applied obfuscation, MobSF can associate its real name too (doesn’t happen all the time or in cases of strong obfuscation).
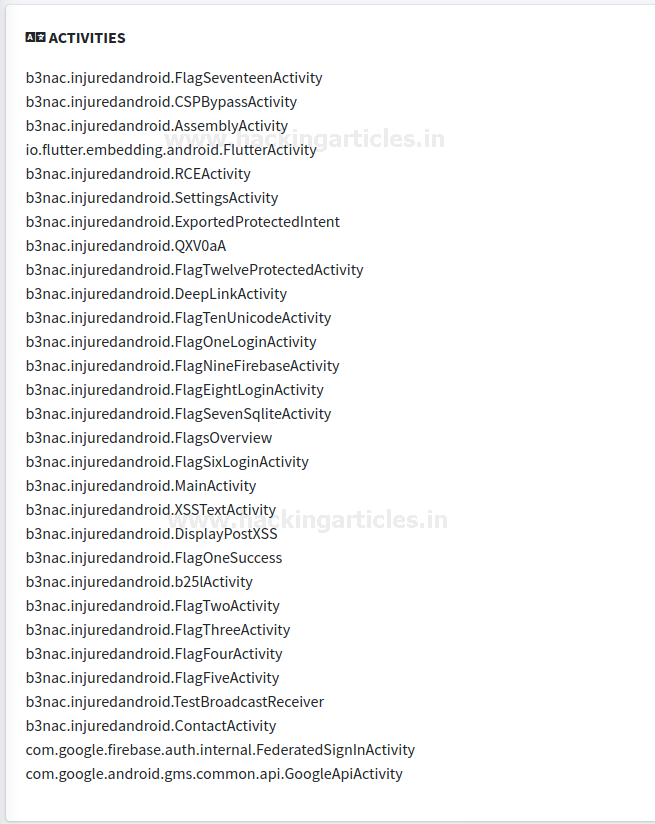
Quite similarly an analyst can also traverse services, broadcast, providers and content receivers along with all the files present in the APK archive to create a map of all the resources present in the application.
Dynamic Analyzer
For dynamic analysis, we’d need to fire up android VM in genymotion first. Here I’ve created an android VM on version 7.1

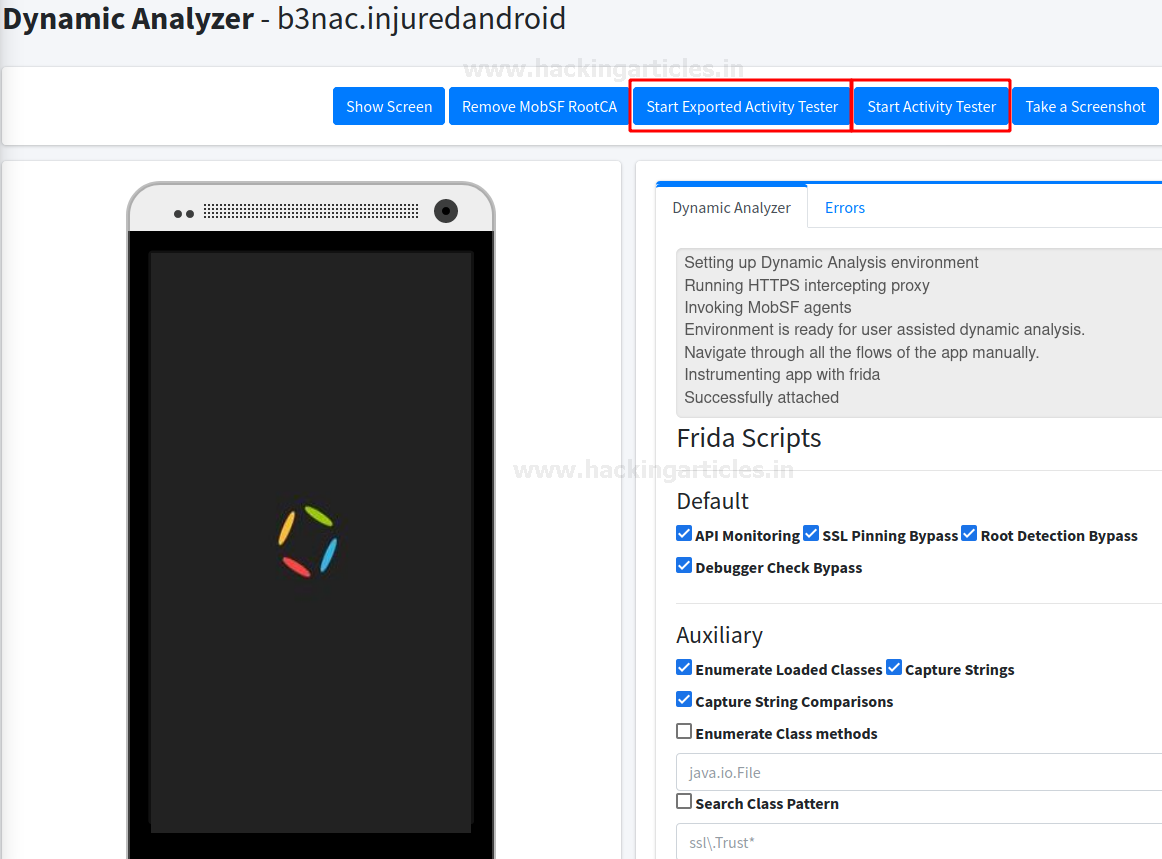
When you press the dynamic analyser option present on the top navigation pane, MobSF will automatically attach itself to VM running if MobSF and genymotion are running on the same base machine. However, if MobSF is in another virtual machine, you might have to attach MobSF agent to genymotion’s VM’s remote IP and port. Once it is attached, we see the following screen.
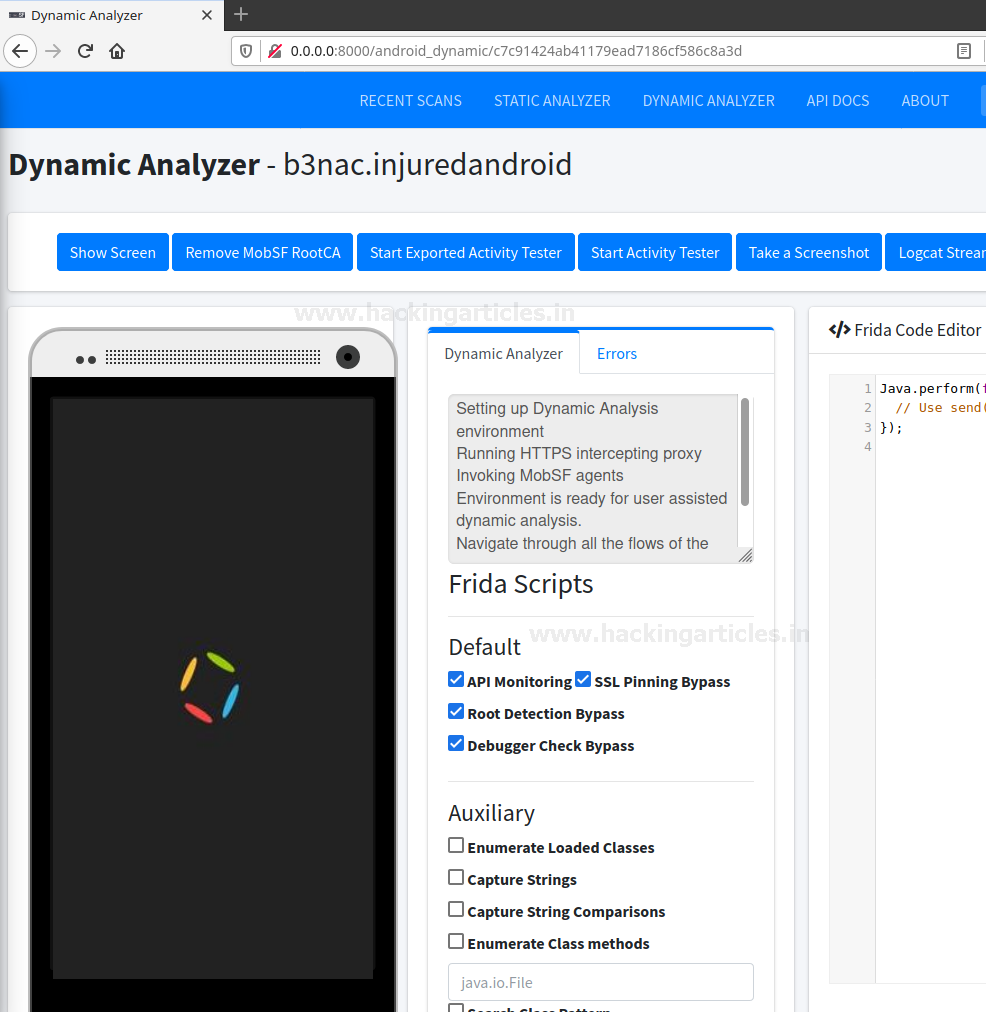
Understanding Frida Scripts for Security Testing
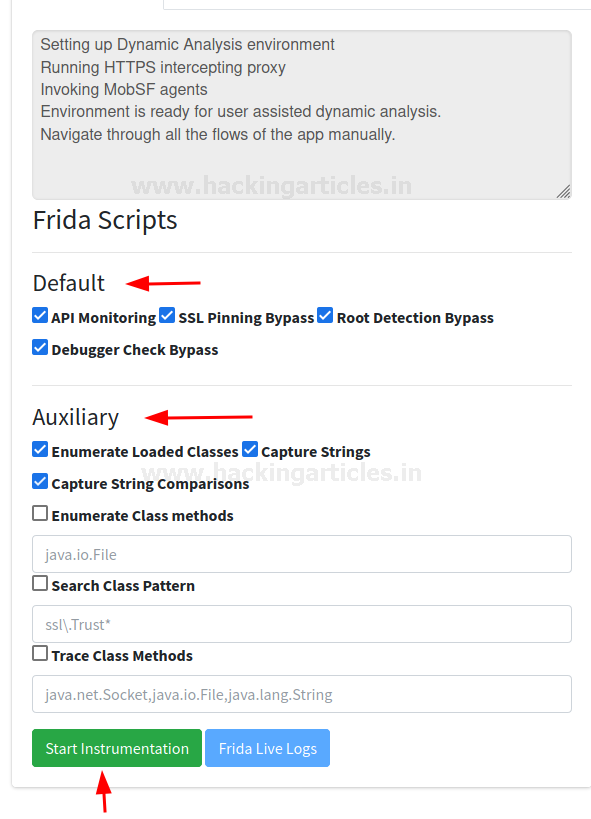
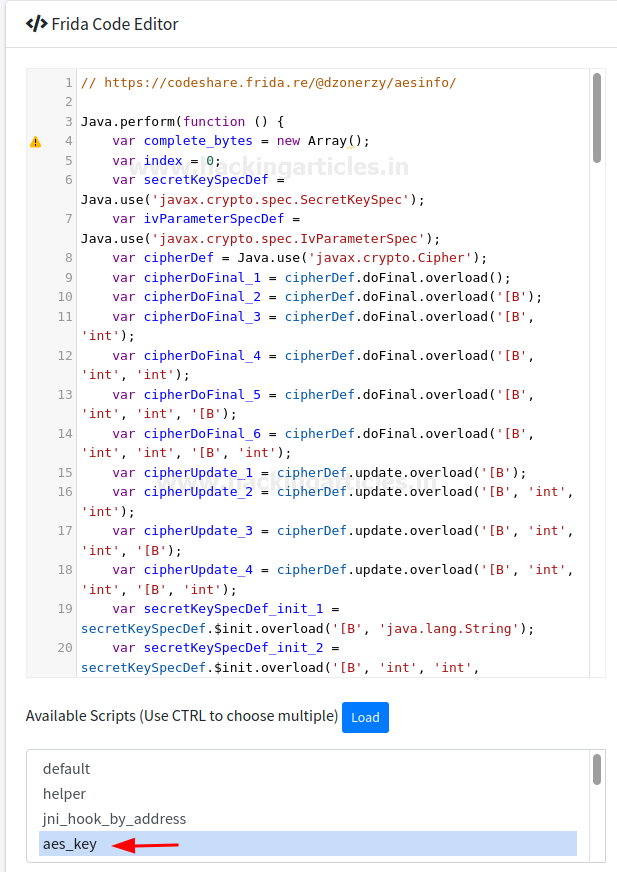
Under the analyzer status bar we can see various default frida scripts available that would check various basic vulnerabilities like SSL Pinning bypass and Root detection checks. If you haven’t read about frida, please do so by going here. There are other auxiliary scripts as well that lets an analyst enumerate various classes and also capture string comparisons in real time (again helpful for malware analysts point of view). Then simply click on start instrumentation and the application will automatically attach the selected scripts. Hence, if I have selected the SSL Pinning bypass script and the system captures traffic (visible in log or API monitor later), that would mean SSL Pinning has bypassed.
Now further, to analyse activities for vulnerabilities, one can see two buttons on the top for both exported and non-exported activities
Logcat Stream
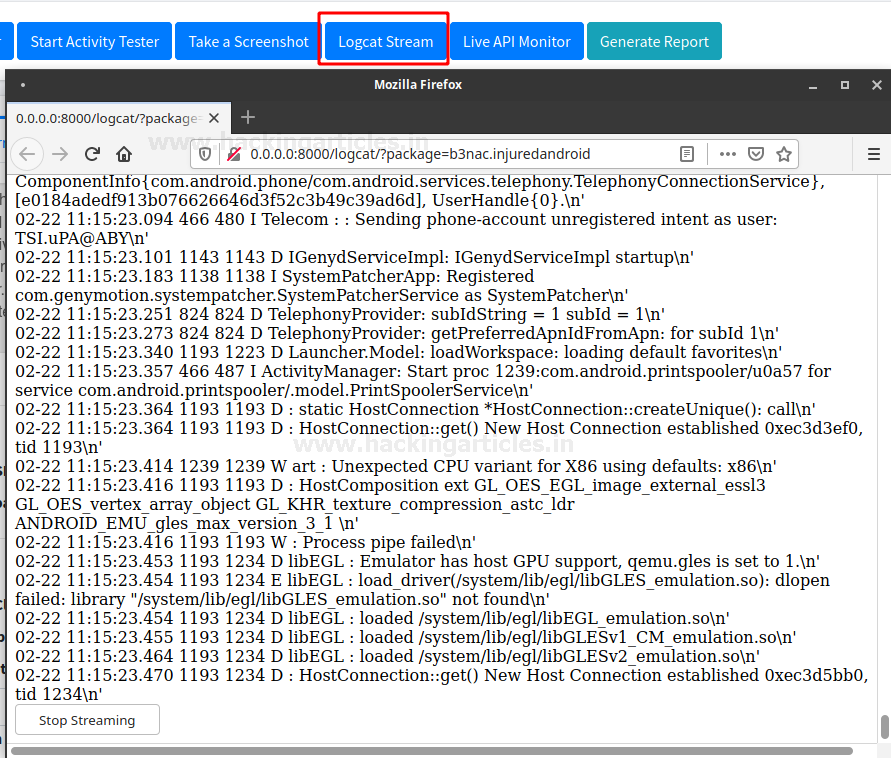
Logcat can also be viewed in MobSF’s native environment. There’s a button at the top menu that lets one view this.
API Monitor
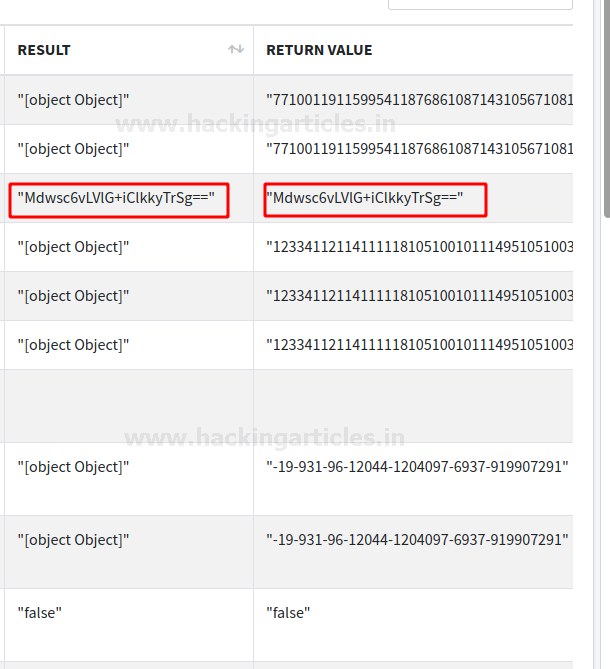
Just like logcat monitors device logs, APIs can also be monitored. APKs use various APIs in real-time to perform various functions, for example, the Base64 library.
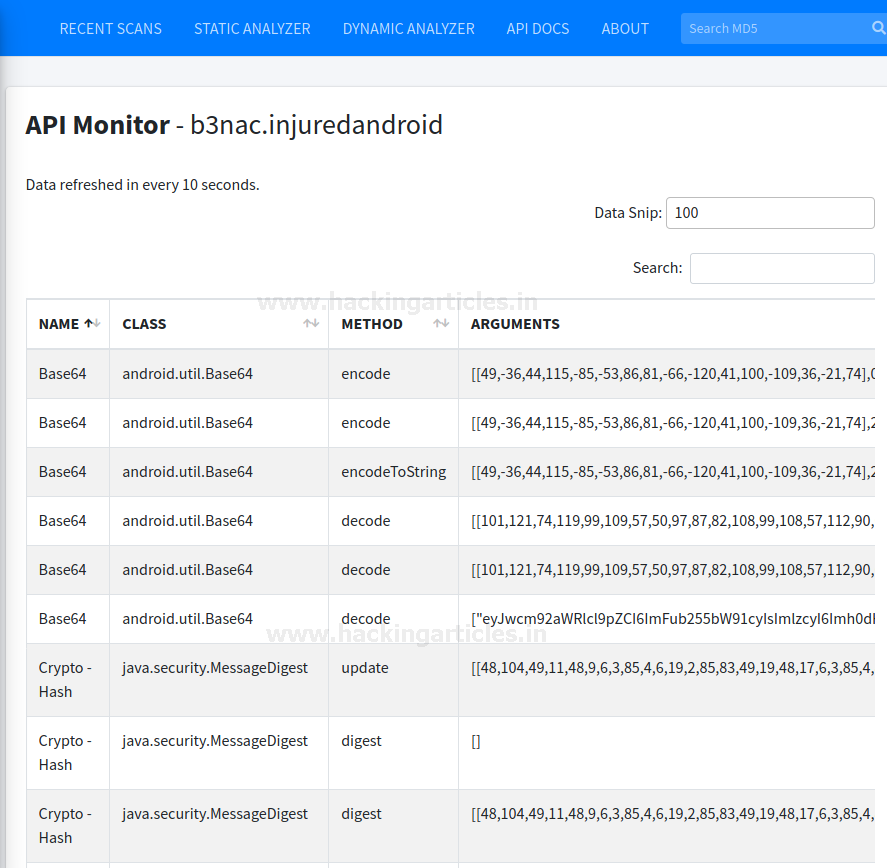
Hence, if a function is using this API and decrypting a value we can see that value here and decode that. For example, down below you can see the return value of once such function in Base64.
Downloading Reports
Once you have done the analysis, it is possible to download the report by sliding the menu bar slider on the left-hand side and click generate the report.
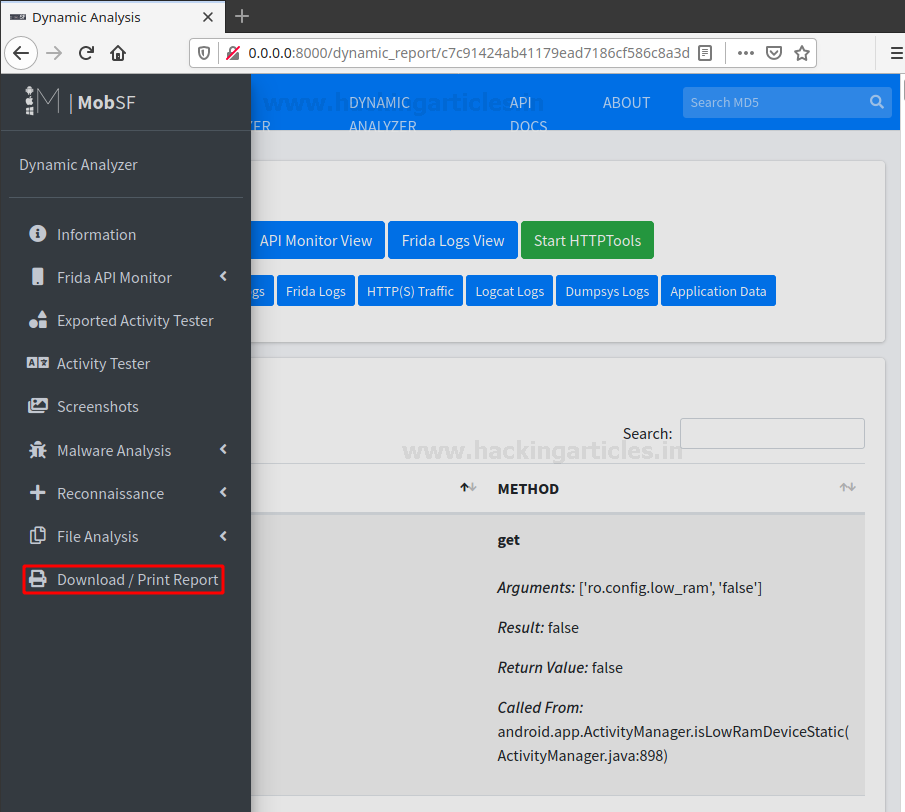
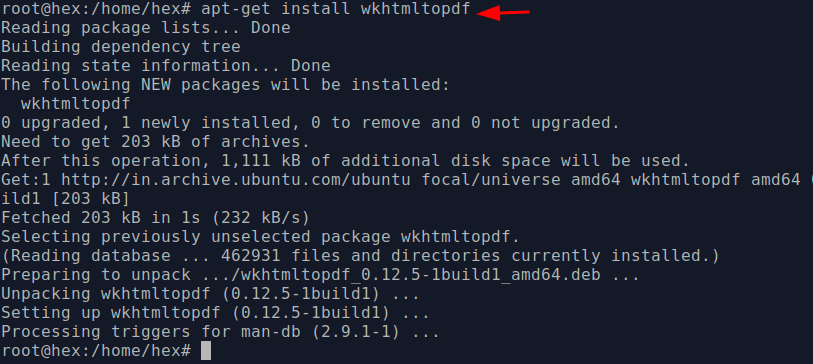
You might notice some errors while generating reports. To resolve this, you can follow the below command and install wkhtmltopdf module:
apt-get install wkhtmltopdf
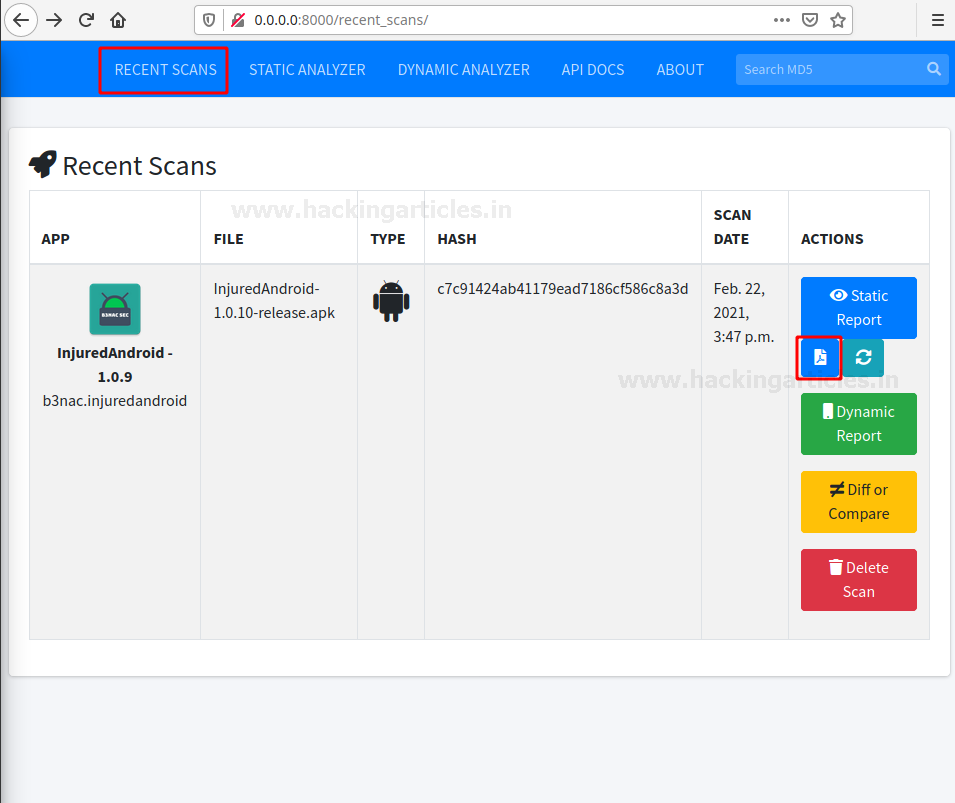
Now, once again if you click on a recent scan bar, you’ll see static and dynamic report generation options.
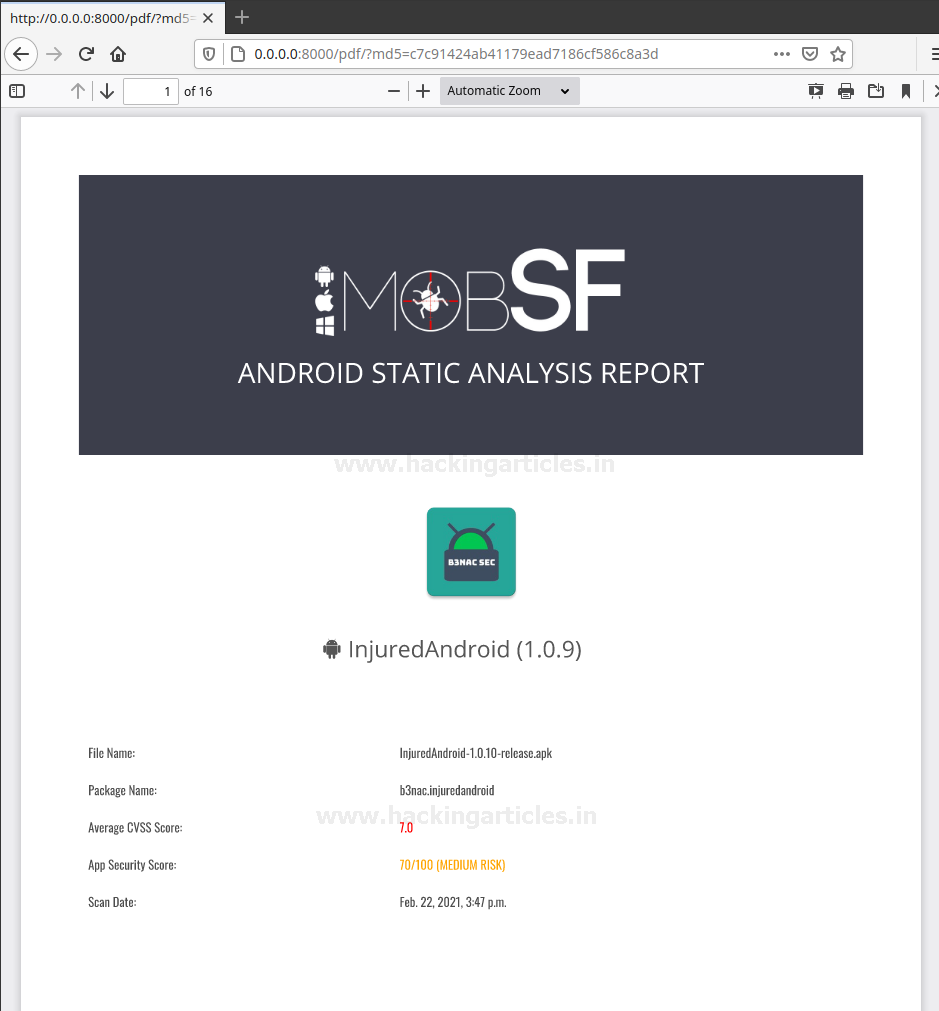
The report looks something like this:
Conclusion
MobSF is a great tool for conducting automated analysis on Android APKs. It doesn’t cover analysis of all the vulnerabilities, and analysts can only conduct many tests manually, but it is a nifty little tool that helps them to a great extent. Thanks for reading.
Author: Harshit Rajpal is an InfoSec researcher and a left and right brain thinker. Contact here
Very good
Best post on Android penetration testing
Está bueno el post, muchas gracias.